Udemy Labs - Certified Kubernetes Application Developer - Labs - Admission Controllers 오답노트
Kubernetes
2
Which admission controller is not enabled by default?
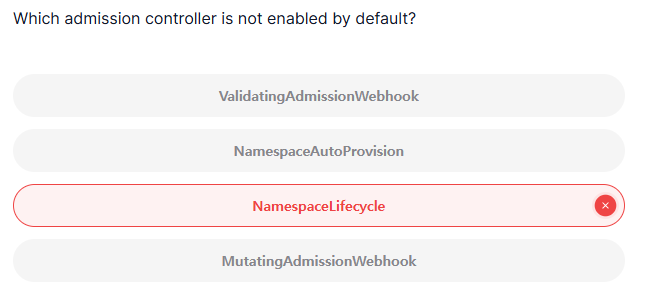
정답
NamespaceAutoProvision
풀이
NamespaceAutoProvision: Kubernetes의 admission controller 중 하나로, 클러스터에서 네임스페이스가 존재하지 않을 때 자동으로 네임스페이스를 생성하는 기능을 제- 기본적으로 활성화되어 있지 않으며, 사용자가 수동으로 활성화해야 함
3
Which admission controller is enabled in this cluster which is normally disabled?
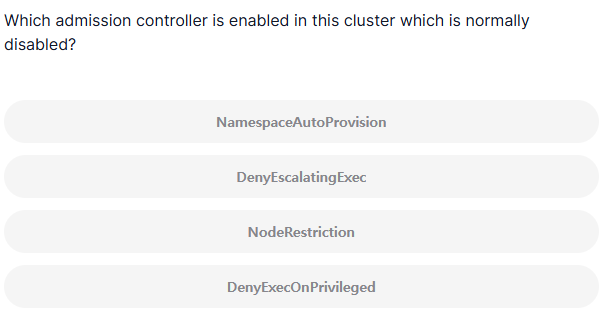
정답
NodeRestriction
풀이
NodeRestriction admission controller: Kubernetes에서 기본적으로 비활성화되어 있지만, 클러스터에서 활성화되면 특정한 제한을 두어 노드 관련 리소스에 대한 접근을 제어하는 기능을 제공- 보안을 강화하고, 사용자가 자신이 소속된 노드에 대해서만 작업을 수행할 수 있도록 제한하는 역할
- 노드 리소스 제한: NodeRestriction admission controller는 주로 Pod와 관련된 요청에서 Node 리소스에 대한 접근을 제한 -> 사용자가 자신이 소속된 노드에서만 Pod를 배포하고 노드 관련 작업을 할 수 있도록 보장
- Node 객체 수정 제한: 이 컨트롤러는 사용자가 자신이 소속된 노드를 제외한 다른 노드에 대한 Node 리소스를 수정하거나 삭제하는 것을 방지
- Pod 노드 배치 제한: 사용자가 Pod를 생성할 때, 자신이 소속된 노드에만 배치할 수 있도록 제한 -> 다른 노드에 Pod를 배치하는 요청을 거부
5
The previous step failed because kubernetes have NamespaceExists admission controller enabled which rejects requests to namespaces that do not exist. So, to create a namespace that does not exist automatically, we could enable the NamespaceAutoProvision admission controller
Enable the NamespaceAutoProvision admission controller
Note: Once you update kube-apiserver yaml file, please wait for a few minutes for the kube-apiserver to restart completely.
정답
- kube-apiserver.yaml 파일 확인
controlplane ~ ➜ cat /etc/kubernetes/manifests/kube-apiserver.yaml
apiVersion: v1
kind: Pod
metadata:
annotations:
kubeadm.kubernetes.io/kube-apiserver.advertise-address.endpoint: 192.168.63.146:6443
creationTimestamp: null
labels:
component: kube-apiserver
tier: control-plane
name: kube-apiserver
namespace: kube-system
spec:
containers:
- command:
- kube-apiserver
- --advertise-address=192.168.63.146
- --allow-privileged=true
- --authorization-mode=Node,RBAC
- --client-ca-file=/etc/kubernetes/pki/ca.crt
- --enable-admission-plugins=NodeRestriction
- --enable-bootstrap-token-auth=true
- --etcd-cafile=/etc/kubernetes/pki/etcd/ca.crt
- --etcd-certfile=/etc/kubernetes/pki/apiserver-etcd-client.crt
- --etcd-keyfile=/etc/kubernetes/pki/apiserver-etcd-client.key
- --etcd-servers=https://127.0.0.1:2379
- --kubelet-client-certificate=/etc/kubernetes/pki/apiserver-kubelet-client.crt
- --kubelet-client-key=/etc/kubernetes/pki/apiserver-kubelet-client.key
- --kubelet-preferred-address-types=InternalIP,ExternalIP,Hostname
- --proxy-client-cert-file=/etc/kubernetes/pki/front-proxy-client.crt
- --proxy-client-key-file=/etc/kubernetes/pki/front-proxy-client.key
- --requestheader-allowed-names=front-proxy-client
- --requestheader-client-ca-file=/etc/kubernetes/pki/front-proxy-ca.crt
- --requestheader-extra-headers-prefix=X-Remote-Extra-
- --requestheader-group-headers=X-Remote-Group
- --requestheader-username-headers=X-Remote-User
- --secure-port=6443
- --service-account-issuer=https://kubernetes.default.svc.cluster.local
- --service-account-key-file=/etc/kubernetes/pki/sa.pub
- --service-account-signing-key-file=/etc/kubernetes/pki/sa.key
- --service-cluster-ip-range=172.20.0.0/16
- --tls-cert-file=/etc/kubernetes/pki/apiserver.crt
- --tls-private-key-file=/etc/kubernetes/pki/apiserver.key
image: registry.k8s.io/kube-apiserver:v1.31.0
imagePullPolicy: IfNotPresent
livenessProbe:
failureThreshold: 8
httpGet:
host: 192.168.63.146
path: /livez
port: 6443
scheme: HTTPS
initialDelaySeconds: 10
periodSeconds: 10
timeoutSeconds: 15
name: kube-apiserver
readinessProbe:
failureThreshold: 3
httpGet:
host: 192.168.63.146
path: /readyz
port: 6443
scheme: HTTPS
periodSeconds: 1
timeoutSeconds: 15
resources:
requests:
cpu: 250m
startupProbe:
failureThreshold: 24
httpGet:
host: 192.168.63.146
path: /livez
port: 6443
scheme: HTTPS
initialDelaySeconds: 10
periodSeconds: 10
timeoutSeconds: 15
volumeMounts:
- mountPath: /etc/ssl/certs
name: ca-certs
readOnly: true
- mountPath: /etc/ca-certificates
name: etc-ca-certificates
readOnly: true
- mountPath: /etc/kubernetes/pki
name: k8s-certs
readOnly: true
- mountPath: /usr/local/share/ca-certificates
name: usr-local-share-ca-certificates
readOnly: true
- mountPath: /usr/share/ca-certificates
name: usr-share-ca-certificates
readOnly: true
hostNetwork: true
priority: 2000001000
priorityClassName: system-node-critical
securityContext:
seccompProfile:
type: RuntimeDefault
volumes:
- hostPath:
path: /etc/ssl/certs
type: DirectoryOrCreate
name: ca-certs
- hostPath:
path: /etc/ca-certificates
type: DirectoryOrCreate
name: etc-ca-certificates
- hostPath:
path: /etc/kubernetes/pki
type: DirectoryOrCreate
name: k8s-certs
- hostPath:
path: /usr/local/share/ca-certificates
type: DirectoryOrCreate
name: usr-local-share-ca-certificates
- hostPath:
path: /usr/share/ca-certificates
type: DirectoryOrCreate
name: usr-share-ca-certificates
status: {}- spec.container.command 밑에
- --enable-admission-plugins=NodeRestriction에NamespaceAutoProvision추가한 후 수정하기
controlplane ~ ➜ vi /etc/kubernetes/manifests/kube-apiserver.yaml확인
controlplane ~ ➜ cat /etc/kubernetes/manifests/kube-apiserver.yaml
apiVersion: v1
kind: Pod
metadata:
annotations:
kubeadm.kubernetes.io/kube-apiserver.advertise-address.endpoint: 192.168.63.146:6443
creationTimestamp: null
labels:
component: kube-apiserver
tier: control-plane
name: kube-apiserver
namespace: kube-system
spec:
containers:
- command:
- kube-apiserver
- --advertise-address=192.168.63.146
- --allow-privileged=true
- --authorization-mode=Node,RBAC
- --client-ca-file=/etc/kubernetes/pki/ca.crt
- --enable-admission-plugins=NodeRestriction,NamespaceAutoProvision8
Disable DefaultStorageClass admission controller
This admission controller observes creation of PersistentVolumeClaim objects that do not request any specific storage class and automatically adds a default storage class to them. This way, users that do not request any special storage class do not need to care about them at all and they will get the default one.
Note: Once you update kube-apiserver yaml file then please wait few mins for the kube-apiserver to restart completely.
정답
- spec.contianers.command밑에 kube-apiserver밑에
- --disable-admission-plugins=DefaultStorageClass추가해줘야 함
controlplane ~ ➜ vi /etc/kubernetes/manifests/kube-apiserver.yaml
controlplane ~ ➜ cat /etc/kubernetes/manifests/kube-apiserver.yaml
apiVersion: v1
kind: Pod
metadata:
annotations:
kubeadm.kubernetes.io/kube-apiserver.advertise-address.endpoint: 192.168.63.146:6443
creationTimestamp: null
labels:
component: kube-apiserver
tier: control-plane
name: kube-apiserver
namespace: kube-system
spec:
containers:
- command:
- kube-apiserver
- --disable-admission-plugins=DefaultStorageClass
- --advertise-address=192.168.63.146
- --allow-privileged=true
- --authorization-mode=Node,RBAC
- --client-ca-file=/etc/kubernetes/pki/ca.crt