1. Cloud
- 공용 클라우드 : AWS, GCP, Azure
- 사설 클라우드 : OpenStack(KVM, OVS)
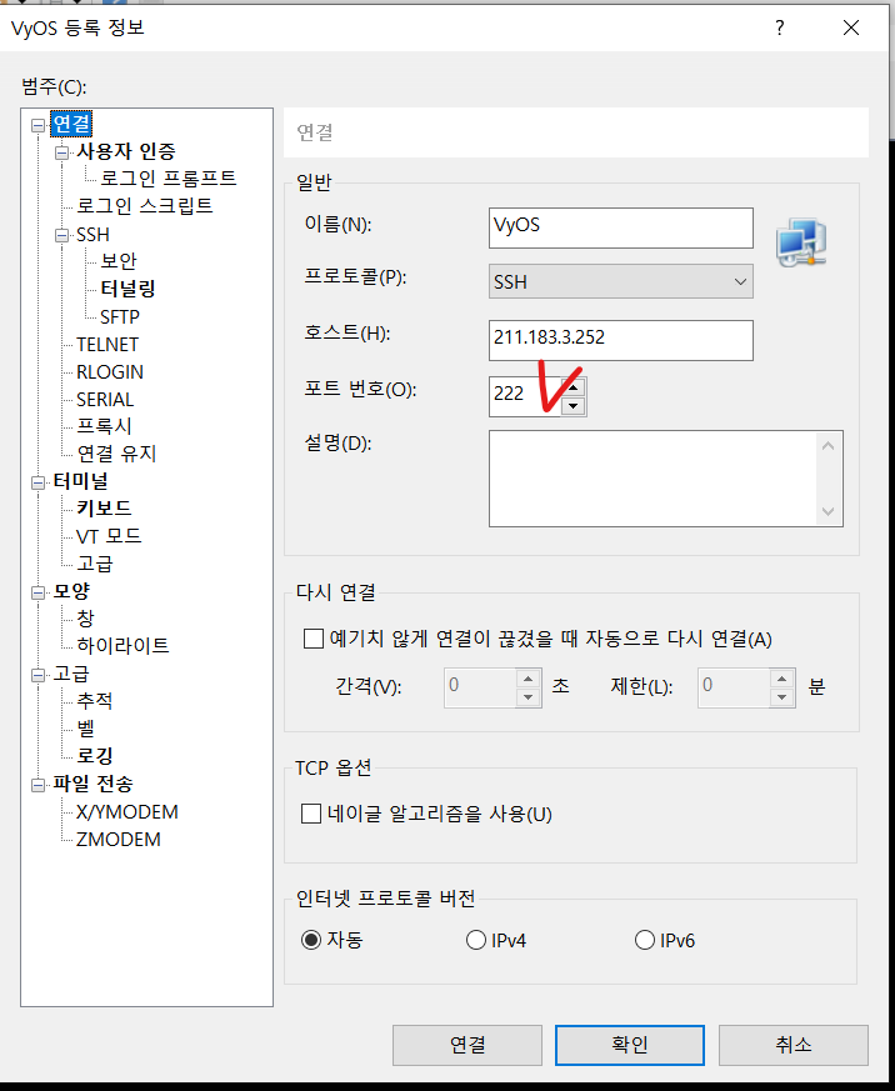
VyOS 과제 정답 : TCP 22번 포트를 열어준다 - Destination NAT 설정
- VyOS 포트 바꾸는 법
vyos@vyos# sh service ssh port
현재 ssh 포트번호 확인 명령어
vyos@vyos# set service ssh port 222
port를 222번으로 하겠다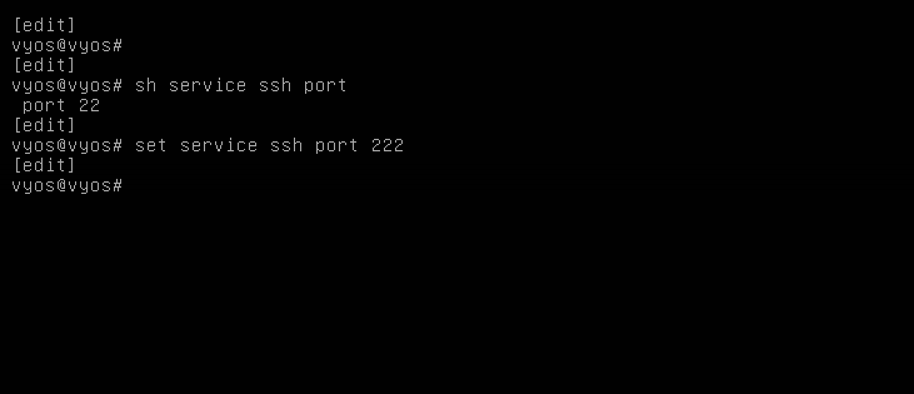
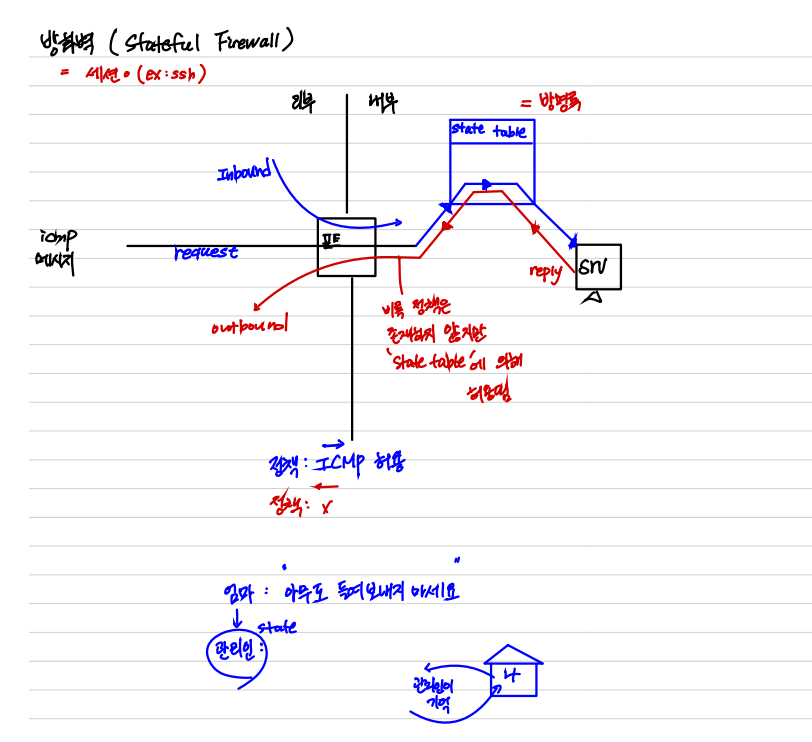
2. 방화벽(Stateful Firewall)
3. 자신만의 방화벽 정책 구현
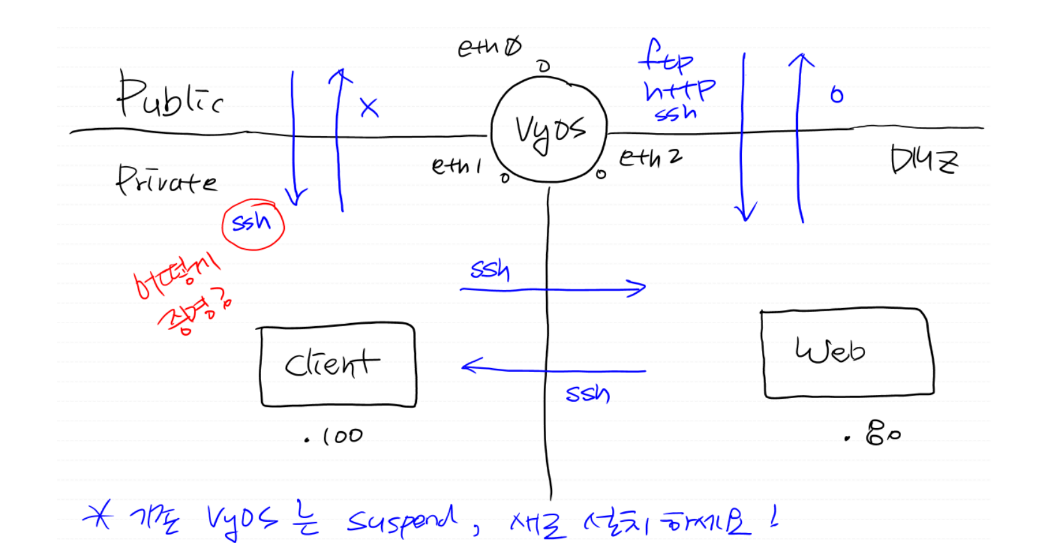
- 설계도
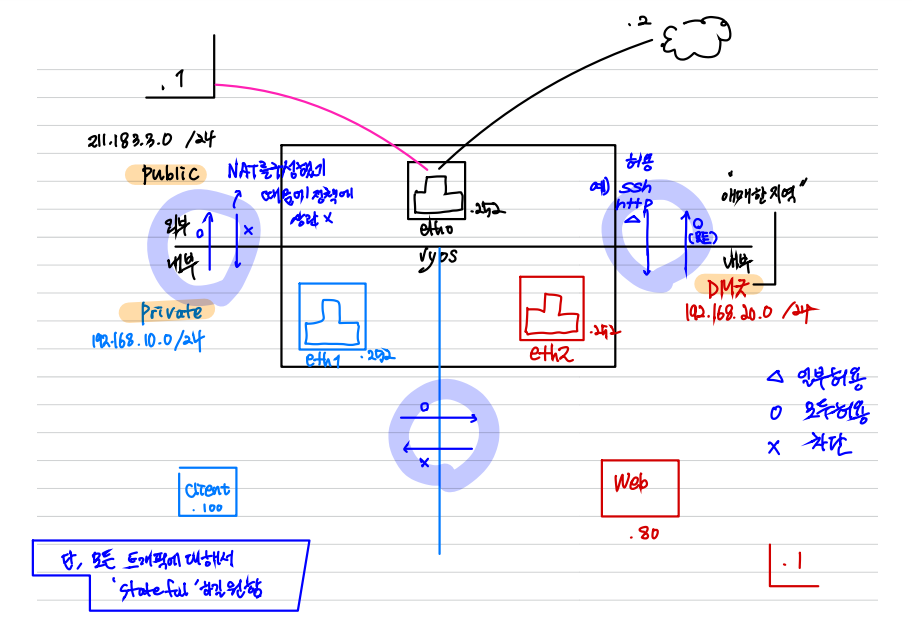
3-1 ZONE 설정하기 - 모든 트래픽이 차단됨
- 내가 의도한대로 방화벽 정책을 검증을 해봐야 한다.
- 기본적으로 아무것도 설정하지 않았을때 클라이언트와 웹이 통신이 되는지 여부를 확인해야 함
vyos@vyos# set zone-policy zone private interface eth1
vyos@vyos# commit
<항상 해줄것!>
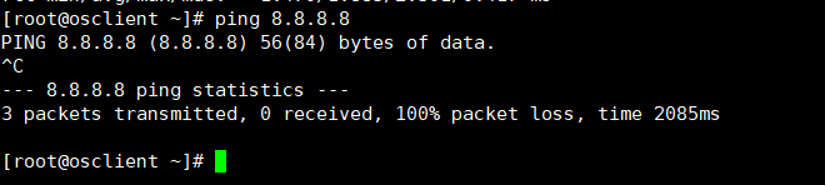
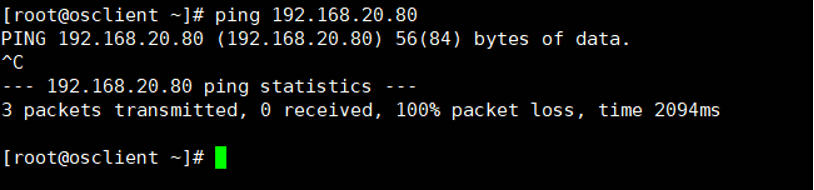
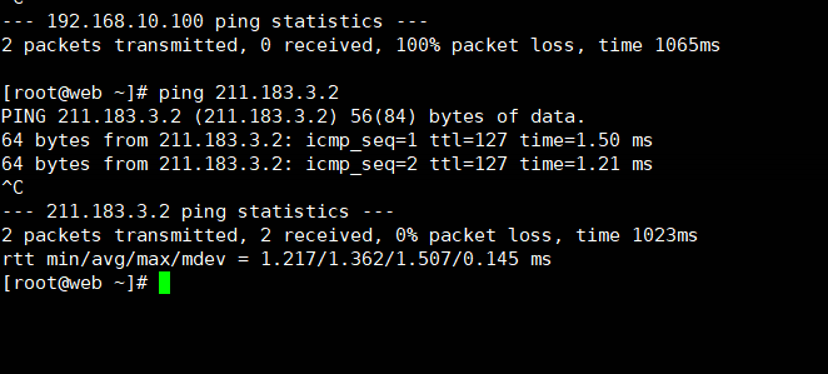
- Client 서버에서 외부 와 웹서버에 핑이 쳐지는지 확인해야 함
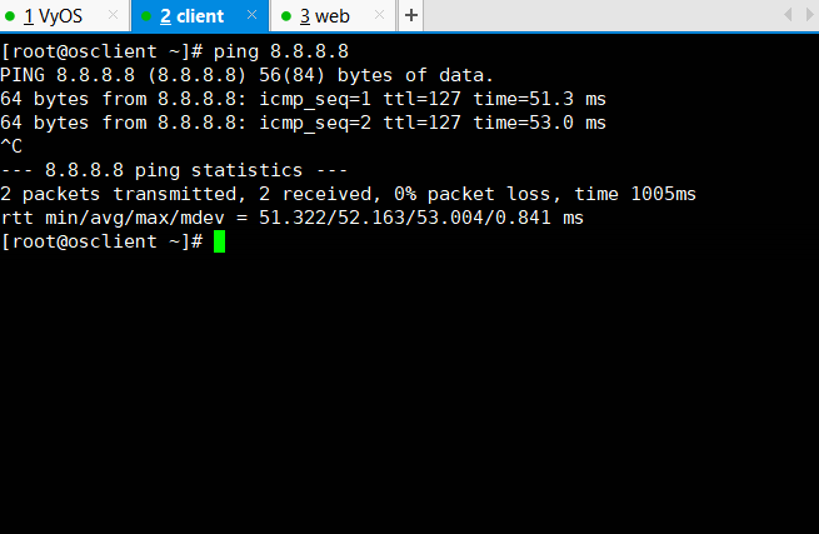
<외부에게 : ping 8.8.8.8>
 <Web서버에게 : ping 192.168.20.80>
<Web서버에게 : ping 192.168.20.80>
동일하게 DMZ, PUBLIC ZONE을 설정해줌
vyos@vyos# set zone-policy zone dmz interface eth2
vyos@vyos# commit
vyos@vyos# set zone-policy zone public interface eth0
vyos@vyos# commit
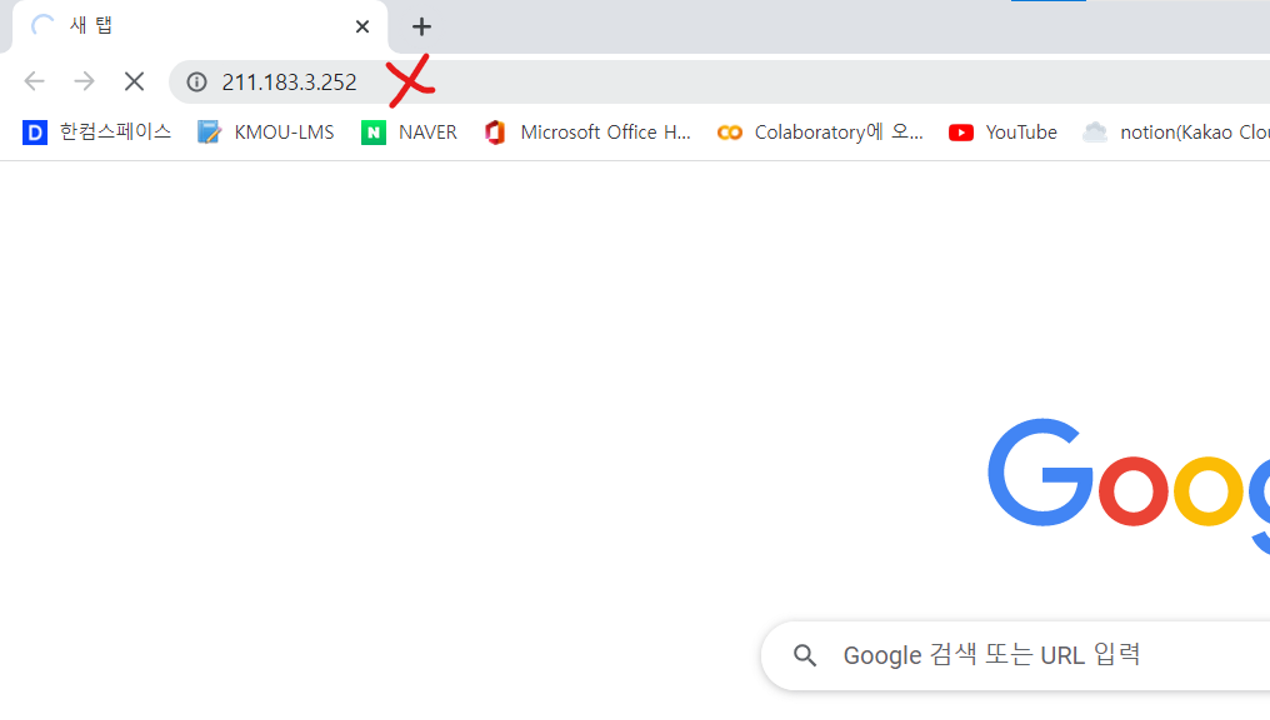
- Test
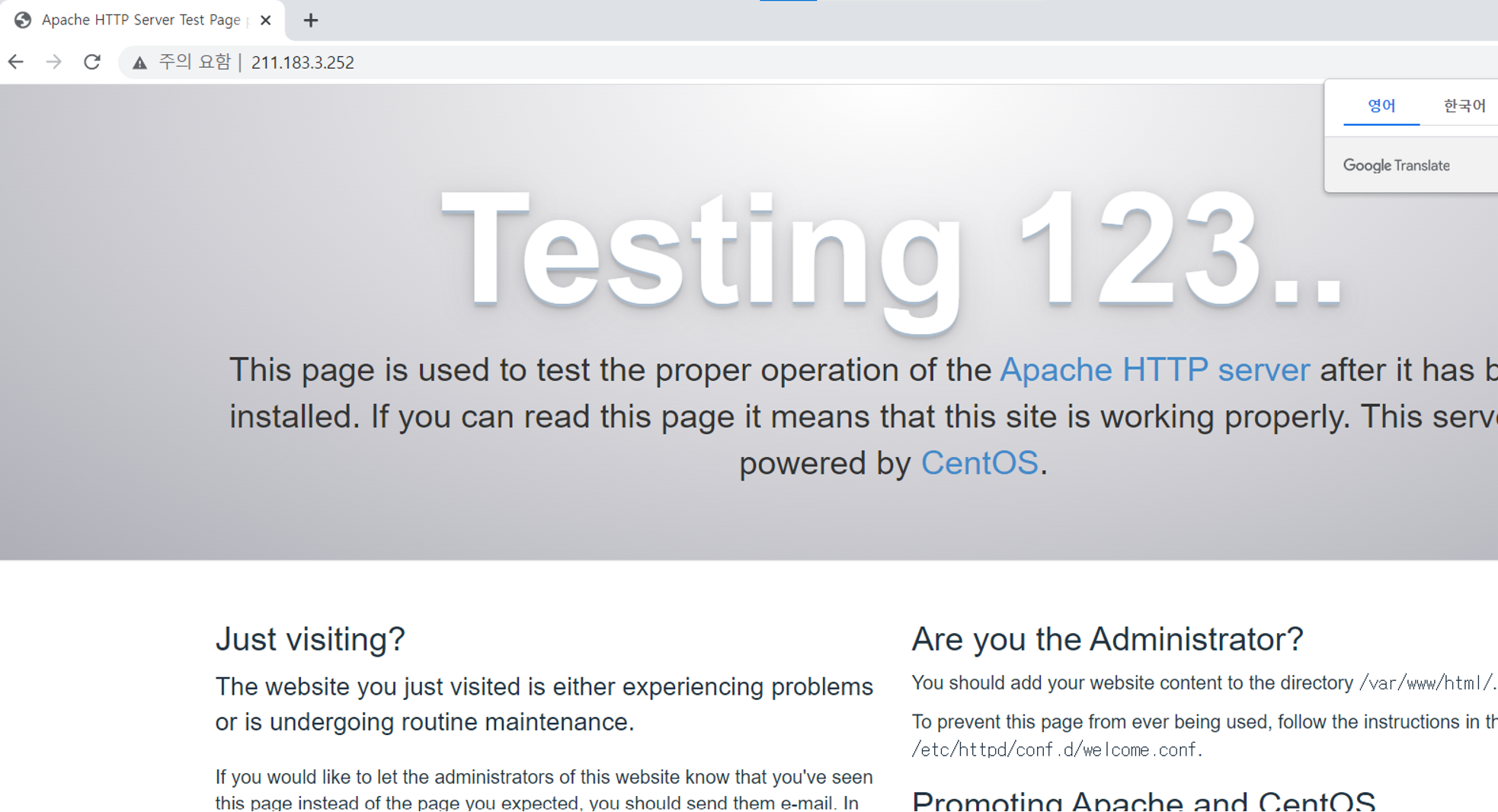
크롬 접속 창에 211.183.3.252
3-2 정책(Rule) 세우기
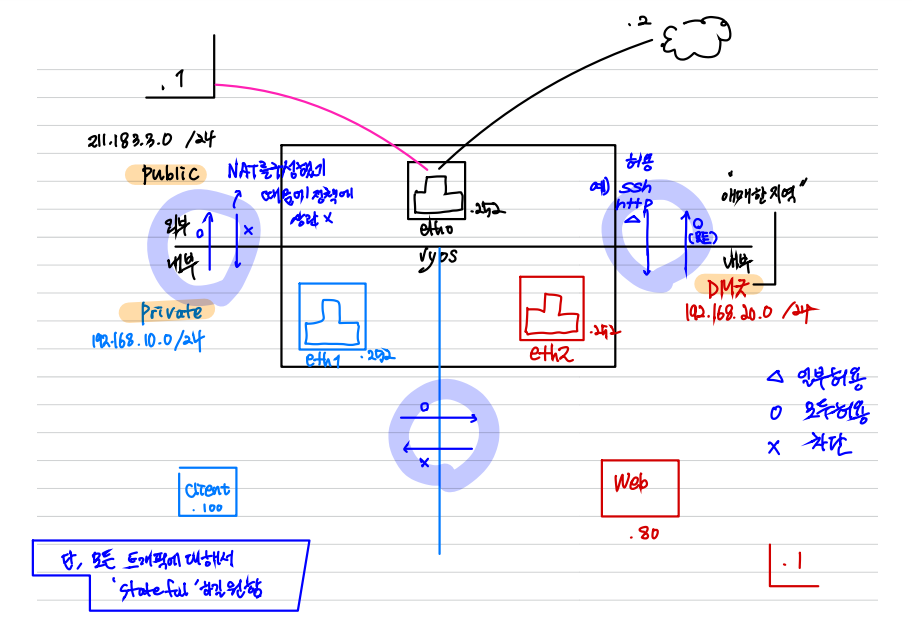
- PRIVATE -> DMZ 로 전체 허용
<모두 허용하는 정책 생성 (NAME : ALL)>
vyos@vyos# set firewall name ALL rule 10 action accept
<해당 트래픽에 반영>
vyos@vyos# set zone-policy zone dmz from private firewall name ALL
vyos@vyos# commit
<전제>
모든 트래픽에 대해서 stateful 하길 원함, dmz 입장에서 들어온 private트래픽에 대해서는
나가는 트래픽을 허용 해줘야 함
- DMZ -> PRIVATE 로 전체 거부
<인바운드 되는 트래픽에 한해 아웃바운드가 가능하도록>
vyos@vyos# set firewall STATE rule 20 action accept
vyos@vyos# set firewall STATE rule 20 state established enable
vyos@vyos# set firewall STATE rule 20 state related enable
< 해당 트래픽에 반영>
vyos@vyos# set zone-policy zone private from dmz firewall name STATE
vyos@vyos# commit-
Client 서버에서 Web Server에 핑
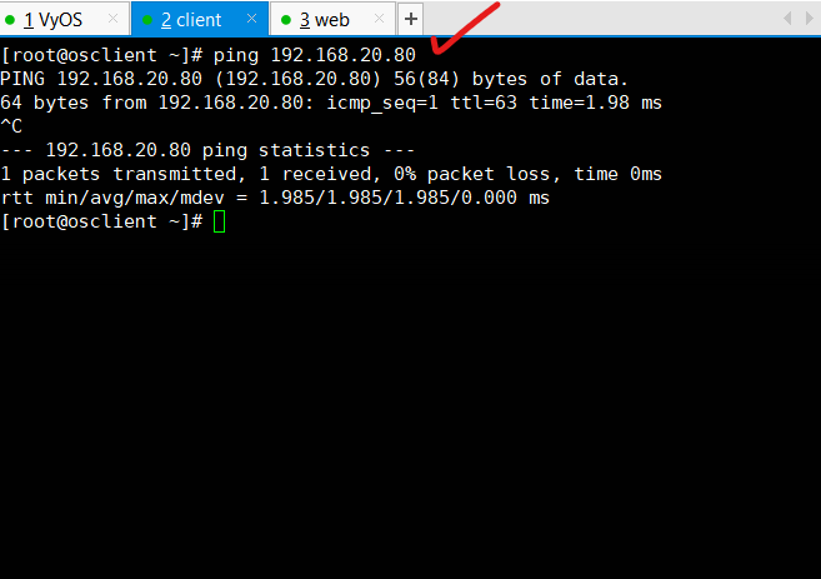
-
Web 서버에서 Client 서버에 핑
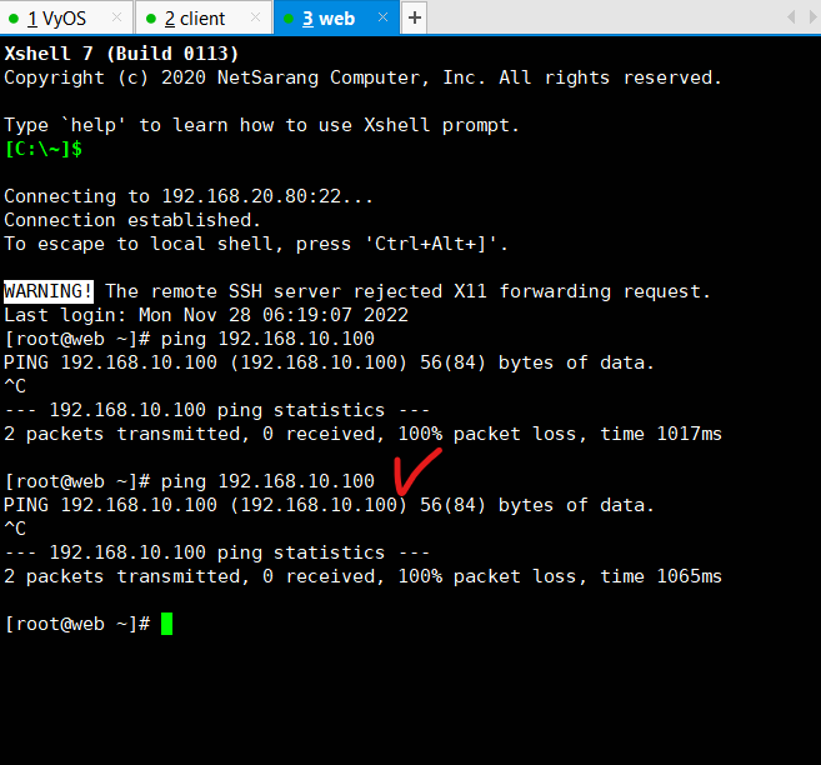
-
ALL, STATE 방화벽 생성 완료
- PRIVATE -> PUBLIC 로 전체 허용(ALL)
이미 ALL 방화벽은 생성해놓았기 때문에 해당 트래픽에 반영만 해주면 된다.
<해당 트래픽에 반영>
vyos@vyos# set zone-policy zone public from private firewall name ALL
vyos@vyos# commit
- ping 을 VyOS 밖에 있는 대상들을 검증 상대로 정하는 것이 좋다
- PUBLIC -> PRIVATE 로 전체 거부(STATE)
<인바운드 되는 트래픽에 한해 아웃바운드가 가능하도록>
vyos@vyos# set zone-policy zone private from public firewall name STATE
vyos@vyos# commit
- DMZ -> PUBLIC 로 전체 허용(ALL)
<해당 트래픽에 반영>
vyos@vyos# set zone-policy zone public from dmz firewall name ALL
vyos@vyos# commit
- Test : Web 서버에서 PUBLIC의 게이트웨이 211.183.3.2 로 핑때리기
- PUBLIC -> DMZ 로 일부허용(HTTP,SSH 허용)
<인바운드 되는 트래픽에 한해 아웃바운드가 가능하도록>
<MAKE RULE>
vyos@vyos# set firewall name SSHWEB rule 10 action accept
vyos@vyos# set firewall name SSHWEB rule 10 destination port 22,80
ssh, http 포트에 대해서만 허용
vyos@vyos# set firewall name SSHWEB rule 10 protocol tcp
<rule 20번 만들기>
vyos@vyos# set firewall name SSHWEB rule 20 action accept
vyos@vyos# set firewall name SSHWEB rule 20 state established enable
vyos@vyos# set firewall name SSHWEB rule 20 state related enable
vyos@vyos# set zone-policy zone dmz from public firewall name SSHWEB
vyos@vyos# commit- Test : 이미 데스티네이션 NAT가 걸려있기 때문에 크롬 브라우저에서 IP를 때린다.
3. Destination Port 예제 문제
- 순서
- PAT and DNAT
- SET Zone
- 정책 세우기
- 정책 반영
- Client SSH port : 2222
- Web SSH port : 22
- FTP port : 21(FTP제어), 20(데이터 전송)
- HTTP port : 80
<PAT>
vyos@vyos# set nat source rule 10 outbound-interface eth0
vyos@vyos# set nat source rule 10 source address 192.168.10.0/24
vyos@vyos# set nat source rule 10 translation address masquerade
vyos@vyos# set nat source rule 20 outbound-interface eth0
vyos@vyos# set nat source rule 20 source address 192.168.20.0/24
vyos@vyos# set nat source rule 20 translation address masquerade
<DNAT-WEB>
vyos@vyos# set nat destination rule 10 inbound-interface eth0
vyos@vyos# set nat destination rule 10 translation address 192.168.20.80
vyos@vyos# set nat destination rule 10 protocol tcp
vyos@vyos# set nat destination rule 10 destination port 20,21,22,80
<DNAT-Client>
vyos@vyos# set nat destination rule 20 inbound-interface eth0
vyos@vyos# set nat destination rule 20 translation address 192.168.10.100
vyos@vyos# set nat destination rule 20 protocol tcp
vyos@vyos# set nat destination rule 20 destination port 2222
<Zone 설정>
vyos@vyos# set zone zone private int eth1
vyos@vyos# set zone zone dmz int eth2
vyos@vyos# set zone zone public int eth0
정책
<모두 허용 = ALL>
vyos@vyos# set firewall name ALL rule 10 action accept
<모두 거부 = STATE>
vyos@vyos# set firewall name STATE rule 20 action accept
vyos@vyos# set firewall name STATE rule 20 state established enable
vyos@vyos# set firewall name STATE rule 20 state related enable
<SSH 기본 22번 포트 허용>
vyos@vyos# set firewall name SSH22 rule 30 action accept
vyos@vyos# set firewall name SSH22 rule 30 destination port 22
vyos@vyos# set firewall name SSH22 rule 30 protocol tcp
vyos@vyos# set firewall name SSH22 rule 40 action accept
vyos@vyos# set firewall name SSH22 rule 40 state established enable
vyos@vyos# set firewall name SSH22 rule 40 state related enable
<SSH 기본 2222번 포트 허용>
vyos@vyos# set firewall name SSH2222 rule 50 action accept
vyos@vyos# set firewall name SSH2222 rule 50 destination port 2222
vyos@vyos# set firewall name SSH2222 rule 50 protocol tcp
vyos@vyos# set firewall name SSH2222 rule 60 action accept
vyos@vyos# set firewall name SSH2222 rule 60 state established enable
vyos@vyos# set firewall name SSH2222 rule 60 state related enable
<FTP,HTTP,SSH 허용>
vyos@vyos# set firewall name FHS rule 70 action accept
vyos@vyos# set firewall name FHS rule 70 destination port 20,21,22,80
vyos@vyos# set firewall name FHS rule 70 protocol tcp
vyos@vyos# set firewall name FHS rule 80 action accept
vyos@vyos# set firewall name FHS rule 80 state established enable
vyos@vyos# set firewall name FHS rule 80 state related enable정책 반영
1. PRIVATE 에서 DMZ = SSH22
vyos@vyos# set zone-policy zone dmz from private firewall name SSH22
2. DMZ 에서 PRIVATE = SSH2222
vyos@vyos# set zone-policy zone private from dmz firewall name SSH2222
3. PRIVATE 에서 PUBLIC 으로. 전체 거부 = STATE
vyos@vyos# set zone-policy zone public from private firewall name STATE
4. PUBLIC 에서 PRIVATE 으로. <SSH2222>
vyos@vyos# set zone-policy zone private from public firewall name SSH2222
5. DMZ 에서 PUBLIC 으로. <전체 허용=ALL>
vyos@vyos# set zone-policy zone public from dmz firewall name ALL
6. PUBLIC 에서 DMZ 로. <FHS>
vyos@vyos# set zone-policy zone dmz from public firewall name FHS
-
FTP서버(port 21) 테스트 파일탐색기 http://211.183.3.252로 테스트
-
HTTP서버(port 80) 테스트 chrom : 211.183.3.252
-
ssh root@192.168.10.100 and ssh root@192.168.20.80
PORT 변경하는법
<sshd_config : 데몬 파일>
> vi /etc/ssh/sshd_config
ssh의 데몬파일이며 포트랄 변경할 수 있음
# port22 <- 이 부분 수정 가능
> systemctl restart sshd
> netstat -alnp
-a : tcp,udp 둘다
-l : listen
-n : 포트 번호
-p : process ID
> netstat -alnp | grep 2222
2222번 포트에 대해서 잘 열려있는지 확인하는 명령어