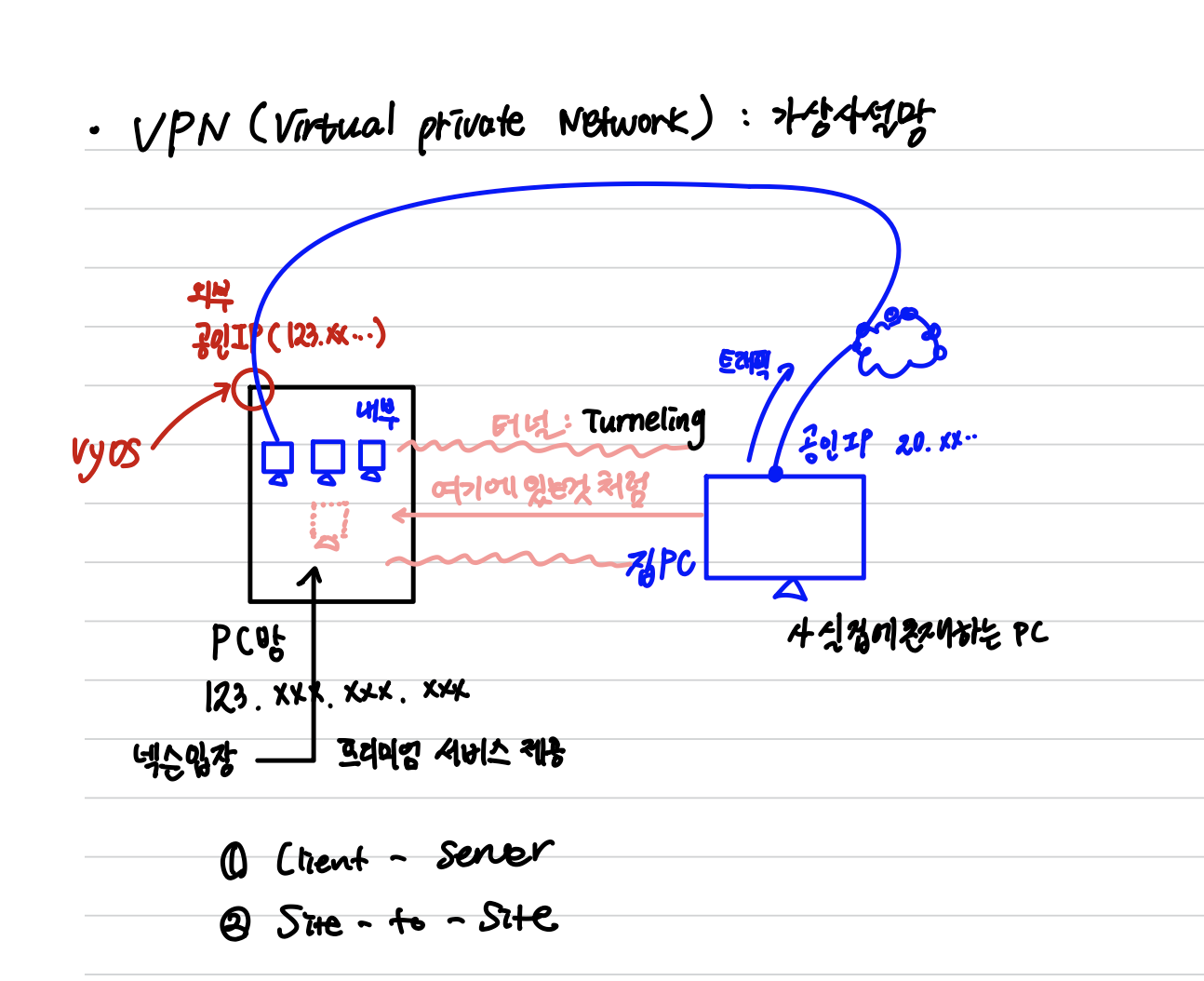
1. VPN (Virtual Private Network)
- 가상 사설망
- 마치 내가 그곳의 대역대에 놓인것 처럼
- 터널링을 통해 해당 사설네트워크에 존재하는 것처럼 동작
종류
1. Client - to - Server
2. Site - to - Site
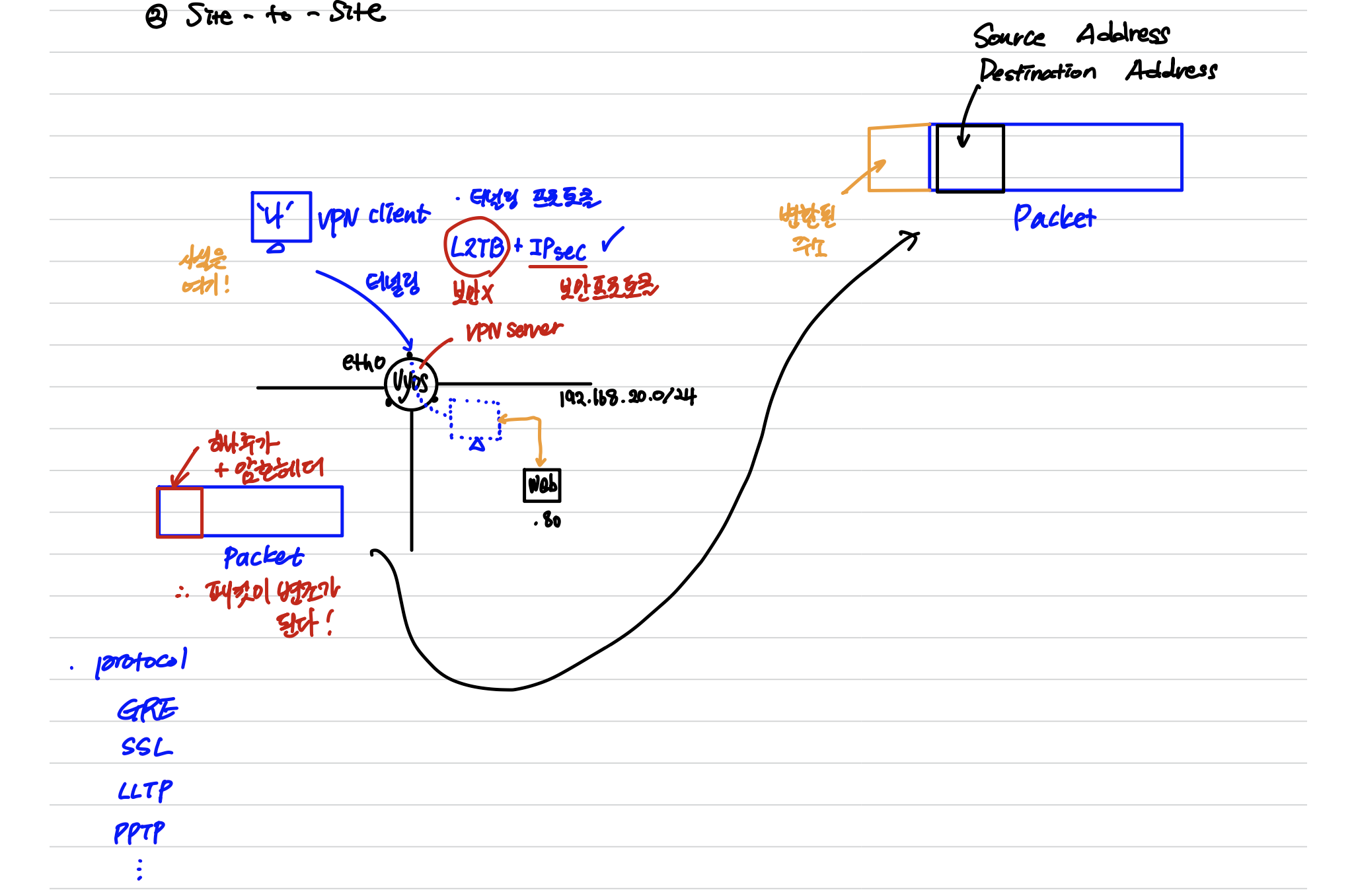
2. 터널링 구성 (Client - to - Server)
vyos@vyos# set vpn ipsec ipsec-interfaces interface eth0
vyos@vyos# set vpn ipsec nat-traversal enable
VPN을 통해 주소 변환이 발생해도 허용하겠다.
vyos@vyos# set vpn ipsec nat-networks allowed-network 0.0.0.0/0
허용할 대역대는 전체 대역대
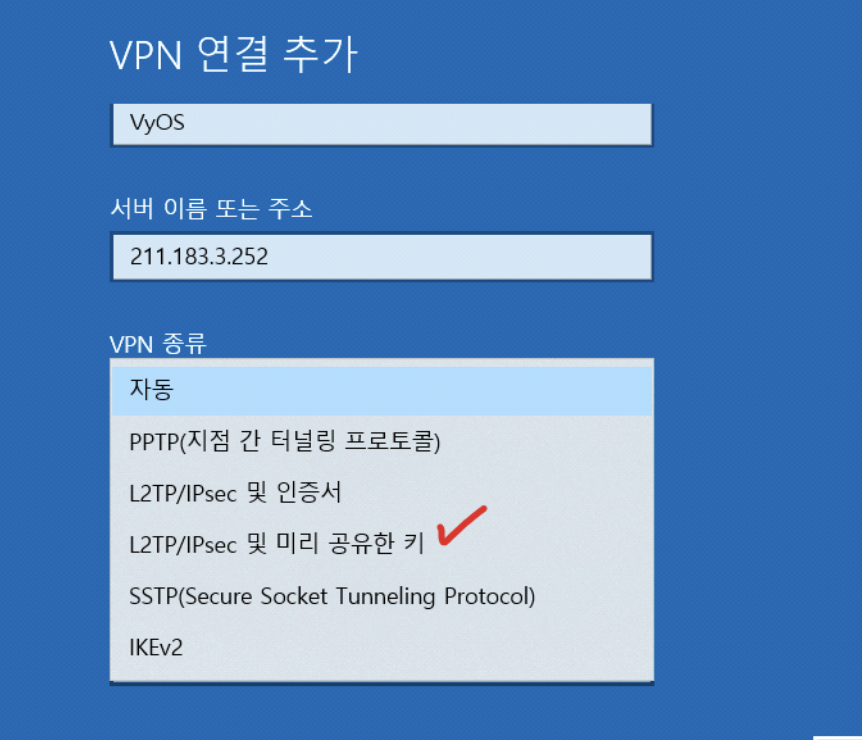
vyos@vyos# set vpn l2tp remote-access outside-address 211.183.3.252
layer 2 Tunneling Protocol을 통해 접속할 서버의 주소
vyos@vyos# set vpn l2tp remote-access client-ip-pool start 192.168.20.100
vyos@vyos# set vpn l2tp remote-access client-ip-pool stop 192.168.20.110
192.168.20.0/24 대역대에 100~110 사이의 사설 IP를 할당해준다.
vyos@vyos# set vpn l2tp remote-access ipsec-settings authentication mode pre-shared-secret
인증방식을 '사전 공유키'로 설정 하겠다.
vyos@vyos# set vpn l2tp remote-access ipsec-settings authentication pre-shared-secret rapa
사전 공유키는 'rapa'로 하겠다
vyos@vyos# set vpn l2tp remote-access authentication mode local
사용자를 구분하기 위해 local의 아이디와 암호를 설정하겠다.
vyos@vyos# set vpn l2tp remote-access authentication local-users username kakao password eng
사용자의 이름은 kakao 이고 PW 는 eng로 하겠다.
vyos@vyos# commit
<터널링 구성 완료>- Command 창에서 VPN 접속
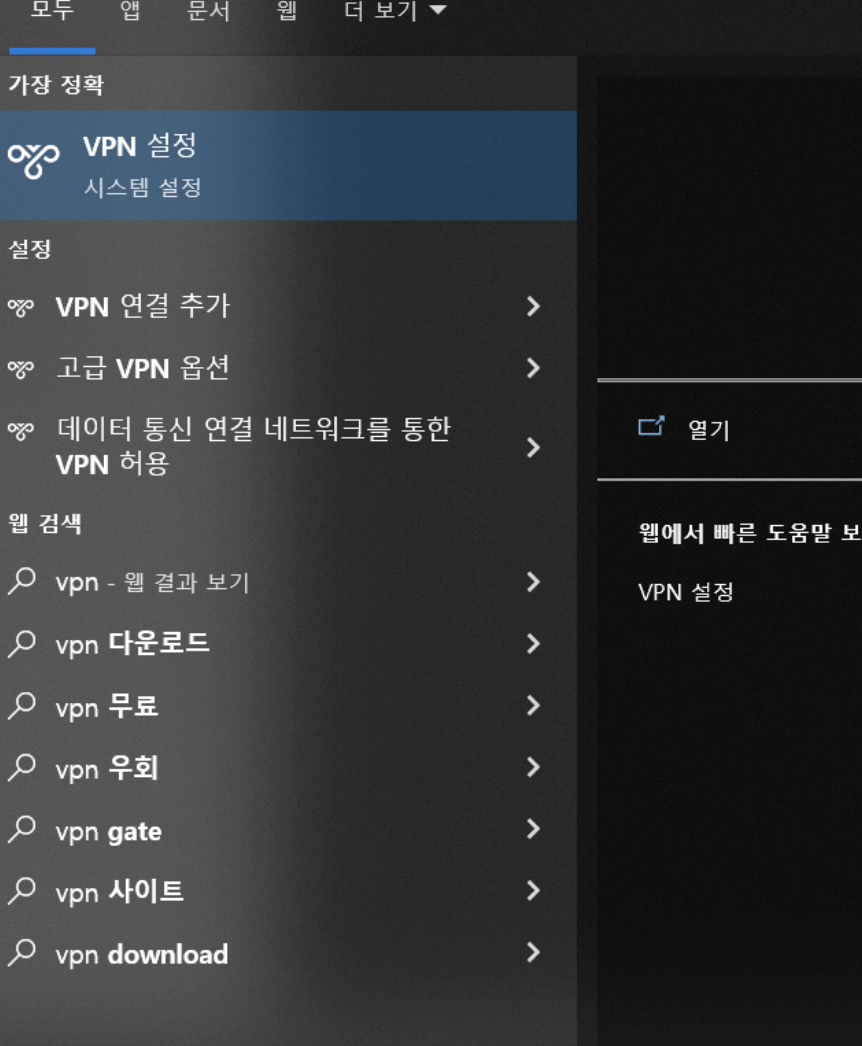
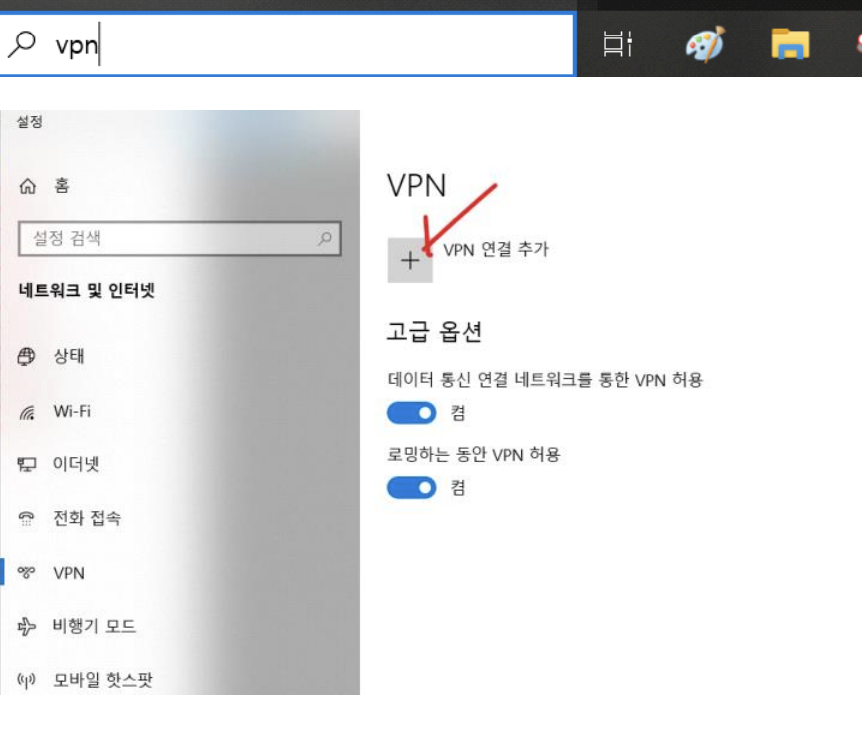

-
어댑터 옵션 변경 클릭
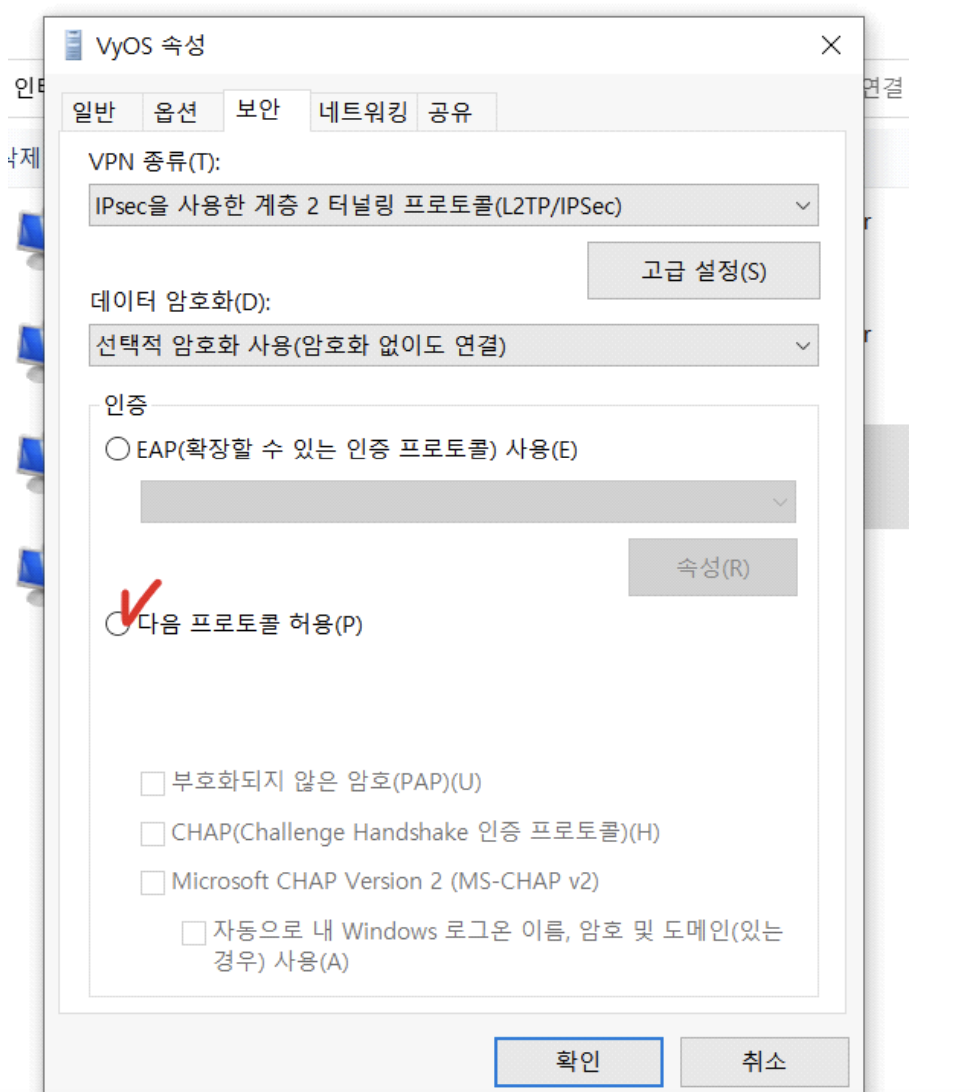
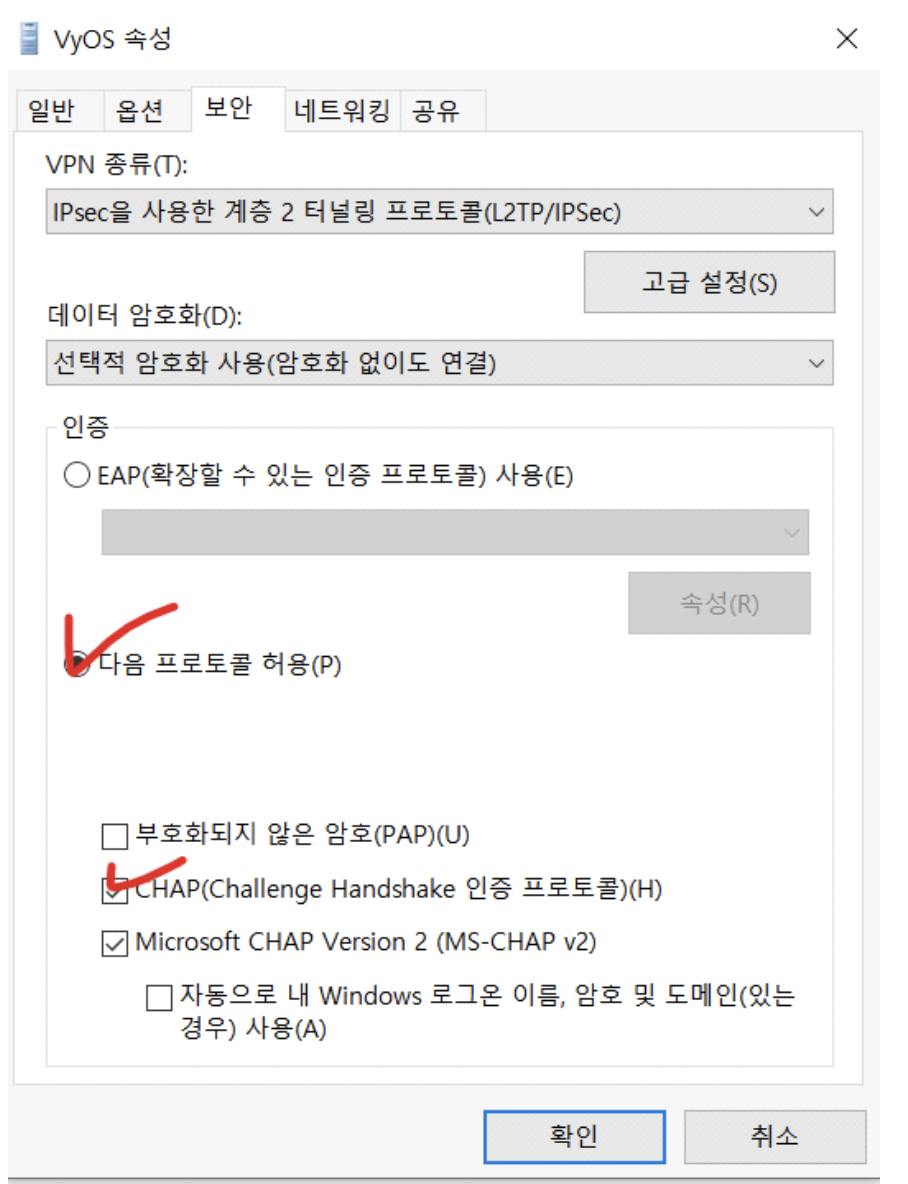
-
연결 성공 - 이더넷(PC Network)이 끊길 것임
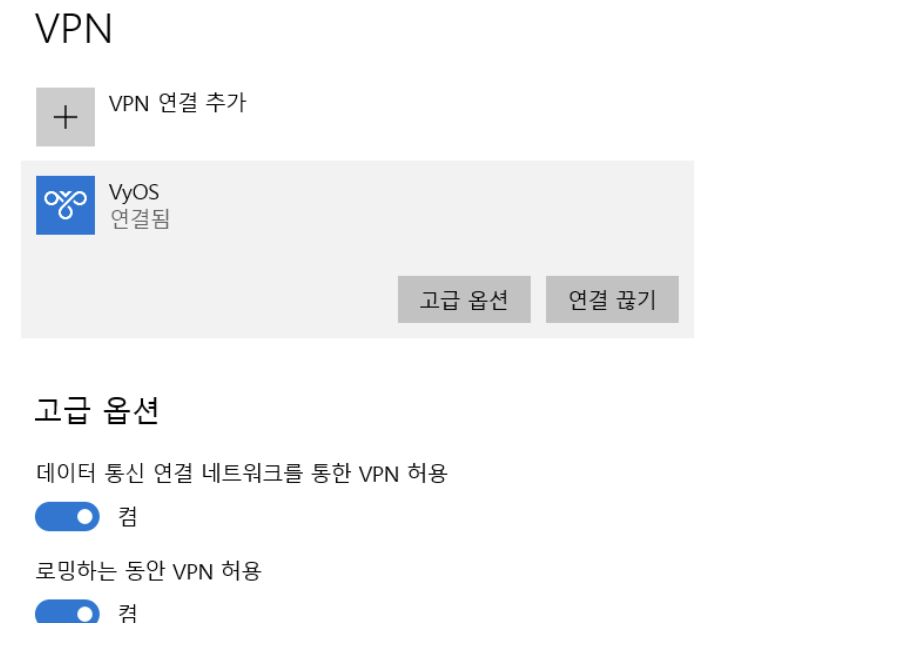
-
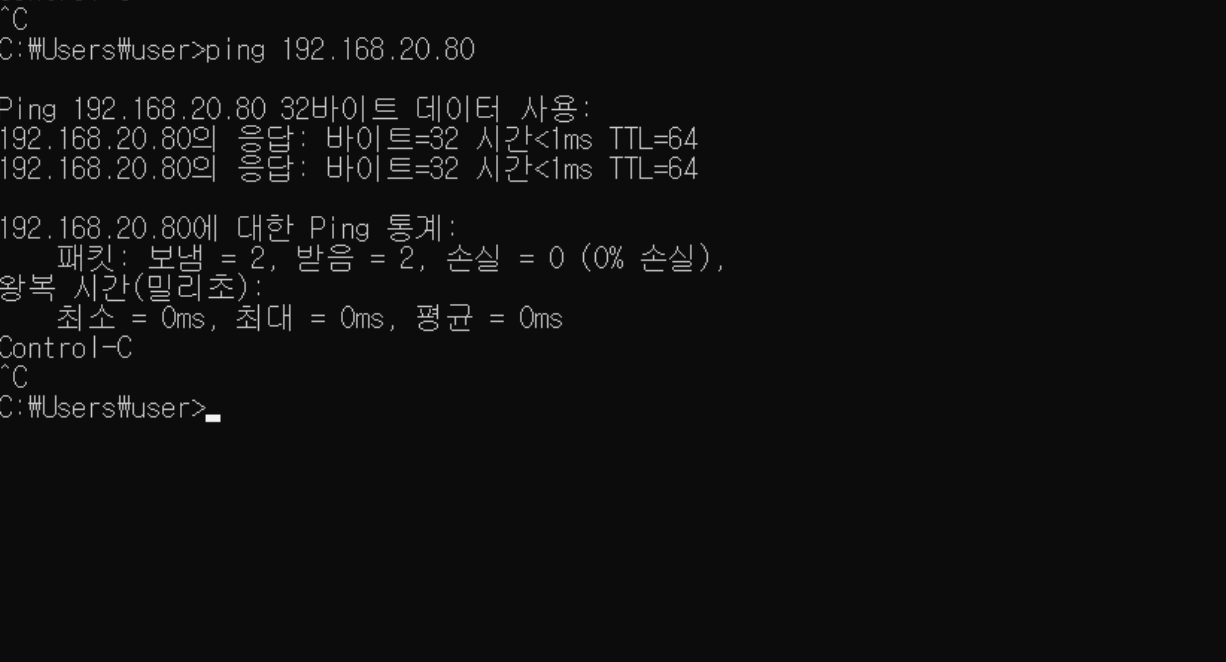
검증 해주기 - cmd 창에서 ping 192.168.20.80 때려보기
확인 완료!
2-1 DNAT 와 VPN의 차이는 무엇일까?
가장 간단히 생각하면 내가 위치해 있는 곳의 차이일 것이다.
VPN 은 안(내부)에 있는 것처럼 동작을 하는것이고, DNAT는 외부에서 내부로 동작을 하는 것이고, 사실 VPN을 사용하고자 하는 서버나 PC는 외부에 있고 DNAT는 외부와 내부는 확실히 경계가 있다.
3. 터널링 구성 (Site - to - Site)
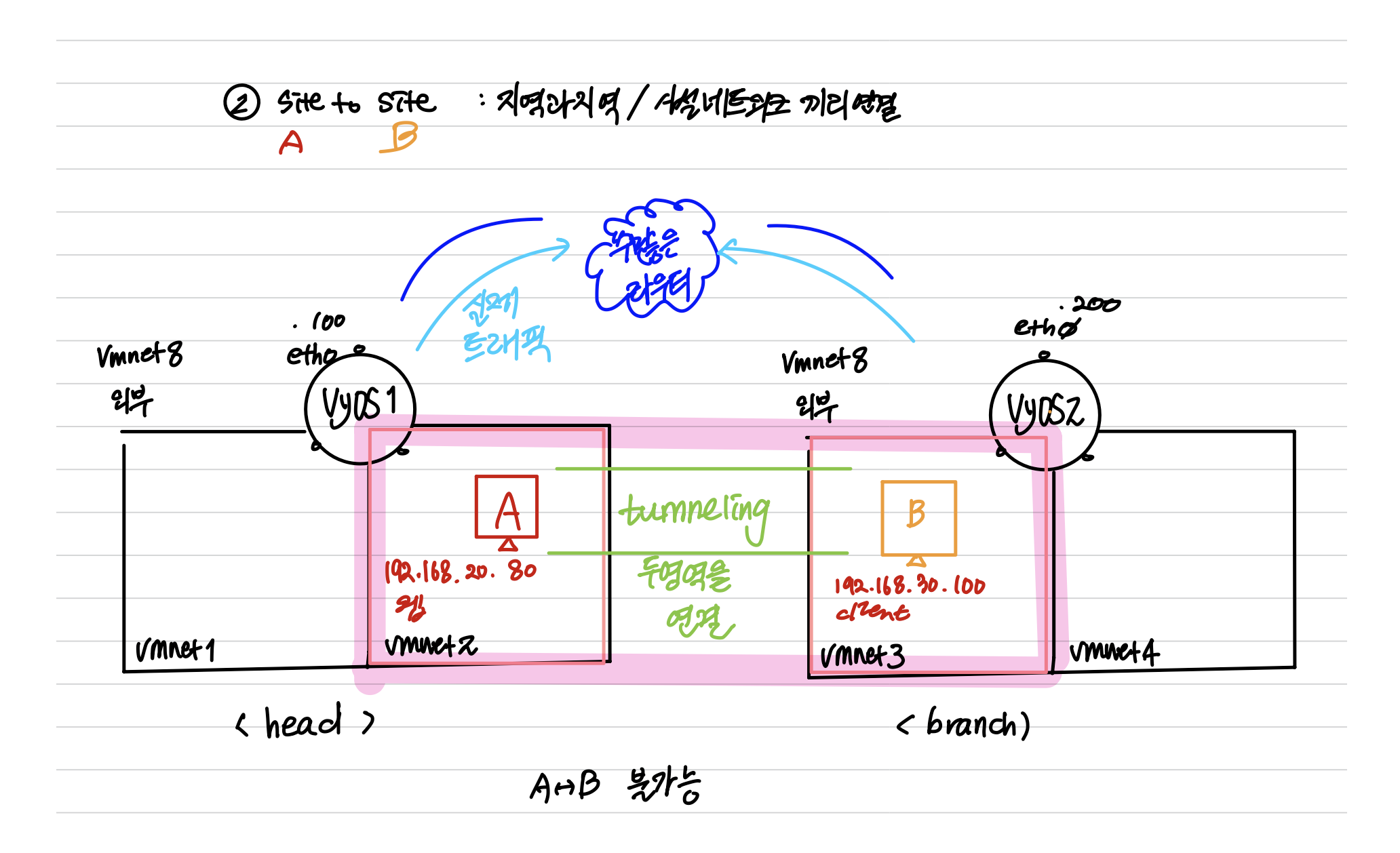
<Site to Site를 구현해보기 위한 환경 세팅>
- VyOS 가 2개
- 기존의 NAT,Zone-Policy, Firewall, VPN 삭제할 것.
- Virtual Network Setting 에서 vmnet2,3 은 Disconnected 상태일 것
- Head VyOS 의 eth0 은 211.183.3.100의 주소를 가지고 있다.
- Head VyOS 의 eth1 은 192.168.10.252의 주소를 가지고 있다.
- Head VyOS 의 eth2 은 192.168.20.252의 주소를 가지고 있다.
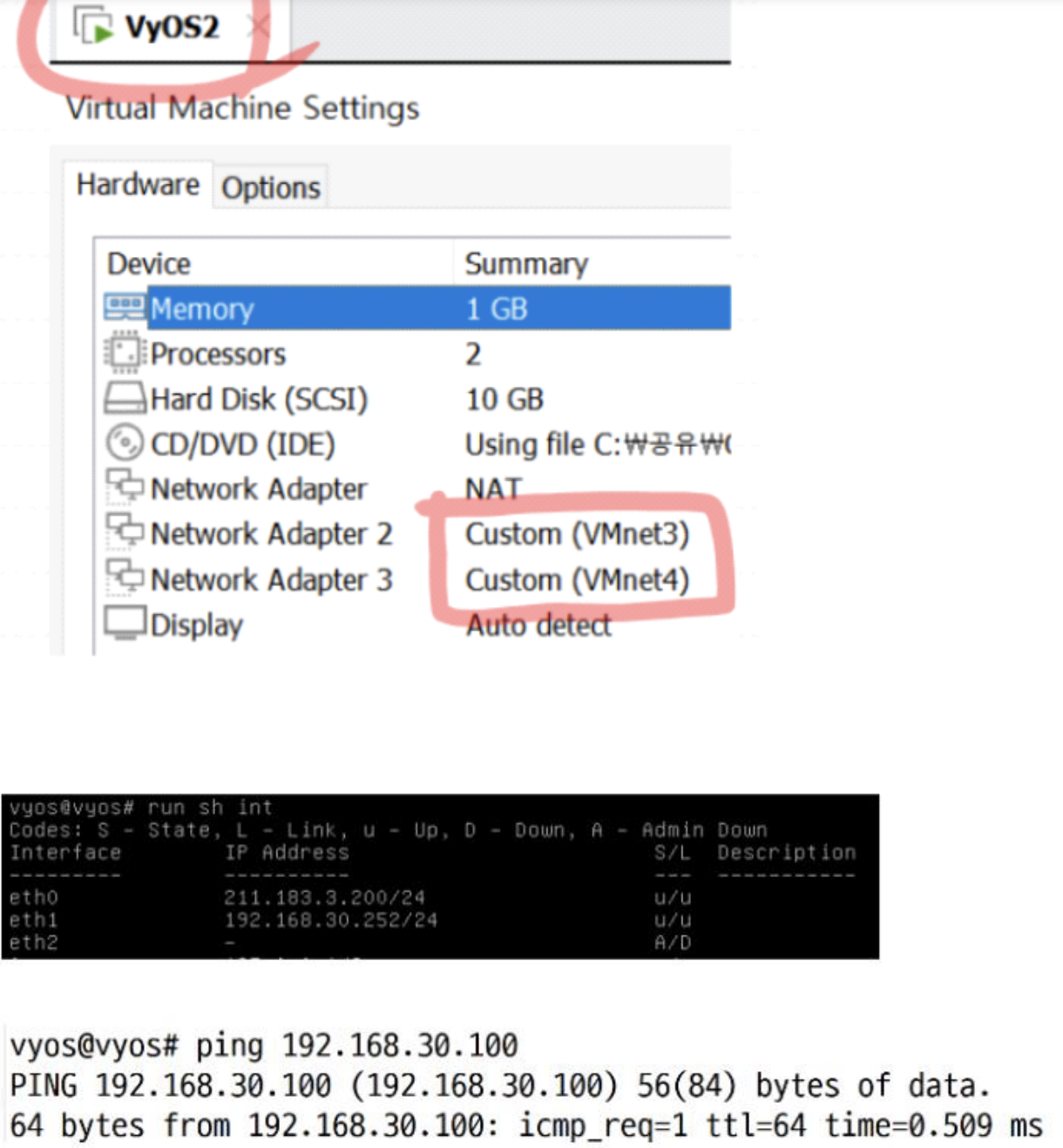
- Branch VyOS 의 eth0 은 211.183.3.200의 주소를 가지고 있다.
- Branch VyOS 의 eth1 은 192.168.30.252의 주소를 가지고 있다.
- Branch VyOS 의 eth2 은 192.168.40.252의 주소를 가지고 있다.
- Head VyOS - Web(192.168.20.80) 과의 통신이 가능 해야함
- Branch VyOS - Client(192.18.30.100)과의 통신이 가능 해야함
- Web - Client 과의 통신이 안되는 것을 확인 해야함
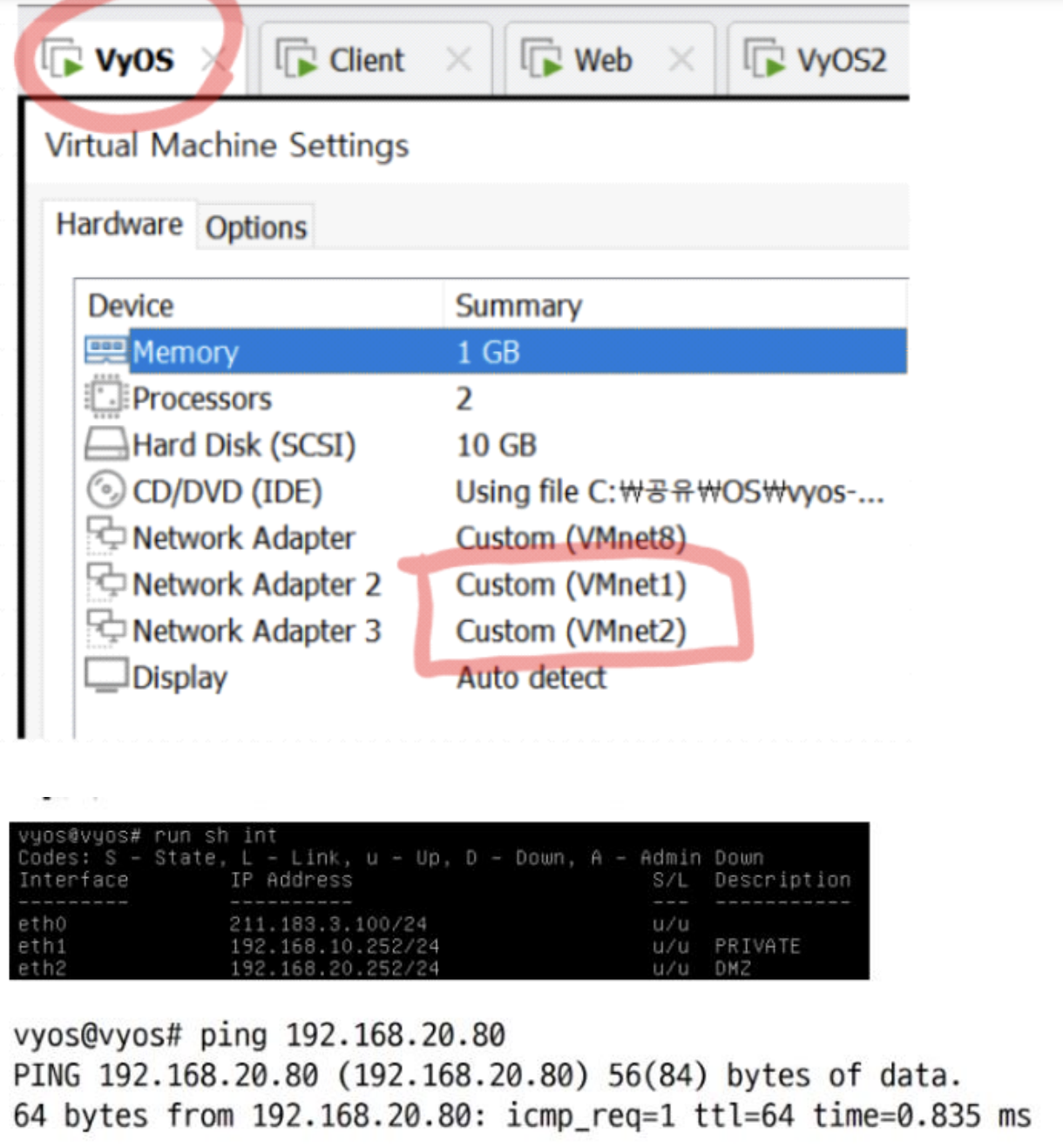
- 설정이 완료된 상태 이제 터널링 (Tunneling)을 해볼 것이다.
4. 터널링 (Site - to - Site)
Head VyOS
vyos@vyos# set vpn ipsec esp-group head-esp compression disable
vyos@vyos# set vpn ipsec esp-group head-esp lifetime 1800
vyos@vyos# set vpn ipsec esp-group head-esp mode tunnel
vyos@vyos# set vpn ipsec esp-group head-esp pfs enable
vyos@vyos# set vpn ipsec esp-group head-esp proposal 1 encryption aes256
vyos@vyos# set vpn ipsec esp-group head-esp proposal 1 hash sha256
vyos@vyos# set vpn ipsec ike-group head-ike ikev2-reauth no
vyos@vyos# set vpn ipsec ike-group head-ike key-exchange ikev1
vyos@vyos# set vpn ipsec ike-group head-ike lifetime 3600
vyos@vyos# set vpn ipsec ike-group head-ike proposal 1 encryption aes256
vyos@vyos# set vpn ipsec ike-group head-ike proposal 1 hash sha256
vyos@vyos# set vpn ipsec ipsec-interfaces interface eth0
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 authentication mode pre-shared-secret
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 authentication pre-shared-secret rapa
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 ike-group head-ike
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 local-address 211.183.3.100
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 tunnel 0 allow-nat-networks disable
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 tunnel 0 allow-public-networks disable
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 tunnel 0 esp-group head-esp
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 tunnel 0 local prefix 192.168.20.0/24
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.200 tunnel 0 remote prefix 192.168.30.0/24
- Branch VyOS
vyos@vyos# set vpn ipsec esp-group branch-esp compression disable
vyos@vyos# set vpn ipsec esp-group branch-esp lifetime 1800
vyos@vyos# set vpn ipsec esp-group branch-esp mode tunnel
vyos@vyos# set vpn ipsec esp-group branch-esp pfs enable
vyos@vyos# set vpn ipsec esp-group branch-esp proposal 1 encryption aes256
vyos@vyos# set vpn ipsec esp-group branch-esp proposal 1 hash sha256
vyos@vyos# set vpn ipsec ike-group branch-ike ikev2-reauth no
vyos@vyos# set vpn ipsec ike-group branch-ike key-exchange ikev1
vyos@vyos# set vpn ipsec ike-group branch-ike lifetime 3600
vyos@vyos# set vpn ipsec ike-group branch-ike proposal 1 encryption aes256
vyos@vyos# set vpn ipsec ike-group branch-ike proposal 1 hash sha256
vyos@vyos# set vpn ipsec ipsec-interfaces interface eth0
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 authentication mode pre-shared-secret
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 authentication pre-shared-secret rapa
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 ike-group branch-ike
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 local-address 211.183.3.200
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 tunnel 0 allow-nat-networks disable
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 tunnel 0 allow-public-networks disable
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 tunnel 0 esp-group branch-esp
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 tunnel 0 local prefix 192.168.30.0/24
vyos@vyos# set vpn ipsec site-to-site peer 211.183.3.100 tunnel 0 remote prefix 192.168.20.0/24
- 터널링 완료
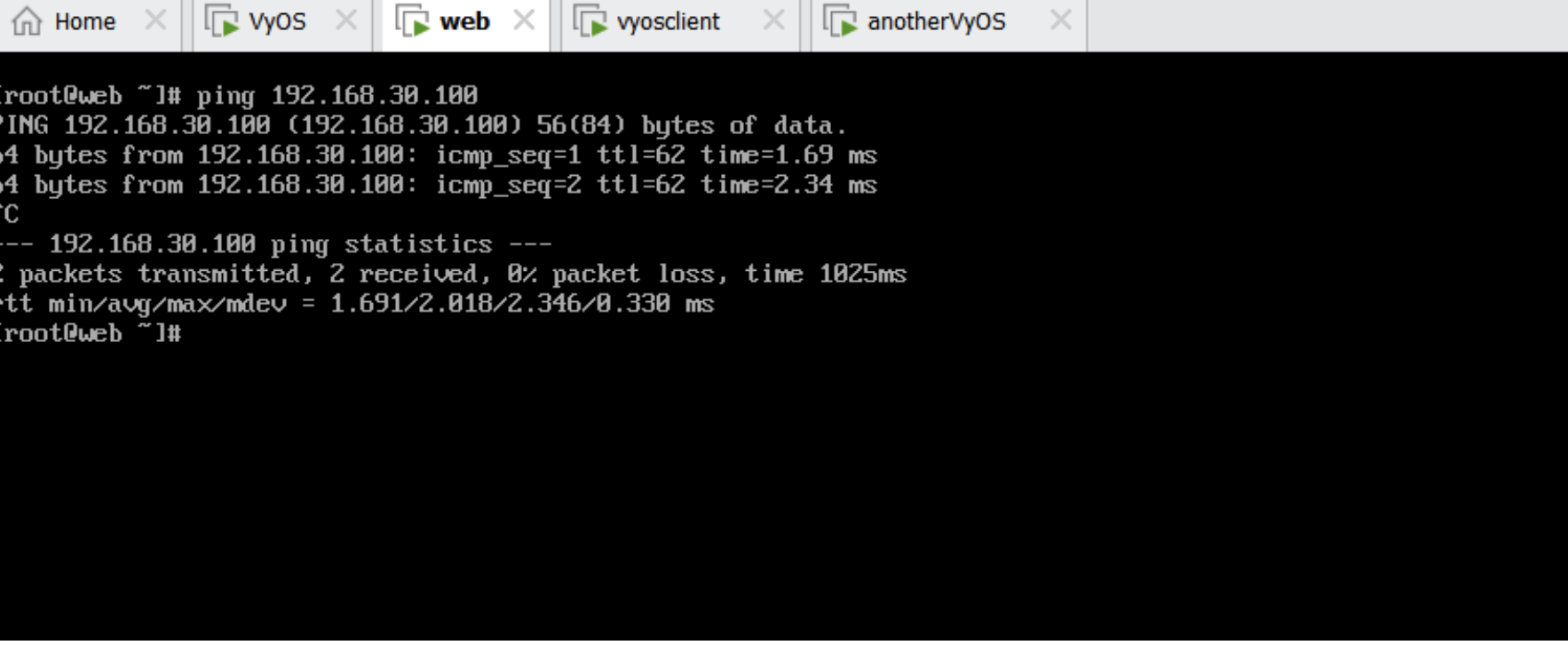
터널링을 통해 Client to Web , Web to Client 가 핑이 때려지는지 확인해야 한다.
- Client to Web
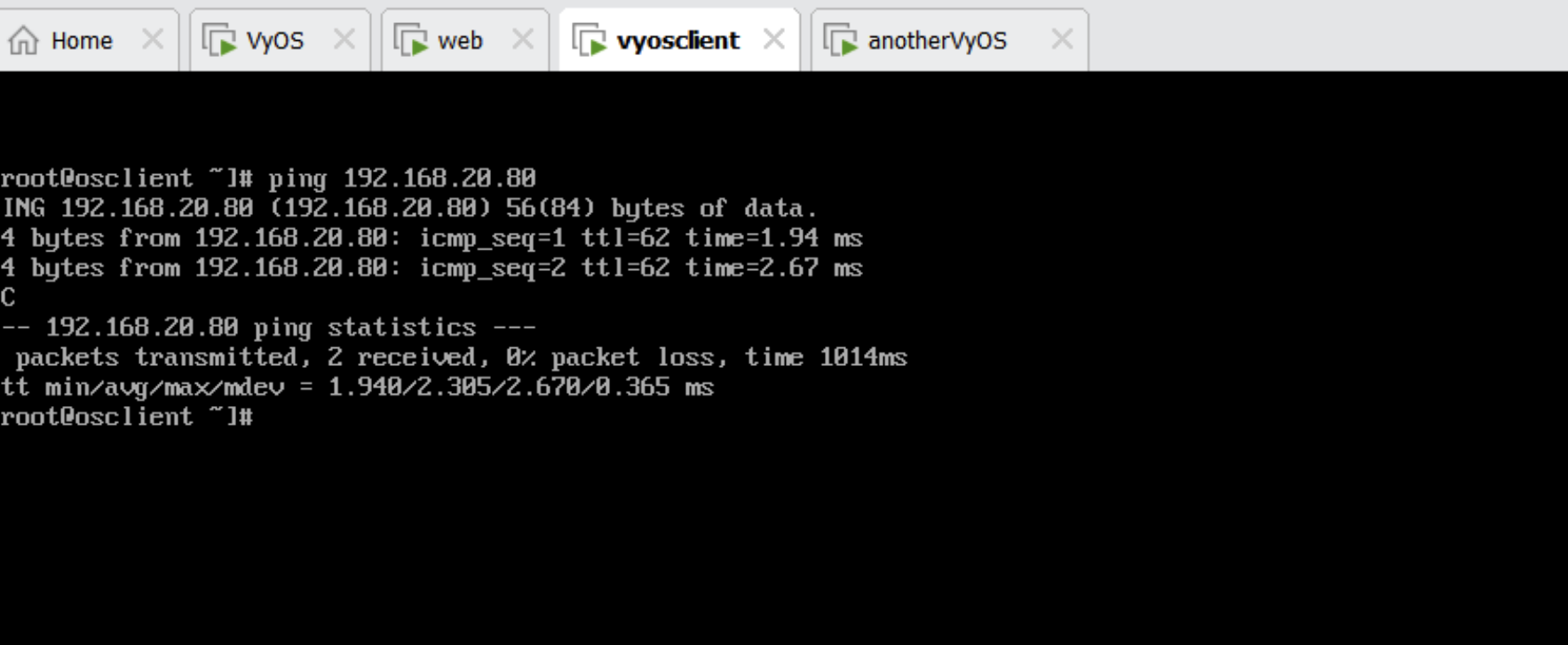
Web to Client
4-1. P A T ( 터널링을 구성한 대역은 PAT 제외 시키기)
- 사설 대역의 서버들이 외부와 통신하기 위한 PAT 설정
- 터널링을 구성한 대역은 PAT를 제외시킨다!!!
- Head VyOs PAT
vyos@vyos# set nat source rule 9 destination address 192.168.30.0/24
vyos@vyos# set nat source rule 9 exclude
vyos@vyos# set nat source rule 9 outbound-interface eth0
vyos@vyos# set nat source rule 9 source address 192.168.20.0/24
vyos@vyos# set nat source rule 10 outbound-interface eth0
vyos@vyos# set nat source rule 10 source address 192.168.20.0/24
vyos@vyos# set nat source rule 10 translation address masquerade- Branch VyOs PAT
vyos@vyos# set nat source rule 9 destination address 192.168.20.0/24
vyos@vyos# set nat source rule 9 exclude
vyos@vyos# set nat source rule 9 outbound-interface eth0
vyos@vyos# set nat source rule 9 source address 192.168.30.0/24
vyos@vyos# set nat source rule 10 outbound-interface eth0
vyos@vyos# set nat source rule 10 source address 192.168.30.0/24
vyos@vyos# set nat source rule 10 translation address masquerade5. 연습문제
-
VyOS1 = 211.183.3.50
-
VyOS2 = 211.183.3.150
-
211.183.3.50 으로 접속 했을때 wordpress 블로그가 뜨기를 바란다.
-
Web 서버에 wordpress 서버가 있어야 한다.
-
Client 서버에 DB 서버가 있어야 한다.
-
양쪽 VyOS 에서 delete VPN, delete NAT 설정 후 시도할 것
- 절차 생각 해보기 (뇌피셜)
-
일단 각각의 인터페이스 (eth0) 의 IP를 수정해줘야 하지 않을까?
-
터널링을 해줘야 하지 않을까?
-
PAT를 해줘야 하지 않을까?
-
Destination NAT를 해야 터널링을 구성한 대역으로 외부의 트래픽이 들어오지 않을까?
-
PAT를 해줘야 Web, Client 서버각각 ping 8.8.8.8 이 가능하며 패키지를 다운받을 수 있지 않을까?
-
Web 에서 wordpress 서버를 구축하기 위한 패키지에는 어떤 것이 있을까?
-
Client 서버에는 mariaDB 서버를 구축하기 위한 패키지에는 어떤 것이 있을까?
-
wordpress 서버의 config 파일은 어떻게 수정해줘야 할까?
