Gnosis Safe는 이더리움 기반의 Multi-signature 지갑으로, 여러 명의 승인을 받아야 자금 이체나 기타 중요한 작업이 수행되도록 설계된 보안 지갑이다.
Proxy Pattern
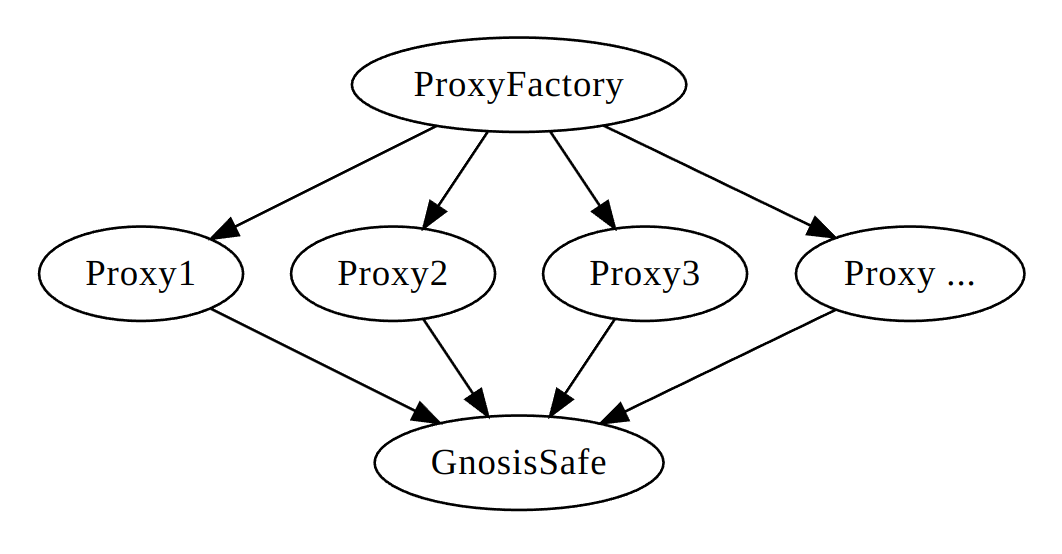
Gnosis Safe는 EIP-1167 Minimal Proxy Pattern을 사용하여 계약을 배포한다. 이를 위해 ProxyFactory Contract와 Master Singleton Contract가 존재한다. Proxy 패턴을 사용하여 Gas 절약이 가능하다. 모든 지갑은 Master 계약을 참조하는 Proxy 계약으로 동작하며, Proxy 계약은 저장 상태를 관리하고 Logic 실행은 Master 계약에게 delegate한다.
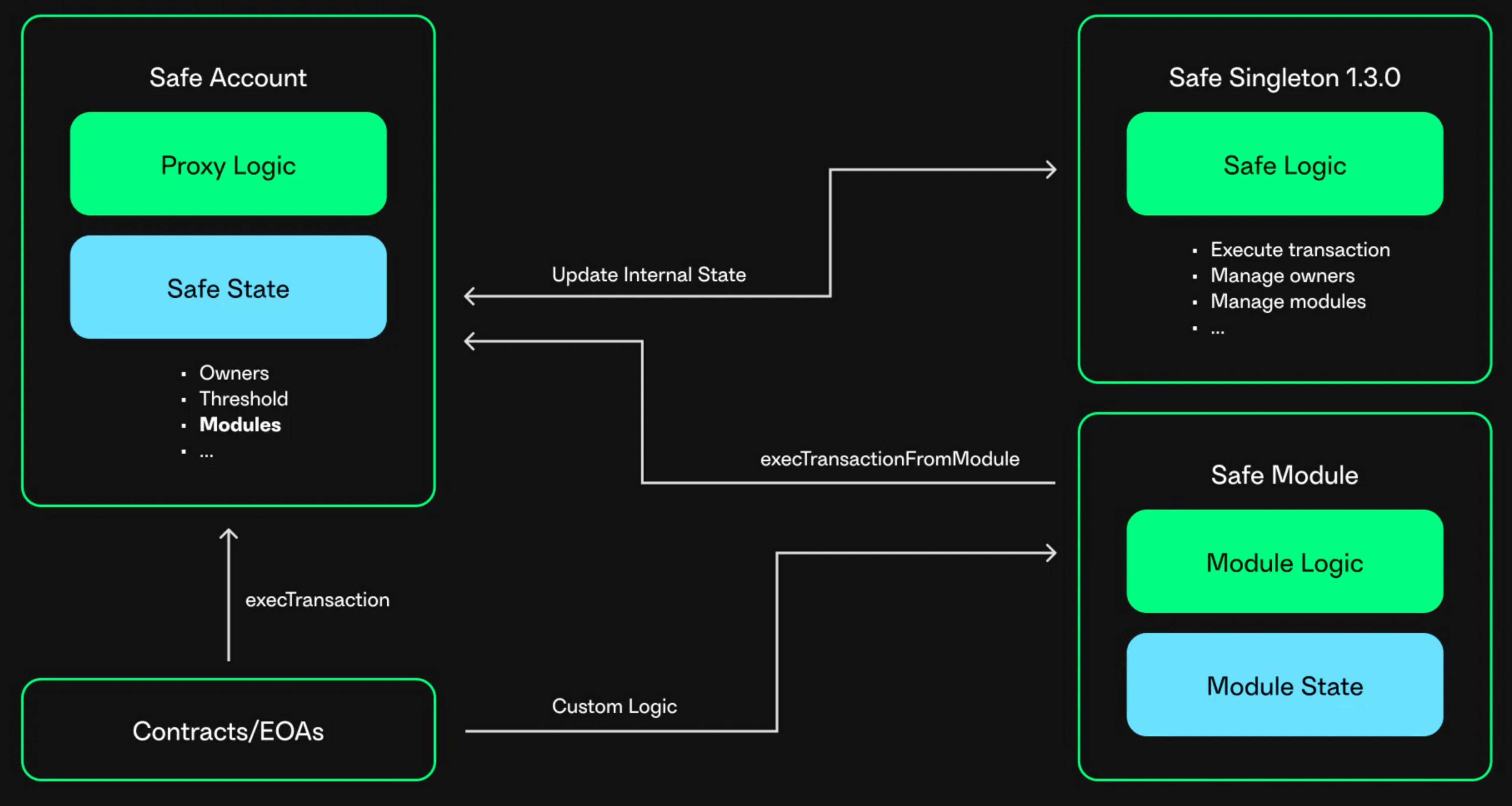
Safe Module
Gnosis Safe 지갑의 핵심 기능은 Multi-Sig 구조인데, 이는 트랜젝션마다 최소 서명 수를 요구한다. 이를 확장하기 위해서 Module이 존재한다. 모듈을 통해 Gnosis Safe 지갑에 추가 기능을 부여할 수 있다. 모듈을 통해 일일 지출 한도 설정, 특정 금액 이하 Multi-Sig 없이 전송 등 기능을 추가할 수 있다.
모듈을 설정하거나 비활성화할 때는 지갑 자체에서 트랜잭션을 실행해야한다. 하나의 지갑은 여러 개의 외부 모듈을 지원할 수 있으며, 각 모듈은 외부 Smart Contract로 관리된다.
이러한 외부 모듈들은 execTransactionFromModule() 함수를 호출하여 지갑이 트랜젝션을 실행하게 한다. 이 방식은 일반적인 execTransaction() 에서 요구되는 N-out-of-M 서명 확인을 우회할 수 있다. 대신, 권한 검사는 모듈 내에서 수행된다.
Guards
Guards는 N-out-of-M Multi-Sig 구조 위에 추가 보안 계층을 더하기 위한 기능이다. Guard를 설정하면, 지갑에서 나가는 모든 트랜잭션은 Guard의 검사를 통과해야만 실행된다.
하지만 잘못 구현된 Guard는 DoS, 지갑 잠금 등과 같은 문제를 일으킬 수 있다.
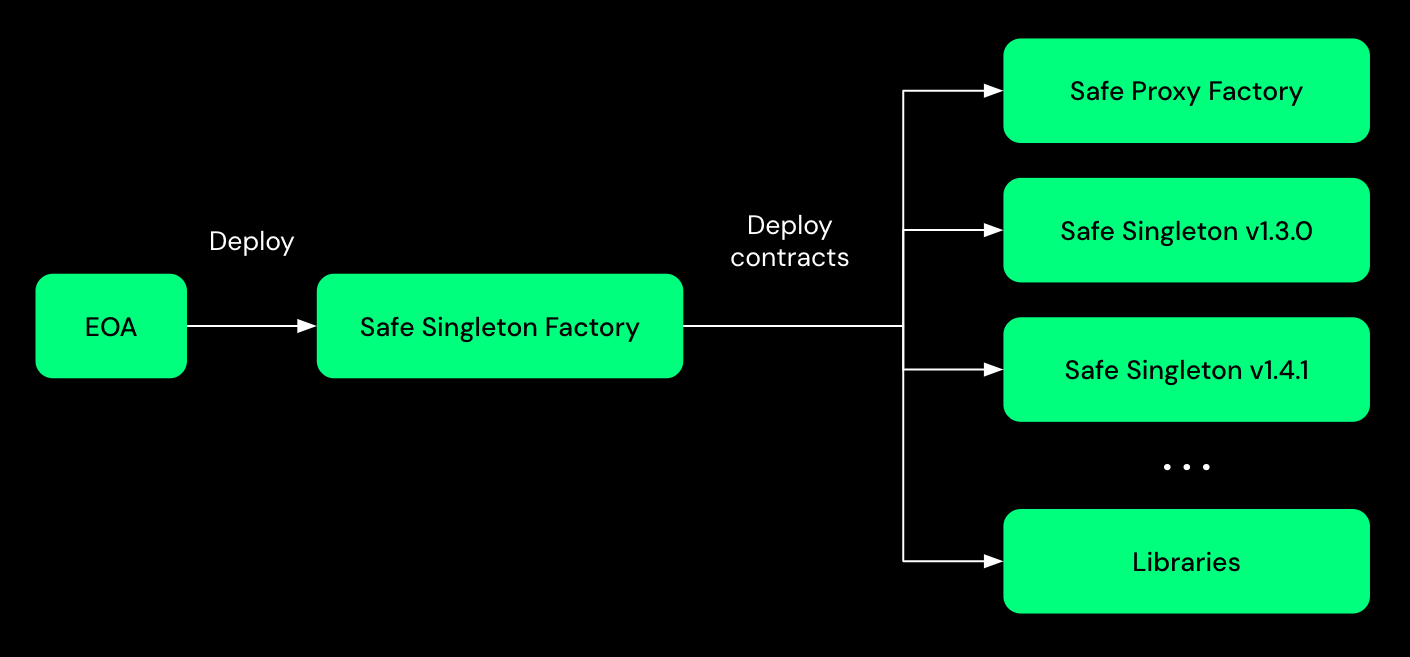
프록시 배포
Gnosis Safe 지갑을 배포하려면 Proxy Factory와 master singleton contract가 필요하다.
/contracts/proxies/SafeProxyFactory.sol 에 Proxy를 생성하고 배포하는 코드가 존재한다. 여기서 생성된 Prxoy 지갑은은 Master 계약에 delegate 하는 역할만을 담당한다.
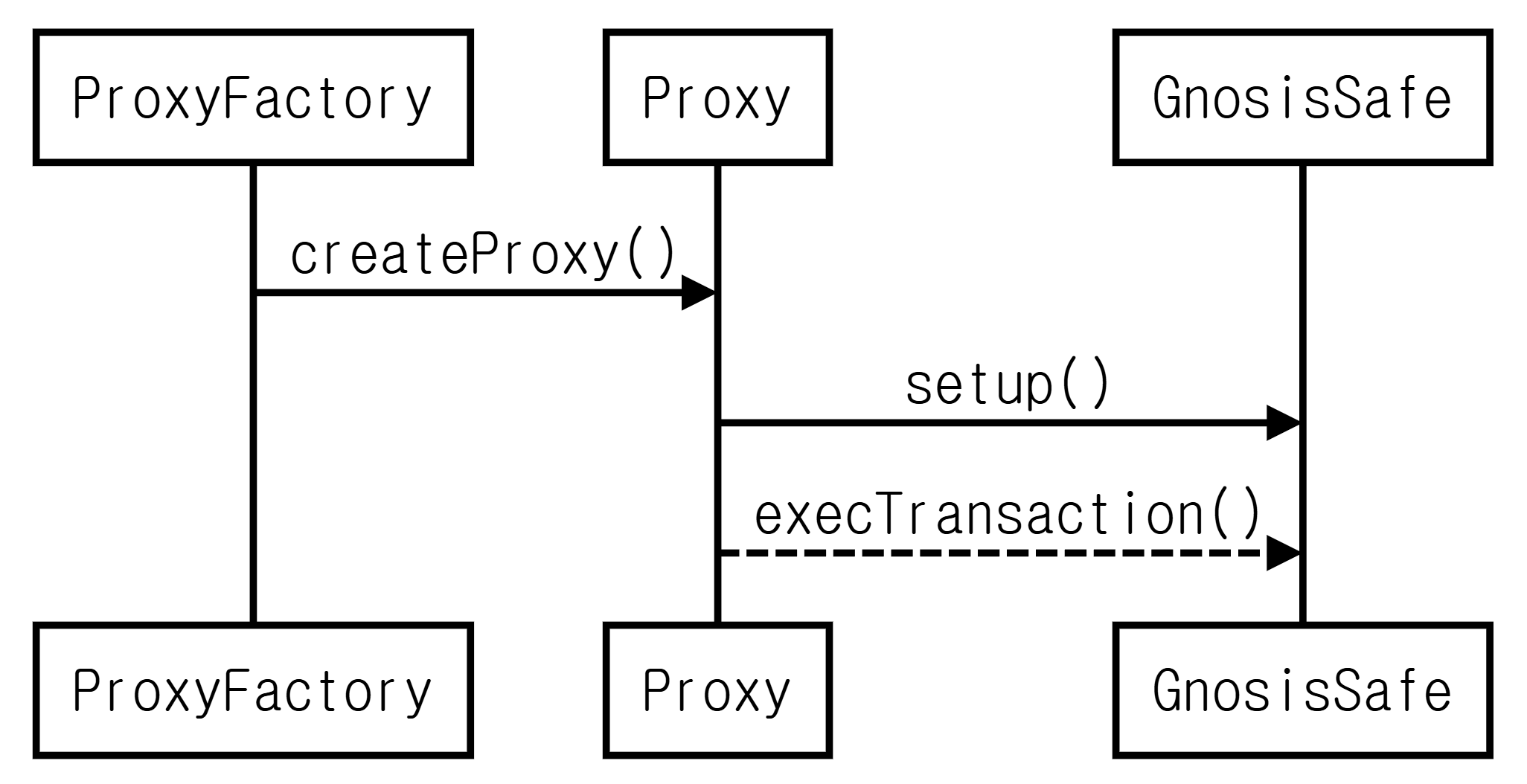
deployProxy 함수를 통해 배포를 하는데, Singleton을 여러 주소에 프록시 형태로 배포하고, initializer가 있다면 해당 프록시에 초기화 call을 수행한다. Sigleton logic 컨트랙트의 기능을 delegate call을 통해 실행한다. create2를 통해 address predictable한 주소를 생성한다.
abi.encodePacked(type(SafeProxy).creationCode, uint160(_singleton)): 프록시 생성 바이트코드 + singleton 주소를 붙여서 배포코드 생성
function setup(
address[] calldata _owners, // 소유자 목록
uint256 _threshold, // 최소 서명수 (N-of-M 에서 N)
address to, // 초기화 트랜잭션 실행 대상 (option)
bytes calldata data, // 초기화 트랜잭션 실행 데이터 (option)
address fallbackHandler, // fallback handler address
address paymentToken, // 초기 gas 비용 지불 토큰
uint256 payment, // 초기 비용
address payable paymentReceiver
) externalinitializer는 Master 계약(Safe)'s setup() 함수를 호출하는 calldata이다.
* @notice Internal method to create a new proxy contract using CREATE2. Optionally executes an initializer call to a new proxy.
* @param _singleton Address of singleton contract. Must be deployed at the time of execution.
* @param initializer (Optional) Payload for a message call to be sent to a new proxy contract.
* @param salt Create2 salt to use for calculating the address of the new proxy contract.
* @return proxy Address of the new proxy contract.
*/
function deployProxy(address _singleton, bytes memory initializer, bytes32 salt) internal returns (SafeProxy proxy) {
require(isContract(_singleton), "Singleton contract not deployed");
bytes memory deploymentData = abi.encodePacked(type(SafeProxy).creationCode, uint256(uint160(_singleton)));
// solhint-disable-next-line no-inline-assembly
assembly {
proxy := create2(0x0, add(0x20, deploymentData), mload(deploymentData), salt)
}
require(address(proxy) != address(0), "Create2 call failed");
if (initializer.length > 0) {
// solhint-disable-next-line no-inline-assembly
assembly {
if eq(call(gas(), proxy, 0, add(initializer, 0x20), mload(initializer), 0, 0), 0) {
revert(0, 0)
}
}
}
}
/**
* @notice Deploys a new proxy with `_singleton` singleton and `saltNonce` salt. Optionally executes an initializer call to a new proxy.
* @param _singleton Address of singleton contract. Must be deployed at the time of execution.
* @param initializer Payload for a message call to be sent to a new proxy contract.
* @param saltNonce Nonce that will be used to generate the salt to calculate the address of the new proxy contract.
*/
function createProxyWithNonce(address _singleton, bytes memory initializer, uint256 saltNonce) public returns (SafeProxy proxy) {
// If the initializer changes the proxy address should change too. Hashing the initializer data is cheaper than just concatinating it
bytes32 salt = keccak256(abi.encodePacked(keccak256(initializer), saltNonce));
proxy = deployProxy(_singleton, initializer, salt);
emit ProxyCreation(proxy, _singleton);
}SafeProxy Contract는 모든 호출을 Master Singleton 계약으로 delegate한다.
delegatecall(gas(), _singleton, 0, calldatasize(), 0, 0)
singleton 변수는 저장소 슬롯의 위치 정렬을 위해 가장 먼저 선언되며, 실제 실행 로직은 Master 계약에서 실행된다.
/contracts/proxies/SafeProxy.sol
// SPDX-License-Identifier: LGPL-3.0-only
pragma solidity >=0.7.0 <0.9.0;
/**
* @title IProxy - Helper interface to access the singleton address of the Proxy on-chain.
* @author Richard Meissner - @rmeissner
*/
interface IProxy {
function masterCopy() external view returns (address);
}
/**
* @title SafeProxy - Generic proxy contract allows to execute all transactions applying the code of a master contract.
* @author Stefan George - <stefan@gnosis.io>
* @author Richard Meissner - <richard@gnosis.io>
*/
contract SafeProxy {
// Singleton always needs to be first declared variable, to ensure that it is at the same location in the contracts to which calls are delegated.
// To reduce deployment costs this variable is internal and needs to be retrieved via `getStorageAt`
address internal singleton;
/**
* @notice Constructor function sets address of singleton contract.
* @param _singleton Singleton address.
*/
constructor(address _singleton) {
require(_singleton != address(0), "Invalid singleton address provided");
singleton = _singleton;
}
/// @dev Fallback function forwards all transactions and returns all received return data.
fallback() external payable {
// solhint-disable-next-line no-inline-assembly
assembly {
let _singleton := and(sload(0), 0xffffffffffffffffffffffffffffffffffffffff)
// 0xa619486e == keccak("masterCopy()"). The value is right padded to 32-bytes with 0s
if eq(calldataload(0), 0xa619486e00000000000000000000000000000000000000000000000000000000) {
mstore(0, _singleton)
return(0, 0x20)
}
calldatacopy(0, 0, calldatasize())
let success := delegatecall(gas(), _singleton, 0, calldatasize(), 0, 0)
returndatacopy(0, 0, returndatasize())
if eq(success, 0) {
revert(0, returndatasize())
}
return(0, returndatasize())
}
}
}OwnerManager
OwnerManager 계약은 지갑의 owner와 관련된 로직을 관리하는 역할을 한다. Safe 지갑이 Multi-Sig를 위해 유지해야 하는 소유자 그룹과 서명 임계값(threshold)을 관리한다.
Solidity내에는 Set, Map 같은 자료구조가 없기 때문에 Owner 주소들을 SIngle Linked List로 관리한다.
- SENTINEL_OWNERS (0x1) → owner0 → owner1 → owner2 → ... → ownerN → SENTINEL_OWNERS
- SENTINEL_OWNERS: 연결 리스트의 시작과 끝을 표시하는 특수 주소(0x1)
- 각 소유자는
mapping(address => address)구조로 다음 소유자의 주소를 저장 - 삽입, 삭제, 조회가 모두 O(1) 시간 복잡도로 수행
소유자를 삭제할 때는 이전 소유자의 주소(prevOwner)를 알아야 한다. Off-Chain에서 별도로 관리하거나, Gnosis relayer를 통해 처리될 수 있다.
/contracts/base/OwnerManager.sol
address internal constant SENTINEL_OWNERS = address(0x1);
mapping(address => address) internal owners;
uint256 internal ownerCount;
uint256 internal threshold;
/**
* @notice Sets the initial storage of the contract.
* @param _owners List of Safe owners.
* @param _threshold Number of required confirmations for a Safe transaction.
*/
function setupOwners(address[] memory _owners, uint256 _threshold) internal {
// Threshold can only be 0 at initialization.
// Check ensures that setup function can only be called once.
require(threshold == 0, "GS200");
// Validate that threshold is smaller than number of added owners.
require(_threshold <= _owners.length, "GS201"); // threshold는 owner 수보다 작아야함
// There has to be at least one Safe owner.
require(_threshold >= 1, "GS202"); // 최소 한명 필수
// Initializing Safe owners.
address currentOwner = SENTINEL_OWNERS;
for (uint256 i = 0; i < _owners.length; i++) { // 주소 유효성 검사 및 중복 체크
// Owner address cannot be null.
address owner = _owners[i];
require(owner != address(0) && owner != SENTINEL_OWNERS && owner != address(this) && currentOwner != owner, "GS203");
// No duplicate owners allowed.
require(owners[owner] == address(0), "GS204");
owners[currentOwner] = owner;
currentOwner = owner;
}
owners[currentOwner] = SENTINEL_OWNERS;
ownerCount = _owners.length;
threshold = _threshold;
}
/**
* @notice Adds the owner `owner` to the Safe and updates the threshold to `_threshold`.
* @dev This can only be done via a Safe transaction.
* @param owner New owner address.
* @param _threshold New threshold.
*/
function addOwnerWithThreshold(address owner, uint256 _threshold) public authorized {
// Owner address cannot be null, the sentinel or the Safe itself.
require(owner != address(0) && owner != SENTINEL_OWNERS && owner != address(this), "GS203");
// No duplicate owners allowed.
require(owners[owner] == address(0), "GS204");
owners[owner] = owners[SENTINEL_OWNERS];
owners[SENTINEL_OWNERS] = owner;
ownerCount++;
emit AddedOwner(owner);
// Change threshold if threshold was changed.
if (threshold != _threshold) changeThreshold(_threshold);
}
/**
* @notice Removes the owner `owner` from the Safe and updates the threshold to `_threshold`.
* @dev This can only be done via a Safe transaction.
* @param prevOwner Owner that pointed to the owner to be removed in the linked list
* @param owner Owner address to be removed.
* @param _threshold New threshold.
*/
function removeOwner(address prevOwner, address owner, uint256 _threshold) public authorized {
// Only allow to remove an owner, if threshold can still be reached.
require(ownerCount - 1 >= _threshold, "GS201"); // 삭제 후에도 threshold를 만족해야 함
// Validate owner address and check that it corresponds to owner index.
require(owner != address(0) && owner != SENTINEL_OWNERS, "GS203");
require(owners[prevOwner] == owner, "GS205");
owners[prevOwner] = owners[owner]; // 리스트 연결 재조정
owners[owner] = address(0); // 삭제
ownerCount--;
emit RemovedOwner(owner);
// Change threshold if threshold was changed.
if (threshold != _threshold) changeThreshold(_threshold);
}
/**
* @notice Replaces the owner `oldOwner` in the Safe with `newOwner`.
* @dev This can only be done via a Safe transaction.
* @param prevOwner Owner that pointed to the owner to be replaced in the linked list
* @param oldOwner Owner address to be replaced.
* @param newOwner New owner address.
*/
function swapOwner(address prevOwner, address oldOwner, address newOwner) public authorized {
// Owner address cannot be null, the sentinel or the Safe itself.
require(newOwner != address(0) && newOwner != SENTINEL_OWNERS && newOwner != address(this), "GS203");
// No duplicate owners allowed.
require(owners[newOwner] == address(0), "GS204");
// Validate oldOwner address and check that it corresponds to owner index.
require(oldOwner != address(0) && oldOwner != SENTINEL_OWNERS, "GS203");
require(owners[prevOwner] == oldOwner, "GS205");
owners[newOwner] = owners[oldOwner];
owners[prevOwner] = newOwner;
owners[oldOwner] = address(0);
emit RemovedOwner(oldOwner);
emit AddedOwner(newOwner);
}ModulesManager
ModulesManager는 Gnosis Safe 지갑의 외부 모듈 확장 기능을 담당한다. OwnerManager처럼, 모듈도 연결 리스트 방식으로 관리된다.
- SENTINEL_MODULES → module0 → module1 → ... → SENTINEL_MODULES
/contracts/base/ModuleManager.sol
address internal constant SENTINEL_MODULES = address(0x1);
mapping(address => address) internal modules;
/**
* @notice Setup function sets the initial storage of the contract.
* Optionally executes a delegate call to another contract to setup the modules.
* @param to Optional destination address of call to execute.
* @param data Optional data of call to execute.
*/
function setupModules(address to, bytes memory data) internal {
require(modules[SENTINEL_MODULES] == address(0), "GS100"); // 중복 초기화 방지
modules[SENTINEL_MODULES] = SENTINEL_MODULES;
if (to != address(0)) {
require(isContract(to), "GS002"); // 유효한 계약주소인지
// Setup has to complete successfully or transaction fails.
require(execute(to, 0, data, Enum.Operation.DelegateCall, type(uint256).max), "GS000"); // delegatecall 실행
}
}잘못된 Cotnract 주소나 악의적인 코드가 delegatecall될 경우, 지갑의 저장소가 위험하다. setupModules에 사용되는 모듈 계약은 반드시 trustful한 코드여야한다.
GuardManager
GuardManager는 Gnosis Safe의 트랜잭션 실행 직전 최종 검사를 담당하는 구성 요소다.
authorized modifier가 붙은 함수는 외부 주소에서 직접 호출이 불가능하고, 지갑 내부 트랜잭션(executeTransaction)을 통해 실행해야 한다.
/contracts/common/SelfAuthorized.sol
abstract contract SelfAuthorized {
function requireSelfCall() private view {
require(msg.sender == address(this), "GS031");
}
modifier authorized() {
// Modifiers are copied around during compilation. This is a function call as it minimized the bytecode size
requireSelfCall();
_;
}
}Guard는 execTransaction()의 사전/사후 검사를 위한 인터페이스 (checkTransaction, checkAfterExecution)를 구현해야한다.
interface Guard is IERC165 {
function checkTransaction(
address to,
uint256 value,
bytes memory data,
Enum.Operation operation,
uint256 safeTxGas,
uint256 baseGas,
uint256 gasPrice,
address gasToken,
address payable refundReceiver,
bytes memory signatures,
address msgSender
) external;
function checkAfterExecution(bytes32 txHash, bool success) external;
}/contracts/base/GuardManager.sol
abstract contract GuardManager is SelfAuthorized {
event ChangedGuard(address indexed guard);
// keccak256("guard_manager.guard.address")
bytes32 internal constant GUARD_STORAGE_SLOT = 0x4a204f620c8c5ccdca3fd54d003badd85ba500436a431f0cbda4f558c93c34c8;
/**
* @dev Set a guard that checks transactions before execution
* This can only be done via a Safe transaction.
* ⚠️ IMPORTANT: Since a guard has full power to block Safe transaction execution,
* a broken guard can cause a denial of service for the Safe. Make sure to carefully
* audit the guard code and design recovery mechanisms.
* @notice Set Transaction Guard `guard` for the Safe. Make sure you trust the guard.
* @param guard The address of the guard to be used or the 0 address to disable the guard
*/
function setGuard(address guard) external authorized {
if (guard != address(0)) {
require(Guard(guard).supportsInterface(type(Guard).interfaceId), "GS300");
}
bytes32 slot = GUARD_STORAGE_SLOT;
// solhint-disable-next-line no-inline-assembly
assembly {
sstore(slot, guard)
}
emit ChangedGuard(guard);
}
/**
* @dev Internal method to retrieve the current guard
* We do not have a public method because we're short on bytecode size limit,
* to retrieve the guard address, one can use `getStorageAt` from `StorageAccessible` contract
* with the slot `GUARD_STORAGE_SLOT`
* @return guard The address of the guard
*/
function getGuard() internal view returns (address guard) {
bytes32 slot = GUARD_STORAGE_SLOT;
// solhint-disable-next-line no-inline-assembly
assembly {
guard := sload(slot)
}
}
}FallbackManager
FallbackManager는 정의되지 않은 함수 호출(e.g. 잘못된 함수 서명, 미지원 인터페이스 등)을 처리할 수 있도록 별도의 핸들러 계약으로 delegate한다.
Safe자체를 Handler로 지정하면 안된다. 공격자가 3바이트짜리 잘못한 함수 signature를 호출하면 Safe에 정의되지 않았으므로 fallback으로 진입한다. FallbackManager가 이 호출을 핸들러에 위임하여 msg.sender를 calldata에 추가한다. 이 추가된 1바이트가 붙어 새로운 4바이트 함수 signature로 해석되어, 공격자는 자신이 의도한 함수로 핸들러를 호출할 수 있게 돼서 내부 접근 권한을 우회할 수 있다.
require(handler != address(this), "GS400");
handler가 설정된 경우, 호출 데이터를 복사하고 msg.sender를 뒤에 붙인다.(20bytes) 해당 데이터를 handler 계약으로 전달한다.
/contracts/base/FallbackManager.sol
// SPDX-License-Identifier: LGPL-3.0-only
pragma solidity >=0.7.0 <0.9.0;
import "../common/SelfAuthorized.sol";
/**
* @title Fallback Manager - A contract managing fallback calls made to this contract
* @author Richard Meissner - @rmeissner
*/
abstract contract FallbackManager is SelfAuthorized {
event ChangedFallbackHandler(address indexed handler);
// keccak256("fallback_manager.handler.address")
bytes32 internal constant FALLBACK_HANDLER_STORAGE_SLOT = 0x6c9a6c4a39284e37ed1cf53d337577d14212a4870fb976a4366c693b939918d5;
/**
* @notice Internal function to set the fallback handler.
* @param handler contract to handle fallback calls.
*/
function internalSetFallbackHandler(address handler) internal {
/*
If a fallback handler is set to self, then the following attack vector is opened:
Imagine we have a function like this:
function withdraw() internal authorized {
withdrawalAddress.call.value(address(this).balance)("");
}
If the fallback method is triggered, the fallback handler appends the msg.sender address to the calldata and calls the fallback handler.
A potential attacker could call a Safe with the 3 bytes signature of a withdraw function. Since 3 bytes do not create a valid signature,
the call would end in a fallback handler. Since it appends the msg.sender address to the calldata, the attacker could craft an address
where the first 3 bytes of the previous calldata + the first byte of the address make up a valid function signature. The subsequent call would result in unsanctioned access to Safe's internal protected methods.
For some reason, solidity matches the first 4 bytes of the calldata to a function signature, regardless if more data follow these 4 bytes.
*/
require(handler != address(this), "GS400");
bytes32 slot = FALLBACK_HANDLER_STORAGE_SLOT;
// solhint-disable-next-line no-inline-assembly
assembly {
sstore(slot, handler)
}
}
/**
* @notice Set Fallback Handler to `handler` for the Safe.
* @dev Only fallback calls without value and with data will be forwarded.
* This can only be done via a Safe transaction.
* Cannot be set to the Safe itself.
* @param handler contract to handle fallback calls.
*/
function setFallbackHandler(address handler) public authorized {
internalSetFallbackHandler(handler);
emit ChangedFallbackHandler(handler);
}
// @notice Forwards all calls to the fallback handler if set. Returns 0 if no handler is set.
// @dev Appends the non-padded caller address to the calldata to be optionally used in the handler
// The handler can make us of `HandlerContext.sol` to extract the address.
// This is done because in the next call frame the `msg.sender` will be FallbackManager's address
// and having the original caller address may enable additional verification scenarios.
// solhint-disable-next-line payable-fallback,no-complex-fallback
fallback() external {
bytes32 slot = FALLBACK_HANDLER_STORAGE_SLOT;
// solhint-disable-next-line no-inline-assembly
assembly {
let handler := sload(slot)
if iszero(handler) {
return(0, 0)
}
calldatacopy(0, 0, calldatasize())
// The msg.sender address is shifted to the left by 12 bytes to remove the padding
// Then the address without padding is stored right after the calldata
mstore(calldatasize(), shl(96, caller()))
// Add 20 bytes for the address appended add the end
let success := call(gas(), handler, 0, 0, add(calldatasize(), 20), 0, 0)
returndatacopy(0, 0, returndatasize())
if iszero(success) {
revert(0, returndatasize())
}
return(0, returndatasize())
}
}
}execTransaction
가장 일반적인 트랜잭션 실행 방식으로, 대부분의 사용자 상호작용은 이 함수를 통해 이뤄진다.
동작 흐름
- 다중 서명 검증
- Safe에 등록된 소유자 중 최소
_threshold이상의 서명이 있어야 실행 - 서명은 EOA 또는 Smart Contract Wallet (e.g., Ledger, Trezor, zkSafe 등)으로 제출 가능
- Safe에 등록된 소유자 중 최소
- Guard 호출 (Option)
- 만약 지갑에 Guard가 설정되어 있다면,
checkTransaction()함수가 호출되어 해당 트랜잭션의 유효성을 검사 - 트랜잭션 실행 전과 후 모두 검사 가능 (
checkAfterExecution())
- 만약 지갑에 Guard가 설정되어 있다면,
- 가스 비용 처리
- 서명자 중 일부가 지정된 경우, 가스 비용을 ERC20 또는 ETH로 대납하거나 환불 처리할 수 있음
/contracts/Safe.sol
/** @notice Executes a `operation` {0: Call, 1: DelegateCall}} transaction to `to` with `value` (Native Currency)
* and pays `gasPrice` * `gasLimit` in `gasToken` token to `refundReceiver`.
* @dev The fees are always transferred, even if the user transaction fails.
* This method doesn't perform any sanity check of the transaction, such as:
* - if the contract at `to` address has code or not
* - if the `gasToken` is a contract or not
* It is the responsibility of the caller to perform such checks.
* @param to Destination address of Safe transaction.
* @param value Ether value of Safe transaction.
* @param data Data payload of Safe transaction.
* @param operation Operation type of Safe transaction.
* @param safeTxGas Gas that should be used for the Safe transaction.
* @param baseGas Gas costs that are independent of the transaction execution(e.g. base transaction fee, signature check, payment of the refund)
* @param gasPrice Gas price that should be used for the payment calculation.
* @param gasToken Token address (or 0 if ETH) that is used for the payment.
* @param refundReceiver Address of receiver of gas payment (or 0 if tx.origin).
* @param signatures Signature data that should be verified.
* Can be packed ECDSA signature ({bytes32 r}{bytes32 s}{uint8 v}), contract signature (EIP-1271) or approved hash.
* @return success Boolean indicating transaction's success.
*/
function execTransaction(
address to,
uint256 value,
bytes calldata data,
Enum.Operation operation,
uint256 safeTxGas,
uint256 baseGas,
uint256 gasPrice,
address gasToken,
address payable refundReceiver,
bytes memory signatures
) public payable virtual returns (bool success) {
bytes32 txHash;
// Use scope here to limit variable lifetime and prevent `stack too deep` errors
{
bytes memory txHashData = encodeTransactionData(
// Transaction info
to,
value,
data,
operation,
safeTxGas,
// Payment info
baseGas,
gasPrice,
gasToken,
refundReceiver,
// Signature info
nonce
);
// Increase nonce and execute transaction.
nonce++;
txHash = keccak256(txHashData);
checkSignatures(txHash, txHashData, signatures);
}
address guard = getGuard();
{
if (guard != address(0)) {
Guard(guard).checkTransaction(
// Transaction info
to,
value,
data,
operation,
safeTxGas,
// Payment info
baseGas,
gasPrice,
gasToken,
refundReceiver,
// Signature info
signatures,
msg.sender
);
}
}
// We require some gas to emit the events (at least 2500) after the execution and some to perform code until the execution (500)
// We also include the 1/64 in the check that is not send along with a call to counteract potential shortings because of EIP-150
require(gasleft() >= ((safeTxGas * 64) / 63).max(safeTxGas + 2500) + 500, "GS010");
// Use scope here to limit variable lifetime and prevent `stack too deep` errors
{
uint256 gasUsed = gasleft();
// If the gasPrice is 0 we assume that nearly all available gas can be used (it is always more than safeTxGas)
// We only substract 2500 (compared to the 3000 before) to ensure that the amount passed is still higher than safeTxGas
success = execute(to, value, data, operation, gasPrice == 0 ? (gasleft() - 2500) : safeTxGas);
gasUsed = gasUsed.sub(gasleft());
// If no safeTxGas and no gasPrice was set (e.g. both are 0), then the internal tx is required to be successful
// This makes it possible to use `estimateGas` without issues, as it searches for the minimum gas where the tx doesn't revert
require(success || safeTxGas != 0 || gasPrice != 0, "GS013");
// We transfer the calculated tx costs to the tx.origin to avoid sending it to intermediate contracts that have made calls
uint256 payment = 0;
if (gasPrice > 0) {
payment = handlePayment(gasUsed, baseGas, gasPrice, gasToken, refundReceiver);
}
if (success) emit ExecutionSuccess(txHash, payment);
else emit ExecutionFailure(txHash, payment);
}
{
if (guard != address(0)) {
Guard(guard).checkAfterExecution(txHash, success);
}
}
}execTransactionFromModule
이 함수는 모듈 실행을 위한 EntryPoint이다.
모듈 내부 로직에서 자체적으로 검증하므로, 지갑 수준의 _threshold 서명 검사를 하지 않는다. Guard가 execTransaction() 경로에서만 동작하므로, 모듈 실행은 이를 우회한다.
/contracts/base/ModuleManager.sol
/**
* @notice Execute `operation` (0: Call, 1: DelegateCall) to `to` with `value` (Native Token)
* @dev Function is virtual to allow overriding for L2 singleton to emit an event for indexing.
* @param to Destination address of module transaction.
* @param value Ether value of module transaction.
* @param data Data payload of module transaction.
* @param operation Operation type of module transaction.
* @return success Boolean flag indicating if the call succeeded.
*/
function execTransactionFromModule(
address to,
uint256 value,
bytes memory data,
Enum.Operation operation
) public virtual returns (bool success) {
// Only whitelisted modules are allowed.
require(msg.sender != SENTINEL_MODULES && modules[msg.sender] != address(0), "GS104");
// Execute transaction without further confirmations.
success = execute(to, value, data, operation, type(uint256).max);
if (success) emit ExecutionFromModuleSuccess(msg.sender);
else emit ExecutionFromModuleFailure(msg.sender);
}Handle Payments
Gnosis Safe에서는 지갑 설정 및 트랜잭션 실행 시 발생하는 가스 비용을 자동으로 처리해주는 메커니즘이 존재한다.
사용자가 ETH가 부족하거나, 지갑 설정이 어려운 경우를 대비해 relay를 사용할 수 있다. Relay를 통해 Safe를 대신 생성해주고, 대가로 ETH 또는 ERC20 토큰으로 보상을 받는다. 이를 통해 쉽게 Safe 지갑을 생성할 수 있게 한다.
트랜잭션 실행 후, 해당 실행에 사용된 가스를 계산하여 refundReceiver에게 가스 비용을 자동 보상한다. gasToken이 0이면 ETH로 보상, 그 외에는 지정된 ERC20 토큰으로 처리된다.
/contracts/Safe.sol
/**
* @notice Handles the payment for a Safe transaction.
* @param gasUsed Gas used by the Safe transaction.
* @param baseGas Gas costs that are independent of the transaction execution (e.g. base transaction fee, signature check, payment of the refund).
* @param gasPrice Gas price that should be used for the payment calculation.
* @param gasToken Token address (or 0 if ETH) that is used for the payment.
* @return payment The amount of payment made in the specified token.
*/
function handlePayment(
uint256 gasUsed,
uint256 baseGas,
uint256 gasPrice,
address gasToken,
address payable refundReceiver
) private returns (uint256 payment) {
// solhint-disable-next-line avoid-tx-origin
address payable receiver = refundReceiver == address(0) ? payable(tx.origin) : refundReceiver;
if (gasToken == address(0)) {
// For ETH we will only adjust the gas price to not be higher than the actual used gas price
payment = gasUsed.add(baseGas).mul(gasPrice < tx.gasprice ? gasPrice : tx.gasprice);
require(receiver.send(payment), "GS011");
} else {
payment = gasUsed.add(baseGas).mul(gasPrice);
require(transferToken(gasToken, receiver, payment), "GS012");
}
}Check Signatures
execTransaction()에서 가장 중요한 단계는 서명 검증이다. checkNSignatures() 함수를 통해 처리한다.
- 서명 개수 및 형식 확인
- 각 서명에 대해 서명 방식(v 값)에 따라 다음 4가지 유형 중 하나로 분기 처리
-
v == 0: 컨트랙트 서명 (EIP-1271)
- 소유자가 EOA가 아니라 스마트 컨트랙트일 경우 EIP-1271을 따르는 계약의
isValidSignature(hash, signature)를 호출하여 검증 EIP1271_MAGIC_VALUE값을 반환하면 유효한 서명으로 간주
- 소유자가 EOA가 아니라 스마트 컨트랙트일 경우 EIP-1271을 따르는 계약의
-
v == 1: 사전 승인된 해시 방식 (approveHash)
- 소유자가 approveHash()로 특정 해시를 미리 승인했을 경우 또는 현재 호출자가 서명자(owner) 본인일 경우 자동으로 허용
- 해당 함수를 통해 특정 해시를 서명 없이 사전 승인 가능
/** * @notice Marks hash `hashToApprove` as approved. * @dev This can be used with a pre-approved hash transaction signature. * IMPORTANT: The approved hash stays approved forever. There's no revocation mechanism, so it behaves similarly to ECDSA signatures * @param hashToApprove The hash to mark as approved for signatures that are verified by this contract. */ function approveHash(bytes32 hashToApprove) external { require(owners[msg.sender] != address(0), "GS030"); approvedHashes[msg.sender][hashToApprove] = 1; emit ApproveHash(hashToApprove, msg.sender); }
-
2 ≤ v ≤ 30: 표준 ECDSA 서명
- 일반적인 EOA 주소가 signTypedData, personal_sign 등을 통해 서명한 방식
ecrecover(dataHash, v, r, s)로 서명자 주소 복원
-
v > 30: eth_sign 방식 (prefix 붙인 ECDSA)
- eth_sign 방식은 서명 전에 특정 접두어를 추가
- `"\x19Ethereum Signed Message:\n32" + dataHash
/contracts/Safe.sol
/**
* @notice Checks whether the signature provided is valid for the provided data and hash. Reverts otherwise.
* @dev Since the EIP-1271 does an external call, be mindful of reentrancy attacks.
* @param dataHash Hash of the data (could be either a message hash or transaction hash)
* @param data That should be signed (this is passed to an external validator contract)
* @param signatures Signature data that should be verified.
* Can be packed ECDSA signature ({bytes32 r}{bytes32 s}{uint8 v}), contract signature (EIP-1271) or approved hash.
* @param requiredSignatures Amount of required valid signatures.
*/
function checkNSignatures(bytes32 dataHash, bytes memory data, bytes memory signatures, uint256 requiredSignatures) public view {
// Check that the provided signature data is not too short
require(signatures.length >= requiredSignatures.mul(65), "GS020");
// There cannot be an owner with address 0.
address lastOwner = address(0);
address currentOwner;
uint8 v;
bytes32 r;
bytes32 s;
uint256 i;
for (i = 0; i < requiredSignatures; i++) {
(v, r, s) = signatureSplit(signatures, i);
if (v == 0) {
require(keccak256(data) == dataHash, "GS027");
// If v is 0 then it is a contract signature
// When handling contract signatures the address of the contract is encoded into r
currentOwner = address(uint160(uint256(r)));
// Check that signature data pointer (s) is not pointing inside the static part of the signatures bytes
// This check is not completely accurate, since it is possible that more signatures than the threshold are send.
// Here we only check that the pointer is not pointing inside the part that is being processed
require(uint256(s) >= requiredSignatures.mul(65), "GS021");
// Check that signature data pointer (s) is in bounds (points to the length of data -> 32 bytes)
require(uint256(s).add(32) <= signatures.length, "GS022");
// Check if the contract signature is in bounds: start of data is s + 32 and end is start + signature length
uint256 contractSignatureLen;
// solhint-disable-next-line no-inline-assembly
assembly {
contractSignatureLen := mload(add(add(signatures, s), 0x20))
}
require(uint256(s).add(32).add(contractSignatureLen) <= signatures.length, "GS023");
// Check signature
bytes memory contractSignature;
// solhint-disable-next-line no-inline-assembly
assembly {
// The signature data for contract signatures is appended to the concatenated signatures and the offset is stored in s
contractSignature := add(add(signatures, s), 0x20)
}
require(ISignatureValidator(currentOwner).isValidSignature(data, contractSignature) == EIP1271_MAGIC_VALUE, "GS024");
} else if (v == 1) {
// If v is 1 then it is an approved hash
// When handling approved hashes the address of the approver is encoded into r
currentOwner = address(uint160(uint256(r)));
// Hashes are automatically approved by the sender of the message or when they have been pre-approved via a separate transaction
require(msg.sender == currentOwner || approvedHashes[currentOwner][dataHash] != 0, "GS025");
} else if (v > 30) {
// If v > 30 then default va (27,28) has been adjusted for eth_sign flow
// To support eth_sign and similar we adjust v and hash the messageHash with the Ethereum message prefix before applying ecrecover
currentOwner = ecrecover(keccak256(abi.encodePacked("\x19Ethereum Signed Message:\n32", dataHash)), v - 4, r, s);
} else {
// Default is the ecrecover flow with the provided data hash
// Use ecrecover with the messageHash for EOA signatures
currentOwner = ecrecover(dataHash, v, r, s);
}
require(currentOwner > lastOwner && owners[currentOwner] != address(0) && currentOwner != SENTINEL_OWNERS, "GS026");
lastOwner = currentOwner;
}
}
