준비 기간은 2개월(회사와 병행) 정도이고, 클라우드 환경과 리눅스에 익숙하지만 보안쪽의 지식은 다소 부족하여 다소 어렵다고 느낌. 이후 테라폼과 함께 학습하면 좋다고 생각함. 시험 문제와 해설은 내가 직접 틀리고 추가 설명으로 적은것이다.
- 응시일자 : 2월 18일
- 문항 수: 약 57~60문항 (True/False, 객관식, Multiple Choice)
- 시험 시간: 60분 + 30분 (Request Accommodation 신청시)
- 합격 기준: 약 70% 이상
- 유효 기간: 2년
- 언어: 영어
- 가격 : 75 USD (현재 환율 10만 4천원 7백원 결제함)
- 준비물 : 여권, 영어이름이 기재된 국제 운전 면허증
- 응시 방법: 시험 시작 15분전 입장하여 감독관 proctored test 진행. 소지품 검사, 360도 환경 보여주고 진행. Macbook 의 경우 Activity Monitor 검사
Sample Test # 1
Q1. When using the Vault Secrets Operator(VSO), where is the secret written to after being retrieved from Vault?
- to the cloud-provider’s native secret manager (Azure Key Vault, AWS Secrets Manager, etc)
- directly to the filesystem of the pod
- the secret is never written to any service or persistent storage
- Kubernetes Secrets
Ans. 4. Kubernetes Secrets
Exp1. When using the Vault Secrets Operator, the secret is written to Kubernetes Secrets after being retrieved from Vault. Kubernetes Secrets provide a way to store sensitive information securely within a Kubernetes cluster, making it a suitable destination for the retrieved secret.
Exp2. The secret
Kor. VSO 를 사용할 때, Vault 에서 가져온 비밀 데이터가 최종적으로 저장되는 위치는 Kubernetes Secrets. VSO 목적은 K8s 내부 서비스(Secret 리소스)로 데이터를 기록하는 것
감시(VSO가 사용자가 정의한 VaultStaticSecret 같은 커스텀 리소스 감시) → 가져오기(설정된 인증 방식을 통해 Vault 서버에서 기밀 정보 읽어옴) → 동기화(가져온 데이터를 클러스터 내의 표준 Kubernetes Secrets 리소스로 생성하거나 업데이트) → 사용(애플리케이션 포드는 일반적인 방식으로 이 생성된 Kubernetes Secret 을 사용)
Q2. Your company's security policies require that all encryption keys must be rotated at least one time per year. After using the Transit secrets engine for a year, the Vault admin issues the proper command to rotate the key named ecommerce that was used to encrypt your data. What command can be used to easily re-encrypt the original data with the new version of the key?
vault write -f transit/keys/ecommerce/update <old data>vault write transit/encrypt/ecommerce v1:v2 <old data>vault write transit/rewrap/ecommerce ciphertext=<old data>vault write -f transit/keys/ecommerce/rotate <old data>
Ans. 3. vault write transit/rewrap/ecommerce ciphertext=<old data>
Exp1. The correct command to re-encrypt the original data with the new version of the key is to use the vault write transit/rewrap/ecommerce command with the ciphertext= parameter. This command will re-wrap the data with the new key without needing to decrypt and re-encrypt the data manually.
Kor. Vault 의 Transit 시크릿 엔진에서 키를 회전(Rotate)시킨 후, 이전 버전의 키로 암호화된 데이터를 최신 버전의 키로 다시 암호화하려면 Rewarp 작업 수행.
Transit 엔진의 키 회전과 데이터 개선 과정
- 키 회전(Rotate) :
vault write -f transit/keys/ecommerce/rotate명령을 실행하면 vault 내부에 새로운 버전(V1→ V2) 의 암호화 키가 생성. 이후의 모든 새로운 암호화 요청은 자동으로 V2 키를 사용 - 데이터 재암호화(Rewrap) : 하지만 기존에 V1 키로 암호화되어 저장된 데이터는 자동으로 업데이트 되지 않음. 이를 최신 버전인 V2로 업그레이드하기 위해 사용하는 명령어는 바로
rewarp - 효율성 :
rewarp작업은 클라이언트가 데이터를 복호화해서 평문을 본 다음 다시 암호화해서 보내는 과정을 거치지 않음. Vault 서버 내부에서 안전하게 새 키로 다시 암호화하여 결과물만 반환하므로 보안성과 효율성이 높음
Q3. You are deploying Vault in a local data center, but want to be sure you have a secondary Vault cluster in the event the primary cluster goes offline. In the secondary data center, you have applications that are running, as they are architected to run active/active. Which type of replication would be best in this scenario?
- disaster recovery replication
- performance replication
Ans. 2. performance replication
Exp1. Performance replication is designed to ensure high availability and consistent performance across multiple clusters. In this scenario, where applications are running actively in the secondary data center, performance replication would be the best choice to maintain the required performance levels and availability in case the primary cluster goes offline.
Kor. Active/Active 구조로 운영되는 멀티 데이터 센터 환경. 이 경우 각 데이터 센터의 애플리케이션이 로컬에 있는 vault 에서 즉각적으로 비밀 정보를 읽어올 수 있어야 하므로 Performance Replication
Active/Active 지원 : 문제에서 보조 데이터 센터의 애플리케이션이 Active 로 가동 중이라고 명시. Performance Replication(성능 복제) 에서는 secondary cluster 도 읽기 요청(Read Reqeust)을 직접 처리
지연 시간 감소 : 로컬 애플리케이션이 멀리 떨어진 기본 데이터 센터까지 가지 않고, 같은 데이터 센터 내의 보보조 Vault 클러스터에서 즉시 데이터를 가져올 수 있어 성능이 최적화됨
구성 요소 복제 : 토큰, 정책, 시크릿 엔진 설정 등이 복제되지만, 각 클러스터는 고유한 Lease 와 토큰을 로컬에서 관리하므로 확장이 용이함
Disaster Recovery(RD) Replication 과 무엇이 다른가?
DR 복제(Active/Passive) : 보조 클러스터가 평상시에는 ‘대기’ 상태이며, 어떠한 요청도 처리 불가. 오직 기본 클러스터가 완전히 중단 되었을 때만 수동 또는 자동으로 활성화. DR 은 말 그대로 재난 복구가 목적이며, performance replication 은 ‘부하 분산 및 로컬 접근성’ 이 목적
Q4. You are using an orchestrator to deploy a new application. Even though the orchestrator creates a new AppRole secret ID, security requires that only the new application has the combination of the role ID and secret ID. What feature can you use to meet these requirements?
- use response wrapping and provide the application server with the unwrapping token instead
- use a batch token instead of a traditional service token
- have the application authenticate with the role ID to retrieve the secret ID
- secure the communication between the orchestrator and Vault using TLS
Ans. 1. use response wrapping and provide the application server with the unwrapping token instead
Exp1. By using response wrapping, you can securely provide the application server with an unwrapping token instead of directly the role ID and secret ID combination. This ensures that only the new application has access to the secret ID, meeting the security requirement while allowing the orchestrator to create the necessary credentials.
Kor. 보안 요구사항의 핵심은 “오케스트레이터가 Secret ID를 알지 못하게 하면서, 오직 최종 애플리케이션만 Role ID 와 Secret ID의 조합을 가지게 하는 것” 이를 위해서 Vault 의 Response Wrapping 기능 사용
Response Wrapping 의 작동 원리
- Wrapping : 오케스트레이터가 Vault 에 Secret ID 생성을 요청할 때, 응답을 wrapping 요청. Vault 는 secret ID를 직접 주는 대신, 이를 보관하고 있는 경로의 일회용 Wrapping Token 반환
- 전달 : 오케스트레이터는 실제 Secret ID 가 무엇인지 모르는 상태로 이 Wrapping Token만 애플리케이션 포드나 서버에 전달
- Unwrapping : 애플리케이션은 전달받은 토큰을 사용하여 Vault 에
unwrap명령 - 보안성 확보, 중간 탈취 방지 : Wrapping Token 은 대게 수명이 매우 짧고 단 한번만(Single-use) 사용. 만약 오케이스레이터나 해커가 먼저 열어보려 했다면, 애플리케이션이 열려고 할 때 이미 사용된 토큰이라는 에러가 발생하여 침해 사실을 즉시 알 수 있음
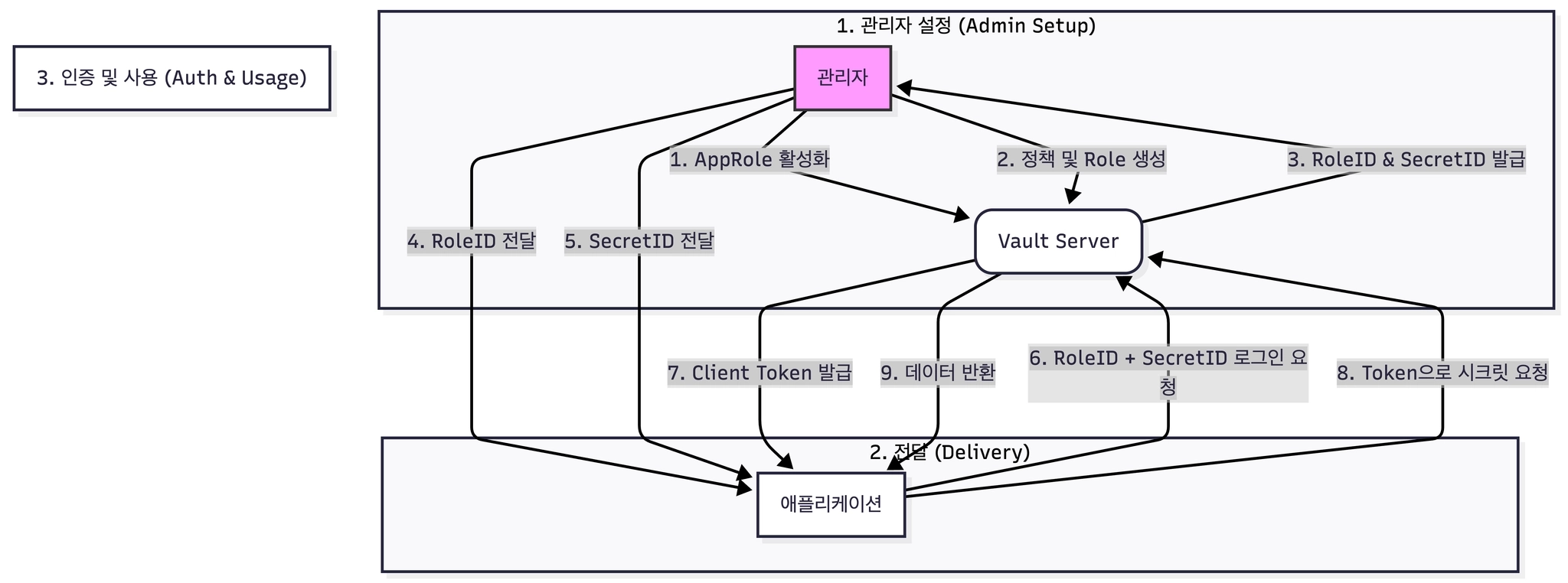
로그인 및 인증 과정(서비스가 Vault 로부터 권한이 있는 토큰 발급받는 과정)
- 관리자가 Vault에 my-app 이라는 역할 생성 후 여기서 Role ID 와 Secret ID 생성
- 오케스트레이터(Jenkins, K8s)가 서비스에 두 값 전달
- 서비스가 이 두 값을 조합하여 Vault의
auth/approle/login앤드포인트에 인증 요청 - Vault 는 두 값이 일치하면, 해당 앱이 사용할 수 있는 기간 한정 Client Token 발급
- 앱은 이 토큰을 들고 필요한 비밀 데이터를 가져옴
Q5. You've set up multiple Vault clusters, one on-premises intended to be the primary cluster, and the second cluster in AWS, which was deployed for performance replication. After enabling replication, developers complain that all the data they've stored in the AWS Vault cluster is missing. What happened?
- all of the data on the secondary cluster was deleted after replication was enabled
- the data was moved to a recovery path after replication was enabled. Use the
vault secrets movecommand to move the data back to its intended location - the data was automatically copied to the primary cluster after replication was enabled since all writes are always forwarded to the primary cluster
- there is a certificate mismatch after replication was enabled since Vault replication generates its own TLS certificates to ensure nodes are trusted entities
Ans. 1. all of the data on the secondary cluster was deleted after replication was enabled
Exp1. All of the data on the secondary cluster was indeed deleted after replication was enabled. This is because enabling replication in Vault involves replicating the primary cluster’s data to the secondary cluster, which overwrites any existing data on the secondary cluster.
Exp2. A certificate mismatch doesn’t result in data loss in the secondary cluster. Vault replication generates its own TLs certificates to ensure secure communication between nodes, but this does not impact the data stored in the cluster.
Kor. Replication 을 활성화하는 순간 보조 클러스터의 기존 데이터는 모두 삭제(Overwritten)됨
Vault 에서 복제를 설정한다는 것은 기본(Primary) 클러스터를 유일한 Single Source of Truth. 복제가 활성화되면 Scondary 클러스터는 자신의 로컬 데이터를 모두 버리고, 기본 클러스터의 데이터를 그대로 복사해옴. 즉, 동기화 이전에 보조 클러스터에 개별적으로 저장했던 데이터느 보호되지 않고 덮어 씌워지게 됨. 실무에서는 보조 클러스터를 복제 노드로 편입시키기 전에, 그 안에 중요한 데이터가 있다면 반드시 백업하거나 기본 클러스터로 미리 옮겨두어야 함.
Primary Cluster : 공유 시크릿(Shared Secrets), 정책 및 설정(Policies & Config), 복제 대상 토큰(Replicated Tokens) 저장
Secondary Cluster : Primary 의 데이터를 실시간으로 복사해오면서 성능을 위해 자기만 가지고 있는 데이터 존재. Primary 의 복제 데이터, 로컬 토큰 및 임리스(Local Tokens & Leases) 저장.
읽기(Local 처리) : 보조 클러스터가 자기 보관함에 있는 복제본을 즉시 앱에 전달
쓰기(Forwarding) : 보조 클러스터에 데이터를 쓰려고 하면, 보조가 이를 Primary 로 전달하여 저장한 뒤 다시 복제하여 받음
전사 공통 데이터 파이프라인 DB 접속 정보는 Primary 에서 관리. 여기서 시크릿 생성하면 AWS에 있는 Vault 로 자동 복제. AWS 에서 돌아가는 분석용 서비스들이 굳이 사내망까지 들어오지 않고 AWS 내의 Vault Secondary 에서 복제된 DB 정보를 읽어감. 이때 AWS 의 서비스가 로그안에서 받은 토큰은 오직 AWS Vault 에만 저장되므로 관리 효율
Q6. Based on the screenshot below, how many auth methods have been enabled on this Vault instance?
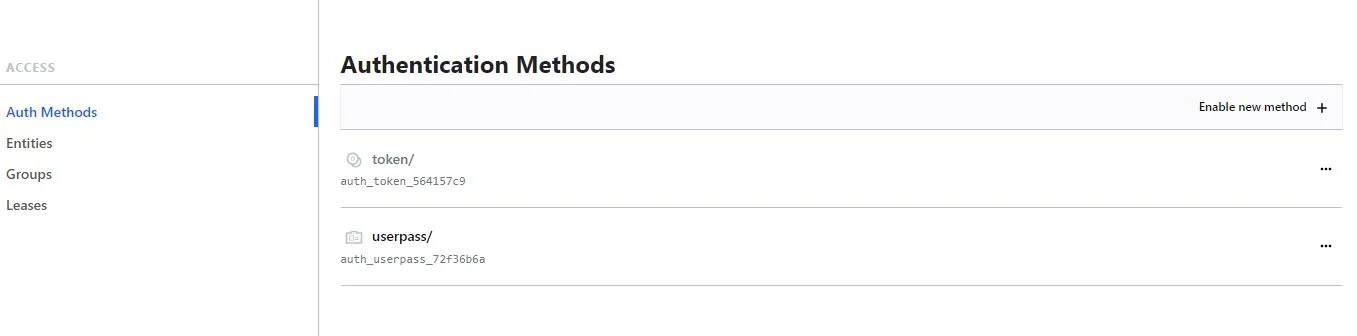
- 2
- 3
- 1
- 4
Ans. 3. 1
Exp1. There is only one auth method enabled on this Vault instance, as indicated by the presence of only one auth method listed in the UI. Tokens are enabled by default.
Kor. Vault 인증 방식(Auth Methods) 정리
- Token Method :
token/방식은 Vault 가 실행될 때 시스템적으로 자동 활성화되는 기본 엔진. 이는 삭제하거나 비활성화할 수 없는 필수 요소이므로, 보통 “새로 활성화된 인증 방법” 을 꼽을 대는 제외하고 계산 - Userpass Method :
userpass/는 관리자가 vault auth enable userpass 명령 등을 통해 의도적으로 추가한 유일한 인증 방법
→ 기본(token, AppRole 이나 Userpass 로 로그인에 성공하면, Vault 는 결국 Token 발행), 추가 인증 방식(userpass, approle, k8s, gibhub 등은 token을 받기 위한 로그인 수단)
Q7. From the options below, select the benefits of using the PKI (x.509 certificates) secrets engine: (select three)
- reducing, or eliminating certificate revocations
- TTLs on Vault certs are longer to ensure certificate are valid for a longer period of time
- Vault can act as an intermediate CA
- reduces time to get a certificate by eliminating the need to generate a private key and CSR
Ans.
- reducing, or eliminating certificate revocations
- Vault can act as an intermediate CA
- reduces time to get a certificate by eliminating the need to generate a private key and CSR
Kor. PKI(Public Key Infrastructure) 는 디지털 인증서를 생성, 관리, 배포, 사용, 저장 및 폐기하는 데 필요한 하드웨어, 소프트웨어, 정책 및 절차의 집합
- Vault 는 중간 인증 기관 역할을 할 수 있음. 최상위 Root CA 로부터 권한을 위임받은 중간 CA로 동작하여 보안성을 높이고 인증서 발급 프로세스를 효율화함.
- 인증서 폐기 목록 관리의 축소 또는 제거. Vault 는 매우 짧은 수명의 인증서를 발급하는 방식을 권장. 인증서가 금방 만료되므로, 굳이 복잡하고 무거운 CRL(인증서 폐기 목록) dlsk. OCSP 를 대규모로 운영할 필요성이 크게 줄어듬
- 개인키 및 CSR 생성 절차 생략을 통한 발급 시간 단축. Vault API 를 사용하면 클라이언트가 직접 복잡한 CSR(Certificate Signing Reqeust) 을 생성할 필요 없이, 요청 한 번으로 개인키와 인증서를 동시에 즉시 발급할 수 있어 자동화에 유리
Q8. What is the difference between the TTL and the Max TTL? (select two)
- the max TTL defines the timeframe for which a token cannot be used
- the TTL defines when the token will expire and be revoked
- the TTL defines when another token will be generated
- the max TTL defines the maximum timeframe for which a token can be renewed
Ans.
- the TTL defines when the token will expire and be revoked
- the max TTL defines the maximum timeframe for which a token can be renewed
Exp1. The statement of 4 correctly explains the role of Max TTL, which sets the maximum duration for which a token can be renewed in Vault.
Q9. When generating dynamic credentials, Vault also creates associated metadata, including information like time duration, renewability, and more, and links it to the credentials.
What is this referred to as?
- secrets engine
- secret
- lease
- token
Ans. 3. lease
Exp1. When generating dynamic credentials, Vault creates a lease associated with the credentials, which includes metadata such as time duration, renewability, and other information. This lease governs the lifecycle of the credentials and it used for managing and revoking them.
Exp2. Secrets engines in Vault are components responsible for managing and interacting with different types of secrets, such as databases, cloud providers, or encryption keys. While dynamic credentials are generated by secrets engines, the metadata associated with them, including leases, is separate from the secrets engine functionality.
Exp3. Secrets in Vault refer to sensitive data that needs to be protected, such as passwords, API keys, or certificates. While dynamic credentials are a type of secret, the metadata associated with them, including time duration and renewability, is specifically managed through leases.
Exp4. Tokens are used for authentication and authorization in Vault, but they are not specifically linked to the metadata associated with dynamic credentials. Tokens the identity of the entity requesting access to Vault and used to access and perform operations.
Kor
Lease : Vault 가 발행한 Dynamic Credential 의 대여 계약서. TTL, Renewability 등의 메타데이터 포함
Secrets Engine : 다양한 종류의 시크릿을 관리하고 생성하는 공장과 같은 컴포넌트. 시크릿 엔진은 자격 증명을 만드는 주체이지, 만들어진 증명의 수명을 관리하는 메타데이터 x
Secret : 민감 데이터(Dynamic, Static credential, API Key, 인증서)
Q10. Which of the following token attributes can be used to renew a token in Vault? (Select two)
- TTL
- token accessor
- identity policy
- token id
Ans. Token accessor, token id
Exp1. The token accessor is a unique identifier for a token in Vault, allowing it to be used to renew the token. The token id is another unique identifier for a token in Vault, allowing it to be used to renew the token.
Kor. 토큰 갱신(Renew)시 사용할 수 있는 속성
- Token ID : Token ID 자체가 인증 수단이므로 노출되면 누구나 해당 권한을 사용할 수 있어 민감하게 취급
- Token Accessor : Token ID 를 직접 노출하지 않고도 특정 토큰을 가리킬 수 있는 참조용 식별자. 토큰을 생성할 때 ID 와 함게 발급. 관리자가 다른 사용자의 토큰을 갱신해주거나 취소하고 싶을 때, 실제 토큰 ID를 몰라도 이 액세서 값만 있으면 작업 수행 가능
Q11. After issuing the command to delete a secret, you run a vault kv list command, but the path to the secret still seems to exist. What command would permanently delete the path from Vault?
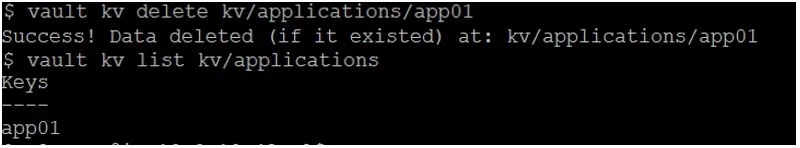
vault kv delete -all kv/applications/app01vault kv destroy -versions=1 kv/applications/app01vault kv metadata delete kv/applications/app01vault kv delete -force kv/applications/app01
ans. 3. vault kv metadata delete kv/applications/app01
Exp1. vault kv metadata delete kv/applications/app01 permanently delete the path from Vault. This command will delete all metadata associated with the specified path, effectively removing it from Vault.
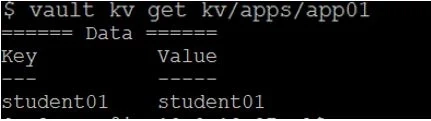
Kor. 터미널 명령어 결과 시크릿 데이터 삭제. 하지만 명령어 바로 뒤에 여전히 app01 이라는 경로(key) 가 리스트에 나타나고 있는 상황. 이는 데이터의 특정 버전만 지워졌을 뿐 해당경로의 메타데이터가 남음. delete 명령어를 사용하면 삭제 표시(soft delete) 가 되거나 데이터만 지워질 뿐, 해당 시크릿의 이력과 설정을 담고 있는 메타데이터는 보존. 리스트에서 경로 자체를 보이지 않게 하려면 메타데이터까지 지워야함. vault kv metadata delete kv/applications/app01
Q12. When using the Transit secrets engine, setting the min_decryption_version will determine the minimum key length of the data key (i.e., 2048, 4096, etc.)
- True
- False
Ans. False
Exp1. min_decryption_version in the Transit secrets engine does not control the key length of the data key. It is specifically used to enforce a minimum version of the key for decryption purposes.
Kor. min_decryption_version 이 제어하는 대상이 무엇인가를 묻는 문제. 이 설정은 키의 물리적 길이(Bit) 가 아닌 생성된 순서(version) 를 관리하는 보안 장치.
Transit Secrets Engine 이란?
Vault 가 직접 데이터를 저장하지 않고, “암호화 서비스(Encryption as a Service)” 역할만 수행하는 엔진.
- 데이터 비보관 : 사용자가 평문을 보내면 Vault는 암호문만 반환하고, 원본 데이터나 암호문을 자신의 저장소에 남기지 않음
- 중앙 집중식 키 관리 : 앱이 직접 암호화 키를 가질 필요가 없음. 모든 키는 Vault 내부에서 안전하게 보호
- 암호화 오프로딩 : 복잡한 암호화 로직을 Vault 가 대신 처리하므로 개발자는 API 호출만으로 보안 강화
- Key Rotation : 명령 하나로 새로운 버전의 키 생성
- Rewarp : 데이터의 평문을 노출하지 않고도, 이전 버전의 키로 암호화된 데이터를 최신 버전의 키로 다시 암호화 가능
- Datakey 생성 : 대량의 데이터를 암호화해야 할 경우, Vault에서 직접 암호화하는 대신 외부에서 사용할 수 있는 일회성 데이터 키를 발급 받을 수 있음
Q13.
Tommy has written an AWS Lambda function that will perform certain tasks for the organization when data has been uploaded to an S3 bucket. Security policies for the organization do not allow Tommy to hardcode any type of credential within the Lambda code or environment variables. However, Tommy needs to retrieve a credential from Vault to write data to an on-premises database.
What auth method should Tommy use in Vault to meet the requirements while not violating security policies?
- AWS
- AppRole
- Token
- userpass
Ans. 1. AWS
Exp1. Using the AWS auth method in Vault allows Tommy to authenticate using AWS IAM credentials without hardcoding any credentials in the Lambda function or environment variables, meeting the security policy requirements.
Exp2. The userpass auth method in Vault is used for username and password authentication which would require Tommy to store credentials within the Lambda code or environment variables, violating the security policy.
Kor. S3에 데이터가 올라오면 실행되는 AWS Lambda 함수가 On-premises DB에 데이터를 기록해야함. 사내 DB에 접속하기 위한 Credential 이 필요함. 보안 정책상 ID/PW 를 하드코딩하거나 람다의 환경 변수에 저장할 수 없음.
AWS Auth Method 를 사용하면 Tommy 는 별도의 비밀번호를 입력하지 않고도 Vault 로부터 토큰을 받을 수 잇음. Lambda 함수는 AWS로부터 부여받은 IAM Role 신분을 이미 가지고 있음. Vault 의 AWS 인증 방식을 사용하면, Vault 가 AWS API 를 통해 “이 람다 함수가 정말 Tommy 가 만든 그 람다가 맞는지 “ 직접 확인. Tommy 가 코드에 비밀번호를 적을 필요 x 람다 자체가 자신의 IAM Role 을 Vault 에 제시
Q14. Given the following policy, which command below would not result in a permission denied error? (select two)
path "secret/*" {
capabilities = ["create", "update"]
allowed_parameters = {
"student" = ["steve", "frank", "jamie", "susan", "gerry", "damien"]
}
}
path "secret/apps/*" {
capabilities = ["read"]
}
path "secret/apps/results" {
capabilities = ["deny"]
}vault kv put secret/common/results student=frankvault kv put secret/apps/app01 student=bryanvault kv put secret/apps/results student03=practicevault kv put secret/apps/certificate key=afljkhdfojasgdvuogbvault kv list secret/apps/app01vault kv get secret/apps/api_key
Ans.
vault kv put secret/common/results student=frankvault kv get secret/apps/api_key
Exp1. vault kv put secret/common/results student=frank would result in a permission denied error because the path “secret/app/app01” is not allowed for create or update capabilities in the policy
Exp2. vault kv get secret/apps/api_key would not result in a permission denied error because the path “secret/apps/api_key” is allowed for read capabilities in the policy.
Kor.
path "secret/*":secret/으로 시작하는 모든 경로에 대해 create와 update 권한을 줍니다. 단, 파라미터 중student의 값은 지정된 명단(steve, frank 등) 내에 있어야만 합니다.path "secret/apps/*":secret/apps/아래의 모든 경로에 대해 read 권한을 줍니다.path "secret/apps/results": 이 특정 경로에 대해서는 모든 접근을 deny(거부)합니다. Vault 정책은 더 구체적인 경로(Specific path)가 우선순위를 갖습니다.
Permission Denied 가 발생하지 않는 명령어
vault kv put secret/common/results student=frank- 경로:
secret/common/results는 첫 번째 규칙(secret/*)에 해당합니다. - 권한:
put명령어는create/update권한이 필요하며, 정책에 명시되어 있습니다. - 파라미터:
student값이frank로 설정되었으며, 이는 허용된 리스트(allowed_parameters)에 포함되어 있습니다. 따라서 허용됩니다.
- 경로:
vault kv get secret/apps/api_key- 경로:
secret/apps/api_key는 두 번째 규칙(secret/apps/*)에 해당합니다. - 권한:
get명령어는read권한이 필요하며, 정책에 명시되어 있습니다. 따라서 허용됩니다.
- 경로:
Q15. After decrypting data using the Transit secrets engine, the plaintext output does not match the plaintext credit card number that you encrypted. Which of the following answers provides a solution?
$ vault write transit/decrypt/creditcard\ ciphertext="vault:v1:cZNHVx+sxdMEr......."
Key Value
--- -----
plaintext Y3JlZGl0LWNhcmQtbnVtYmVyCg==- Vault is sealed, therefore the data cannot be decrypted. Unseal vault to properly decrypt the data
- The data is corrupted. Execute the encryption command again using a different data key
- The resulting plaintext data is base64-encoded. To reveal the original plaintext, use the
base64 —decodecommand. - the user does not have permission to decrypt the data, therefore Vault returns false data so as not to reveal if the data was actually encrypted by Vault
Ans. 3. The resulting plaintext data is base64-encoded. To reveal the original plaintext, use the base64 —decode command.
Exp1. The plaintext output is base64-encoded, so using the base64 --decode command will decode the base64-encoded data and reveal the original plaintext credit card number.
Kor. 결과로 나온 평문 데이터는 Base64 인코딩되어 있음. 원본을 보려면 base64 —decode 명령어를 사용해야함.
Vault 의 Transit 엔진은 바이너리 데이터나 특수 문자가 포함된 데이터를 안전하게 처리하기 위해, 암호화 전의 입력값과 복호화 후의 출력값을 모두 Base 64 인코딩된 상태로 주고 받음.
- 원본 데이터에 포함될 수 있는 줄바꿈, 공백, 특수 문자 등이 네트워크 통신 중에 깨지는 것을 방지(인코딩 이유)
- 출력된
Y3JlZGl0...문자열을 복사하여 터미널에서$ echo "Y3JlZGl0..." | base64 --decode명령을 실행하면 실제 신용카드 번호를 확인할 수 있습니다.
Vault 가 sealed 된 상태라면 아예 복호화 명령어 자체 실행 불가
데이터가 손상되었다면 복호화 과정에서 오류 발생. 권한이 없으면 에러 발생.
Q16. What are the primary benefits of running Vault in a production deployment over dev server mode? (select two)
- ability to enable auth methods
- persistent storage
- access to all of the secret engines
- encryption via TLS
- faster deployment
ans.
- persistent storage
- encryption via TLS
Exp1. Encryption via TLS ensures that all communication with Vault is encrypted, providingan additional layer of security for sensitive data.
Kor. 개발 모드는 편의를 위해 HTTP로 통신하지만 네트워크 상에서 시크릿이 평문으로 노출 될 위험 큼. 운영환경에서는 TLS(HTTPS)를 강제하여 클라이언트와 Vault 서버 간의 모든 통신을 암호화함으로써 민감한 데이터를 안전하게 보호. 운영 환경은 unseal, 인증서 설정, 스토리지 구성 등 복잡한 절차가 필요하여 배포 속도가 더 느림. a
Q17. Select the policies below that permit you to create a new entry of environment=prod at the path /secrets/apps/my_secret (select three)
#1
path "secrets/apps/my_secret" {
capabilities = ["update"]
}
#2
path "secrets/apps/*" {
capabilities = ["create"]
allowed_parameters = {
"environment" = ["dev", "test", "qa", "prod"]
}
}
#3
path "secrets/apps/my_secret" {
capabilities = ["create"]
allowed_parameters = {
"environment" = []
}
}
#4
path "secrets/+/my_secret" {
capabilities = ["create"]
allowed_parameters = {
"*" = []
}
}Ans. 2,3,4
Exp1. This policy allows creating a new entry at any path under secrets/ with the my_secret suffix, and it allows any parameter to be set. It does not restrict the environment parameter to a specific value, so it does not meet the requirements for creating a new entry with the specified environment at the path /secrets/apps/my_secret.
Kor. 특정 경로에 특정 파라미터(environment=prod) 를 사용하여 새로운 ㄷ이터를 생성할 수 있는 정책( policy) 차는 것.
#2. create 권한이 있음. allowed_parameters 리스트에 prod 포함 되어 있음
#3. create 권한이 있음. allowed_parameters 리스트가 비어있는 경우 모든 값 허용
#4. create 권한이 있음. + 와일드카드는 한 단계의 모든 경로를 의미하므로 secret/apps/my_secret 과 매칭됨. 모든 파라미터 미름에 대해 모든 값 허용
Q19. From the unseal options listed below, select the options you can use if you're deploying Vault on-premises. (select four)
- transit
- AWS KMS
- HSM PKCS11
- certificates
- key shards
ans.
- transit, AWS KMS, HSM PKCS11, key shards
Exp1. Assuming the Vault cluster has access to the services listed above, you can use any of these valid unseal options for a Vault cluster deployed on-premises. For example, if Vault is provisioned on-premises but has internet access, it can communicate with the public AWS KMS API endpoints to unseal Vault with a KMS key. (Remember that AWS services have public API endpoints)
Kor. 온프레미스 환경에 Vault 를 배포할 때 사용할 수 있는 unseal 옵션. 온프레미스 환경이라 하더라도 외부 서비스와의 통신이 가능하다면 클라우드 기반의 자동 unseal 도구를 활용 가능.
Key shards : Vault 의 가장 기본적인 unseal 방식. 마스터 키를 여러 조각으로 나누어 관리자들에게 배분. 일정 수 이상의 조각이 모여 Vault unseal 가능
AWS KMS : AWS 에서 제공하는 키 관리 서비스(KMS) 를 이용해 Vault 를 자동으로 unseal. 온프레미스 서버가 인터넷망을 통해 AWS KMS 의 퍼블릭 API 엔드포인트에 접근할 수 있다면, 클라우드에 있는 키를 사용하여 자동으로 봉인 해제.
Transit (Transit Auto Unseal) : 이미 운영 중인 또 다른 Vault 서버의 Transit 시크릿 엔진을 사용하여 현재 Vault 의 봉인을 해재하는 방식. 사내에 ‘중앙 보안 vault’ 가 구축되어 있다면, 이를 통해 다른 여러 대의 Vault 클러스터를 자동 unseal 구성
HSM PCKS11 : 하드웨어 보안 모듈(HSM)을 사용하여 unseal 키를 안전하게 보관하고 자동 unseal 수행
Q19. The Vault Secrets Operator does NOT encrypt client cache, such as Vault tokens and leases, by default in Kubernetes Secrets.
- True
- False
Ans. True
Exp1. The Vault Secrets Operator does not encrypt client cache, such as Vault tokens and leases, by default in k8s Secrets. This means sensitive information stored in the client cache may be exposed if proper encryption measures are not implemented. This can be added by configuring encrypted client cache.
Kor. VSO 가 K8s 환경에서 클라이언트 캐시 데이터를 처리하는 기본 방식에 관한 문제. VSO 는 기본적으로 K8s 시크릿에 저장되는 Vault 토큰이나 리스와 같은 클라이언트 캐시를 암호화 하지 않음.
VSO는 K8s 네이티브 시크릿 시스템과 연동되는데, 기본 설정 상태에서는 클라이언트 캐시(토큰, 리스 등)를 암호화하지 않은 상태로 K8s 시크릿에 저장. 캐시가 암호화되지 않으면, K8s 클러스터에 대한 접근 권한이 있는 공격자가 secrets 을 조회하여 민감한 Vault 토큰 정보를 노출시킬 위험이 있음.
Q20. During a service outage, you must ensure all current tokens and leases are copied to another Vault cluster for failover so applications don't need to authenticate.
How can you accomplish this?
- Replicate to another cluster using Performance Replication and promote the secondary cluster during an outage
- Have Vault write all the tokens and leases to a file so you have a second copy of them
- Configure Disaster Recovery replication and promote the secondary cluster during an outage
- Configure all application to use the auto-auth feature of the Vault Agent
Ans. 3. Configure Disaster Recovery replication and promote the secondary cluster during an outage
Exp1. Configuring Disaster Recovery replication allows you to replicate all tokens and leases to another Vault cluster for failover. By promoting the secondary cluster during an outage, applications can seamlessly continue to access the tokens and leases without needing to re-authenticate.
Kor. Disaster Recovery 복제는 주 클러스터의 모든 데이터(토큰, 리스, 설정, 시크릿 등) 모두 복제. 장애시 승격하면 재인증 과정 없이 새로운 클러스터에서 즉시 작업 이어감.
Performance 복제는 여러 지역에서 시크릿을 빠르게 읽기 위해 사용. 성능 복제는 각 클러스터가 고유한 토큰과 리스를 관리. 즉, 주 클러스터의 토큰은 보조 클러스터에 유효하지 않으므로 장애 조치 시 앱이 다시 인증
Q21. Which scenario most strongly indicates a need to run a self-hosted Vault cluster instead of using HCP Vault Dedicated?
- You want to offload all operational tasks and rely on HashiCorp to manage patching, upgrades, and infrastructure.
- Your organization does not require any custom security policies or intricate network topologies
- You prefer a fully managed environment that is readily scalable with minimal configuration overhead
- You must maintain specific compliance or custom integration requirements that demand full control over the Vault environment, including infrastructure provisioning and plugin development.
Ans. 4. You must maintain specific compliance or custom integration requirements that demand full control over the Vault environment, including infrastructure provisioning and plugin development.
Exp1. This choice highlights the need to maintain specific compliance or custom integration requirements that demand full control over the Vault environment, including infrastructure provisioning and plugin development. In such cases, running a self-hosted Vault cluster would be more suitable to have complete control over the environment.
Exp2. Different deployment options are available to support HahsiCups' business needs. The Vault Community edition supports a self-managed deployment model.
Vault Enterprise can also be self-managed and is available as a managed service through the HashiCorp Cloud Platform (HCP).
HashiCups would be responsible for the design, deployment, security, reliability, scaling, and upgrading for the Vault cluster when deploying in a self-managed model. When using HCP Vault Dedicated, HashiCups would need to select the appropriate size and tier for the Vault cluster.
Some features such as FIPS 140-2 and seal wrapping are not available with the HCP deployment option.
Kor. HashiCorp Cloud Platform(HCP) Vault Dedicated 대신 Self-hosted(직접 설치형) Vault 클러스터를 운영해야하는 가장 강력한 상황
- 인프라 통제권(Full Control) : 데이터가 저장되는 물리적 서버나 VM의 위치
Q22. A Jenkins server is using the following token to access Vault. Based on the lookup shown below, what type of token is this?
$ vault token lookup hvs.FGP1A77Hxa1Sp6Pkp1yURcZB
Key Value
--- -----
accessor RnH8jtgrxBrYanizlyJ7Y8R
creation_time 1604604512
creation_ttl 24h
display_name token
entity_id n/a
expire_time 2025-11-06T14:28:32.8891566-05:00
explicit_max_ttl 0s
id hvs.FGP1A77Hxa1Sp6KRau5eNB
issue_time 2025-11-06T14:28:32.8891566-05:00
meta <nil>
num_uses 0
orphan false
path auth/token/create
period 24h
policies [admin default]
renewable true
ttl 23h59m50s
type service- orphaned token
- periodic token
- batch token
- secondary token
Ans. 2. periodic token
Exp1. The token in the lookup has a period set, indicating that it is a periodic token that will automatically renew within the specific period
Kor. vault token lookup 결과에 대한 문제. period 가 설정된 토큰은 주기적 토큰(Periodic Token)” 으로 분류됨. 이 토큰은 유효 기간(TTL) 내에 갱신(Renew)될 때마다, 처음 설정된 주기(24시간) 만큼 수명이 계속 연장.
일반적인 토큰은 max_ttl 이라는 최대 수명이 있어 결국 만료되지만, 주기적 토큰은 주기적으로 갱신만 해준다면 무한히 유지될 수 있음.
orphaned token : 결과의 orphan 항목이 false 이므로 고아토큰이 아님(부모토큰이 삭제되어도 살아남는 토큰을 의미)
batch token : type 항목이 service 로 명시되어 있음. 배치 토큰은 저장소에 기록되지 않는 매우 가벼운 토큰이며, 갱신이 불가능하다는 특징이 있음
secondary token : 복제된 클러스터 간의 관계에서 사용되는 용어로, 이 룩업 결과와는 직접적인 관련이 없음
Q23. How long does the Transit secrets engine store the resulting ciphertext by default?
- 32 days
- 30 days
- transit does not store data
- 24 hours
Ans. 3. transit does not store data
Exp1. The transit secrets engine in Vault does not store the resulting cipher-text by default. It is designed to perform encryption and decryption operation in real-time without persisting the data.
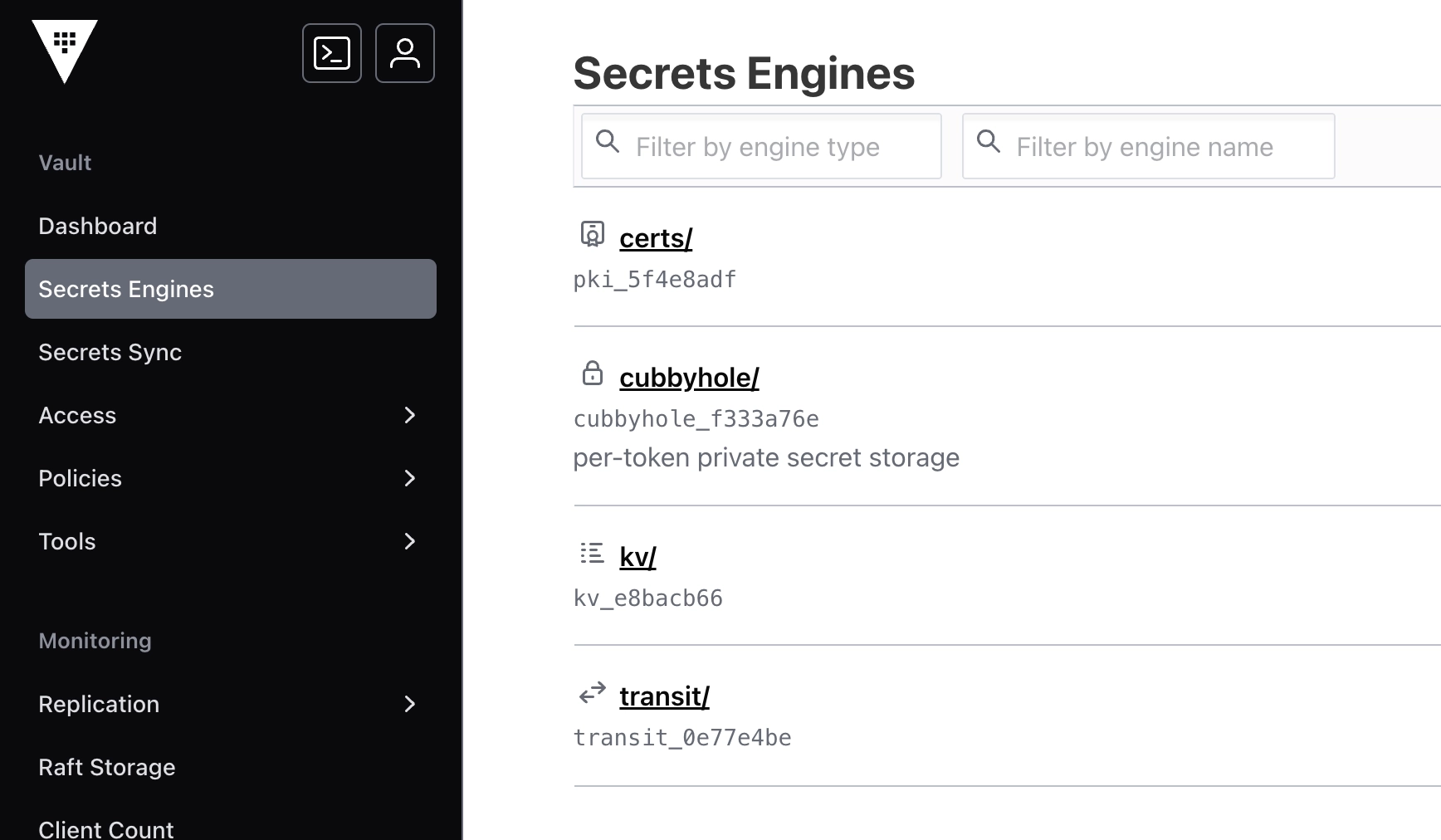
Q24. Given the following screenshot, how many secrets engines have been enabled by a Vault user?
- 5
- 3
- 4
- 2
Ans. 2. 3
Exp1. 3 secrets engines enabled by the Vault user. Cubbyhole is enabled automatically for every Vault token.
Kor. cubbyhole 은 Vault 서버가 실행될 때 모든 토큰에 대해 자동으로 활성화되는 시스템 기본 엔진. 따라서 사용자가 명시적으로 활성화 명령을 내린 엔진은 3개( certs/ kv/ transit/)
kv/ (Key-Value Secrets Engine)
→ 가장 기본적이고 널리 쓰이는 데이터 보관소. 앱의 설정 파일에 하드코딩된 비밀번호나 API 를 제거하고, Vault 내부에 안전하게 격리하여 관리하기 위해 존재. DB 접속 정보 보관시 사용됨(앱이 읽어갈 비밀번호를 저장할 때 사용)
transit/ (Transit Secret Engine)
→ Vault 가 직접 데이터를 저장하지 않고, 암호화 및 복호화 API 만 제공하는 서비스형 암호화 엔진. DB 필드 단위로 암호화를 수행할 때 사용
certs/ (PKI Secrets Engine)
→ 디지털 신분증을 발급해주는 사내 인증 기관(CA). X.509 인증서(SSL/TLS) 를 동적으로 발급하고 관리하는 엔진. 서버 간 암호화 통신(VM 사이의 통신을 암호화하기 위한 인증서 발급 시 사용)
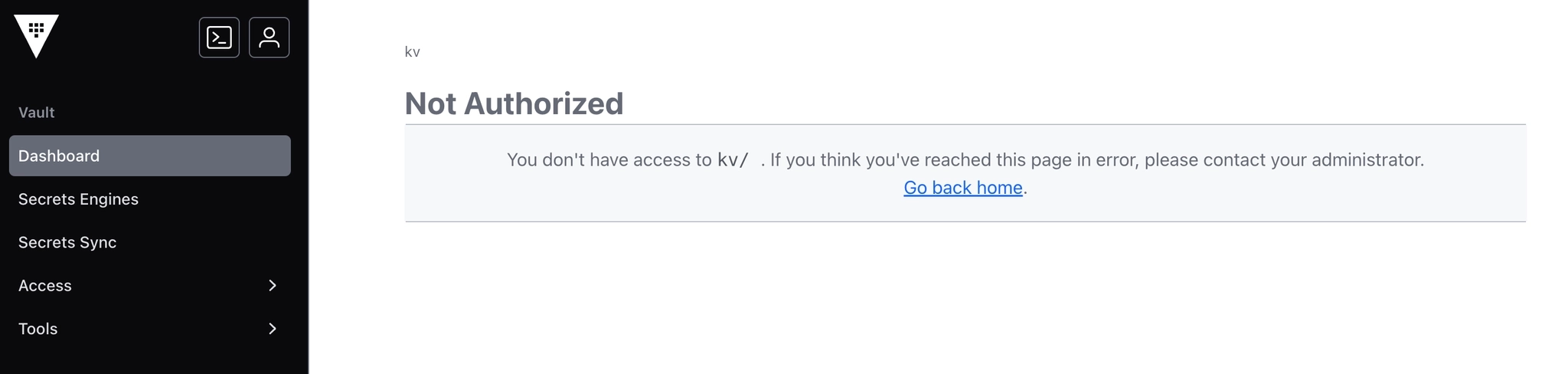
Q34. A user is assigned the following policy, and they can successfully retrieve secrets using the CLI. However, the user reports receiving the following error message in the UI. Why can't the user access the secret in the Vault UI?
path "kv/apps/app01" {
capabilities = ["read"]
}Successful retrieval using the CLI
Error message from the Vault UI:
1. the user needs list permissions to brows the UI
2. the user does not have permissions to retrieve the data from the UI, only the CLI
3. the user’s token is invalid
4. the user does not know what they are doing
Ans. 1. the user needs list permissions to brows the UI
Exp1. The error message in the Vault UI indicates that the user needs “list” permissions in addition to “read” permissions to access the secret. Without the “list” permission, the user will not be able to browse and access the secret in the Vault UI
Exp2. The user is able to retrieve the data using the CLI, which means they have the necessary permissions to access the secret. The issue lies in accessing the secret through the UI, not in the user’s permissions to retrieve the data.
Kor.
Policy 설명 : kv 이름의 시크릿 엔진 내부, apps/app01 이라는 경로에 대해서만 read 권한을 줌. vault kv get kv/apps/app01 명령을 내리면, Vault 는 경로를 탐색하지 않고 해당 주소로 직접 접근하여 데이터를 가져옴. read 권한이 있기 때문에 성공.
UI 에서 실패한 이유 : Vault UI는 웹 브라우저 기반이므로 사용자가 클릭하며 폴더를 찾아 들어가야 함. kv/ 폴더를 클릭하고, 그 안의 apps/ 폴더를 클릭하는 과정에서 해당 경로에 무엇이 있는지 목록을 보여주는 list 권한이 필요함. 현재 정책에서는 list 가 없으므로 권한 없음을 띄움
Read : 특정 경로에 있는 데이터의 상세 내용을 가져오는 권한. 금고 안에 있는 문서의 내용을 읽는 것
list : 특정 경로 아래에 어떤 항목들이 있는지 목록을 보는 권한. 금고 복도에서 어느 사물함들이 있는지 확인하는 것
Q35. What is the proper command to enable the AWS secrets engine at the default path?
vault enable secrets awsvault enable aws secrets enginevault secrets enable awsvault secrets aws enable
Ans. 3. vault secrets enable aws
Exp1. The command format for enabling Vault features is vault <feature> <enable/disable> <name>, therefore the correct answer would be vault secrets enable aws
Kor. vault [서브커맨드] [동작] [대상]
vault secrets enable [엔진이름] : 특정 시크릿 엔진을 기본 경로에 활성화
AWS Secrets engine 은 별도의 독립된 서버나 서비스가 아니라, Vault 서버 내부에 탑재된 하나의 기능 모듈
Vault 서버를 처음 설치하면 엔진들이 꺼져 있는 상태. 사용자가 vault secrets enable aws 명령어를 입력하는 순간, Vault 서버 안에서 AWS와 통신할 수 있는 엔진 활성화
Q36. After encrypting data using the Transit secrets engine, you've received the following output. Which of the following is true based on the output displayed below?
Key Value
--- -----
ciphertext vault:v2:45f9zW6cglbrzCjI0yCyC6DBYtSBSxnMgUn9B5aHcGEit71xefPEmmjMbrk3 - similar to the KV secrets engine, the transit secrets engine was enabled using the
transit v2option - the original encryption key has been rotated at least once
- the data is stored in Vault using a KV v2 secrets engine
- this is the second version of the encrypted data
Ans. 2. the original encryption key has been rotated at least once
Exp1. The output does not provide information about the version of the encrypted data. The “v2” in the ciphertext refers to the version of the encryption key, not the data itself.
Q37. From the options below, select the benefits of using a batch token over a service token. (select four)
- lightweight and scalable
- has accessors
- can be used on performance replication clusters (if orphan)
- often used for ephemeral, high-performance workloads
- can be a root token
- no storage cost for token creation
Ans.
- lightweight and scalable
- can be used on performance replication clusters (if orphan)
- often used for ephemeral, high-performance workloads
- no storage cost for token creation
Exp1. Batch tokens are designed to be lightweight and scalable, making them suitable for scenarios where a large number of tokens need to be generated and managed efficiently
Exp2. Batch tokens can be used on performance replication clusters if they are orphaned, meaning they can still be utilized in scenarios where token replication is required for maintaining system performance
Exp3. Batch tokens are well-suited for ephemeral and high-performance workloads, where tokens need to be generated and used quickly without incurring unnecessary overhead
Exp4. One of the advantages of using a batch token is that there is no storage cost associated with token creation, which can be beneficial in environments where minimizing storage usage is a priority
Q38. How can Vault be used to programmatically obtain a generated code for MFA, somewhat similar to Google Authenticator?
- cubbyhole
- the identity secrets engine
- the random byte generator
- TOTP secrets engine
Ans. 4. TOTP secrets engine
Exp1. The TOTP secrets engine in vault can be used to generate time-based one-time passwords for MFA, similar to Google Authenticator. The TOTP secrets engine can act as TOTP code generator. In this mode, it can replace traditional TOTP generators like Google Authenticator.
Q39. Below is a list of parent and child tokens and their associated TTL. Which token(s) will be revoked first?
├───hvs.y4fUERqCtUV0xsQjWLJar5qX - TTL: 4 hours
├───hvs.FNiIFU14RUxxUYAl4ErLfPVR - TTL: 6 hours
├───hvs.Jw9LMpu7oCQgxiKbjfyzyg75 - TTL: 4 hours
├───hvs.3IrlhEvcerEGbae11YQf9FvI - TTL: 3 hours
├───hvs.hOpweMVFvqfvoVnNgvZq8jLS - TTL: 5 hours - only
hvs.3IrlhEvcerEGbae11YQf9FvI - only
hvs.Jw9LMpu7oCQgxiKbjfyzyg75 - both
hvs.3IrlhEvcerEGbae11YQf9FvIandhvs.hOpweMVFvqfvoVnNgvZq8jLS - both
hvs.3IrlhEvcerEGbae11YQf9FvIandhvs.Jw9LMpu7oCQgxiKbjfyzyg75
Ans. 3. both hvs.3IrlhEvcerEGbae11YQf9FvI and hvs.hOpweMVFvqfvoVnNgvZq8jLS
Q40. Once you create a KV v1 secrets engine and place data in it, there is no way to modify the mount to include the features of a KV v2 secrets engine.
- True
- False
Ans. False
Exp1. In value, it is possible to modify a KV v1 secrets engine to include the features of a KV v2 secrets engine. This upgrade process allows for taking advantage of the additional security and functionality provided by the newer version of the secrets engine.
Exp2.
The kv enable-versioning command turns on versioning for an existing non-versioned key/value secrets engine (K/V Version 1) at its path.
*ProTip: You can use vault secrets list -detailed to see what version the KV store is using. Look under the Options header.*
-
map[] = v1
-
map[version:2] = v2
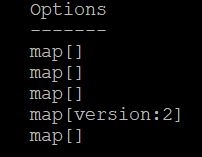
Kor. 시크릿 엔진 버전 업그레이드. KV v1 으로 이미 데이터를 넣어서 사용 중이더라도 명령어 한 줄로 KV v2 업그레이드 가능. v2 에는 없는 v1 에는 없는 보안 및 관리 기능 추가
KV v1 : 데이터의 현재 값만 저장. 수정하면 이전 값은 영구히 사라짐
KV v2 : 데이터의 버전 관리 가능. 실수로 데이터를 지워도 이전 버전으로 되돌릴 수 있고, 삭제된 데이터 복구
Q41. What command would have created the token displayed below?
$ vault token lookup hvs.nNeZ2I64ALCxuO7dqQEJGPrO
Key Value
--- -----
accessor mfvaVMFgOcXHIeqlRasroSOn
creation_time 1604610457
creation_ttl 768h
display_name token
entity_id n/a
expire_time 2024-12-07T16:07:37.7540672-05:00
explicit_max_ttl 0s
id hvs.nNeZ2I64ALCxuO7dqQEJGPrO
issue_time 2024-11-05T16:07:37.7540672-05:00
meta <nil>
num_uses 5
orphan false
path auth/token/create
policies [default dev]
renewable true
ttl 767h59m49s
type servicevault token create -policy=dev -ttl=768hvault token create -policy=devvault token create -policy=dev -use-limit=5vault token create -policy=dev -policy=default -ttl=768h
Ans. 3. vault token create -policy=dev -use-limit=5
Exp1. First command is incorrect because it specifies a different TTL value than the one displayed for the token
Exp2. The token displayed has a policy of “dev” and use limit of 5, so the correct command to create this token would be vault token create -policy=dev -use-limit=5
Kor. 사용자의 별도 설명이 없으면 토큰은 자동으로 768h(32일) 설정
Q42. Which of the following are accurate statements regarding the use of a KV v2 secrets engine? (select three)
- issuing a
vault kv metadata deletecommand permanently deletes the secret - issuing a
vault kv destroycommand permanently deletes the current version of the secret - issuing a
vault kv destroycommand deletes all versions of a secret - issuing a
vault kv deletecommand permanently deletes the secret - issuing a
vault kv deletecommand performs a soft delete of the current version
Ans.
- issuing a
vault kv metadata deletecommand permanently deletes the secret - issuing a
vault kv destroycommand permanently deletes the current version of the secret - issuing a
vault kv deletecommand performs a soft delete of the current version
Exp1. kv delete command deletes the data for the provided path in the key/value secrets engine. If using KV v2, its versioned data will bot be fully removed but marked as deleted and will no longer be returned in normal get requests.
Exp2. kv destroy command permanently removes the specified version’s data from the key/value secrets engine.
Q43. Which of the following Vault policies will allow a Vault client to read a secret stored at secrets/applications/app01/api_key?
#1
path "secrets/*" {
capabilities = ["list"]
}
#2
path "secrets/applications/+/api_*" {
capabilities = ["read"]
}
#3
path "secrets/applications/" {
capabilities = ["read"]
allowed_parameters = {
"certificate" = []
}
}
#4
path "secrets/applications/app01/api_key/*" {
capabilities = ["update", "list", "read"]
}
Ans. 2
Exp1. This policy uses globbing to match the path "secrets/applications/app01/api_key" and allows the client to only read the secret. It is the correct choice as it porivdes the necessary access without unnecessary permissions.
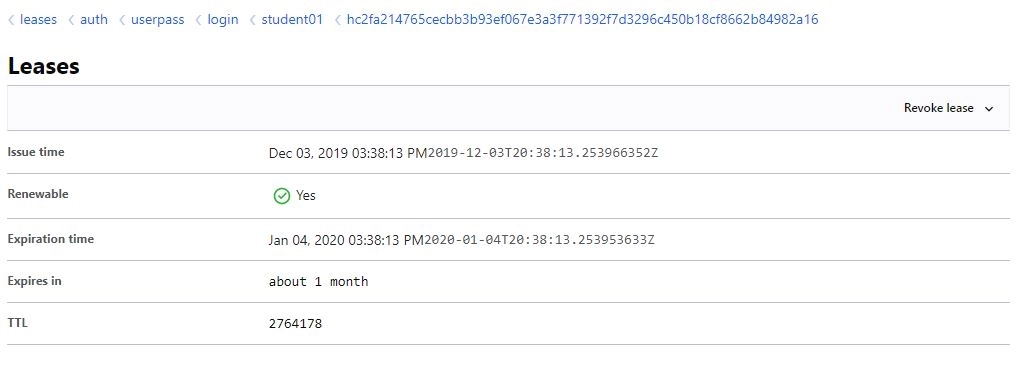
Q44. According to the screenshot below, what auth method did this client use to log in to Vault?
- root token
- userpass
- child token
- auth
Ans. 2. userpass
Exp1. The screenshot displays the “userpass” text, indicating that the client used the userpass authentication method to log in to Vault.
Kor. Vault 서버로부터 자신의 신분을 확인받고, 이후 작업에 필요한 토큰을 발급받는 과정. 스크린샷은 Vault UI의 Lease 화면으로 사용자가 userpass 방식을 통해 성공적으로 로그인한 화면
주요 인증 방법
- 사용자 중심
- Userpass : Valut 내부에 생성한 ID/PW 로 로그인
- github / Okta : 기존에 사용하던 외부 서비스 계정으로 로그인
- LDAP / AD : 사내먕(Active Directory) 계정 정보를 연동하여 로그인
- 시스템 중심
- AppRole : 앱에 부여된 Role ID 와 Secret ID 를 사용하여 로그인
- AWS / Azure / GCP : 클라우드 인스턴스의 IAM 권한을 이용하여 자동으로 로그인
- K8s : 쿠버네티스 pod 서비스 어카운트 사용하여 로그인
- 기본
- Token : 이미 발급받은 토큰 자체를 입력하여 접속
Q45. All dynamic secrets in Vault are required to have a lease.
- True
- False
Ans. 1. True
Exp1. All dynamic secrets in Vault are required to have a lease, which determine the duration for which the dynamic secret is valid. Once the lease expires, the dynamic secret is automatically revoked by Vault to ensure security and prevent unauthorized access.
Exp2. The benefit of leases should be clear: consumers of secrets need to check in with Vault routinely to either renew the lease or request a replacement secret. This makes the Vault audit logs more valuable and also makes key rolling a lot easier.
Q46. If Bobby is currently assigned the following policy, what additional policy can be added to ensure Bobby cannot access the data stored at secret/apps/confidential but still read all other secrets?
path "secret/apps/*" {
capabilities = ["create", "read", "update", "delete", "list"]
}#1
path "secret/apps/confidential/*" {
capabilities = ["deny"]
}
#2
path "secret/apps/*" {
capabilities = ["deny"]
}
#3
path "secret/apps/confidential" {
capabilities = ["deny"]
}
#4
path "secret/*" {
capabilities = ["read", "deny"]
}Ans. 3.
#1 will deny Bobby access to all secrets under secret/apps/confidential , but it does not address the requirement to all other secrets under secret/apps
#2 will deny Bobby access to all secrets under secret/app, including secret/app/confidential, which is not the desired outcome
#3 will specifically deny Bobby access to the data stored at secret/apps/confidential while still allowing access to all other secrets under secret/apps
#4 will not achieve the desired outcome as it only allows read access to all secrets under secret and denies all other operations, but it does not specifically address the restriction needed for secret/apps/confidential
Q47. When configuring Vault replication and monitoring its status, you keep seeing something called 'WALs'. What are WALs?
- warning of allocated logs
- write-ahead logs
- wake after lan
- write along logging
Ans. write-ahead logs
Kor. Vault 에서 복제 및 모니터링 시, 데이터베이스와 스토리지 시스템에서 데이터의 안정성을 보장하기 위해 사용하는 표준적인 기술로, Vault 의 고가용성(HA) 및 복제 메커니즘에서 핵심적인 역할 수행
WAL 은 데이터를 실제 저장소(DB) 에 영구적으로 기록하기 전, 수행할 작업 내용을 먼저 기록하는 로그 파일. 먼저 로그를 쓰고 나중에 데이터를 바꾼다 라는 뜻.
Q48. You logged into the Vault CLI and attempted to enable an auth method, but you received this error message. What can you do to resolve the error and configure Vault?
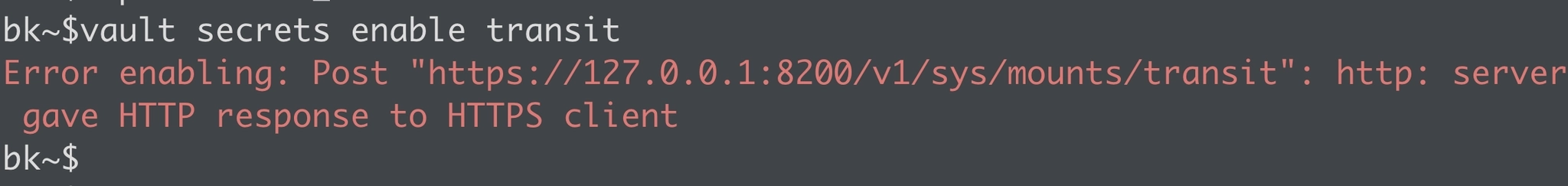
- ask an admin to grant you permission to enable the userpass auth method
- restart the Vault service on this node
- change ‘userpass’ to ‘userpass and password’
- set the
VAULT_ADDRenvironment variable to HTTP
Ans. 4. set the VAULT_ADDR environment variable to HTTP
Exp1. Setting the ‘VAULT_ADDR’ environment variable to HTTP will resolve the error as it specifies the address where the Vault server is running, allowing the CLI to communicate with the server.
Kor. 에러메시지는 Vault 사용 시 프로토콜 불일치(HTTP vs HTTPS)
HTTPS Client (CLI) : 사용자의 Vault CLI 는 보안 연결(https://) 로 서버에 말을 걸려고 시도
HTTP response (Server) : 하지만 실제 Vault 서버는 보안 기능이 꺼진 일반 연결(http://) 상태로 대기중
- Vault CLI 는 기본적으로
VAULT_ADDR환경 변수에 설정된 주소를 바라봄. 만약 이 변수가 설정되어 있지 않거나 https:// 로 되어있다면 CLI가 보안 통신 시도 - 터미널
export VAULT_ADDR='[http://127.0.0.1:8200](http://127.0.0.1:8200/)'입력하면 CLI가 더 이상 HTTPS를 고집하지 않게 되어 정상적으로 통신 가능
Q49. By default, what TCP port does Vault replication use?
- tcp/8301
- tcp/8300
- tcp/8200
- tcp/8201
Ans. 4. tcp/8201
Exp.
tcp/8301 : Serf protocal in Vault
tcp/8300 : Raft protocal in Vault
tcp/8200 : Default port for Vault’s HTTP API
tcp/8201 : Vault replication
Q50. What API endpoint is used to manage secrets engines in Vault?
/sys/mounts/sys/capabilities/sys/kv/secret-engines/
Ans. 1. /sys/mounts
Exp1. The correct API endpoint to manage secrets engines in Vault is /sys/mounts. This endpoint is used to mount and manage secrets engines with Vault, allowing user to enable, disable, and configure different secrets engines for storing and retrieving secrets securely.
Exp2. While the Key-Value secrets engine is commonly used in Vault, the correct endpoint for managing secrets engines is /sys/mounts, which is dedicated to managing all types of secrets engines in Vault.
Kor. Vault 에서 모든 시크릿 엔진의 생성, 수정, 삭제와 같은 관리 작업은 오직 /sys/mounts 엔드포인트를 통해 이루어짐. /sys/mounts 뒤에 내가 관리하고 싶은 엔진의 이름을 붙여 HTTP 요청을 보냄
- 활성화 :
POST /v1/sys/mounts/aws새로운 aws 엔진을 특정 경로에 생성 - 목록 확인 :
GET /v1/sys/mounts현재 Vault에 어떤 시크릿 엔진들이 어디에 설치되어 있는지 목록 확인 - 설정 변경 :
POST /v1/sys/mounts/<path>/tune해당 엔진에서 발행하는 시크릿의 TTL 수정 - 비활성화 :
DELETE /v1/sys/mounts<path>설치된 엔진 제거
Q51. Which of the following is NOT a valid way in which a lease can be revoked in Vault?
- via the CLI using the
vault tokencommand - using the user interface(UI)
- automatically when the TTL or Max-TTL expires
- using the API to call the
/v1/sys/leasesendpoint
Ans. 1. via the CLI using the vault token command
Exp1. Revoking a lease via the CLI using the vault token is not a valid way in which a lease can be revoked in Vault. The ‘vault token’ command is used for managing tokens, not for revoking leases.
Kor. vault token 명령어는 오직 토큰 자체의 생성, 조회, 취소 를 위해 존재. 리스만 특정해서 취소하고 싶을 때 vault lease
Q52. Which of the following statements are true regarding Vault seal and unseal? (select three)
- Vault uses recovery keys to automatically unseal during a service restart
- Vault can use a third-party KMS solution to automatically unseal during a service restart
- Vault supports high availability for the Auto Unseal feature, allowing you to point to multiple keys
- By default, Vault uses the Shamir Sharing algorithm to create unseal keys during the initialization process
- When using Vault Auto Unseal feature, Vault returns unseal keys to the user when it is initialized
Ans.
- Vault can use a third-party KMS solution to automatically unseal during a service restart
- Vault supports high availability for the Auto Unseal feature, allowing you to point to multiple keys
- By default, Vault uses the Shamir Sharing algorithm to create unseal keys during the initialization process
Exp1. Vault can indeed leverage a third-party Key Management Service(KMS) solution to automatically unseal itself during a service restart. This allows for a seamless unsealing process without intervention
Exp2. Vault Support high availability for the Auto Unseal feature, enabling users to configure multiple keys for unsealing. This redundancy enhances the reliability and availability of the unsealing process in case of key failures.
Exp3. By default, Vault utilizes the Shamir Sharing algorithm to generate unseal keys during the initialization process. This algorithm ensures secure key generation and distribution for unsealing Vault.
Q53. Jason has enabled the userpass auth method at the path users/. What path would Jason and other Vault operators use to interact with this new auth method?
- auth/users
- users/
- users/auth/
- authentication/users
Ans. 1. auth/users
Exp1. The auth/ in auth/users is required to access authentication methods.
Kor. Vault 의 모든 인증 방법은 기본적으로 auth/ 라는 시스템 예약 경로 아래에 위치해야 함
Q54. Which of the following secrets engines does NOT issue a lease upon a read request?
- KV
- Consul
- AWS
- Database
Ans. 2. Consul
Kor. 시크릿 엔진은 크게 두 종류로 나뉘어 리스 발급 여부가 결정됨.
Q55. You've hit the URL for the Vault UI, but you're presented with this screen. Why doesn't Vault present you with a way to log in?
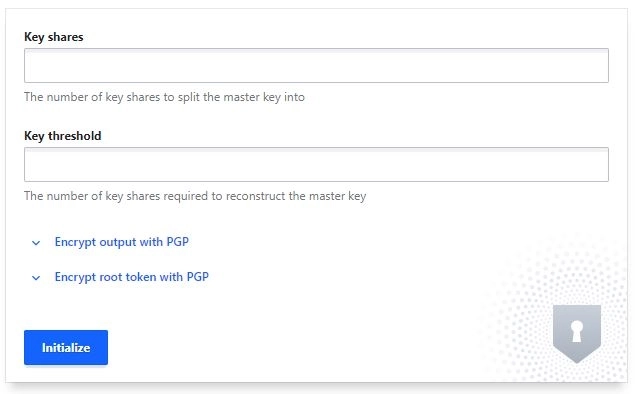
- the consul storage backend was not configured correctly
- vault needs to be initialized before it can be used
- the vault configuration file has an incorrect configuration
- a Vault policy is preventing you from logging in
Ans. 2. vault needs to be initialized before it can be used
Exp1. Vault needs to be initialized before it can be used, as the initialization process sets up the initial configuration and encryption keys required for Vault to operate securely
Kor. 스크린샷은 Vault 서버를 설치한 후 가장 먼저 수행해야하는 Initialization 단계.
Key shares : 마스터 키를 몇 개의 조각으로 나눌 것인지
Key threshold : Unseal 하기 위해 최소 몇 개의 조각이 필요한지
Q56. Which of the following statements best describes the difference in cluster strategies between self-managed Vault and HashiCorp-managed Vault?
- Self-managed clusters require users to handle setup, maintenance, and scaling, whereas HCP Vault Dedicated is fully managed by HashiCorp and offloads most operational tasks.
- In self-managed clusters, HashiCorp is responsible for scaling, upgrades, and patching, while HCP Vault Dedicated requires the user to handle all operational overhead.
- Both self-managed clusters and HCP Vault Dedicated require manual patching and upgrades, but only self-managed clusters are hosted in the user’s cloud.
- Neither self-managed clusters nor HCP Vault Dedicated include enterprise security features such as replication or disaster recovery.
Ans. Self-managed clusters require users to handle setup, maintenance, and scaling, whereas HCP Vault Dedicated is fully managed by HashiCorp and offloads most operational tasks.
Exp1.
Kor. Vault 를 내가 직접 설치해서 운영하느냐 Hashicorp에서 제공하는 클라우드 서비스로 쓰느냐 의 차이
| 구분 | Self-managed Vault (직접 관리) | HCP Vault Dedicated (매니지드) |
|---|---|---|
| 설치 및 구축 | 서버 준비, OS 설정, Vault 설치를 직접 수행 | 클릭 몇 번으로 HashiCorp 클라우드에 즉시 생성 |
| 운영 및 유지보수 | 사용자 책임: 패치, 업그레이드, 백업 직접 수행 | HashiCorp 책임: 버전 업그레이드 및 패치 자동 수행 |
| 확장성 (Scaling) | 트래픽 증가 시 서버 노드를 수동으로 추가 | 클릭이나 설정을 통해 운영 부담 없이 확장 가능 |
| 보안 및 가용성 | 고가용성(HA) 및 재해 복구(DR)를 직접 설계 | 엔터프라이즈급 보안 및 복구 기능이 이미 포함됨 |
| 모니터링 | 직접 모니터링 도구(Grafana 등)를 연동해야 함 | HashiCorp에서 기본적으로 모니터링 및 운영 대행 |
Q57. What could you do with the feature found in the screenshot below? (select two)
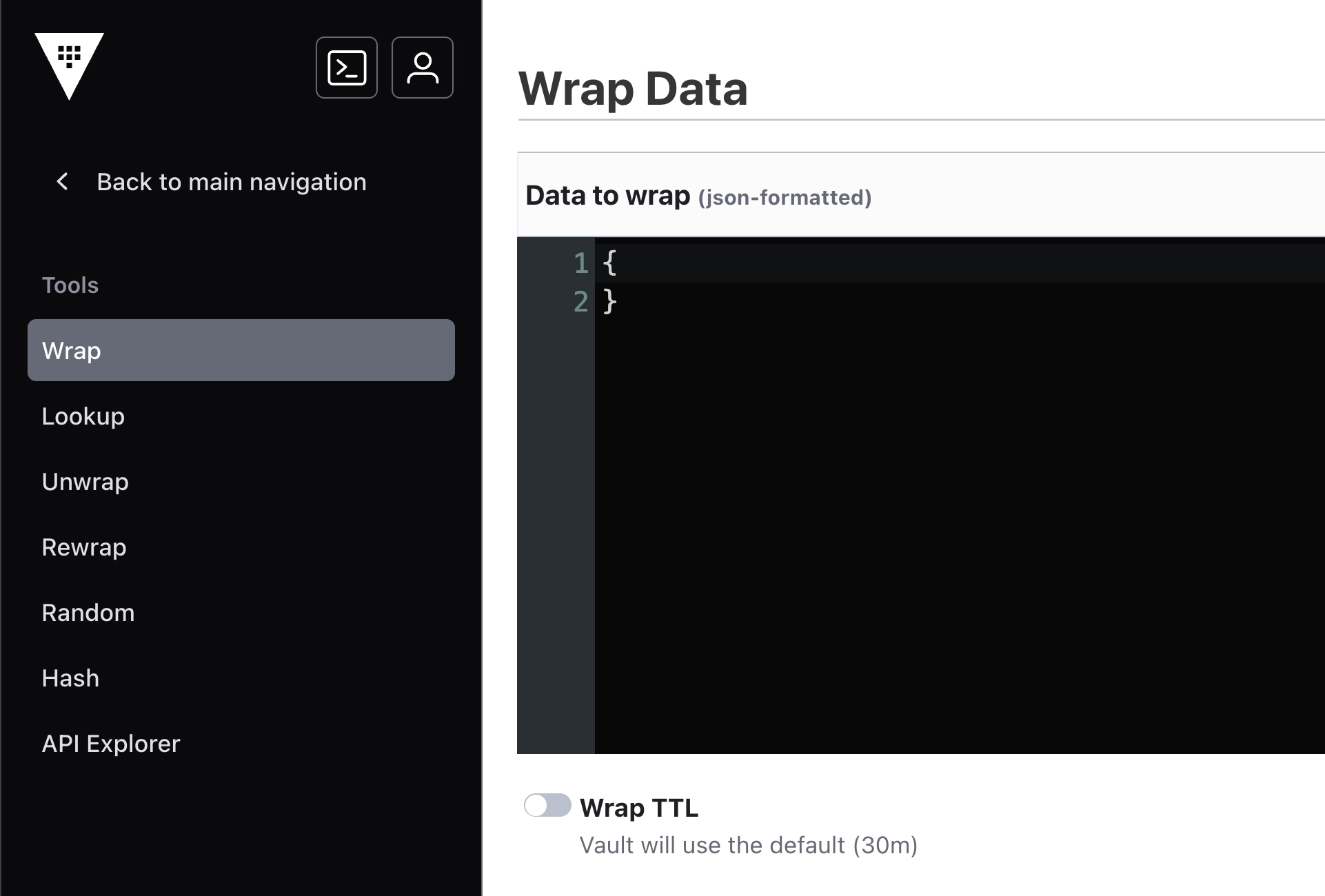
- use response-wrapping to protect data
- using a short TTL, you could encrypt data in order to place only the encrypted data in Vault
- encrypt sensitive data to send to a colleague over email
- encrypt the Vault master key that is stored in memory
Ans.
- use response-wrapping to protect data
- encrypt sensitive data to send to a colleague over email
Exp1. With the feature shown, you can use response-wrapping to protect data by wrapping the response in a secure token that can only be unwrapped by authorized parities, adding an extra layer of security
Exp2. The feature in the screenshot allows you to encrypt sensitive data before sending it to a colleague over email, ensuring the data remains secure during transit.
Exp3. Vault includes a feature called response wrapping. When requested, Vault can take the response it would have sent to an HTTP client and instead insert it into the cubbyhole of a single-use token, returning that single-use token instead. Logically speaking, the response is wrapped by the token, and retrieving it requires an unwrap operation against this token.
Sample Test #2
Q1. Once the minimum decryption version is set on an encryption key, older versions of the key are removed from Vault and are no longer available for decryption operations.
- True
- False
Ans. 2. False
Exp1. Setting the minimum decryption version on an encryption key in Vault does not automatically remove older versions of the key. Older versions are still retained in Vault and can still be used for decryption operations if necessary. The minimum decryption version simply specifies the minimum version of the key that can be used for decryption, but it does not delete older versions.
Q2. Compared to service tokens, batch tokens are ideal for what type of action?
- short-lived, high-volume, or “ephemeral” tasks
- for daily batch jobs requesting secrets from Vault
- generating dynamic credentials
- renewing other tokens
Ans. 1. short-lived, high-volume, or “ephemeral” tasks
Q3. Mike's Cereal Shack uses Vault to encrypt customer data to ensure it is always stored securely. They are developing a new application integration to send new customer data to be encrypted using the following API request:
curl \
--header "X-Vault-Token: hvs.sf4vj1rFV5PvQSV3M9dcv832brxQFsfbXA" \
--request POST \
--data @data.json \
https://vault.mcshack.com:8200/v1/transit/encrypt/customer-data What would be contained within the data.json file?
- transit secrets engine configuration file
- ciphertext to be decrypted
- the encryption key to be used for encrypting the data
- cleartext customer data to be encrypted
Ans. 4. cleartext customer data to be encrypted
Exp1. The data.json file would contain the cleartext customer data that needs to be encrypted. This data will be sent to the Vault API endpoint for encryption using the transit secrets engine.
Q4. Which of the following statements are true about HCP Vault Dedicated? (select three)
- increases reliability and ease of use so you can onboard applications and teams easily
- provides 100% feature parity compared to Vault self-managed clusters
- helps reduce operational overhead for organizations with push-button deployment and fully managed upgrades
- increases security across clouds and machines through a single interface
Ans.
- increases reliability and ease of use so you can onboard applications and teams easily
- helps reduce operational overhead for organizations with push-button deployment and fully managed upgrades
- increases security across clouds and machines through a single interface
Q5. All Vault policies are deny by default.
- False
- True
Ans. 2. True
Exp1. ll policies are deny by default. This means that unless a policy explicitly allows access to a certain path or operation, it will be denied by default. This security principle ensures that access must be explicitly granted, reducing the risk of unauthorized access to sensitive data or operations.
Q7. The Vault Agent provides which of the following benefits? (select three)
- token renewal
- client-side caching of responses
- authentication to Vault
- automatically creates secrets in the desired storage backend
Ans.
- token renewal
- client-side caching of responses
- automatically creates secrets in the desired storage backend
Q7. Which statement best explains the role and usage of storage backends in HashiCorp Vault?
- They store only unseal keys, while all secrets data remains in Vault’s memory
- They store only ephemeral tokens, ensuring no persistent data is ever saved.
- They handle the encryption of all secrets so that Vault remains completely stateless.
- They store Vault’s persistent data, affecting the scalability and performance of managing Vault.
Ans. 4. They store Vault’s persistent data, affecting the scalability and performance of managing Vault.
Exp1. Storage backends in HashiCorp Vault play a crucial role in storing Vault's persistent data, including secrets, policies, and audit logs. The choice of storage backend directly impacts the durability, scalability, performance, and overall complexity of managing Vault. Different storage backends offer various features and trade-offs, such as high availability, disaster recovery, and performance optimizations.
Q8. After initializing Vault or restarting the Vault service, each individual node in the cluster needs to be unsealed.
- True
- False
Ans. 1. True
Q9. Which two interfaces automatically assume the token for subsequent requests after successfully authenticating? (select two)
- CLI
- API
- UI
Ans. CLI & UI
Exp1. The CLI interface in Vault automatically assumes the token for subsequent requests after successful authentication.
Exp2. User interacting with Vault through the API must include the token in each request to authenticate and access resources
Exp3. The UI interface in Vault also automatically assumes the token for subsequent requests after successful authentication. This simplifies the user experience by eliminating the need to repeatedly enter the token for each interaction within the graphical user interface.
Q10. Which statement best explains how Vault handles data encryption?
- Vault offloads all encryption to third-party services, so no secret data is ever processed by Vault.
- Vault encrypts data using a root key stored in plain text on the server’s filesystem.
- Vault uses encryption to secure data at rest and in transit, using an encryption key protected by the root key.
- Vault stores data in plaintext on disk but encrypts it only when transmitting it over the network.
Ans. 3. Vault uses encryption to secure data at rest and in transit, using an encryption key protected by the root key.
Exp1. Vault follows best practices by using encryption to secure data both at rest and in transit. It uses an encryption key that is protected by the root key, ensuring that data is encrypted and secure throughout its lifecycle within Vault.
Q11. You have a long-running app that can not handle a regeneration of a token or secret. What type of token should be created for this application in order to authenticate and interact with Vault?
- Periodic Service Token
- Orphan Token
- Service Token with Use Limit
- Batch Token
Ans. 1. Periodic Service Token
Exp1. A Periodic Service Token is the most suitable option for a long-running application that cannot handle token or secret regeneration. Periodic Service Tokens are renewable tokens that can be renewed by the client indefinitely without user intervention, making them ideal for long-running processes that need continuous access to Vault.
Kor. Periodic Service Token 은 생성 시 period 를 설정. 만료되기 전(24시간 이내)에 갱신 요청을 보내면, 다시 24시간의 수명이 부여됨. 일반적인 서비스 토큰과 달리 Max TTL 이 없음. 즉, 앱이 돌아가는 동안 갱신만 갱신만 해주면 토큰 값이 변경되지 않음
Service Token with Use Limit 는 수명(TTL) 외에 사용할 수 있는 횟수에 제한을 두는 방식
Q12. After creating a dynamic credential on a database, the DBA accidentally deletes the credentials on the database itself. When attempting to remove the lease, Vault returns an error stating that the credential cannot be found.
What command can be run to make Vault remove the secret?
vault lease revoke -force -prefix <lease_path>vault lease revoke -enforcevault revoke -applyvault lease -renew
Ans. vault lease revoke -force -prefix <lease_path>
Exp1. Using the “-force” flag allows Vault to forcefully revoke the lease even if the credential cannot be found, ensuring that the secret is removed from the database.
Kor. Vault 와 DB 간의 상태 불일치 상황
Vault 가 동적 계정 생성을 하고 앱에게 알려준 상황. DB 관리자가 이를 삭제해 버림. 나중에 Vault 가 리스를 정리하려고 DB에 접속해 기존 생성된 동적 계성을 삭제하려고 했지만 이미 없음.
-force : 대상 시스템에서 실제 계정을 지우는 데 실패하더라도, Vault 내부의 리스 데이터는 강제로 삭제
-prefix : 특정 경로 하위의 모든 리스를 한꺼번에 지정할 때 사용
Q13. Which of the following best describes a token accessor?
- a value that describes which clients have access to the attached token
- describes the value associated with the tokens TTL
- a token used for clients to access Vault secrets engines
- a value that acts as a reference to a token which can be used to perform limited actions against the token
Ans. 4. a value that acts as a reference to a token which can be used to perform limited actions against the token
Exp1. A token accessor is a value that acts as a reference to a token, allowing limited actions to be performed against the token. It does not directly grant access to Vault secrets engines but rather serves as a way to interact with and manage the token itself.
Exp2. This choice is incorrect because a token accessor is not a token used by clients to access Vault secrets engines. Token accessors are used to manage and interact with tokens, not to directly access secrets within Vault.
Q14. Beyond encryption and decryption of data, which of the following is not a function of the Transit secrets engine?
- sign and verify data
- act as a source of random bytes
- generate hashes and HMACs of data
- store the encrypted data securely in Vault for retrieval
Ans. 4. store the encrypted data securely in Vault for retrieval
Exp1. Storing encrypted data securely in Vault for retrieval is not a function of the Transit secrets engine. The primary purpose of the Transit secrets engine is to handle encryption and decryption operations, while data storage and retrieval are typically managed by other Vault engines or systems
Q15. Which of the following unseal options can automatically unseal Vault upon the start of the Vault service? (select four)
- AWS KMS
- Transit
- HSM
- Key Shards
- Azure KMS
Ans. AWS KMS / Transit / HSM / Key Shards / Azure KMS
Exp1. Transit can automatically unseal Vault by using a pre-configured encryption key stored in Vault itself to encrypt the unseal key
Exp2. Key Shards are not an option for automatically unsealing Vault upon service start. Key Shards are typically used for Shamir's Secret Sharing to split the master key into multiple parts for added security.
Q16. Which of the following is not an action associated with the Transit secrets engine when interacting with data?
- update
- encrypt
- rewrap
- decrypt
Ans. 1. update
Q17. Which of the following statements best describes the difference between static and dynamic credentials in a secrets management system?
- They are functionally identical—the only difference is what secrets engine creates them.
- Static credentials only apply to specific use cases, while dynamic credentials can be used everywhere.
- Static credentials are ephemeral and rotated frequently, while dynamic credentials remain unchanged indefinitely.
- Static credentials often remain persistent for long periods of time, while dynamic are short-lived and auto-rotated.
Ans. 4. Static credentials often remain persistent for long periods of time, while dynamic are short-lived and auto-rotated.
Q18. Which of the following best describes the function of the Vault Secrets Operator in a Kubernetes environment?
- It continuously reconciles and synchronizes secrets from Vault to Kubernetes, ensuring secrets are always updated
- It replaces the Kubernetes secrets API entirely and operates purely as a certificate authority for all workloads.
- It provides an interface to dynamically provision Kubernetes clusters through Vault’s infrastructure secrets.
- It is a standalone Vault server that automatically applies security policies and rotates root tokens.
Ans. 1. It continuously reconciles and synchronizes secrets from Vault to Kubernetes, ensuring secrets are always updated
Kor. VSO의 핵심 역할은 동기화(Synchronization) 과 상태 유지(Reconciliation)
- 지속적인 동기화 : Vault 에 저장된 시크릿 데이터와 K8s 내부의 Secret 오브젝트를 실시간으로 비교. 만약 Vault 에서 값이 변경되면, VSO가 이를 감지하여 K8s 의 시크릿 값도 자동으로 업데이트
- 상태 조정 : 사용자가 “이 Vault 경로의 값을 K8s 시크릿으로 유지해줘” 라고 선언하면, VSO 가 계속해서 그 상태가 유지되도록 감시하고 조정
- Native 사용 : 앱 개발자는 Vault API를 직접 호출하는 복잡한 코드를 짤 필요 없이, 평소처럼 k8s secret 마운트해서 사용
오답 분석
API 대체 및 CA 역할 : VSO 는 k8s 의 Secret API를 대체하는 것이 아니라 활용. 또한, 모든 워크로드의 CA 역할을 수행하는 것은 Vault의 PKI 시크릿 엔진이나 cert-manager 의 역할이지 VSO 의 주 목적은 아님
클러스터 프로비저닝 : 인프라(클러스터 자체) 를 생성하는 것은 Terraform 이나 Crossplan 같은 도구의 영역. VSO는 이미 만들어진 클러스터 내부에서 시크릿 데이터를 관리하는 도구
독립형 Vault 서버: VSO 는 Vault 서버가 아님. 외부 혹은 내부의 Vault 서버와 통신하는 “클라이언트 앱”
Vault vs K8s Secret
보안과 관리의 중심은 Vault 에 두고, 앱이 읽기 편한 형태는 K8s Secret 에 위치
Vault : 모든 비밀번호의 “원본” 누가 언제 바궛는지(감사 로그), 언제 만료되는지(TTL), 버전 관리 등을 전문적으로 수행
K8s Secret(로컬 캐시) : K8s 환경에서 앱(pod) 이 시크릿에 접근하는 표준 방식. 앱이 굳이 복잡한 Vault API 사용법을 몰라도, 평소 하던 대로 환경 변수나 파일 마운트로 데이터를 가져갈 수 있게 배달해 놓은 결과물
K8s Secret 오브젝트
쿠버네티스에서 비밀번호, 토큰, 키 같은 민감한 정보를 저장하기 위해 만든 표준 리소스 타입
- 생성/갱신 : 원래 관리자가 kubectl create secret 으로 직접 생성. VSO를 쓰면 VSO가 관리자 대신 Vault 원본을 보고 K8s Secret 을 자동으로 생성
- 갱신 : 만약 사용자가 Vault 에서 비밀번호를 바꾸면, VSO가 k8s secret 오브젝트의 내용도 변경
Secret API(K8s) vs Vault API
Vault API : 원본 데이터를 가져오기(Pull) 위해 사용
K8s Secrets API : 가져온 데이터를 K8s 클러스터 내부 리소스로 쓰기(write) 위해 사용
역할 분담
VSO : “지시를 내리고 행동하는 주체” Vault를 계속 감시하다가 데이터가 바뀌면 K8s에도 업데이트라고 결정하고 움직이는 두뇌이자 손발
K8s Secrets API : 업데이트를 수행하는 통로. VSO가 K8s 내부에 데이터를 쓰고 싶을 때 무작정 쓰는게 아닌 API 호출해서 secret 오브젝트 내용을 바꿔줘 요청
Q19. Which of the following are benefits of using the Vault Secrets Operator (VSO)? (select three)
- automatic secret drift and remediation
- bi-directional sync between Vault and Kubernetes Secrets
- support for syncing from multiple secret sources
- automatic secret rotation for multiple Kubernetes resource types
Ans.
- automatic secret drift and remediation
- support for syncing from multiple secret sources
- automatic secret rotation for multiple Kubernetes resource types
Exp1. One of the key benefits of using the Vault Secrets Operator (VSO) is its ability to automatically detect and remediate secret drift. This means that if there are any discrepancies or unauthorized changes in the stored secrets, the VSO can automatically identify these issues and take corrective actions to maintain the integrity and security of the secrets.
Exp2. The Vault Secrets Operator (VSO) does not provide bi-directional sync between Vault and Kubernetes Secrets. While it facilitates the management of secrets within Kubernetes environments, it focuses on one-way synchronization from Vault to Kubernetes, ensuring that secrets are securely delivered and updated in Kubernetes resources.
Kor.
자동 드리프트 감지 및 복구(automatic secret drift and remediation) : 누군가 실수로 K8s Secret 의 값을 직접 수정했을 때(Drift), VSO 가 감지하여 (Vault 의 원본 데이터와 K8s의 복사본이 다르다는 걸 감지) K8s Secret 을 강제 복구(Remediation)
다양한 시크릿 소스 지원 : VSO는 단순히 KV 엔진뿐만 아니라, DB, AWS, PKI 등 Vault 의다양한 시크릿 엔진으로부터 데이터를 가져올 수 있음
Q20. You have deployed an application that needs to encrypt data before writing to a database. What secrets engine should you use?
- SSH
- Transit
- PKI
- TOTP
Ans. 2. Transit
Exp1. The TOTP (Time-based One-Time Password) secrets engine in Vault is used for generating time-based one-time passwords for two-factor authentication. It is not designed for encryption tasks like encrypting data before writing to a database.
Q21. Select the two default policies created in Vault. (select two)
- admin
- base
- default
- root
- vault
- user
Ans. default / root
Exp1. The "default" policy is another default policy created in Vault. It is a basic policy that grants limited access to certain operations and paths within Vault, making it a good starting point for users who do not need full administrative privileges.
Exp2. The "root" policy is one of the default policies created in Vault. It provides the highest level of access and control over the Vault system, including the ability to perform all operations and manage all policies and authentication methods.
Q22. Which statement most accurately describes how the response wrapping feature functions in Vault?
- Vault encrypts the response with a dedicated key and sends it directly to the client, never storing it on the server or using single-use tokens for additional security.
- Vault divides the response into separate parts and stores each part in different tokens, requiring all tokens to be combined before disclosing the secret to the requesting client.
- Vault takes the response it would have sent to an HTTP client and instead inserts it into the cubbyhole of a single-use token, returning that single-use token instead.
- Vault duplicates the response within a persistent token and allows multiple unwraps, ensuring that any user with the correct token can retrieve the secret repeatedly without time restrictions.
Ans. 3. Vault takes the response it would have sent to an HTTP client and instead inserts it into the cubbyhole of a single-use token, returning that single-use token instead.
