프로젝트 때 cloudFormation 이용하면 좋을 듯.
IaC
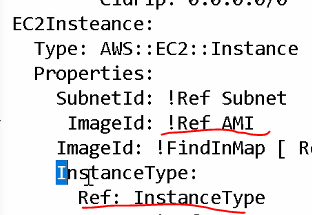
느낌표 있으면 한줄로 표현가능, 없으면 줄바꾸고 표현가능
cloudformation VPC, EC2 한번에 만들기
// 파일명 all.yaml
AWSTemplateFormatVersion: 2010-09-09
Resources:
VPC:
Type: AWS::EC2::VPC
Properties:
CidrBlock: 192.168.0.0/16
EnableDnsSupport: true
EnableDnsHostnames: true
InstanceTenancy: default
Tags:
- Key: Name
Value: NEW-VPC
SubnetA:
Type: AWS::EC2::Subnet
Properties:
AvailabilityZone: ap-northeast-2a
VpcId: !Ref VPC
CidrBlock: 192.168.0.0/20
MapPublicIpOnLaunch: true
Tags:
- Key: Name
Value: NEW-PUBLIC-SUBNET-2A
SubnetB:
Type: AWS::EC2::Subnet
Properties:
AvailabilityZone: ap-northeast-2b
VpcId: !Ref VPC
CidrBlock: 192.168.16.0/20
MapPublicIpOnLaunch: true
Tags:
- Key: Name
Value: NEW-PUBLIC-SUBNET-2B
SubnetC:
Type: AWS::EC2::Subnet
Properties:
AvailabilityZone: ap-northeast-2c
VpcId: !Ref VPC
CidrBlock: 192.168.32.0/20
MapPublicIpOnLaunch: true
Tags:
- Key: Name
Value: NEW-PUBLIC-SUBNET-2C
SubnetD:
Type: AWS::EC2::Subnet
Properties:
AvailabilityZone: ap-northeast-2d
VpcId: !Ref VPC
CidrBlock: 192.168.48.0/20
MapPublicIpOnLaunch: true
Tags:
- Key: Name
Value: NEW-PUBLIC-SUBNET-2D
InternetGateway:
Type: AWS::EC2::InternetGateway
Properties:
Tags:
- Key: Name
Value: NEW-IGW
VPCGatewayAttachment:
Type: AWS::EC2::VPCGatewayAttachment
Properties:
VpcId: !Ref VPC
InternetGatewayId: !Ref InternetGateway
RouteTableA:
Type: AWS::EC2::RouteTable
Properties:
VpcId: !Ref VPC
Tags:
- Key: Name
Value: NEW-PUBLIC-RTB
InternetRoute:
Type: AWS::EC2::Route
DependsOn: InternetGateway
Properties:
DestinationCidrBlock: 0.0.0.0/0
GatewayId: !Ref InternetGateway
RouteTableId: !Ref RouteTableA
SubnetARouteTableAssociation:
Type: AWS::EC2::SubnetRouteTableAssociation
Properties:
RouteTableId: !Ref RouteTableA
SubnetId: !Ref SubnetA
SubnetBRouteTableAssociation:
Type: AWS::EC2::SubnetRouteTableAssociation
Properties:
RouteTableId: !Ref RouteTableA
SubnetId: !Ref SubnetB
SubnetCRouteTableAssociation:
Type: AWS::EC2::SubnetRouteTableAssociation
Properties:
RouteTableId: !Ref RouteTableA
SubnetId: !Ref SubnetC
SubnetDRouteTableAssociation:
Type: AWS::EC2::SubnetRouteTableAssociation
Properties:
RouteTableId: !Ref RouteTableA
SubnetId: !Ref SubnetD
Mappings:
RegionMap:
ap-northeast-2:
AMIID: ami-0fd0765afb77bcca7
ap-northeast-1:
AMIID: ami-0b7546e839d7ace12
Parameters:
InstanceTypeParameter:
Type: String
Default: t2.micro
Description: Enter instance size. Default is t2.micro
# VPC:
# Type: String
# Default: vpc-01a276b266db7833b
# Description: VPC ID.
# Subnet:
# Type: String
# Default: subnet-01132b9dddcf71d3d
# Description: Subnet ID.
AMI:
Type: String
Default: AMIID
Description: The Linux AMI to use.
Key:
Type: String
Default: new-key
Description: The key used to access the instance.
Resources:
InstanceSecurityGroup:
Type: AWS::EC2::SecurityGroup
Properties:
GroupName: "NEW-SG-WEB"
GroupDescription: "NEW-SG-WEB"
VpcId: !Ref VPC
SecurityGroupIngress:
- IpProtocol: tcp
FromPort: '80'
ToPort: '80'
CidrIp: 0.0.0.0/0
- IpProtocol: tcp
FromPort: '22'
ToPort: '22'
CidrIp: 123.142.252.25/32
- IpProtocol: icmp
FromPort: '-1'
ToPort: '-1'
CidrIp: 0.0.0.0/0
SecurityGroupEgress:
- IpProtocol: -1
CidrIp: 0.0.0.0/0
Linux:
Type: 'AWS::EC2::Instance'
Properties:
SubnetId: !Ref SubnetA
# ImageId: !Ref AMI
ImageId: !FindInMap [ RegionMap, !Ref "AWS::Region", !Ref AMI ]
InstanceType:
Ref: InstanceTypeParameter
KeyName: !Ref Key
SecurityGroupIds:
- Ref: InstanceSecurityGroup
BlockDeviceMappings:
- DeviceName: /dev/xvda
Ebs:
VolumeSize: 8
- DeviceName: /dev/xvdb
Ebs:
VolumeSize: 8
Tags:
- Key: Name
Value: NEW-EC2
UserData:
Fn::Base64: |
#cloud-boothook
#!/bin/bash
yum install -y httpd
systemctl enable --now httpd
echo "Hello World!" > /var/www/html/index.html
Outputs:
PublicIp:
Description: PublicIp Output
Value: {"Fn::GetAtt": ["Linux","PublicIp"]}테라폼 terraform
vpc 만들기
콘솔에선 라우팅 테이블을 만들고 나서 라우팅 정보를 넣어주어야함
테라폼은 라우팅을 만들고 동시에 라우팅 정보를 넣어줌
--- vpc 만들기
# vi new-vpc.tf
provider "aws" {
region = "ap-northeast-2"
}
data "aws_availability_zones" "available" {
state = "available"
}
resource "aws_vpc" "new_vpc" {
cidr_block = "192.168.0.0/16"
enable_dns_hostnames = true
enable_dns_support = true
instance_tenancy = "default"
tags = {
Name = "NEW-VPC"
}
}
resource "aws_subnet" "new_public_subnet_2a" {
vpc_id = aws_vpc.new_vpc.id
cidr_block = "192.168.0.0/20"
map_public_ip_on_launch = true
availability_zone = data.aws_availability_zones.available.names[0]
tags = {
Name = "NEW-PUBLIC-SUBNET-2A"
}
}
resource "aws_subnet" "new_public_subnet_2b" {
vpc_id = aws_vpc.new_vpc.id
cidr_block = "192.168.16.0/20"
map_public_ip_on_launch = true
availability_zone = data.aws_availability_zones.available.names[1]
tags = {
Name = "NEW-PUBLIC-SUBNET-2B"
}
}
resource "aws_subnet" "new_public_subnet_2c" {
vpc_id = aws_vpc.new_vpc.id
cidr_block = "192.168.32.0/20"
map_public_ip_on_launch = true
availability_zone = data.aws_availability_zones.available.names[2]
tags = {
Name = "NEW-PUBLIC-SUBNET-2C"
}
}
resource "aws_subnet" "new_public_subnet_2d" {
vpc_id = aws_vpc.new_vpc.id
cidr_block = "192.168.48.0/20"
map_public_ip_on_launch = true
availability_zone = data.aws_availability_zones.available.names[3]
tags = {
Name = "NEW-PUBLIC-SUBNET-2D"
}
}
resource "aws_internet_gateway" "new_igw" {
vpc_id = aws_vpc.new_vpc.id
tags = {
Name = "NEW-IGW"
}
}
resource "aws_route_table" "new_public_rtb" {
vpc_id = aws_vpc.new_vpc.id
route {
cidr_block = "0.0.0.0/0"
gateway_id = aws_internet_gateway.new_igw.id
}
tags = {
Name = "NEW-PUBLIC-RTB"
}
}
resource "aws_route_table_association" "new_public_subnet_2a_association" {
subnet_id = aws_subnet.new_public_subnet_2a.id
route_table_id = aws_route_table.new_public_rtb.id
}
resource "aws_route_table_association" "new_public_subnet_2b_association" {
subnet_id = aws_subnet.new_public_subnet_2b.id
route_table_id = aws_route_table.new_public_rtb.id
}
resource "aws_route_table_association" "new_public_subnet_2c_association" {
subnet_id = aws_subnet.new_public_subnet_2c.id
route_table_id = aws_route_table.new_public_rtb.id
}
resource "aws_route_table_association" "new_public_subnet_2d_association" {
subnet_id = aws_subnet.new_public_subnet_2d.id
route_table_id = aws_route_table.new_public_rtb.id
}ec2 만들기
vi new-ec2.tf
provider "aws" {
region = "ap-northeast-2"
}
/** 수정사항
data "aws_vpc" "new_vpc" {
tags = {
Name = "NEW-VPC"
}
}
data "aws_subnet" "apne2_az1" {
tags = {
Name = "NEW-PUBLIC-SUBNET-2A"
}
}
**/
resource "aws_instance" "example" {
ami = "ami-0fd0765afb77bcca7"
instance_type = "t2.micro"
subnet_id = data.aws_subnet.apne2_az1.id // 아이디를 가져올 땐 큰따옴표 스면 안됨.
vpc_security_group_ids = [aws_security_group.instance.id]
key_name = "new-key"
user_data = <<-EOF
#!/bin/bash
yum install -y httpd
systemctl enable --now httpd
echo "Hello, Terraform" > /var/www/html/index.html
EOF
tags = {
Name = "terraform-example"
}
}
resource "aws_security_group" "instance" {
name = var.security_group_name
vpc_id = data.aws_vpc.new_vpc.id // 수정사항
ingress {
from_port = 80
to_port = 80
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
ingress {
from_port = 22
to_port = 22
protocol = "tcp"
cidr_blocks = ["123.142.252.25/32"]
}
ingress {
from_port = -1
to_port = -1
protocol = "icmp"
cidr_blocks = ["0.0.0.0/0"]
}
egress {
from_port = 0
to_port = 0
protocol = "-1"
cidr_blocks = ["0.0.0.0/0"]
}
tags = {
Name = "terraform-sg"
}
}
variable "security_group_name" {
description = "The name of the security group"
type = string
default = "terraform-example-instance"
}
output "public_ip" {
value = aws_instance.example.public_ip
description = "The public IP of the Instance"
}
output "public_dns" {
value = aws_instance.example.public_dns
description = "The Public dns of the Instance"
}
output "private_ip" {
value = aws_instance.example.private_ip
description = "The Private_ip of the Instance"
}ALB 만들기
Life cycle : 기본 인스턴스니까 지우지마라는 설정
health check 경로지정해주면 *.html 파일이 q반드시 있어야한다.
provider "aws" {
region = "ap-northeast-2"
}
data "aws_availability_zones" "available" {
state = "available"
}
resource "aws_vpc" "new_vpc" {
cidr_block = "192.168.0.0/16"
enable_dns_hostnames = true
enable_dns_support = true
instance_tenancy = "default"
tags = {
Name = "NEW-VPC"
}
}
resource "aws_subnet" "new_public_subnet_2a" {
vpc_id = aws_vpc.new_vpc.id
cidr_block = "192.168.0.0/20"
map_public_ip_on_launch = true
availability_zone = data.aws_availability_zones.available.names[0]
tags = {
Name = "NEW-PUBLIC-SUBNET-2A"
}
}
resource "aws_subnet" "new_public_subnet_2b" {
vpc_id = aws_vpc.new_vpc.id
cidr_block = "192.168.16.0/20"
map_public_ip_on_launch = true
availability_zone = data.aws_availability_zones.available.names[1]
tags = {
Name = "NEW-PUBLIC-SUBNET-2B"
}
}
resource "aws_subnet" "new_public_subnet_2c" {
vpc_id = aws_vpc.new_vpc.id
cidr_block = "192.168.32.0/20"
map_public_ip_on_launch = true
availability_zone = data.aws_availability_zones.available.names[2]
tags = {
Name = "NEW-PUBLIC-SUBNET-2C"
}
}
resource "aws_subnet" "new_public_subnet_2d" {
vpc_id = aws_vpc.new_vpc.id
cidr_block = "192.168.48.0/20"
map_public_ip_on_launch = true
availability_zone = data.aws_availability_zones.available.names[3]
tags = {
Name = "NEW-PUBLIC-SUBNET-2D"
}
}
resource "aws_internet_gateway" "new_igw" {
vpc_id = aws_vpc.new_vpc.id
tags = {
Name = "NEW-IGW"
}
}
resource "aws_route_table" "new_public_rtb" {
vpc_id = aws_vpc.new_vpc.id
route {
cidr_block = "0.0.0.0/0"
gateway_id = aws_internet_gateway.new_igw.id
}
tags = {
Name = "NEW-PUBLIC-RTB"
}
}
resource "aws_route_table_association" "new_public_subnet_2a_association" {
subnet_id = aws_subnet.new_public_subnet_2a.id
route_table_id = aws_route_table.new_public_rtb.id
}
resource "aws_route_table_association" "new_public_subnet_2b_association" {
subnet_id = aws_subnet.new_public_subnet_2b.id
route_table_id = aws_route_table.new_public_rtb.id
}
resource "aws_route_table_association" "new_public_subnet_2c_association" {
subnet_id = aws_subnet.new_public_subnet_2c.id
route_table_id = aws_route_table.new_public_rtb.id
}
resource "aws_route_table_association" "new_public_subnet_2d_association" {
subnet_id = aws_subnet.new_public_subnet_2d.id
route_table_id = aws_route_table.new_public_rtb.id
}
#data "aws_vpc" "new_vpc" {
# tags = {
# Name = "NEW-VPC"
# }
#}
#data "aws_subnet" "apne2_az1" {
# tags = {
# Name = "NEW-PUBLIC-SUBNET-2A"
# }
#}
#data "aws_subnet" "apne2_az3" {
# tags = {
# Name = "NEW-PUBLIC-SUBNET-2C"
# }
#}
variable "security_group_name" {
description = "The name of the security group"
type = string
default = "NEW-SG-ALB"
}
resource "aws_security_group" "new_sg_alb" {
name = var.security_group_name
# vpc_id = data.aws_vpc.new_vpc.id
vpc_id = aws_vpc.new_vpc.id
ingress {
from_port = 80
to_port = 80
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
ingress {
from_port = 443
to_port = 443
protocol = "tcp"
cidr_blocks = ["0.0.0.0/0"]
}
egress {
from_port = 0
to_port = 0
protocol = "-1"
cidr_blocks = ["0.0.0.0/0"]
}
tags = {
Name = "NEW-SG-ALB"
}
}
resource "aws_lb" "frontend" {
name = "alb-example"
internal = false
load_balancer_type = "application"
security_groups = aws_security_group.new_sg_alb.id
subnets = [
aws_subnet.new_public_subnet_2a.id,
aws_subnet.new_public_subnet_2c.id
]
tags = {
Name = "NEW-ALB"
}
lifecycle { create_before_destroy = true }
}
resource "aws_instance" "alb_vm_01" {
ami = "ami-0fd0765afb77bcca7"
instance_type = "t2.micro"
subnet_id = aws_subnet.new_public_subnet_2a.id
vpc_security_group_ids = aws_security_group.new_sg_alb.id
key_name = "new-key"
user_data = <<-EOF
#! /bin/bash
yum install -y httpd
systemctl enable --now httpd
echo "Hello, Terraform01" > /var/www/html/index.html
EOF
tags = {
Name = "ALB01"
}
}
resource "aws_instance" "alb_vm_02" {
ami = "ami-0fd0765afb77bcca7"
instance_type = "t2.micro"
subnet_id = aws_subnet.new_public_subnet_2c.id
vpc_security_group_ids = aws_security_group.new_sg_alb.id
key_name = "new-key"
user_data = <<-EOF
#! /bin/bash
yum install -y httpd
systemctl enable --now httpd
echo "Hello, Terraform02" > /var/www/html/index.html
EOF
tags = {
Name = "ALB02"
}
}
resource "aws_lb_target_group" "tg" {
name = "TargetGroup"
port = 80
target_type = "instance"
protocol = "HTTP"
vpc_id = aws_vpc.new_vpc.id
health_check {
path = "/"
protocol = "HTTP"
matcher = "200"
interval = 15
timeout = 3
healthy_threshold = 2
unhealthy_threshold = 2
}
}
resource "aws_alb_target_group_attachment" "tgattachment01" {
target_group_arn = aws_lb_target_group.tg.arn
target_id = aws_instance.alb_vm_01.id
port = 80
}
resource "aws_alb_target_group_attachment" "tgattachment02" {
target_group_arn = aws_lb_target_group.tg.arn
target_id = aws_instance.alb_vm_02.id
port = 80
}
resource "aws_lb_listener" "front_end" {
load_balancer_arn = aws_lb.frontend.arn
port = "80"
protocol = "HTTP"
default_action {
type = "forward"
target_group_arn = aws_lb_target_group.tg.arn
}
}
output "lb_dns_name" {
description = "The DNS name of the load balancer."
value = aws_lb.frontend.dns_name
}
오류
aws s3 ls : 로그인 확인할 때 씀
terraform plan이 안됐음
시간이 안 맞았다.
yum install rdate
rdate -s time.bora.net
timedatectl set-timezone Asia/Seoul