2024 클라우드 보안 가이드(AWS, AZURE, GCP)
https://www.skshieldus.com/kor/support/eventDetail.do?idx=501#
클라우드서비스 보안인증기준 해설서(2023.03)
클라우드 취약점 점검 가이드
https://isms-p.kisa.or.kr/main/csap/notice/
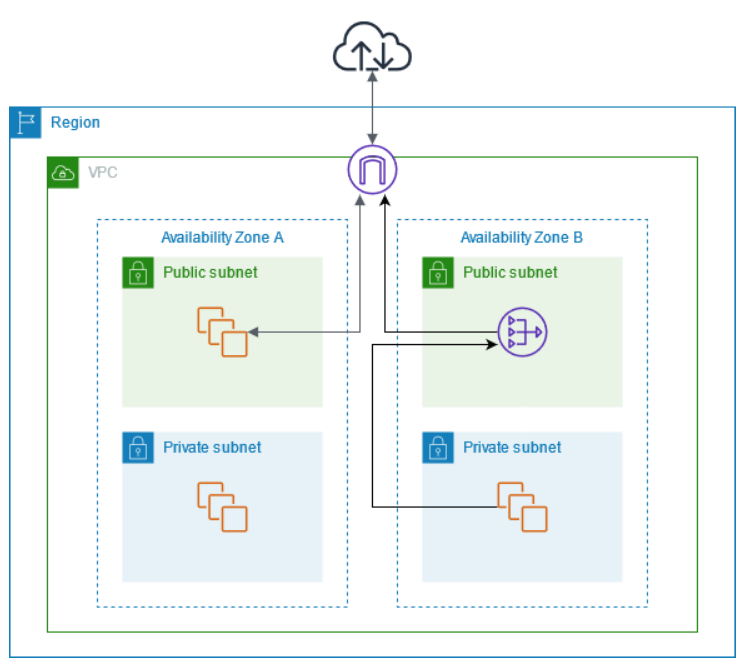
📌 NAT Gateway
프라이빗 서브넷
인터넷 게이트웨이로의 라우팅이 포함되지 않은 서브넷
NAT 게이트웨이
NAT(네트워크 주소 변환) 서비스
프라이빗 서브넷의 인스턴스는 VPC 외부의 서비스에 연결할 수 있지만 외부 서비스에서 이러한 인스턴스와의 연결을 시작할 수 없도록 NAT 게이트웨이의 사용이 가능
https://docs.aws.amazon.com/ko_kr/vpc/latest/userguide/nat-gateway-scenarios.html
📌 리소스 정리
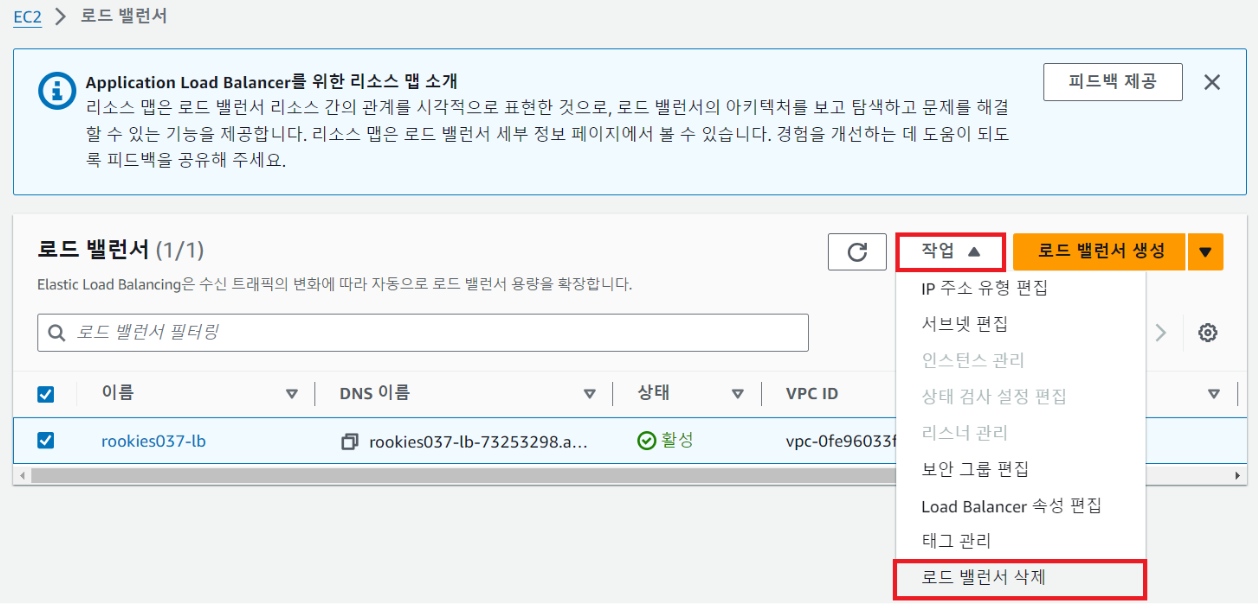
① 로드밸런서 삭제
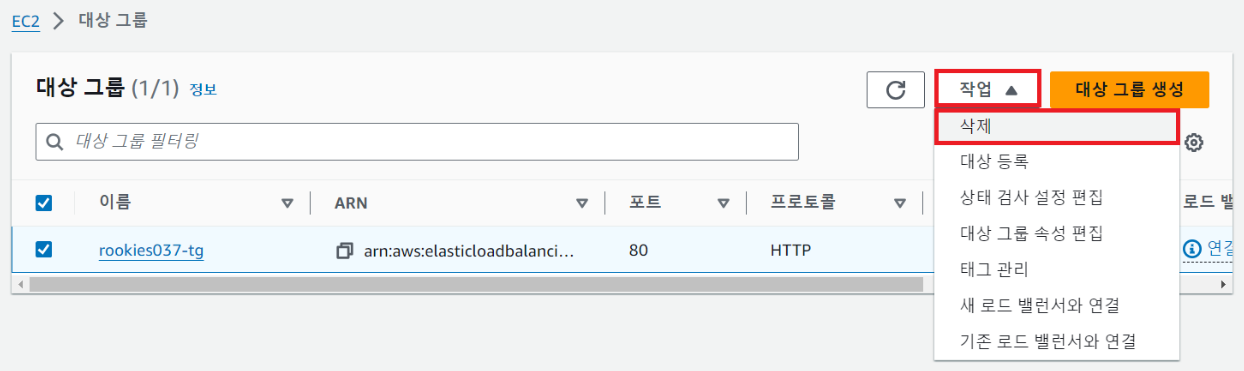
② 대상 그룹 삭제
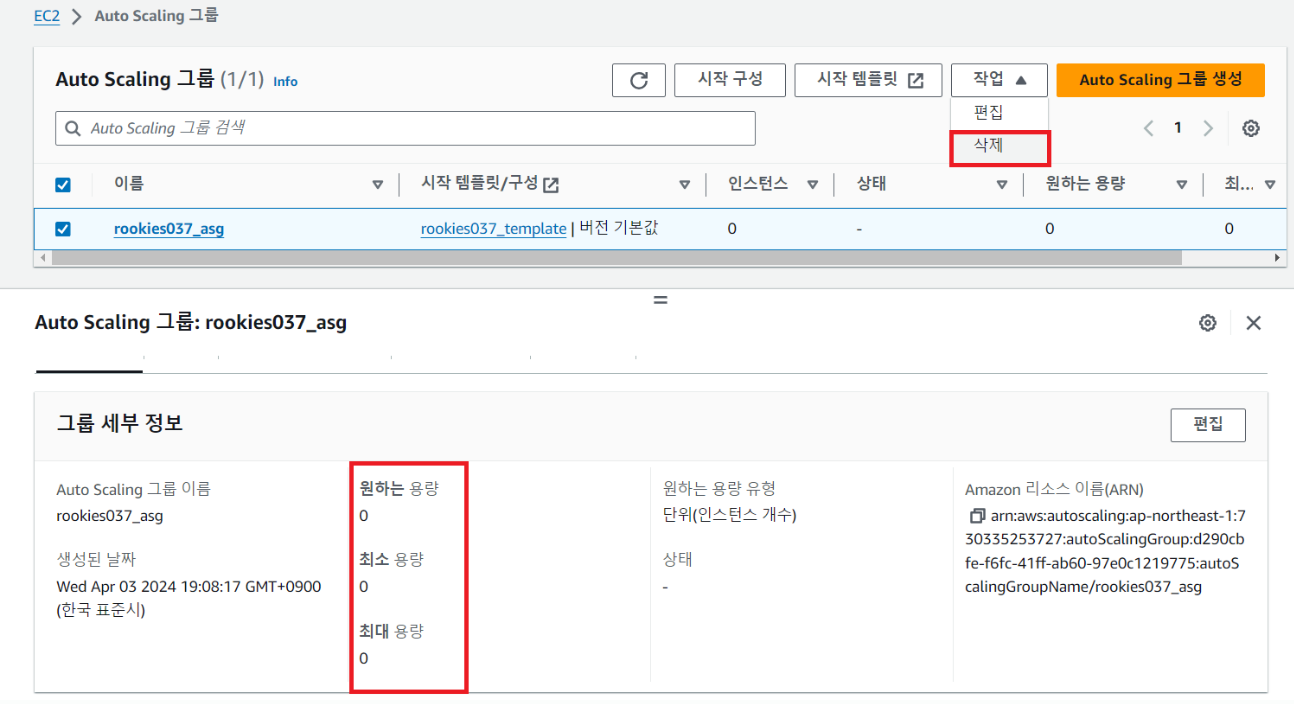
③ 오토 스케일링 그룹 크기 조정 후 오토 스케일링 그룹 삭제
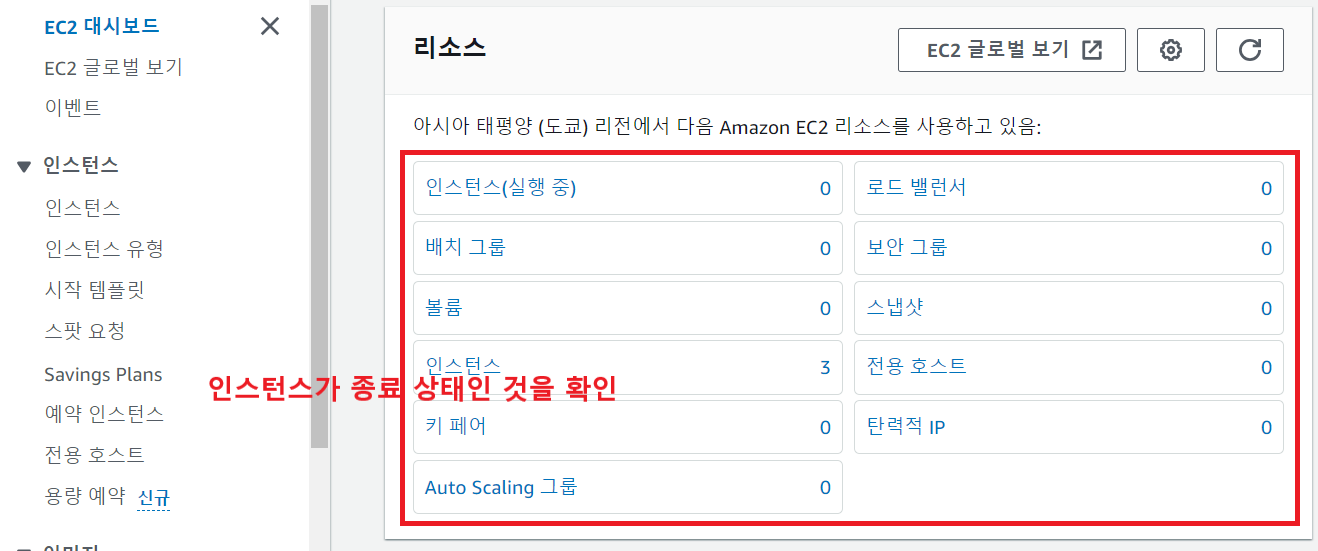
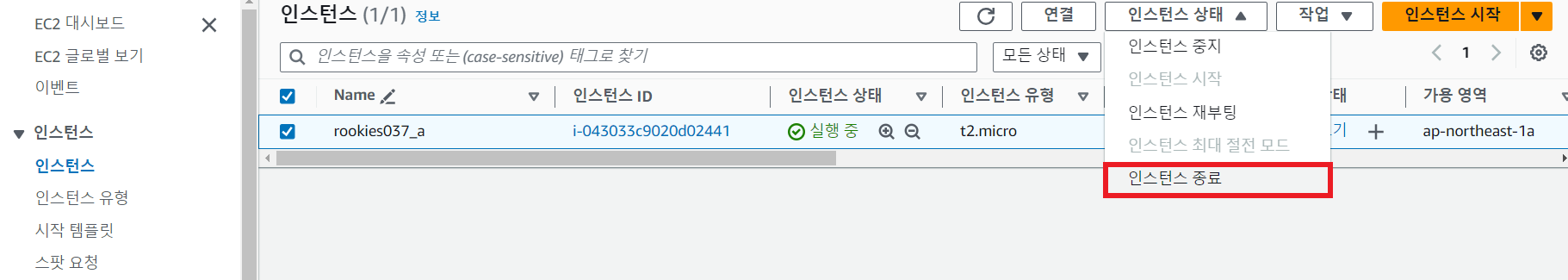
④ 모든 인스턴스 종료 확인
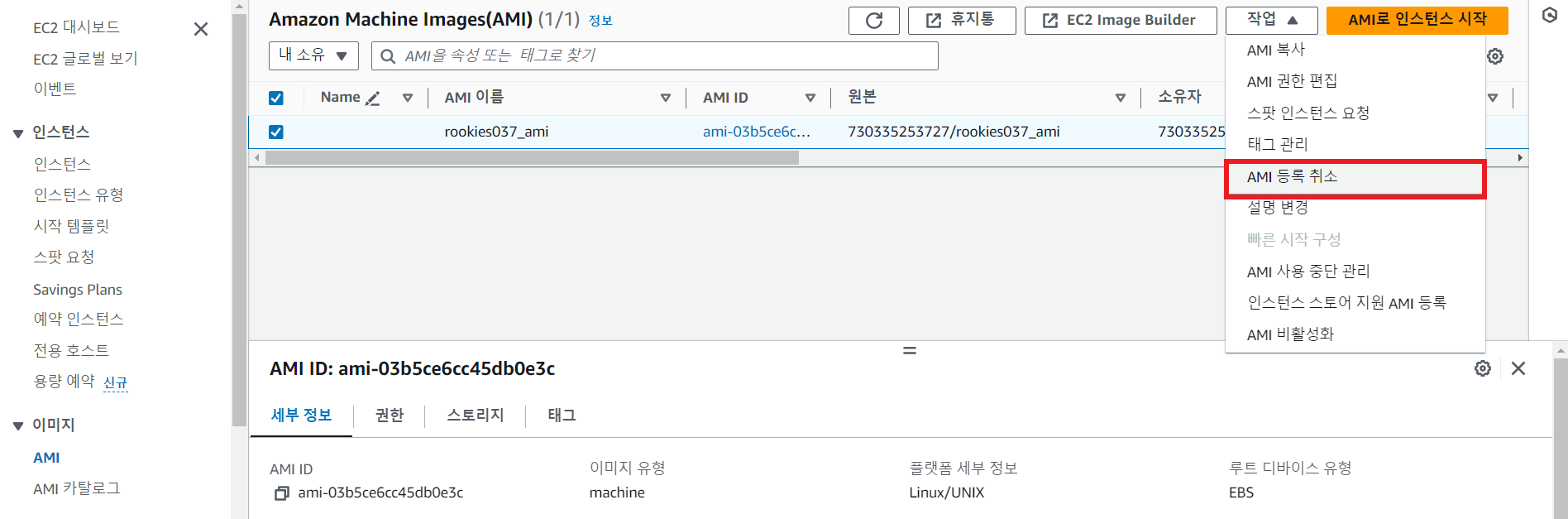
⑤ AMI 삭제
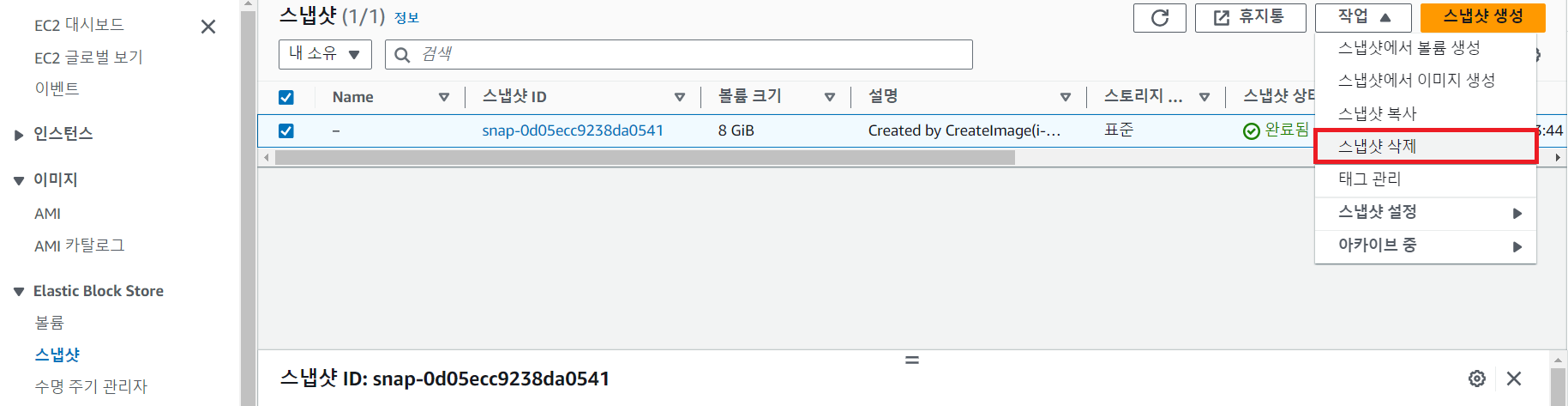
⑥ 스냅샷 삭제
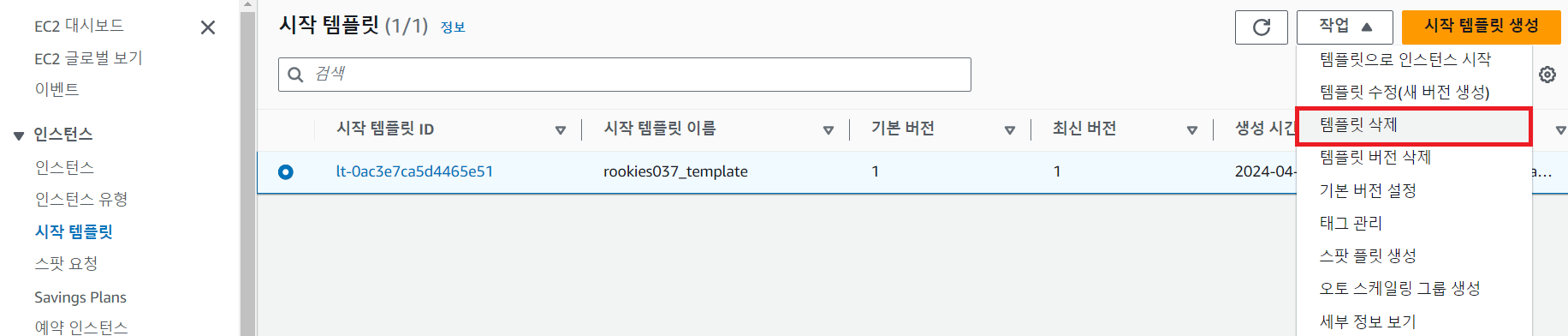
⑦ 시작 템플릿 삭제
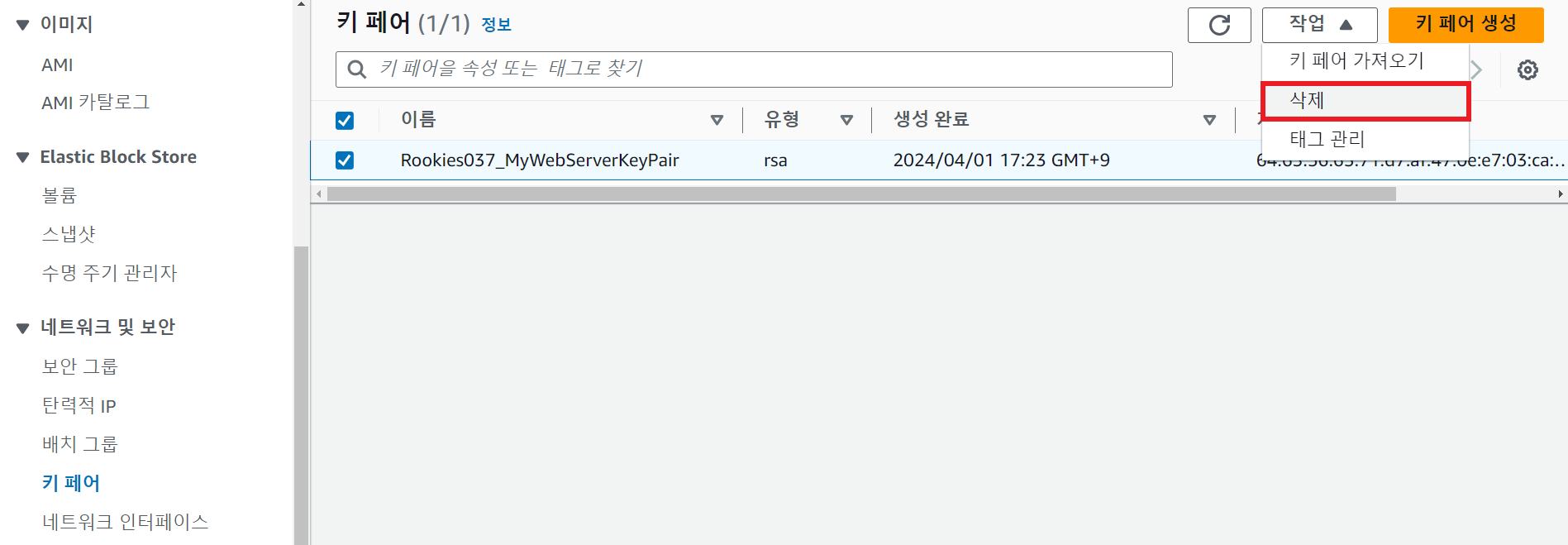
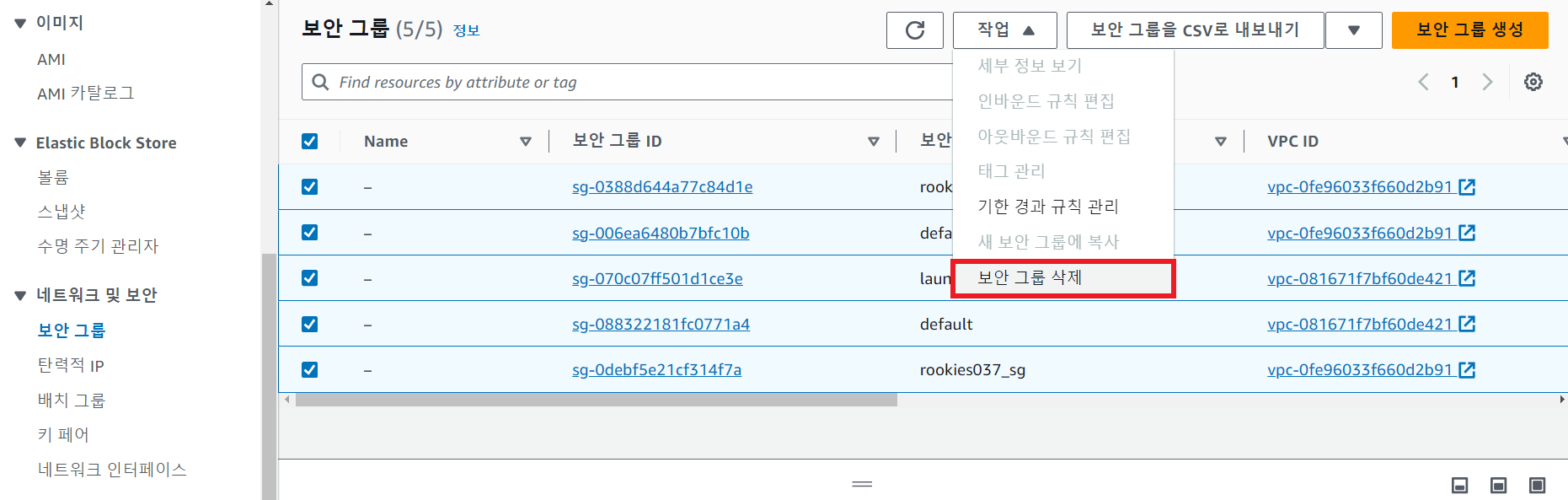
⑧ 키페어, 보안그룹 삭제
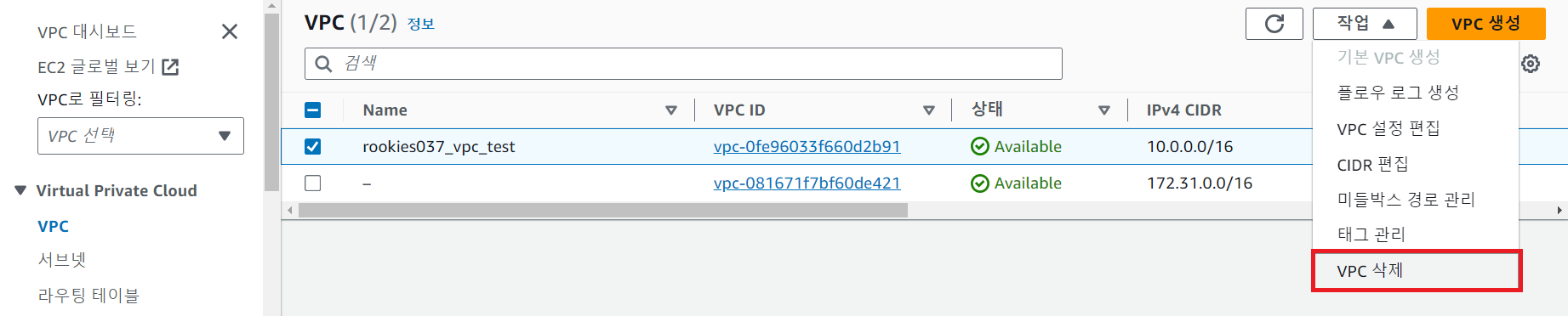
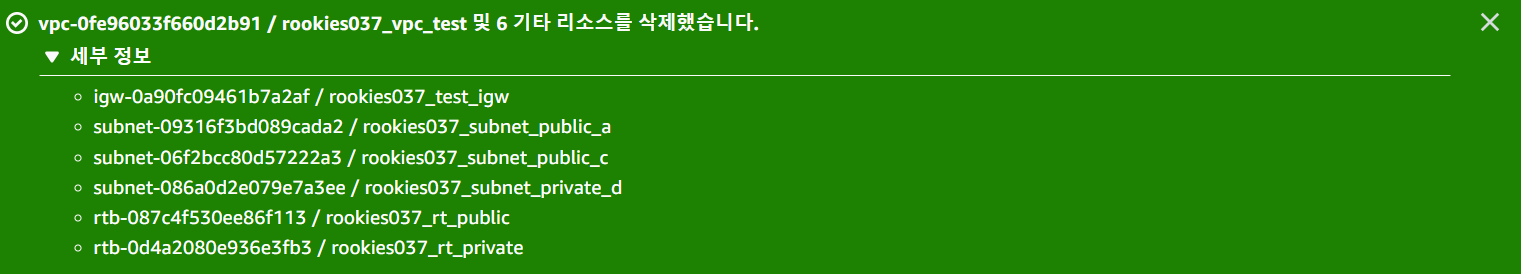
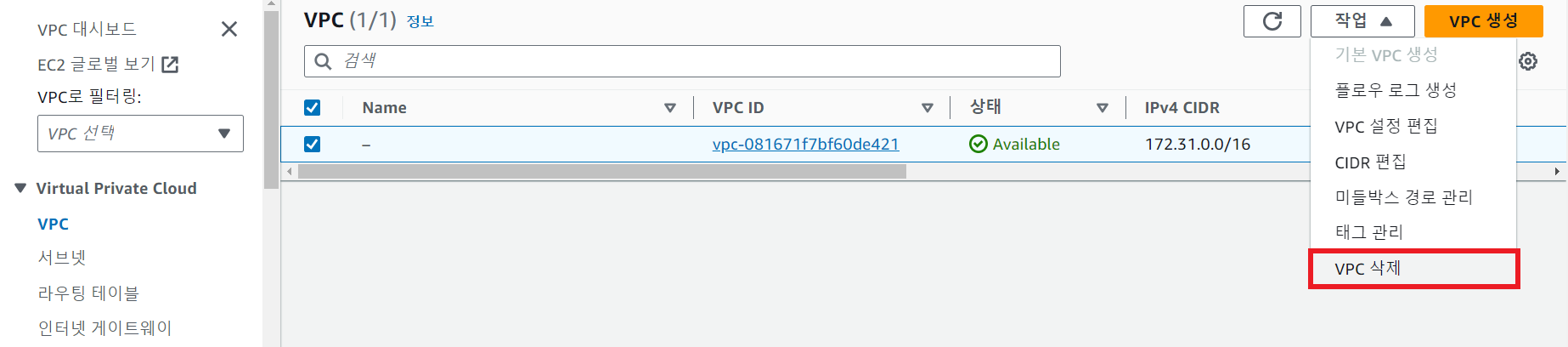
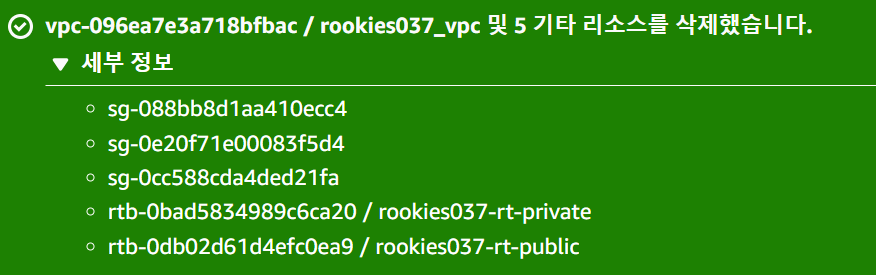
⑨ VPC 삭제 (개별적으로 삭제)

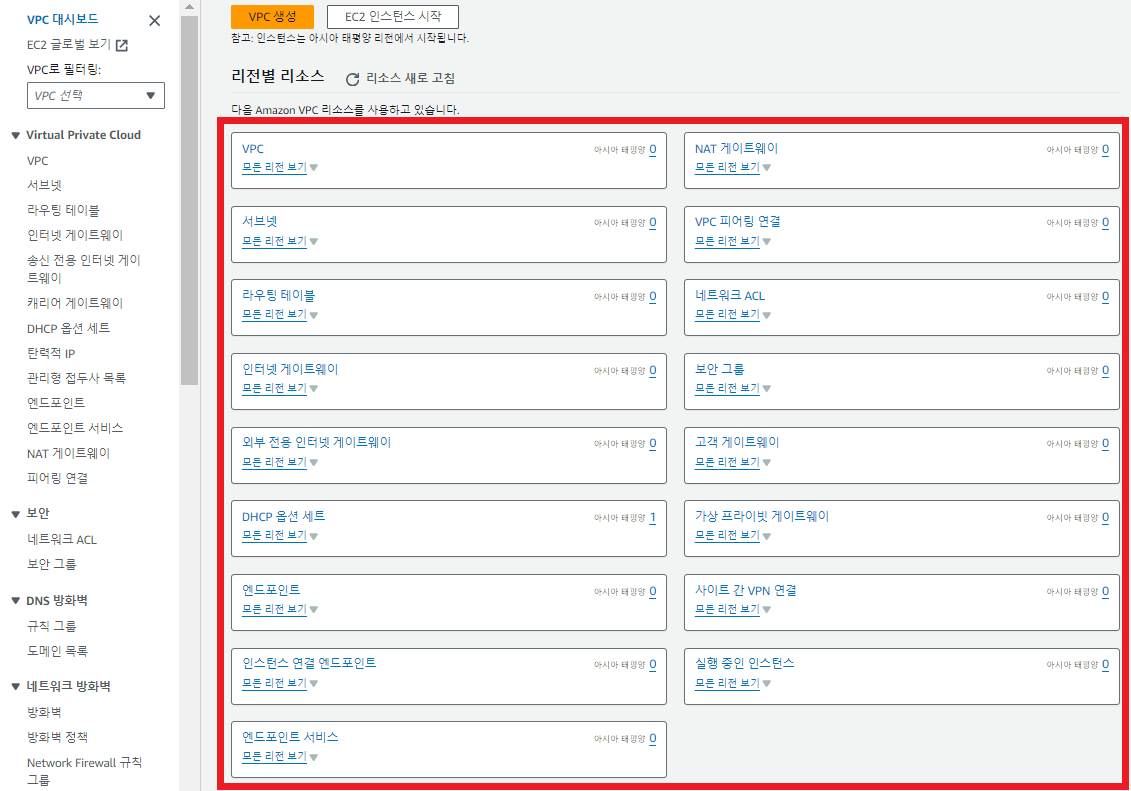
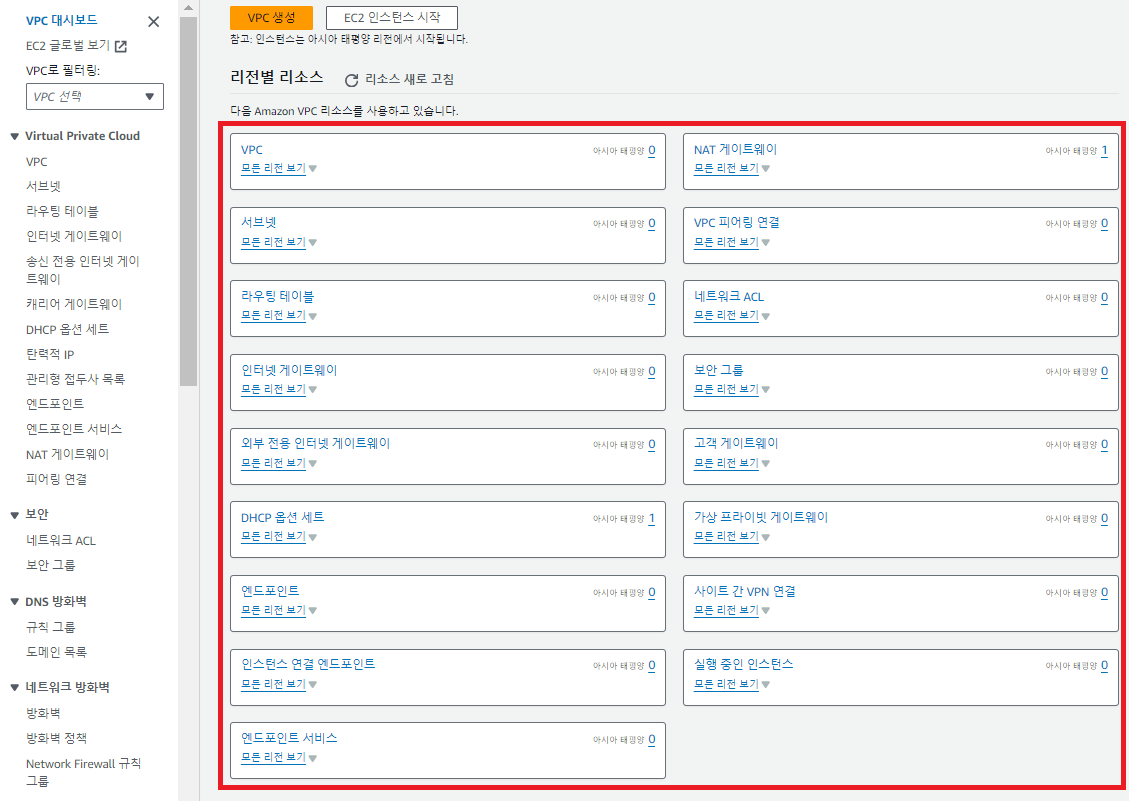
⑩ VPC 대시보드 확인
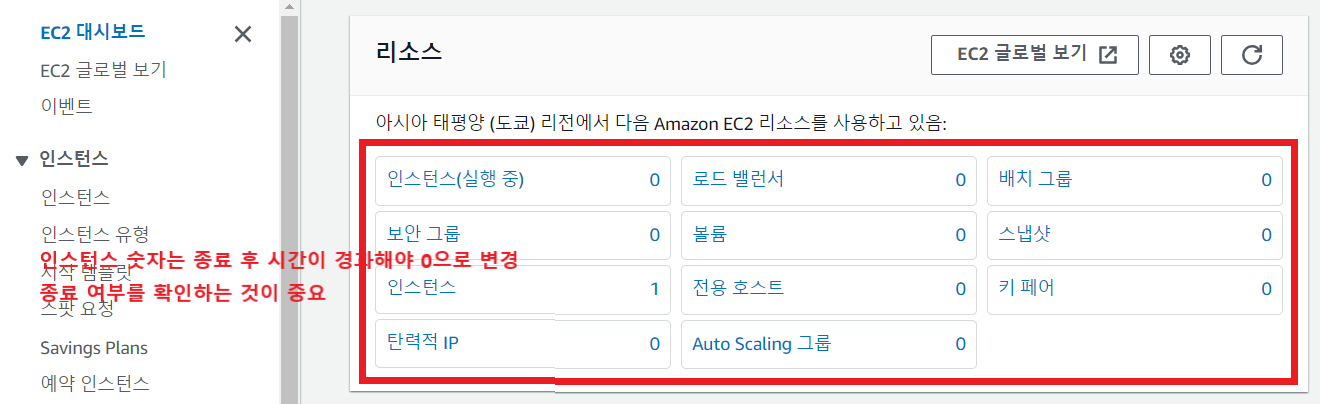
⑪ EC2 대시보드 확인
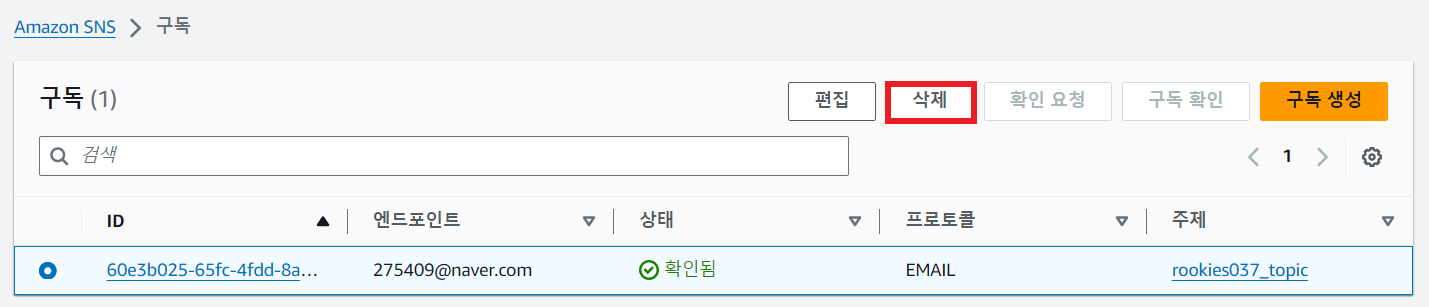
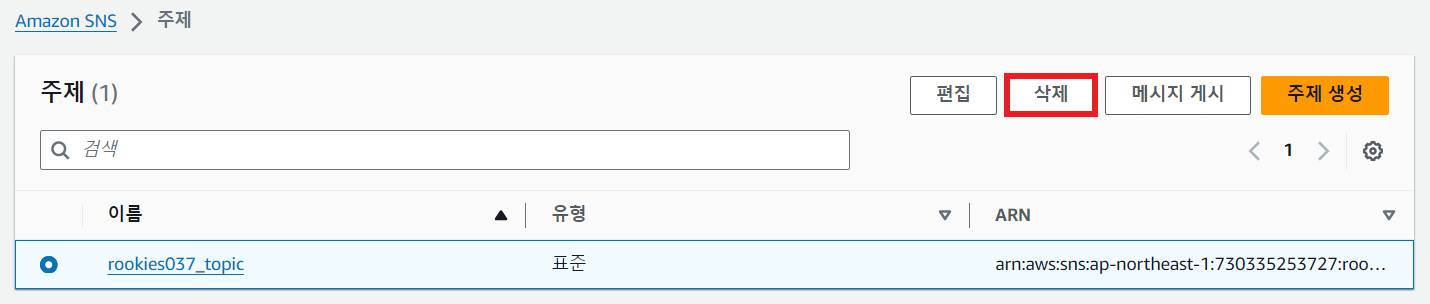
⑫ SNS의 구독, 주제 삭제
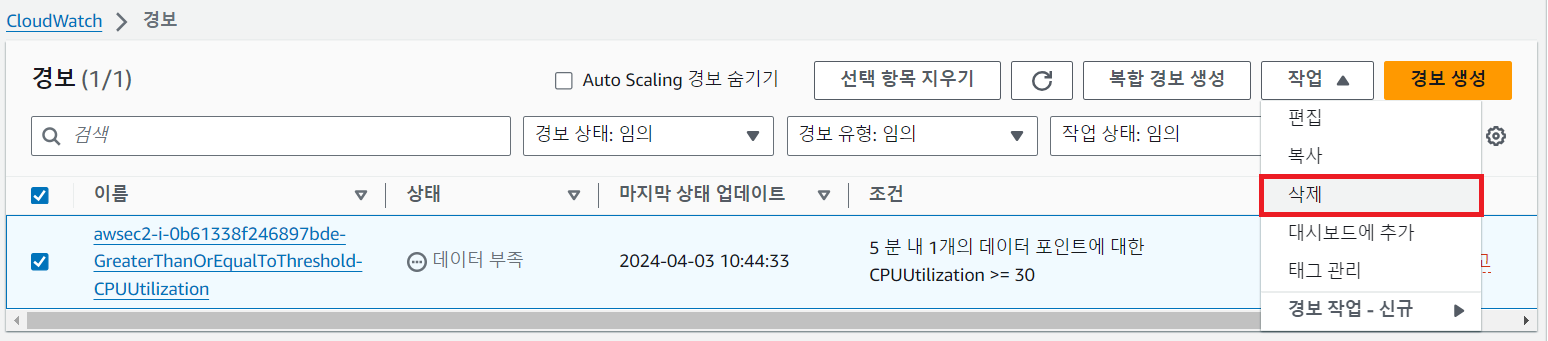
⑬ CloudWatch 경보 삭제
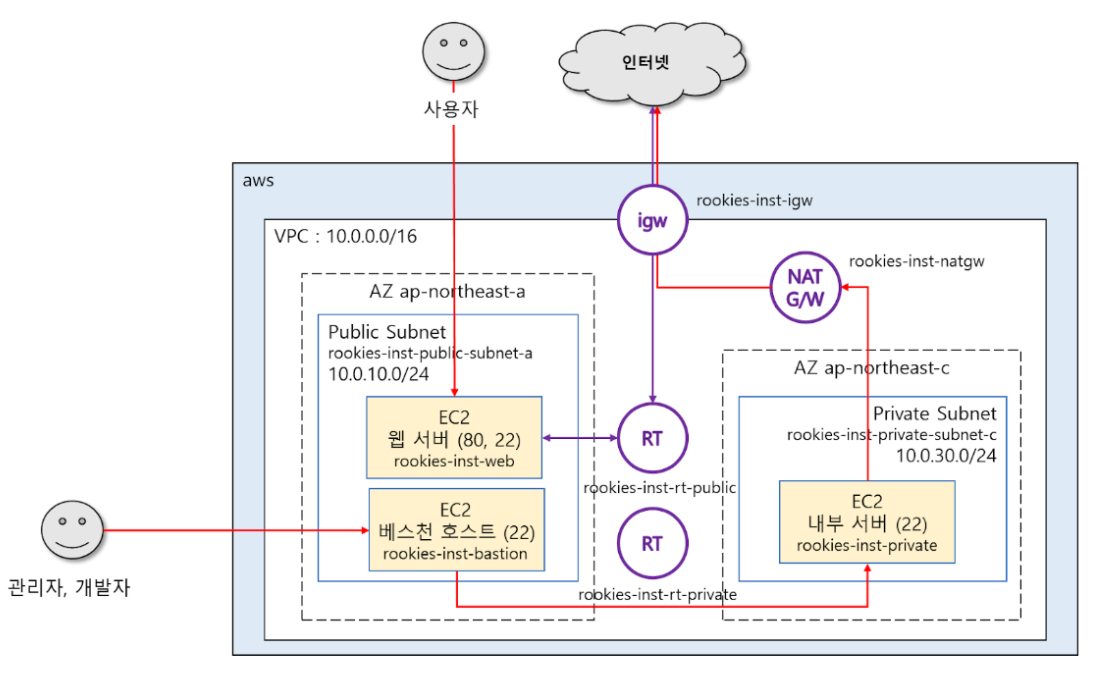
📌 실습
운영 위주
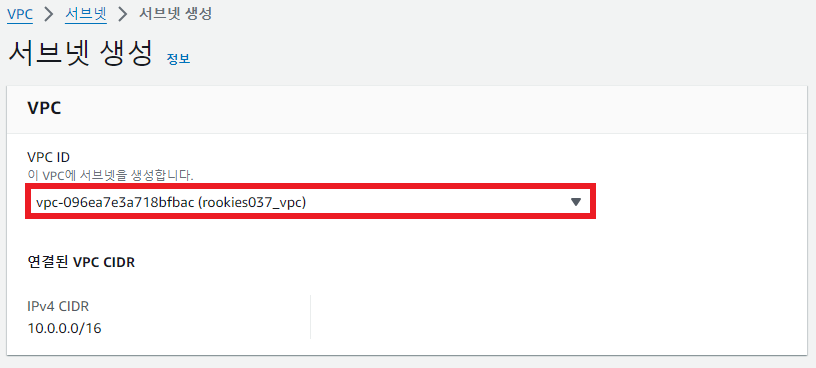
① VPC 생성

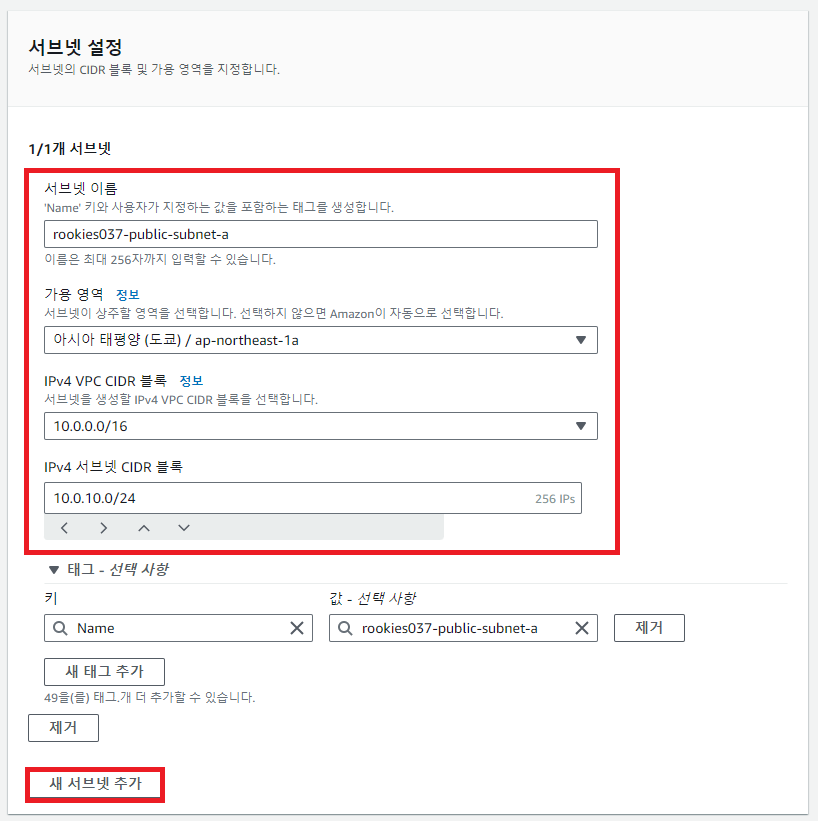
② 서브넷 생성
두 개의 가용영역에 각각 하나의 서브넷 생성
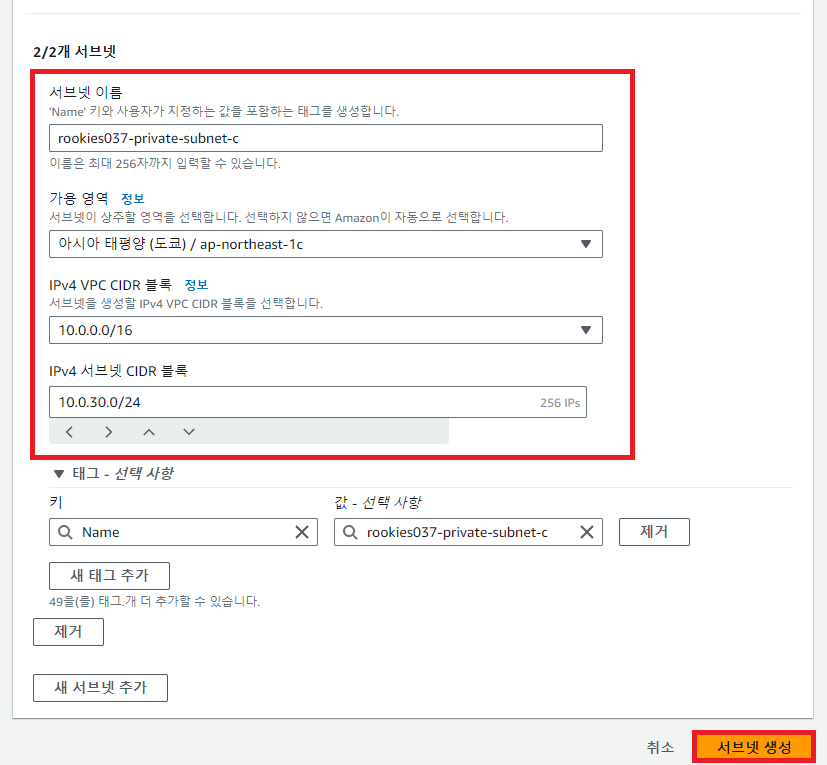
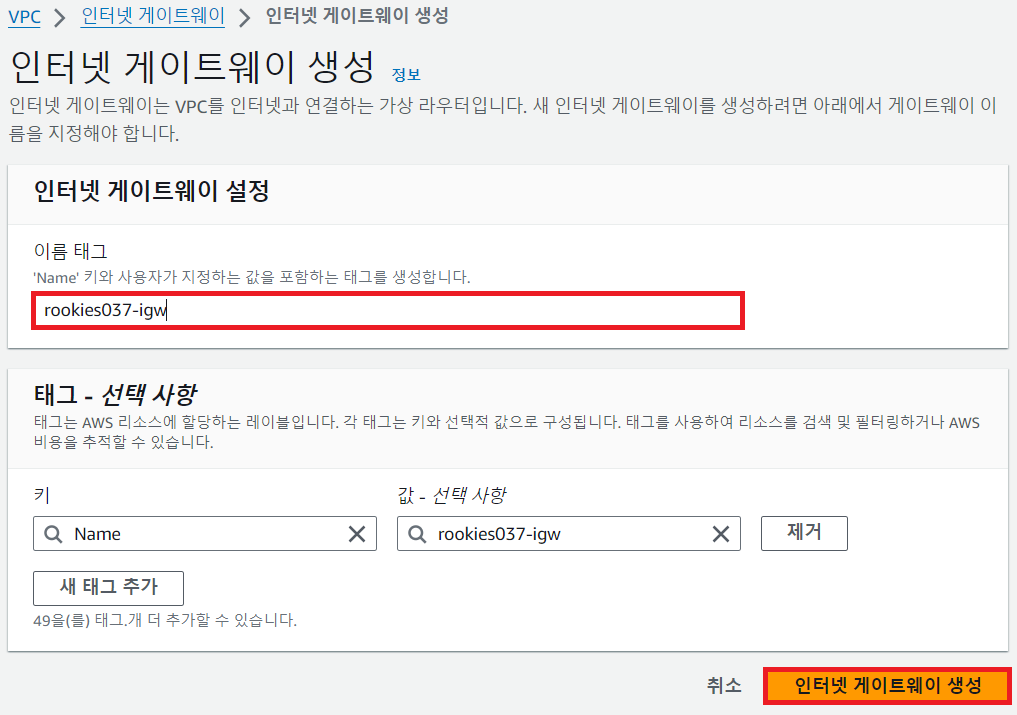
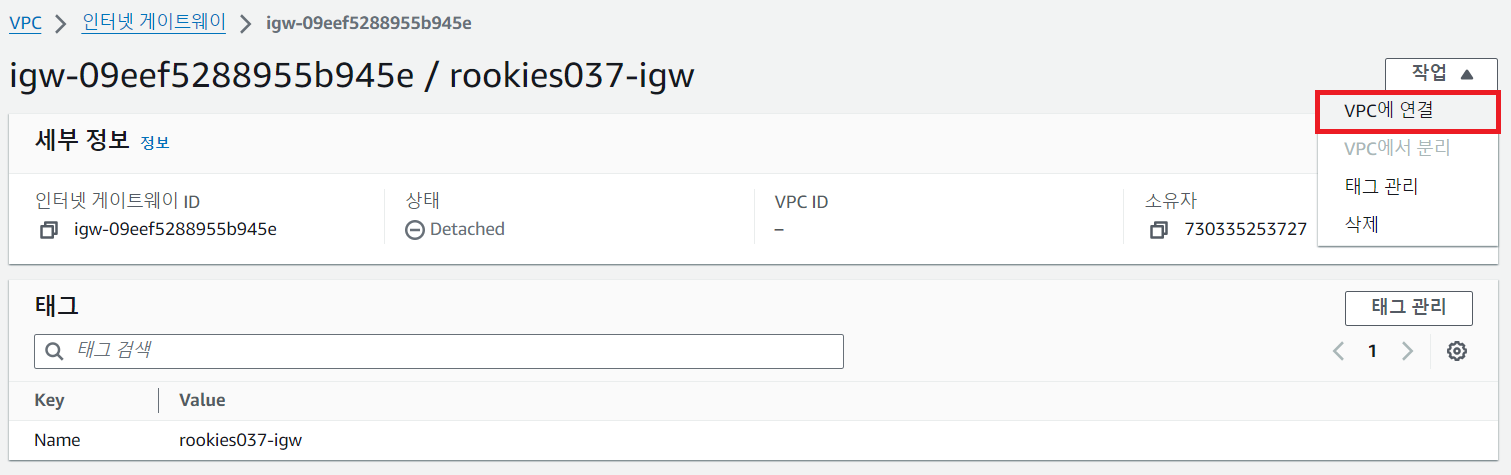
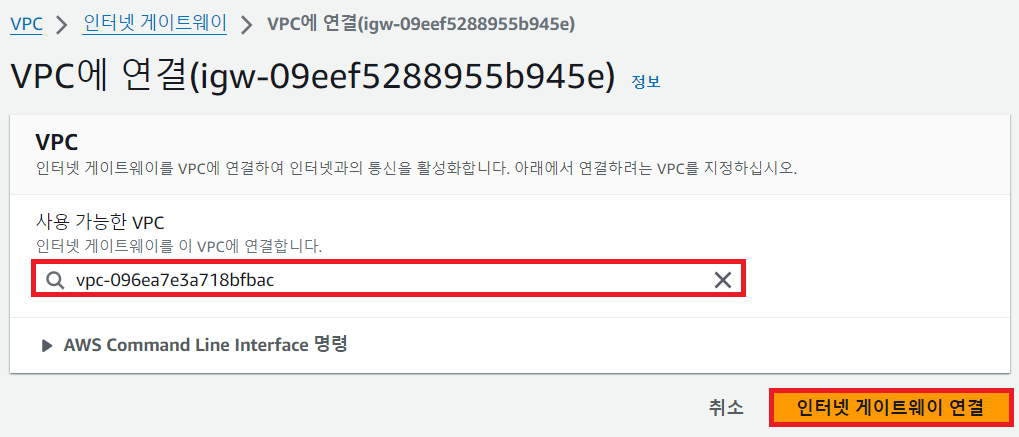
③ 인터넷 게이트웨이 생성 및 VPC 연결
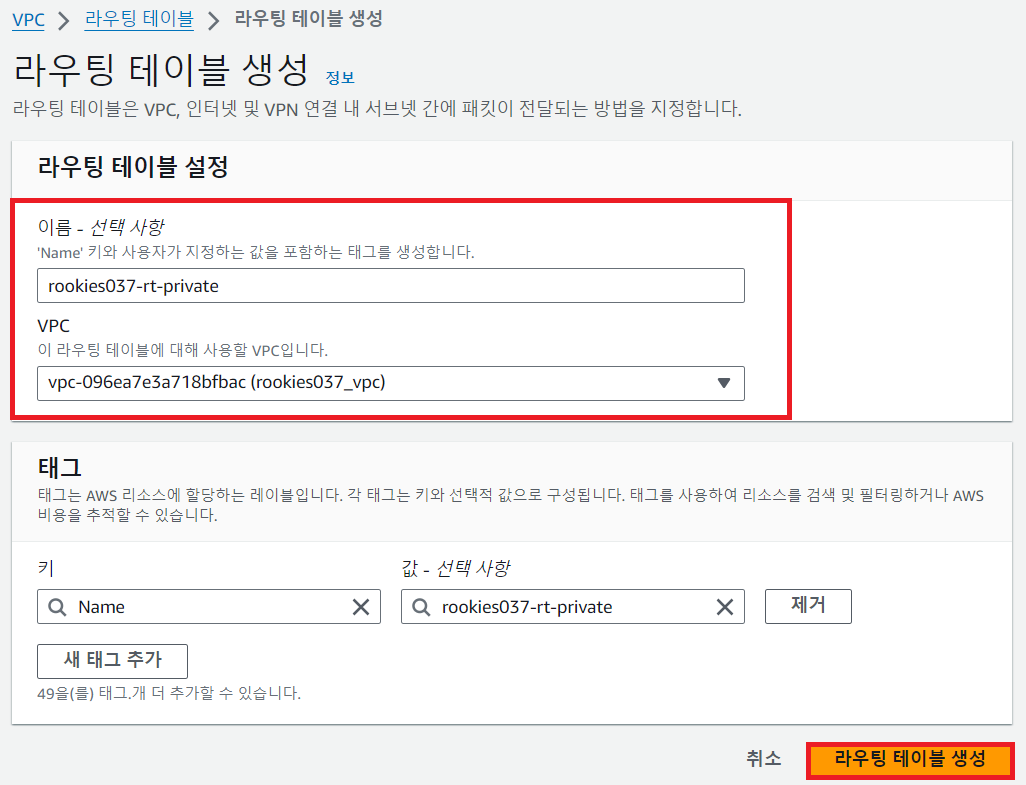
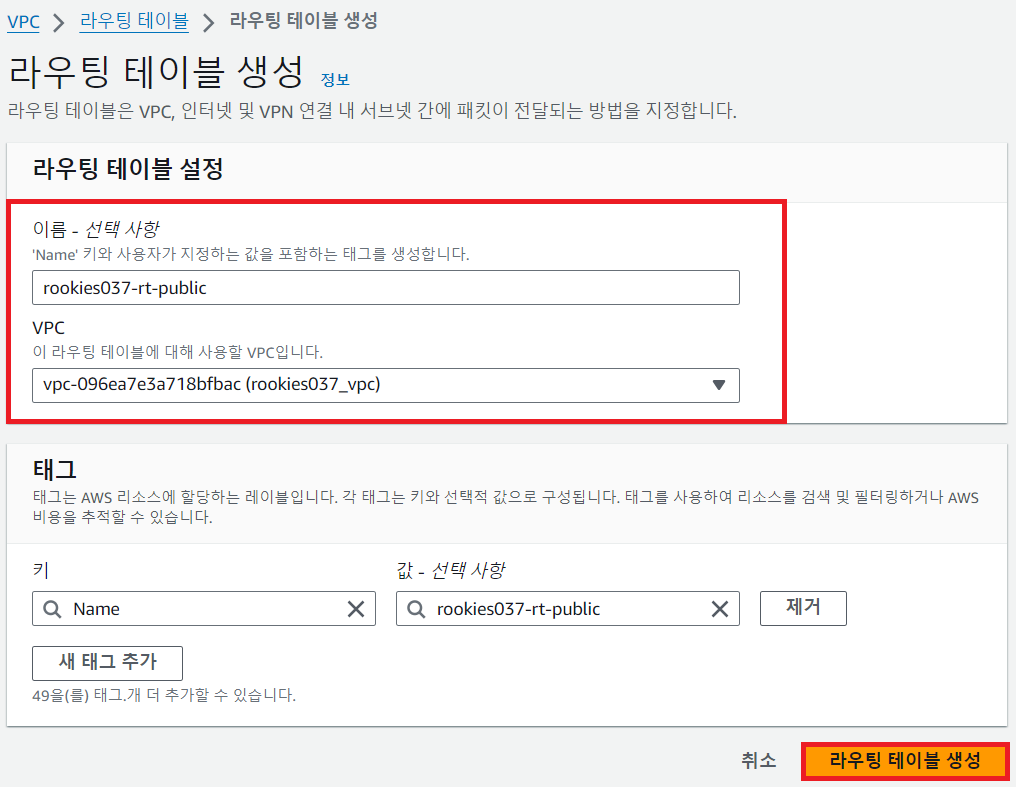
④ 라우팅 테이블 생성
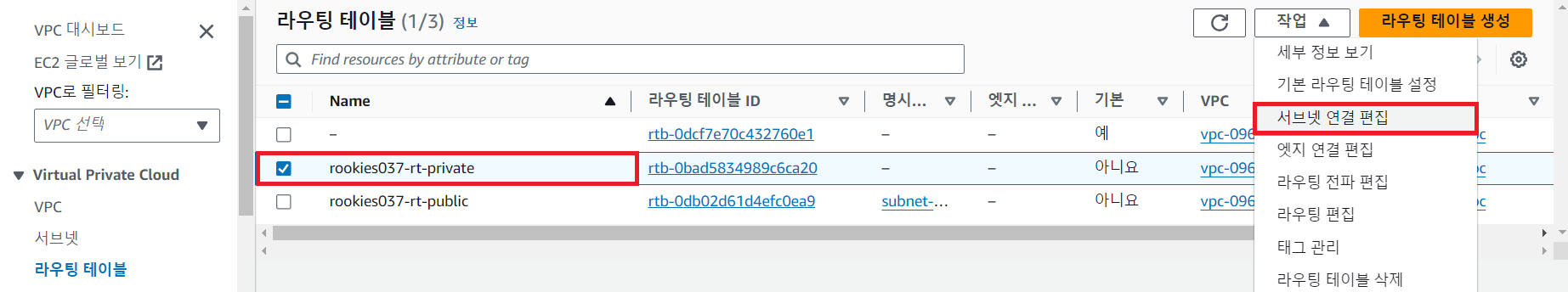
💻 프라이빗 라우팅 테이블

💻 퍼블릭 라우팅 테이블

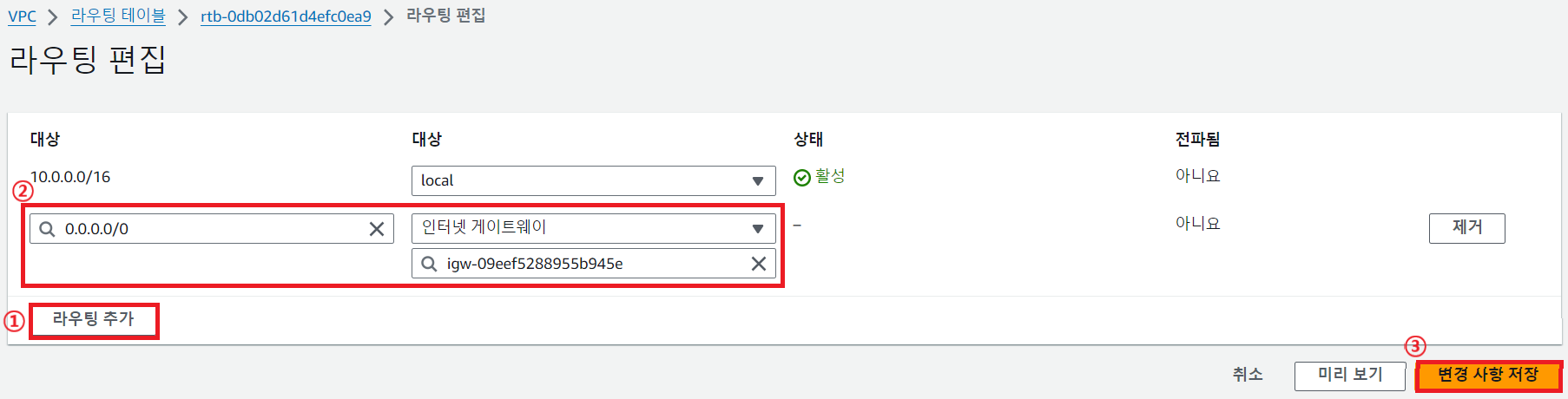
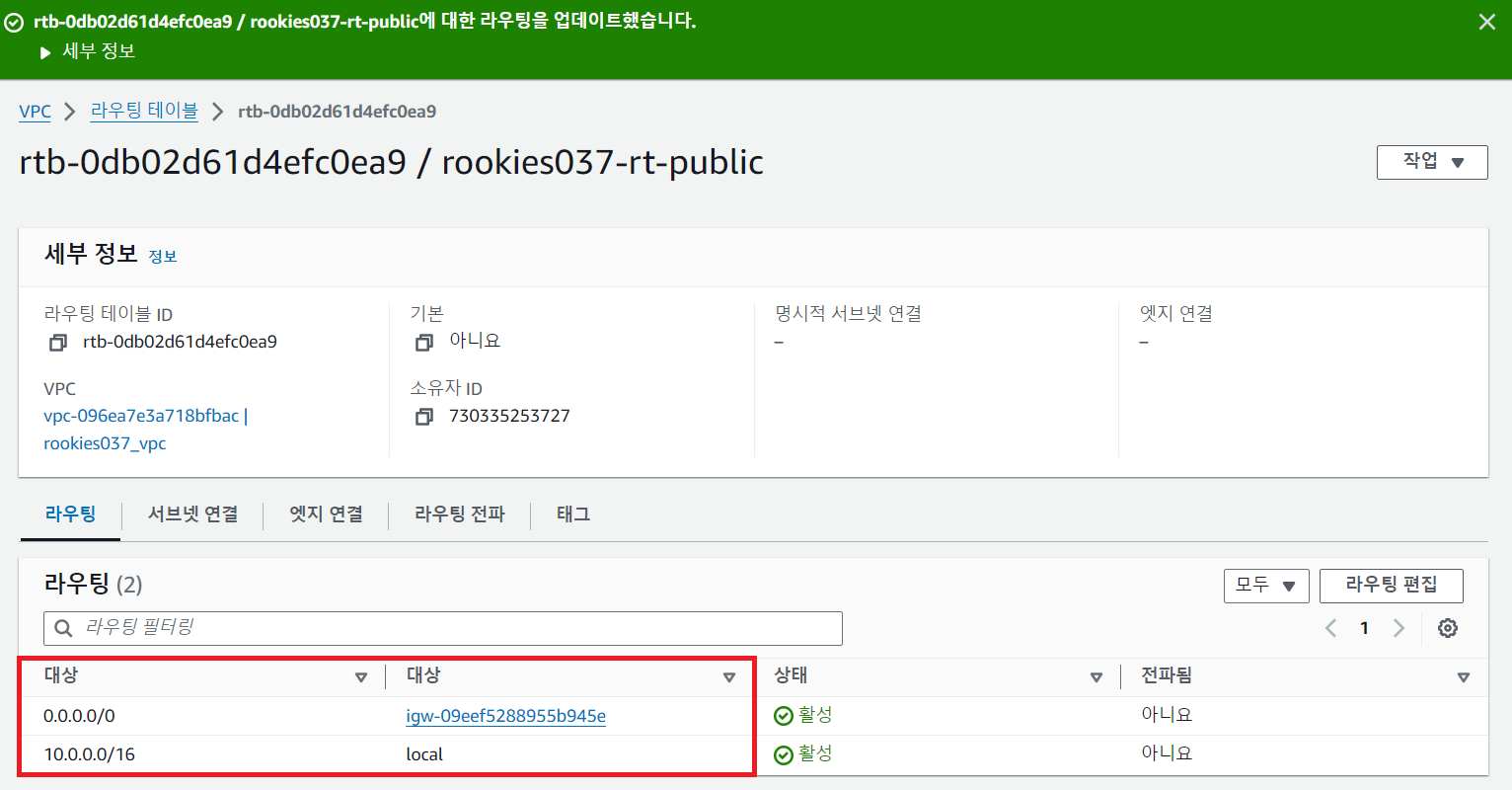
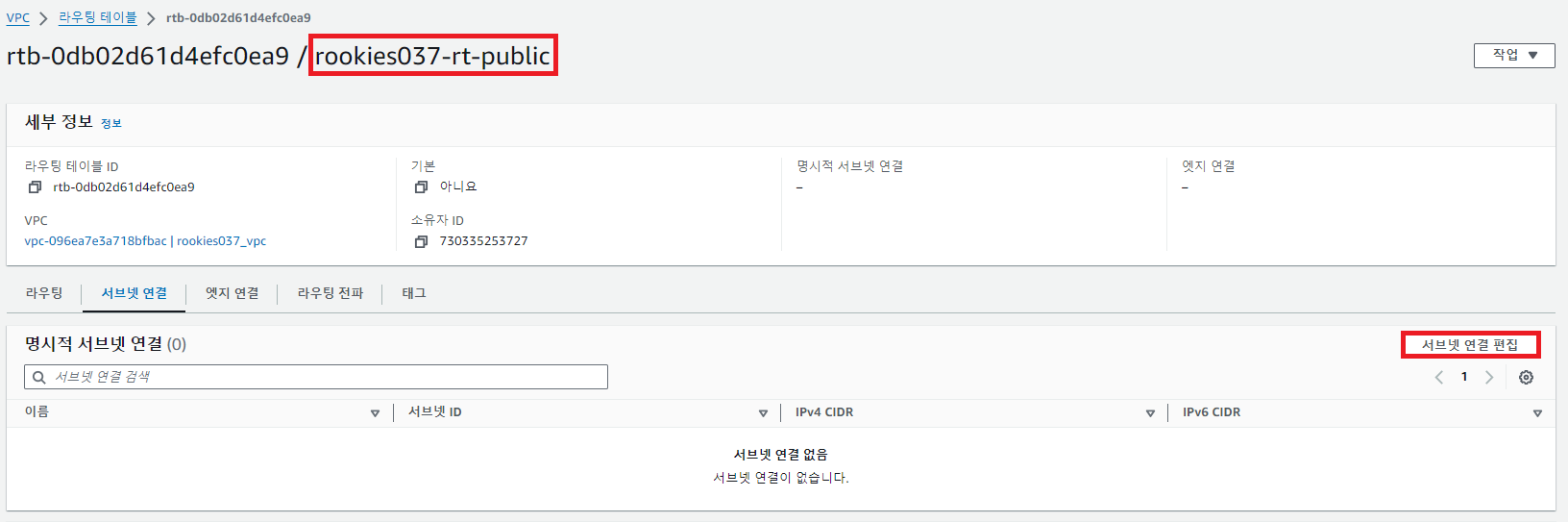
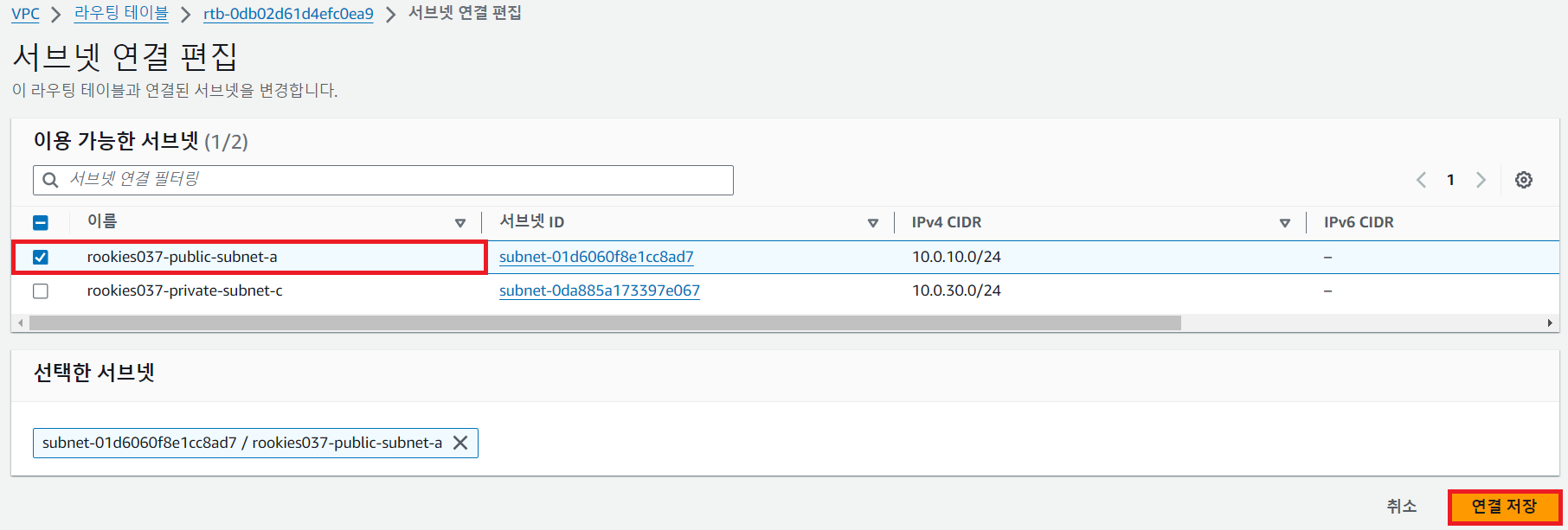
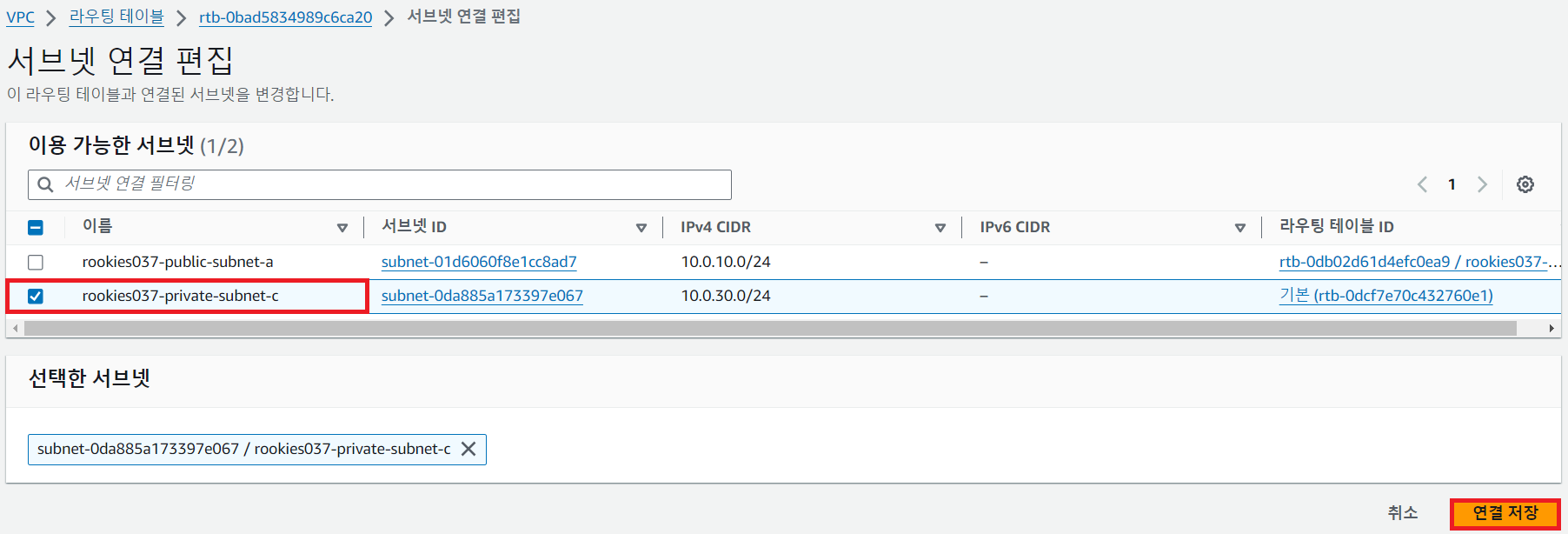
⑤ 라우팅 테이블을 서브넷과 연결
💻 퍼블릭 라우팅 테이블
💻 프라이빗 라우팅 테이블
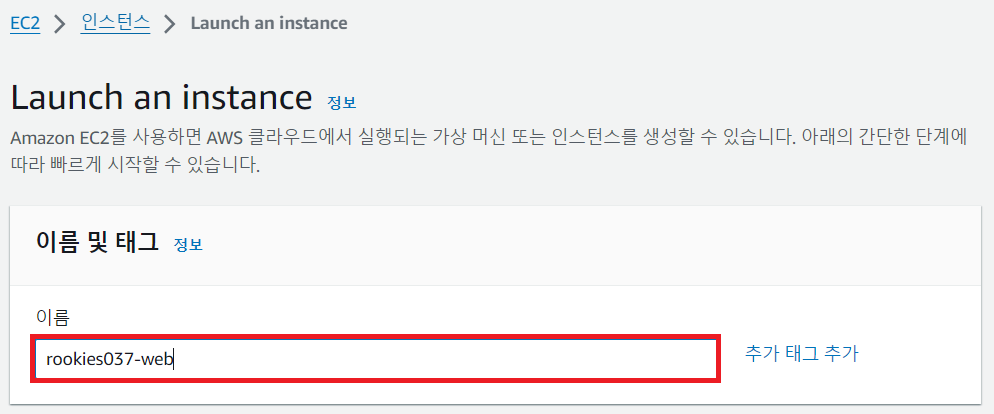
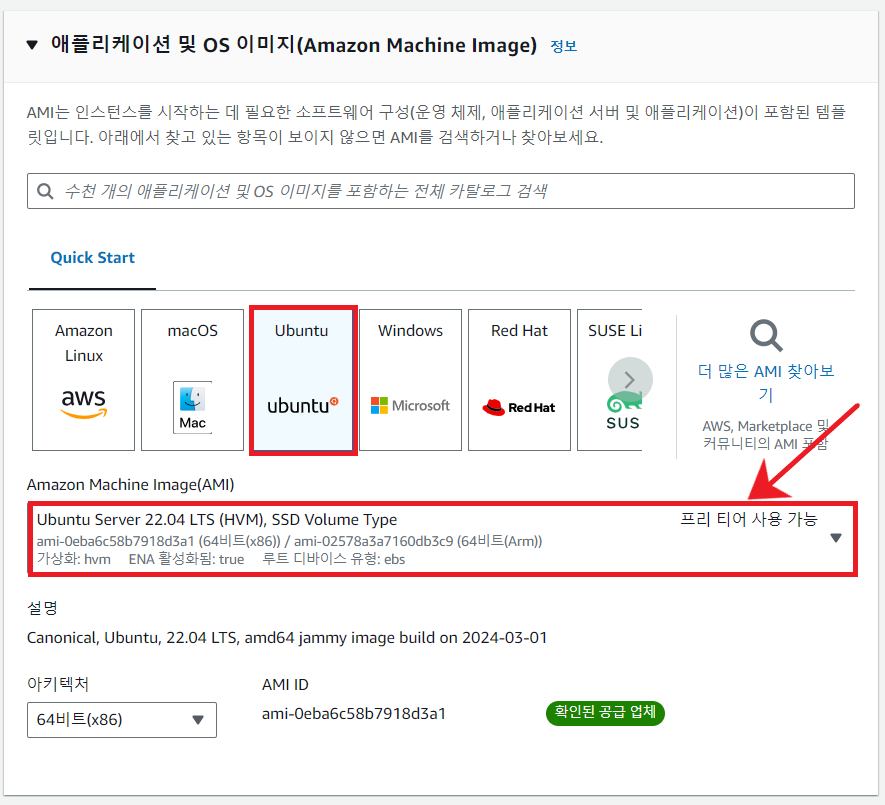
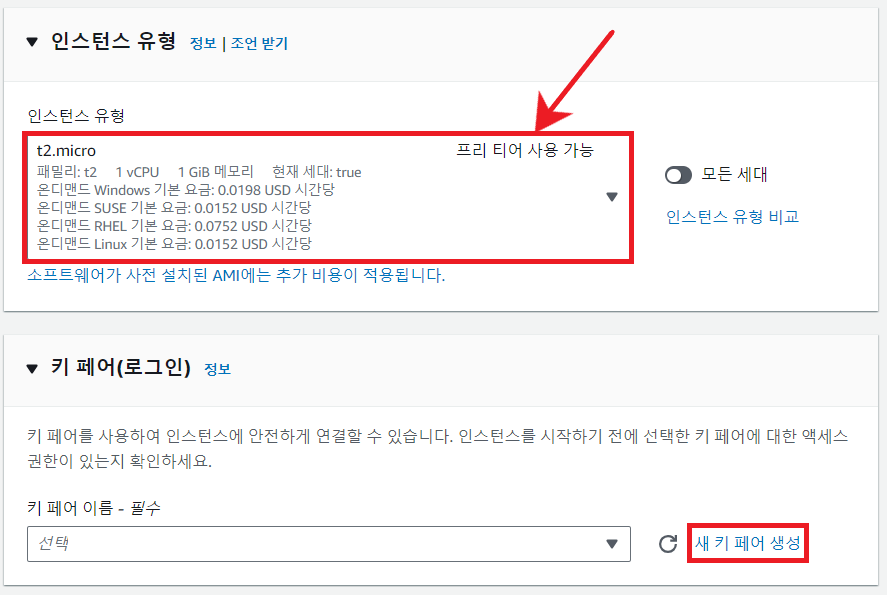
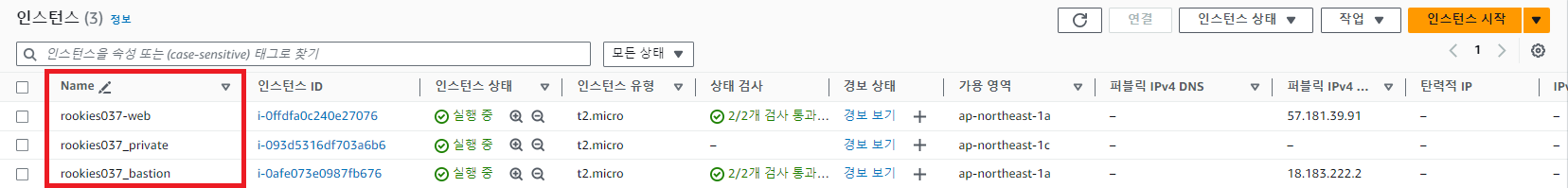
⑥ EC2 생성
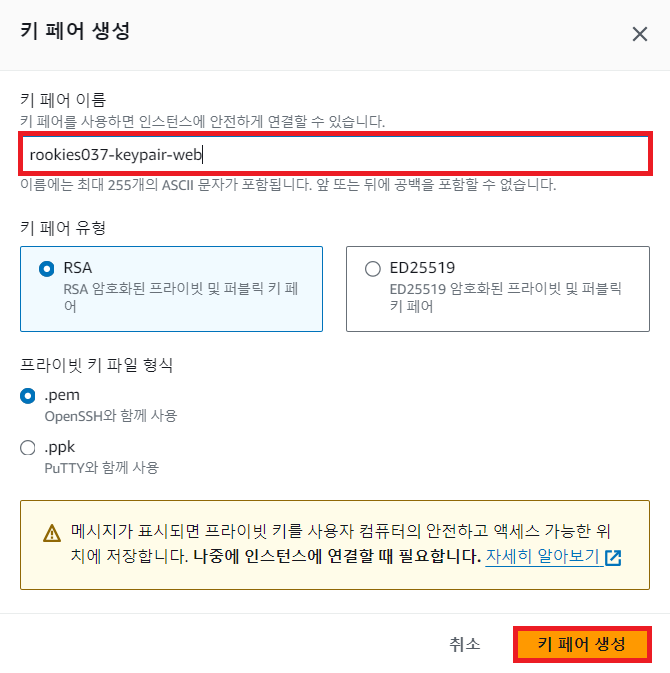
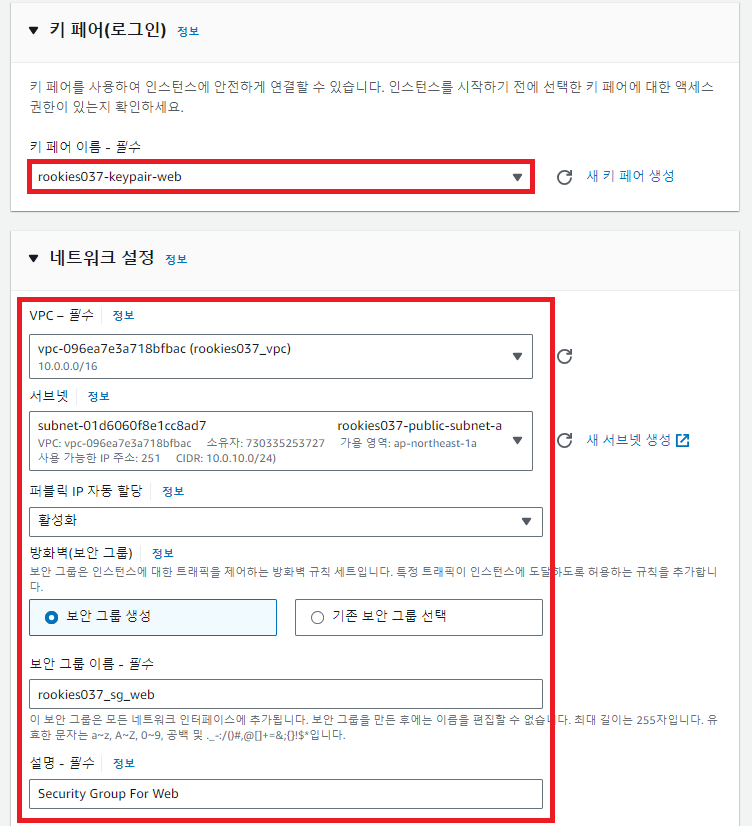
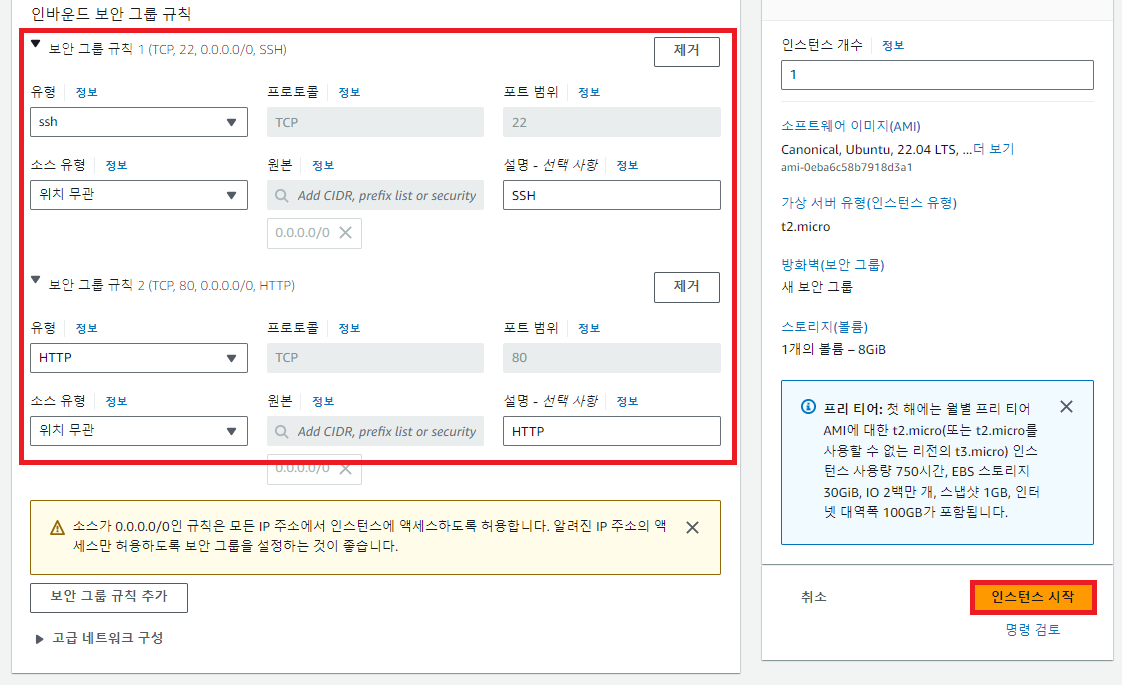
💻 웹 서버
위와 같은 방법으로 인스턴스 2개 더 생성
💻 베스천 호스트
- 인스턴스 이름
rookies037_bastion - 키 페어 이름
rookies037_keypair_bastion - 보안 그룹 이름
rookies037_sg_bastion(22번 포트만 허용)
💻 내부 서버
private subnet에 위치하고 퍼블릭 IP 자동 할당 선택 X
- 인스턴스 이름
rookies037_private - 키 페어 이름
rookies037_keypair_private - 보안 그룹 이름
rookie037_sg_private(22번 포트만 허용)
⑦ 웹 서버에 SSH 접속해서 아파치 설치
cmd에서 키 페어를 내려받은 폴더로 이동
C:\Users\r2com> cd d:\aws
d:\aws> dir
D 드라이브의 볼륨: 새 볼륨
볼륨 일련 번호: AE30-D2D6
d:\aws 디렉터리
2024-04-04 오후 02:47 <DIR> .
2024-04-04 오후 02:47 <DIR> ..
2024-04-04 오후 01:15 1,674 rookies037-keypair-web.pem
2024-04-04 오후 01:25 1,678 rookies037_keypair_bastion.pem
2024-04-04 오후 01:28 1,678 rookies037_keypair_private.pem
3개 파일 5,030 바이트
2개 디렉터리 83,785,228,288 바이트 남음
# ssh -i 키파일 사용자@서버주소
d:\aws>ssh -i rookies037-keypair-web.pem ubuntu@57.181.39.91
The authenticity of host '57.181.39.91 (57.181.39.91)' can't be established.
ECDSA key fingerprint is SHA256:1LPnZuhzn9l604Ga8X397IkdAXxb9ku2ch6O0VS448o.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '57.181.39.91' (ECDSA) to the list of known hosts.
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: UNPROTECTED PRIVATE KEY FILE! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
Permissions for 'rookies037-keypair-web.pem' are too open.
It is required that your private key files are NOT accessible by others.
This private key will be ignored.
Load key "rookies037-keypair-web.pem": bad permissions
ubuntu@57.181.39.91: Permission denied (publickey).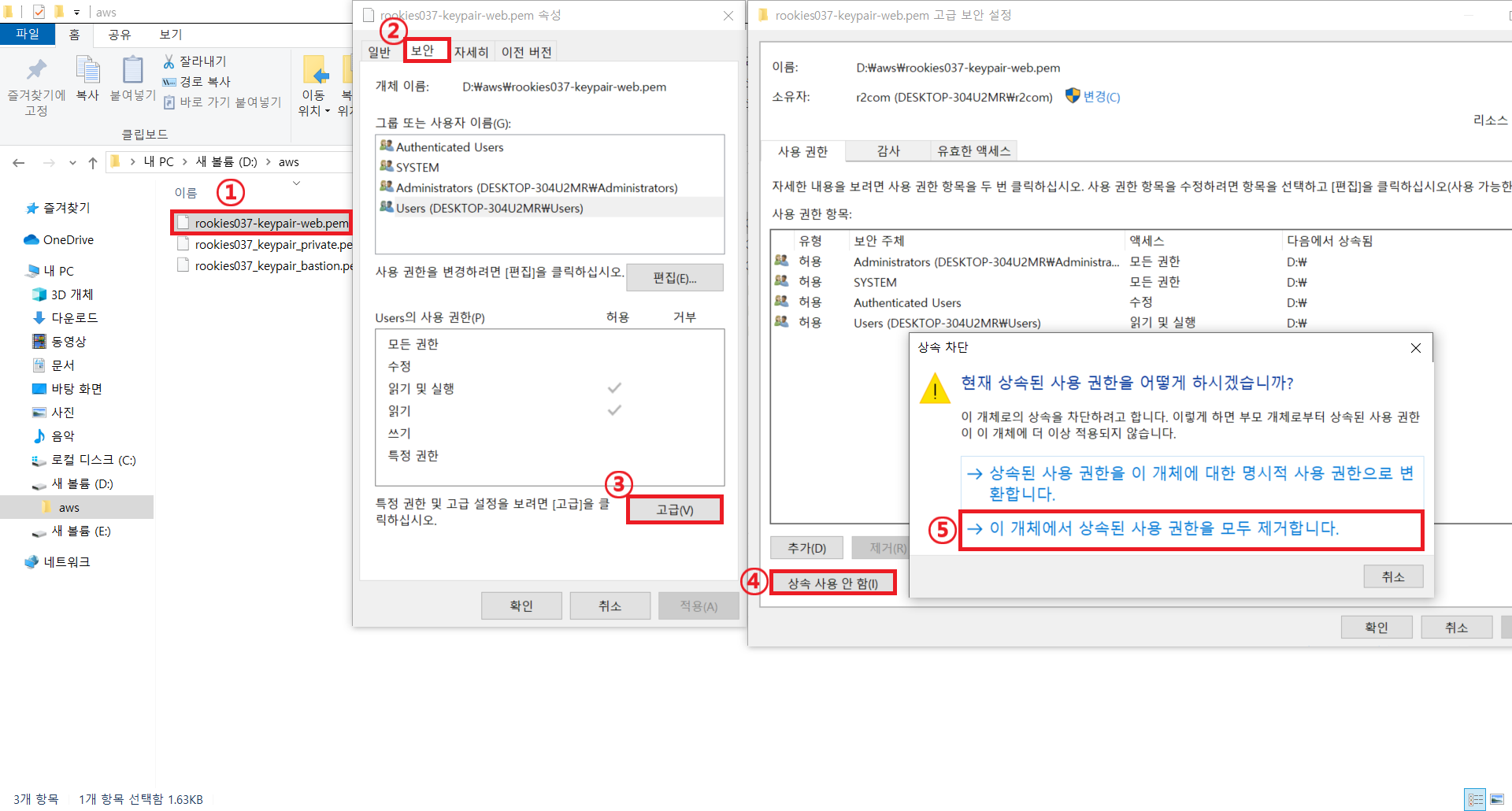
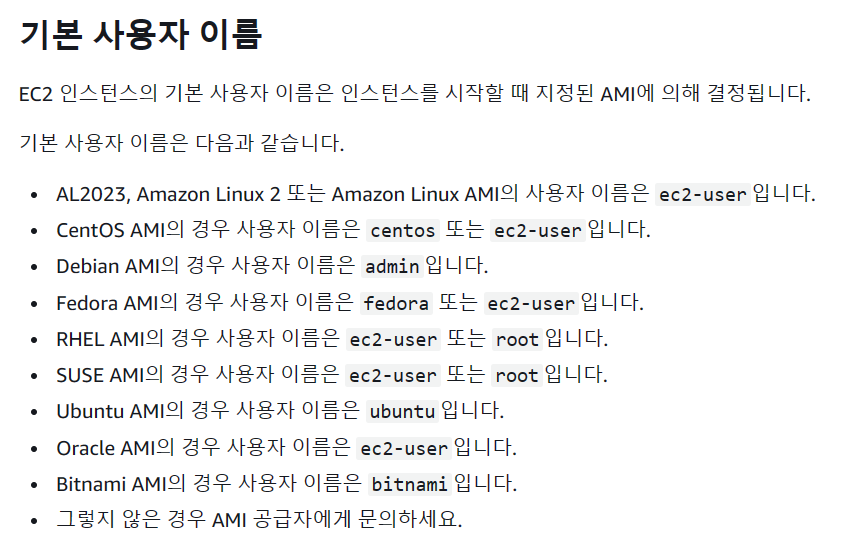
https://docs.aws.amazon.com/ko_kr/AWSEC2/latest/UserGuide/managing-users.html#ami-default-user-names
d:\aws>ssh -i rookies037-keypair-web.pem ubuntu@57.181.39.91
Welcome to Ubuntu 22.04.4 LTS (GNU/Linux 6.5.0-1014-aws x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/pro
System information as of Thu Apr 4 07:14:48 UTC 2024
System load: 0.0 Processes: 98
Usage of /: 20.7% of 7.57GB Users logged in: 1
Memory usage: 20% IPv4 address for eth0: 10.0.10.211
Swap usage: 0%
Expanded Security Maintenance for Applications is not enabled.
0 updates can be applied immediately.
Enable ESM Apps to receive additional future security updates.
See https://ubuntu.com/esm or run: sudo pro status
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Last login: Thu Apr 4 05:32:23 2024 from 219.255.90.59
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
ubuntu@ip-10-0-10-211:~$
ubuntu@ip-10-0-10-211:~$ sudo apt update
ubuntu@ip-10-0-10-211:~$ sudo apt install -y apache2
ubuntu@ip-10-0-10-211:~$ sudo systemctl start apache2
ubuntu@ip-10-0-10-211:~$ sudo systemctl enable apache2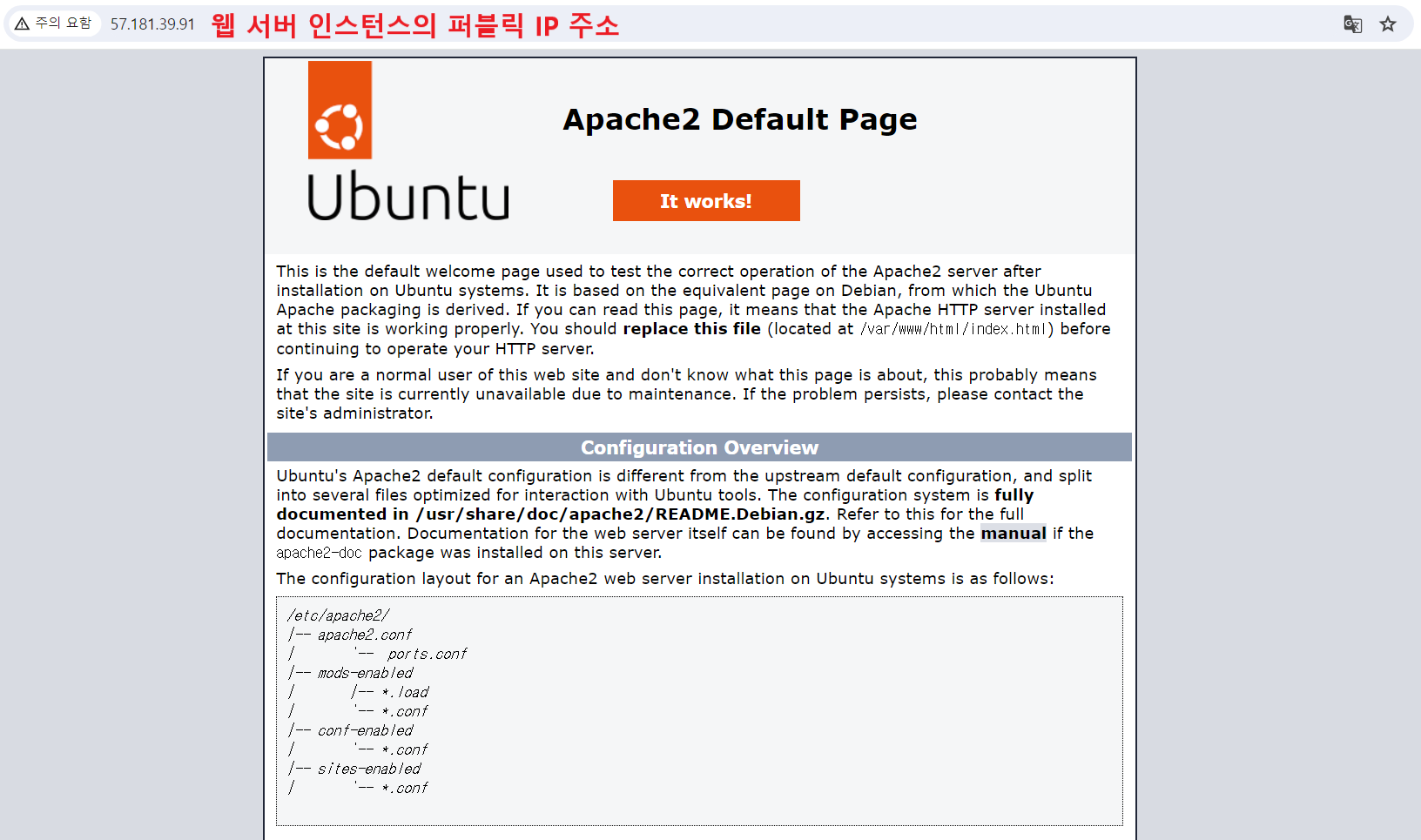
⑧ 베스천 호스트를 이용해서 내부 서버로 SSH 접속
💻 베스천 호스트로 SSH 접속
C:\Users\r2com> d:
d:\aws> dir *.pem
D 드라이브의 볼륨: 새 볼륨
볼륨 일련 번호: AE30-D2D6
d:\aws 디렉터리
2024-04-04 오후 01:15 1,674 rookies037-keypair-web.pem
2024-04-04 오후 01:25 1,678 rookies037_keypair_bastion.pem
2024-04-04 오후 01:28 1,678 rookies037_keypair_private.pem
3개 파일 5,030 바이트
0개 디렉터리 83,785,228,288 바이트 남음
d:\aws>ssh -i rookies037_keypair_bastion.pem ubuntu@18.183.222.2
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ~~~~~~~~~~~~~
# 베스천 호스트의 개인키 및 퍼블릭 IP 사용
The authenticity of host '18.183.222.2 (18.183.222.2)' can't be established.
ECDSA key fingerprint is SHA256:ImGCmtuUnVz+y8TT5994W210Y6qzL11Tdk9MT3Ya4ks.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '18.183.222.2' (ECDSA) to the list of known hosts.
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: UNPROTECTED PRIVATE KEY FILE! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
Permissions for 'rookies037_keypair_bastion.pem' are too open.
It is required that your private key files are NOT accessible by others.
This private key will be ignored.
Load key "rookies037_keypair_bastion.pem": bad permissions
ubuntu@18.183.222.2: Permission denied (publickey).
d:\aws>whoami
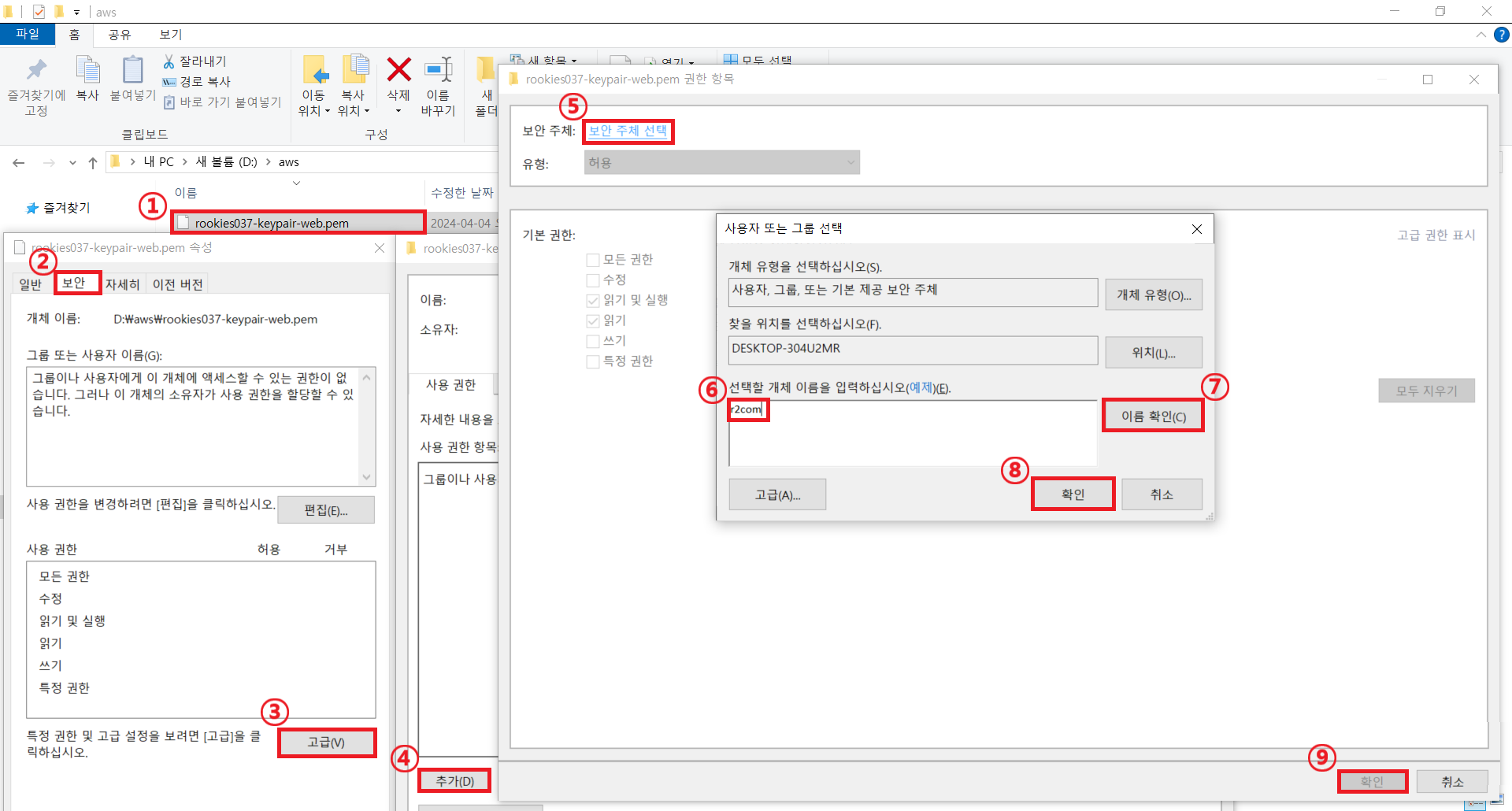
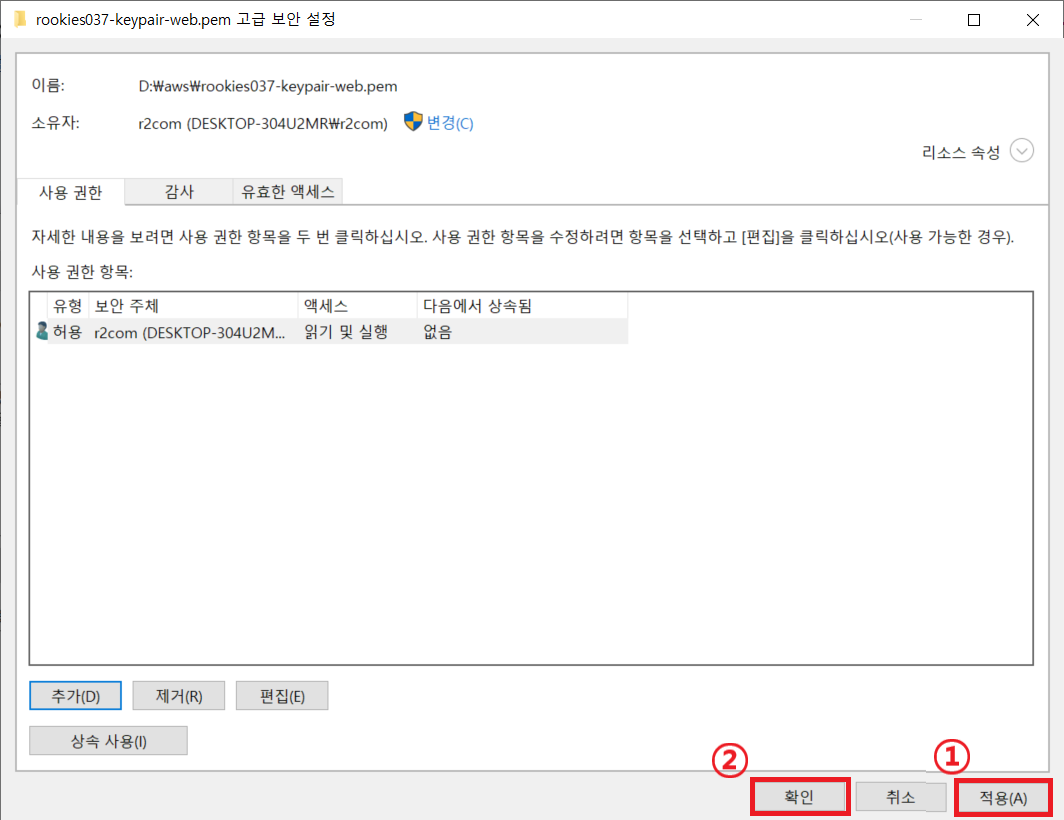
desktop-304u2mr\r2com현재 로그인한 사용자만 인증서 파일을 읽고 실행할 수 있도록 권한 변경 (위에 내용 참조)
d:\aws>ssh -i rookies037_keypair_bastion.pem ubuntu@18.183.222.2
Welcome to Ubuntu 22.04.4 LTS (GNU/Linux 6.5.0-1014-aws x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/pro
System information as of Thu Apr 4 07:39:18 UTC 2024
System load: 0.0 Processes: 95
Usage of /: 20.7% of 7.57GB Users logged in: 0
Memory usage: 20% IPv4 address for eth0: 10.0.10.100
Swap usage: 0%
Expanded Security Maintenance for Applications is not enabled.
0 updates can be applied immediately.
Enable ESM Apps to receive additional future security updates.
See https://ubuntu.com/esm or run: sudo pro status
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
ubuntu@ip-10-0-10-100:~$💻 명령 프롬프트를 하나 더 실행해 로컬 PC에 있는 개인키 파일을 베스천 호스트로 복사
D:\aws>scp -i rookies037_keypair_bastion.pem rookies037_keypair_private.pem ubuntu@18.183.222.2:/home/ubuntu/
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
| | |
| | +-- 베스천 호스트의 username, IP,
| +-- 베스천 호스트로 복사할 파일 파일을 복사할 위치
| 내부 서버로 SSH 접속에 사용할 개인키
+-- 베스천 호스트 접속에 사용하는 개인키
rookies037_keypair_private.pem 100% 1678 42.2KB/s 00:00
💻 키 파일 확인
ubuntu@ip-10-0-10-100:~$ ls -l
total 4
-rw-rw-r-- 1 ubuntu ubuntu 1678 Apr 4 08:34 rookies037_keypair_private.pem💻 키 파일을 이용해 내부 서버로 SSH 접속
ubuntu@ip-10-0-10-100:~$ ssh -i rookies037_keypair_private.pem ubuntu@10.0.30.174
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ~~~~~~~~~~~~~~~~~~
| |
| +-- 내부 서버의 username과 내부 IP
+-- scp 명령으로 복사해 온 내부 서버의 개인 키 파일
The authenticity of host '10.0.30.174 (10.0.30.174)' can't be established.
ED25519 key fingerprint is SHA256:RMTEAvE1LsMwgZH3IDz/to/oh5+CKk/v1U6pepVQi4o.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.0.30.174' (ED25519) to the list of known hosts.
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
@ WARNING: UNPROTECTED PRIVATE KEY FILE! @
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
Permissions 0664 for 'rookies037_keypair_private.pem' are too open.
It is required that your private key files are NOT accessible by others.
This private key will be ignored.
Load key "rookies037_keypair_private.pem": bad permissions
ubuntu@10.0.30.174: Permission denied (publickey).
ubuntu@ip-10-0-10-100:~$ chmod 700 rookies037_keypair_private.pem
ubuntu@ip-10-0-10-100:~$ ls -l
total 4
-rwx------ 1 ubuntu ubuntu 1678 Apr 4 08:34 rookies037_keypair_private.pem
ubuntu@ip-10-0-10-100:~$ ssh -i rookies037_keypair_private.pem ubuntu@10.0.30.174
Welcome to Ubuntu 22.04.4 LTS (GNU/Linux 6.5.0-1014-aws x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/pro
System information as of Thu Apr 4 08:52:29 UTC 2024
System load: 0.080078125 Processes: 95
Usage of /: 20.7% of 7.57GB Users logged in: 0
# 내부 서버로 SSH 접속
Memory usage: 20% IPv4 address for eth0: 10.0.30.174
Swap usage: 0%
Expanded Security Maintenance for Applications is not enabled.
0 updates can be applied immediately.
Enable ESM Apps to receive additional future security updates.
See https://ubuntu.com/esm or run: sudo pro status
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
ubuntu@ip-10-0-30-174:~$💻 내부 서버에 NGINX 서버 설치
private subnet에 위치하므로 외부로 연결할 수 없으므로 NAT Gateway를 추가하고 연결하는 과정 필요
ubuntu@ip-10-0-30-174:~$ sudo apt update💻 NAT Gateway 생성
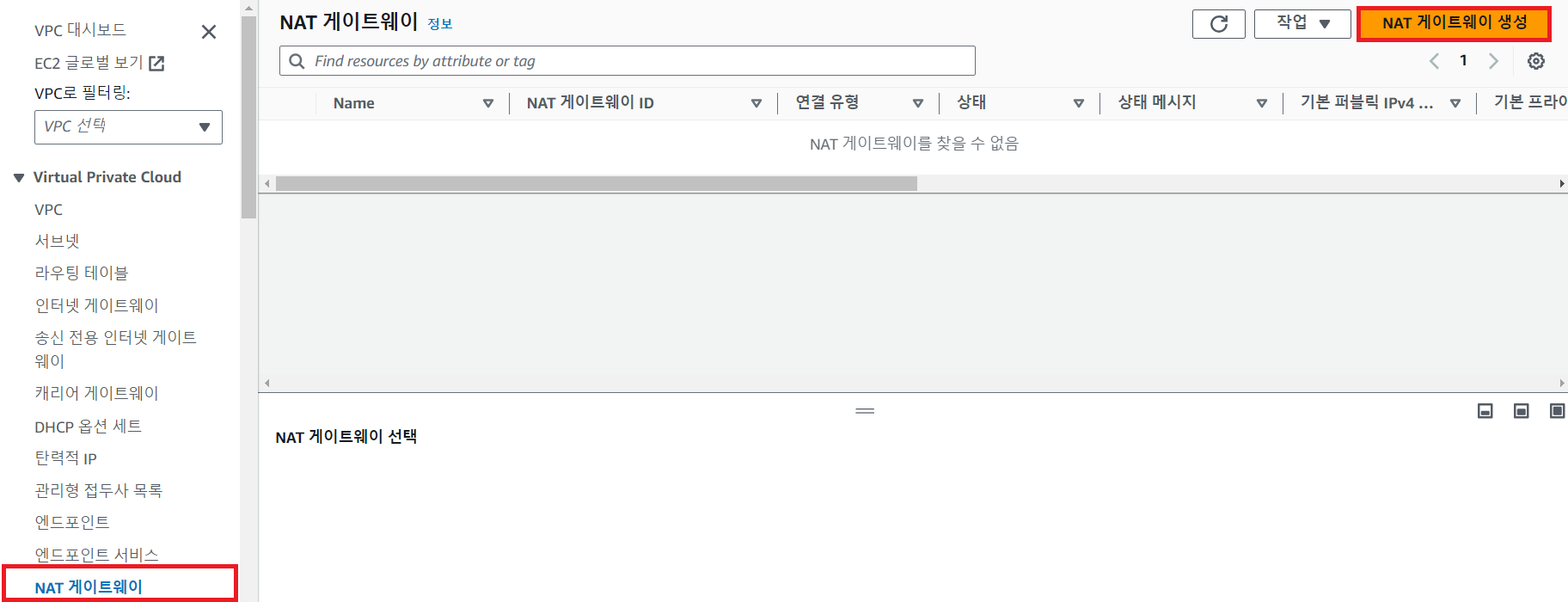
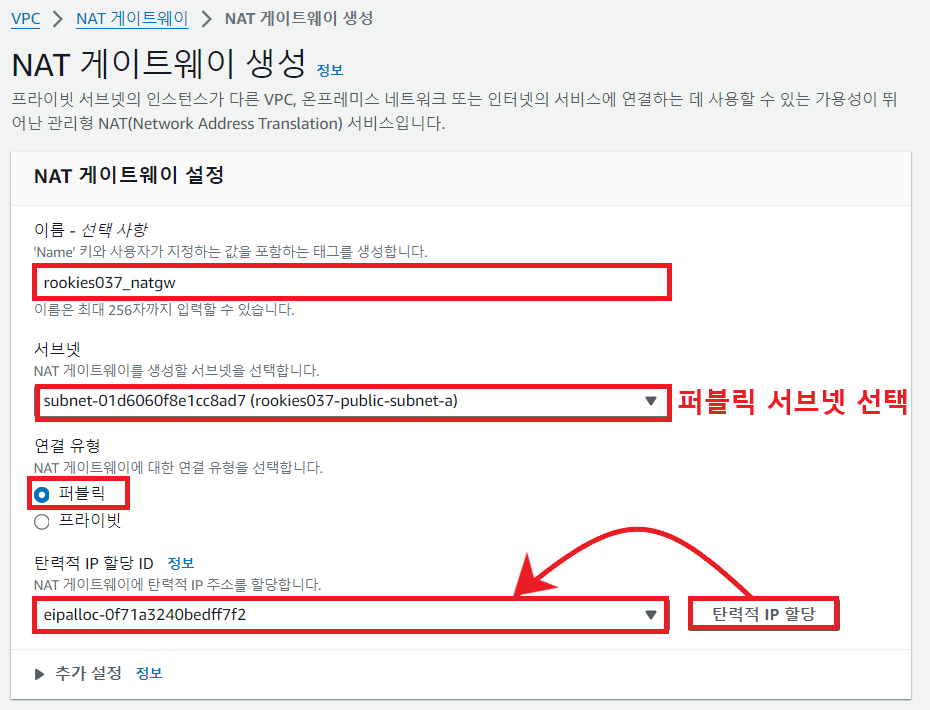
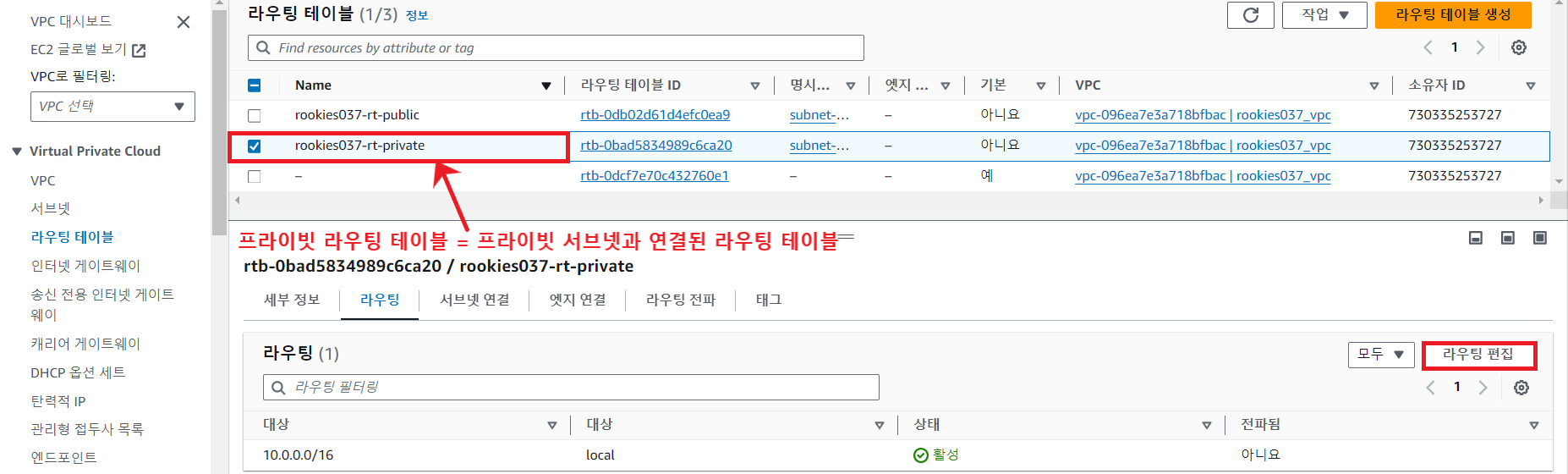
💻 프라이빗 서브넷에 연결된 라우팅 테이블 수정
NAT Gateway로의 라우팅을 추가
💻 내부 서버의 SSH 접속에서 NGINX 서버 설치
ubuntu@ip-10-0-30-174:~$ sudo apt update
ubuntu@ip-10-0-30-174:~$ sudo apt install nginx -y
ubuntu@ip-10-0-30-174:~$ sudo ufw app list
Available applications:
Nginx Full
Nginx HTTP
Nginx HTTPS
OpenSSH
ubuntu@ip-10-0-30-174:~$ sudo ufw allow 'Nginx HTTP'
Rules updated
Rules updated (v6)
ubuntu@ip-10-0-30-174:~$ sudo ufw enable
Command may disrupt existing ssh connections. Proceed with operation (y|n)? y
Firewall is active and enabled on system startup
ubuntu@ip-10-0-30-174:~$ sudo ufw status
Status: active
To Action From
-- ------ ----
Nginx HTTP ALLOW Anywhere
Nginx HTTP (v6) ALLOW Anywhere (v6)
💻 SSH 접속 해제
ubuntu@ip-10-0-30-174:~$ exit # 내부 서버의 SSH 접속 종료
logout
Connection to 10.0.30.174 closed.
ubuntu@ip-10-0-10-100:~$ exit # 베스천 호스트
ubuntu@ip-10-0-10-100:~$ exit # 베스천 호스트의 SSH 접속 종료
logout
Connection to 18.183.222.2 closed.
d:\aws> # 내 PC📌 리소스 정리
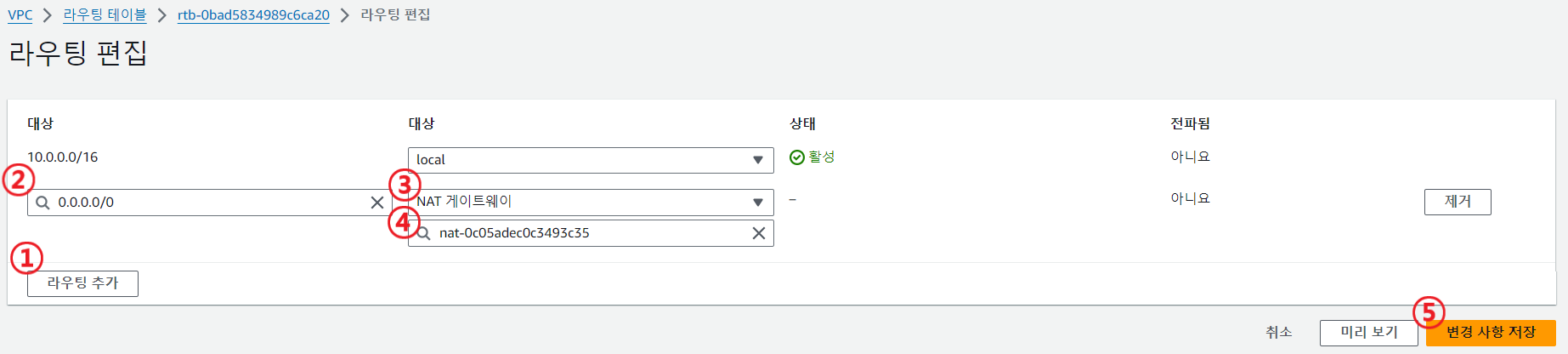
📖 EC2 종료
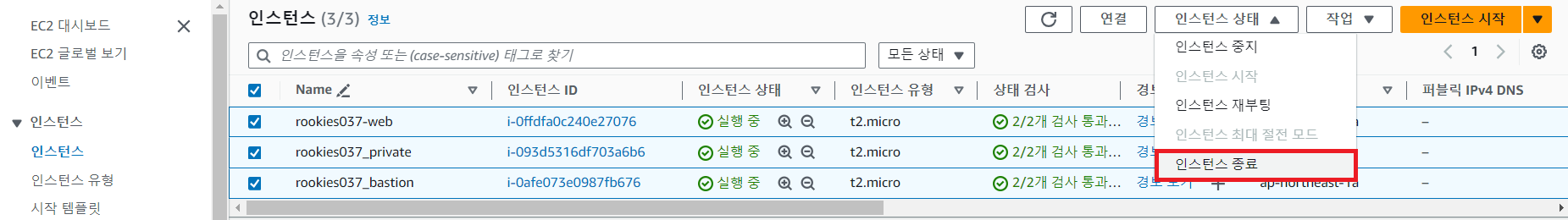
📖 키 페어 삭제
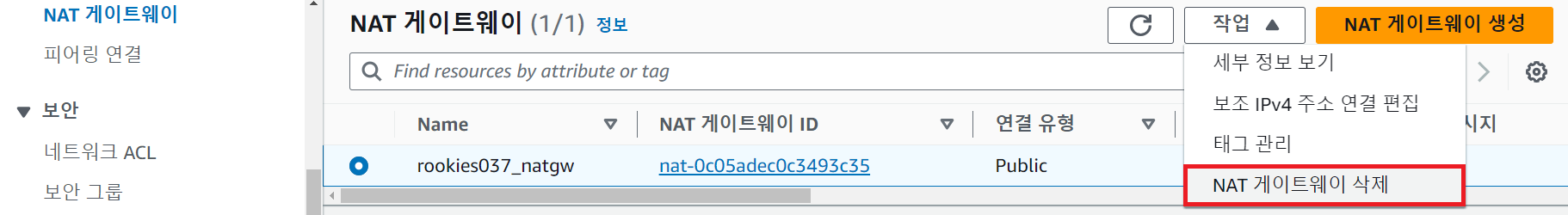
📖 NAT 게이트웨이 삭제
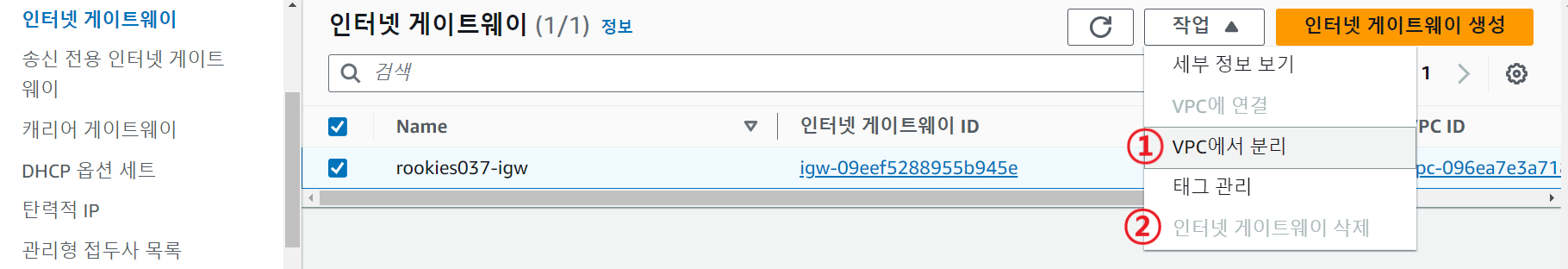
📖 인터넷 게이트웨이 VPC에서 분리 후 삭제
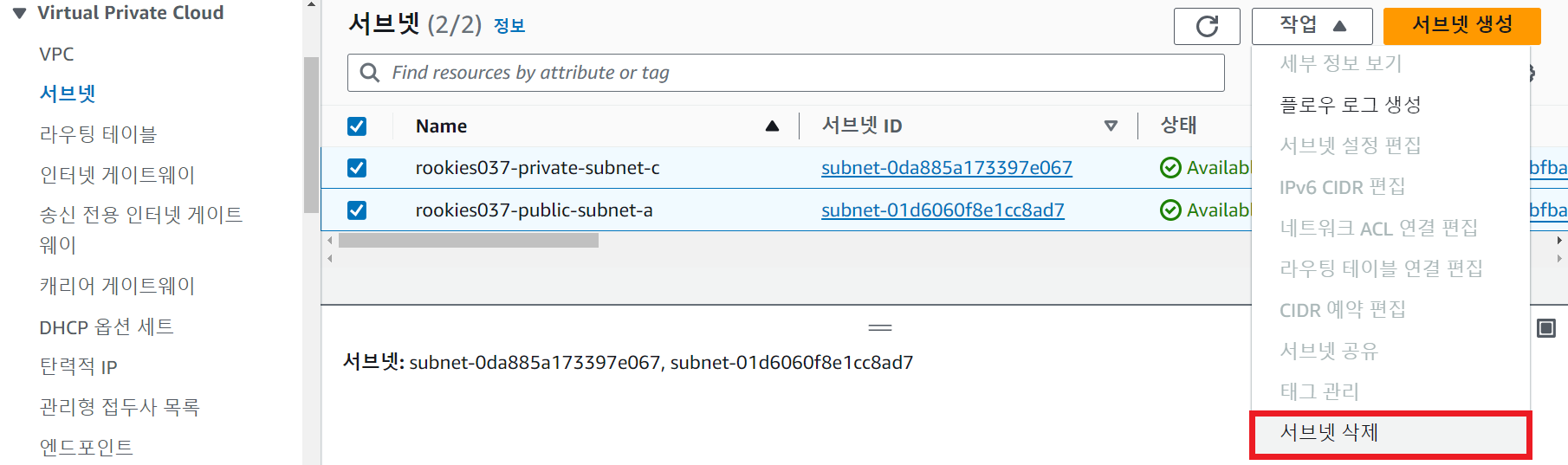
📖 서브넷 삭제
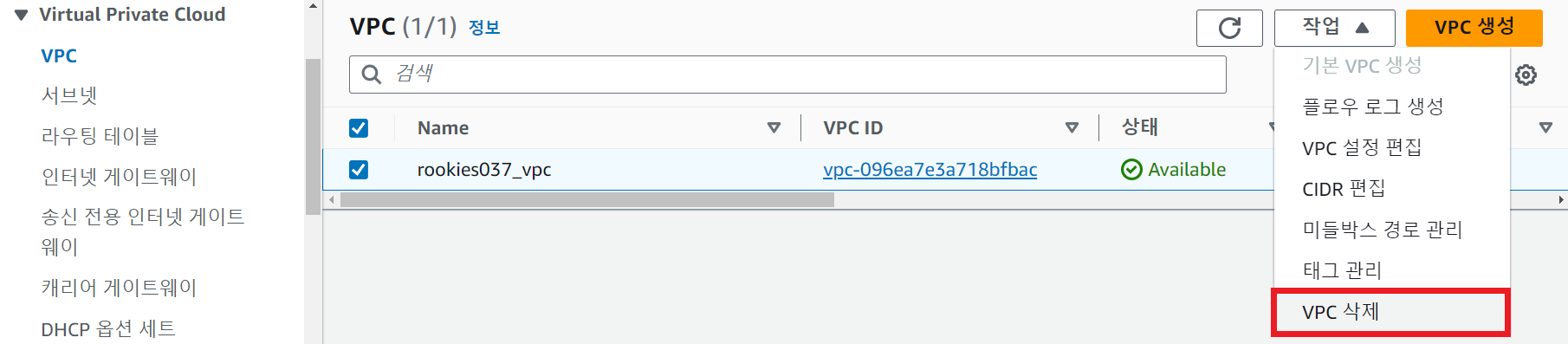
📖 VPC 삭제
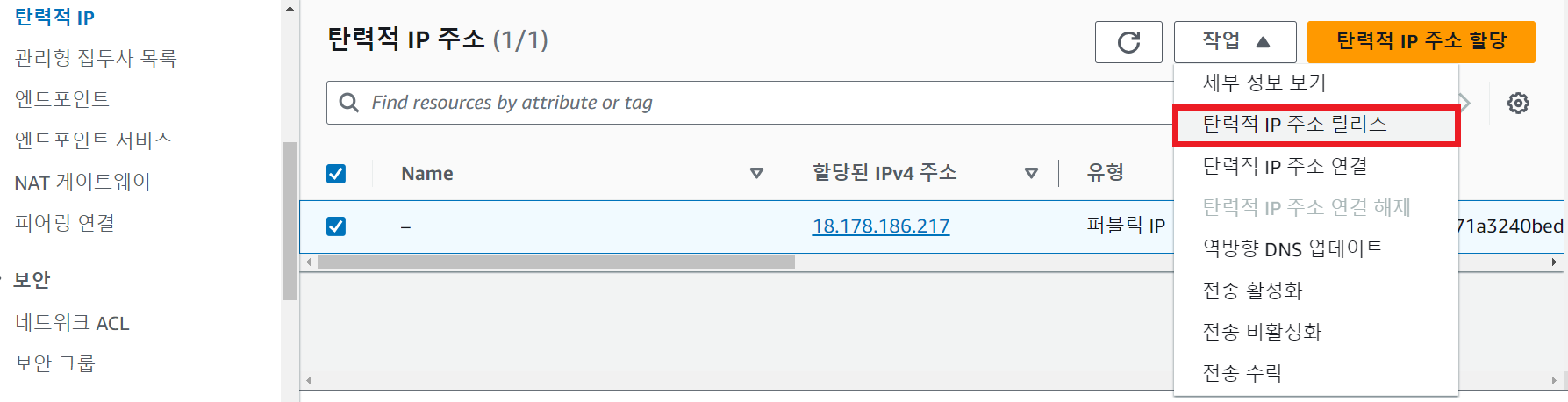
📖 탄력적 IP 삭제
📖 VPC 대시보드 확인
📖 EC2 대시보드 확인