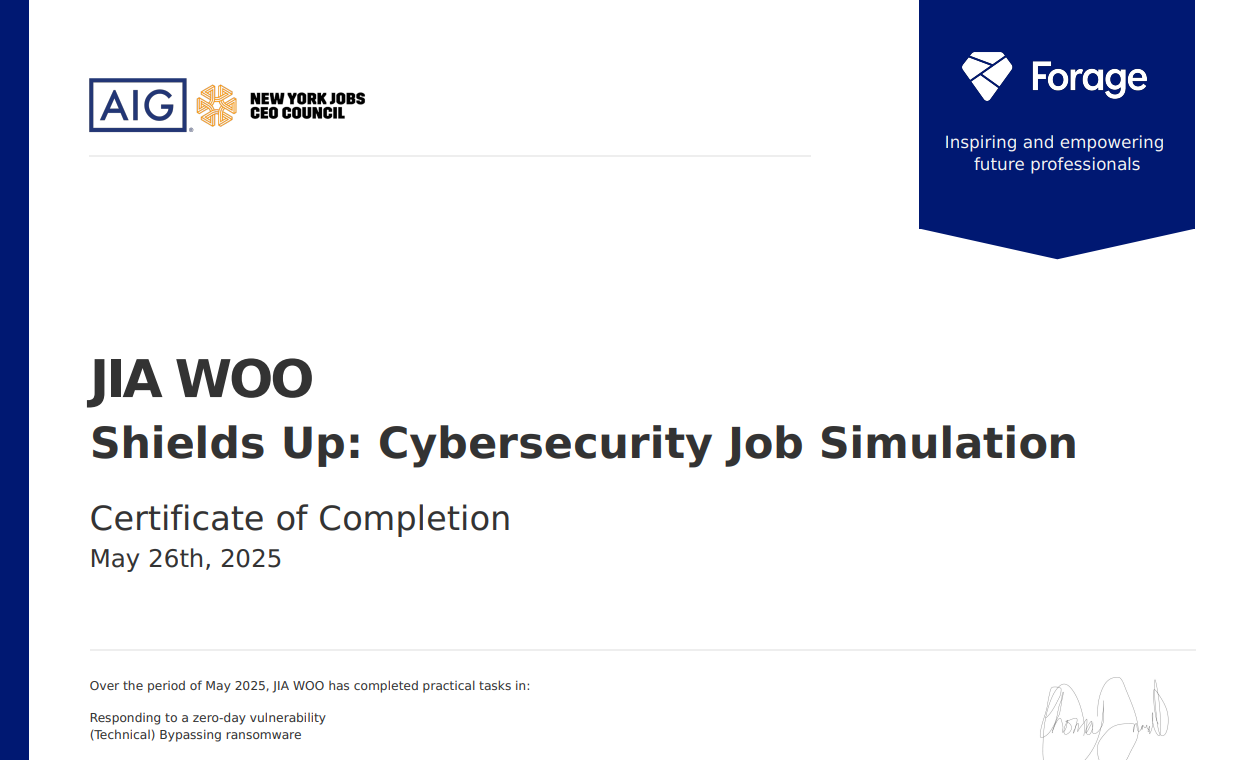
forage - AIG Shildes up : Cybersecurity Job Simulation
해당 시뮬레이션은 사이버 시큐리티의 기본 개념에 대한 퀴즈와 스크립트 작성 및 경고 이메일 작성 까지 완료 하였다
아젠다
- 사이버 보안 및 인프라 보안 기관(CISA)의 최근 간행물을 검토 및 보고된 취약점 조사
- 영향을 받는 팀에 취약점을 알리고 해결 방법을 설명
- Python을 사용하여 랜섬웨어 바이러스에 대응하는 방법
- 암호화된 파일의 해독 키를 무차별 대입 공격하는 Python 스크립트 작성
인프라 소유자에게 이 취약점의 심각성을 알리는 경고 이메일을 작성하기
Subject: [Critical] Missing 2FA on Internal Login – Immediate Action Required
Dear SpongeBob, Product Development Team Lead,
AIG Cyber & Information Security Team has identified a critical security vulnerability in the internal login process, which may expose your team to unauthorized access and data leakage.
Vulnerability
The internal login system allows authentication without enforcing two-factor authentication (2FA). Any valid credentials can be used to access sensitive systems without additional verification.
Risk / Potential Impact
Severity: High
Impact: Exposure of sensitive internal data, unauthorized access to team environments
Affected systems: All internal applications that rely solely on ID/PW login
Exploitation Scenario
An attacker who obtains a valid employee ID/password—via phishing, credential stuffing, or other means—can directly log in without being stopped, since no secondary verification (2FA) is in place.
Recommended Remediation Steps
Please take the following actions immediately:
Enforce 2FA for all internal login systems.
Recommended methods include:
Biometric authentication (fingerprint, iris scan)
Employee ID badge-based authentication
One-time passwords (OTP) or mobile authentication apps
Audit all login endpoints for 2FA enforcement.
Notify the Security Team upon completion for validation.
We will provide implementation documentation and offer hands-on support upon request.
Please contact us if you need assistance or have any questions.
암호화된 파일의 암호 해독 키를 무차별 대입 공격으로 빼내는 Python 스크립트를 작성하기
import zipfile
zip_file_path = 'secret.zip'
password_file_path = 'rockyou.txt'
with zipfile.ZipFile(zip_file_path) as zf:
with open(password_file_path, 'rb') as pf:
for line in pf:
password = line.strip()
try:
zf.extractall(pwd=password)
print(f"[+] PASSWOEDFOUNDIT! --> {password.decode()}")
break
except:
print(f"[-] FALE: {password.decode(errors='ignore')}")