Microservices architecture on Azure Kubernetes Service (AKS)
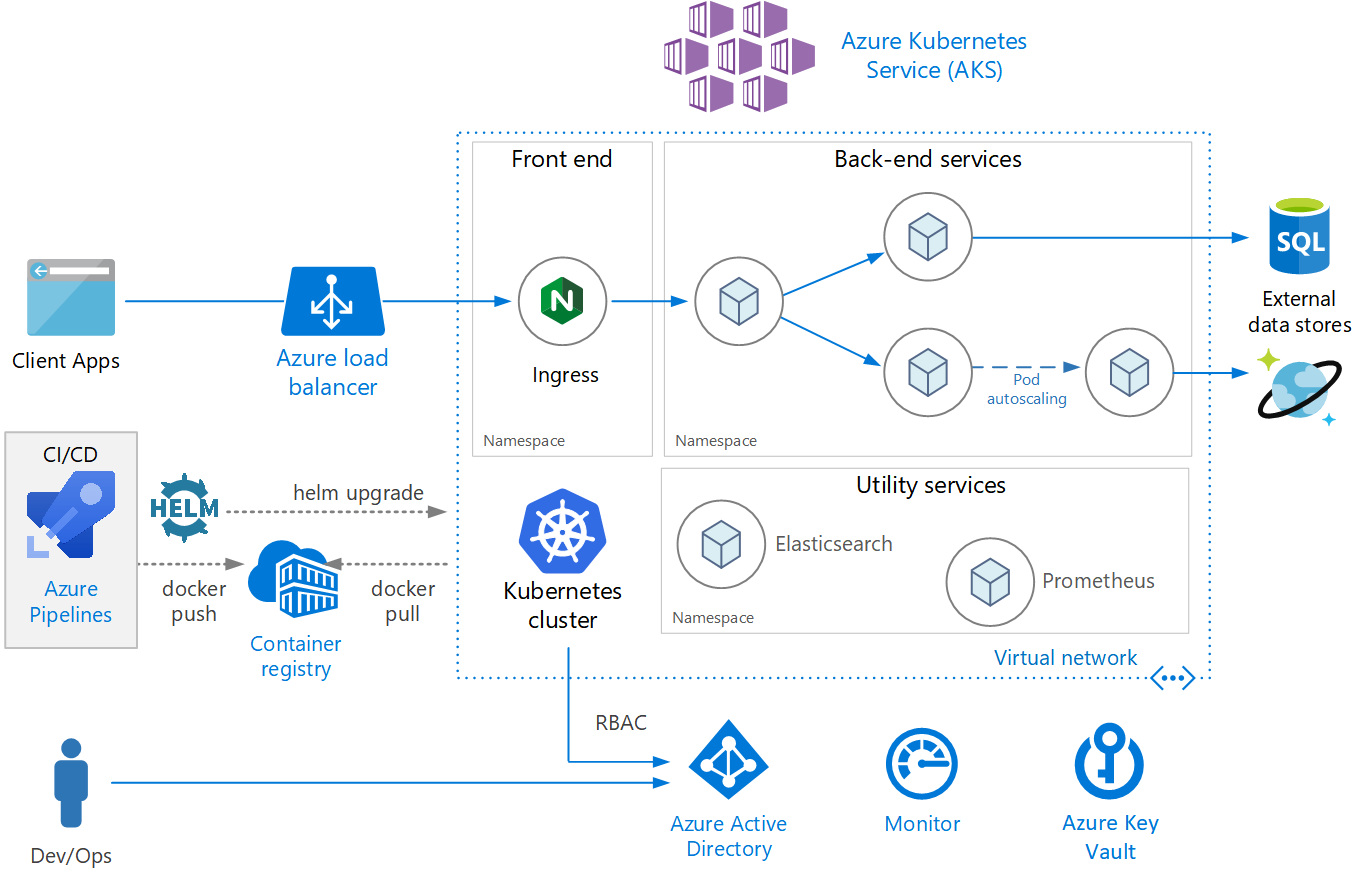
Architecture
- Component list
- Azure Kubernetes Service(AKS), Kubernetes cluster, Virtual network, Ingress, Azure Load Balancer, External data stores, Azure Active Directory, Azure Container Registry, Azure Pipelines, Helm, Azure Monitor
Design considerations
Microservices
- A microservice is a loosely coupled
- independently deployable
- communicate through well-defined APIs
- discoverable through some form of service discovery
Service object
Service object provides a set of capabilities that match these requirements
- IP address : a static internal IP address for a group of pods
- Load balancing : Traffic sent to the service's IP address is load balanced to the pods.
- Service discovery : Services are assigned internal DNS entries by the Kubernetes DNS service.

API gateways
-
Functionality
- Gateway Routing : provides a single endpoint for clients, and helps to decouple clients from services.
- Gateway Aggregation : Cache
- Gateway Offloading : SSL termination, authentication, IP whitelisting, or client rate limiting
-
Most common implementation : Deploy an edge router or reverse proxy, such as Nginx, HAProxy, or Traefik,
-
Risk A reverse proxy server is a potential bottleneck or single point of failure, so always deploy at least two replicas for high availability.
Kubernetes Ingress resource type
Kubernetes ingress
- 설명을 이해하기 어렵다.
- The Kubernetes Ingress resource type abstracts the configuration settings for a proxy server. if you need complete control over the settings, you may want to bypass this abstraction and configure the proxy server manually.
- the Ingress Controller has access to the Kubernetes API, so it can make intelligent decisions about routing and load balancing.
Data storage
- services should not share data storage.
- Each service should own its own private data in a separate logical storage
- Why?
- To avoid hidden dependencies among services.
- To avoid unintentional coupling between services,
Avoid storing persistent data in local cluster storage
- DB
- Persistent Volume mount
Namespaces
- Use namespaces to organize services within the cluster.
- namespaces help prevent naming collisions.
- Apply resource constraints to a namespace,
- Apply policies at the namespace level
- For a microservices architecture, considering organizing the microservices into bounded contexts
- Place utility services into their own separate namespace.
Scalability considerations
Pod autoscaling
- The Horizontal Pod Autoscaler (HPA) scales pods based on observed CPU, memory, or custom metrics.
- Side effects
- pods may be created or evicted more frequently
- Use readiness probes
- Use pod disruption budgets to limit
Cluster autoscaling
- The cluster autoscaler scales the number of nodes.
Availability considerations
Health probes
- Readiness probe : Ready to accept requests
- Liveness probe : Whether a pod should be removed and a new instance started.
- Design probes
- If your code has a long startup time -> use the initialDelaySeconds setting
- 뜻 해석이 안됨 : A liveness probe doesn't help unless restarting the pod is likely to restore it to a healthy state. You can use a liveness probe to mitigate against memory leaks or unexpected deadlocks, but there's no point in restarting a pod that's going to immediately fail again.
- readiness probes are used to check dependent services. creating cascading failures upstream. A better approach is to implement retry handling within your service
Resource constraints
- Define resource constraints for containers, so that a single container cannot overwhelm the cluster resources
- Use resource quotas to limit the total resources allowed for a namespace.
Security considerations
Role based access control (RBAC)
Kubernetes RBAC controls permissions to the Kubernetes API.
- To assign Kubernetes permissions to users, you create roles and role bindings.
- A Role is a set of permissions that apply within a namespace.
- A RoleBinding assigns users or groups to a Role.
Secrets management and application credentials
- HashiCorp Vault
- etcd
Pod and container security
- Don't run containers in privileged mode.
- avoid running processes as root inside containers.
- Store images in a trusted private registry
- Don't leave any known security vulnerabilities.
Deployment (CI/CD) considerations
- services can build and deploy independently, without affecting or disrupting other teams.
- dev/test/QA environments for validation.
- can be deployed side by side with the previous version.

It's great to see a practical explanation of how MSA can enhance scalability and maintainability. I also came across another insightful article (https://www.cleveroad.com/blog/benefits-of-microservices-architecture/) that discusses the benefits of microservices architecture in depth.