Dreamhack/SystemHacking
1.[Dreamhack - System Hacking] STAGE 2 : Computer Architecture

dreamhack system hacking lecture 로드맵 중 stage 2의 [Computer Architecture] 내용 정리
2.[Dreamhack - System Hacking] STAGE 2 : Computer Architecture QUIZ

dreamhack system hacking lecture 로드맵 중 stage 2의 [Computer Architecture] QUIZ 정답과 풀이
3.[Dreamhack - System Hacking] STAGE 2 : Linux Memory Layout

dreamhack system hacking lecture 로드맵 중 stage 2의 [Linux Memory Layout] 내용 정리
4.[Dreamhack - System Hacking] STAGE 2 : Linux Memory Layout QUIZ

dreamhack system hacking lecture 로드맵 중 stage 2의 [Linux Memory Layout] QUIZ 정답과 풀이
5.[Dreamhack - System Hacking] STAGE 2 : x86 Assembly : Essential Part(1)

dreamhack system hacking lecture 로드맵 중 stage 2의 [x86 Assembly : Essential Part(1)] 내용 정리
6.[Dreamhack - System Hacking] STAGE 2 : x86 Assembly 1 Quiz

dreamhack system hacking lecture 로드맵 중 stage 2의 [x86 Assembly : Essential Part(1)] QUIZ
7.[Dreamhack - System Hacking] STAGE 2 : x86 Assembly : Essential Part(2)

dreamhack system hacking lecture 로드맵 중 stage 2의 [x86 Assembly : Essential Part(2)] 내용 정리
8.[Dreamhack - System Hacking] STAGE 2 : x86 Assembly 2 QUIZ

dreamhack system hacking lecture 로드맵 중 stage 2의 [x86 Assembly : Essential Part(2)] QUIZ 풀이와 정답
9.[Dreamhack - System Hacking] STAGE 4 : Exploit Tech: Shellcode

dreamhack system hacking lecture 로드맵 중 stage 4의 [Exploit Tech - Shellcode] 개념 정리
10.[Dreamhack - System Hacking] STAGE 5 : Calling Convention
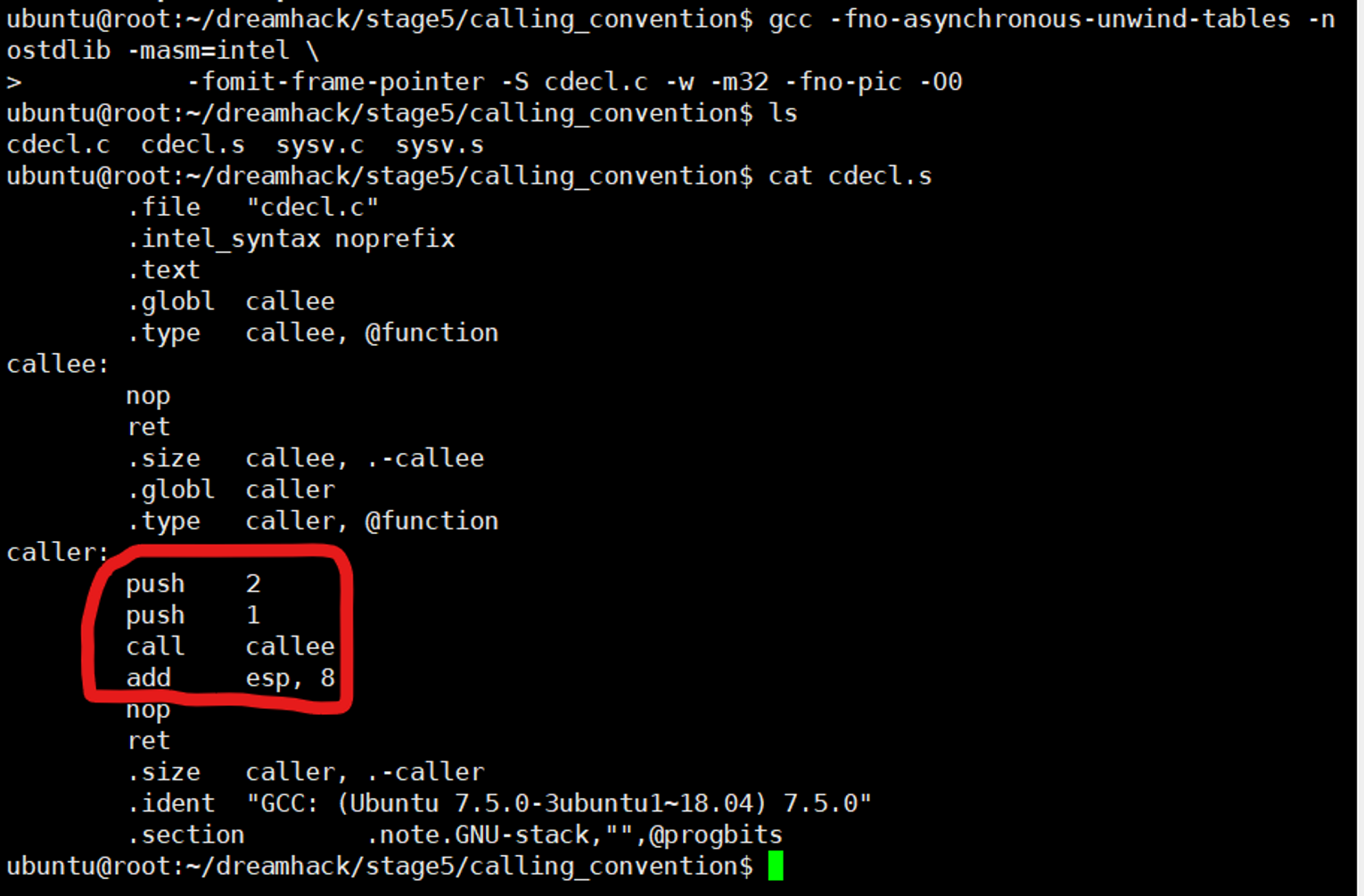
dreamhack system hacking lecture 로드맵 중 stage 5의 [Calling Convention] 개념 정리
11.[Dreamhack - System Hacking] STAGE 5 : Background: Calling Convention QUIZ

dreamhack system hacking lecture 로드맵 중 stage 5의 [Calling Convention] QUIZ 풀이와 정답
12.[Dreamhack - System Hacking] STAGE 5 : Memory Corruption: Stack Buffer Overflow

dreamhack system hacking lecture 로드맵 중 stage 5의 [Memory Corruption: Stack Buffer Overflow] 개념 정리