AWS환경의 VPC를 구성하고 Subnet을 Public과 Private로 구분하여 internet_gateway, nat_gateway를 구성하고 route table에 설정하도록 하겠습니다.
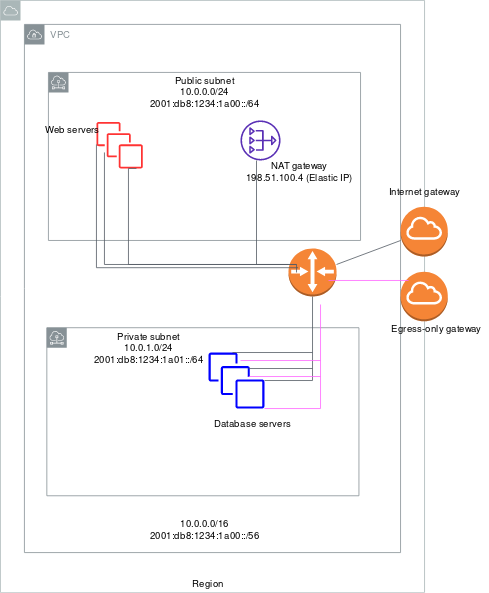
퍼블릭 및 프라이빗 서브넷이 있는 VPC(NAT) : https://docs.aws.amazon.com/ko_kr/vpc/latest/userguide/VPC_Scenario2.html
Getting Started
실습 환경 정보는 아래와 같습니다.
Terraform : Terraform v1.0.0 on linux_amd64
aws cli : aws-cli/2.2.11 Python/3.8.8
os : Linux/4.14.232-176.381.amzn2.x86_64 exe/x86_64.amzn.2 prompt/off
Setting up and running
vpc-aws.tf
$ cat vpc-aws.tf
resource "aws_vpc" "main" {
cidr_block = "10.0.0.0/16"
tags = {
Name = "101-vpc"
}
}
resource "aws_subnet" "public_subnet" {
vpc_id = aws_vpc.main.id
cidr_block = "10.0.0.0/24"
availability_zone = "ap-northeast-2c"
tags = {
Name = "101-public-subnet"
}
}
resource "aws_subnet" "private_subnet" {
vpc_id = aws_vpc.main.id
cidr_block = "10.0.10.0/24"
tags = {
Name = "101-private_subnet"
}
}
resource "aws_internet_gateway" "igw" {
vpc_id = aws_vpc.main.id
tags = {
Name = "101-igw"
}
}
resource "aws_eip" "nat_eip" {
vpc = true
lifecycle {
create_before_destroy = true
}
}
resource "aws_nat_gateway" "nat_gateway" {
allocation_id = aws_eip.nat_eip.id
subnet_id = aws_subnet.public_subnet.id
tags = {
Name = "101-ngw"
}
}
resource "aws_route_table" "public" {
vpc_id = aws_vpc.main.id
# inner rule
route {
cidr_block = "0.0.0.0/0"
gateway_id = aws_internet_gateway.igw.id
}
tags = {
Name = "101-rt-public"
}
}
resource "aws_route_table_association" "route_table_association_public" {
subnet_id = aws_subnet.public_subnet.id
route_table_id = aws_route_table.public.id
}
resource "aws_route_table" "private" {
vpc_id = aws_vpc.main.id
tags = {
Name = "101-rt-private"
}
}
resource "aws_route_table_association" "route_table_association_private" {
subnet_id = aws_subnet.private_subnet.id
route_table_id = aws_route_table.private.id
}
resource "aws_route" "private_nat" {
route_table_id = aws_route_table.private.id
destination_cidr_block = "0.0.0.0/0"
nat_gateway_id = aws_nat_gateway.nat_gateway.id
}Terraform init, plan, apply
Terraform init
terraform plan
terraform apply
terraform state list다음 시간에는 Terraform으로 AWS IAM 구성하는 실습을 해보도록 하겟습니다.
