In this post, we’ll break down how to build a secure network architecture using well-known and widely adopted networking concepts.
VLAN
Virtual Local Area Network
One of the most effective ways to separate network areas is by using VLANs. Devices (nodes) in different VLANs are isolated at Layer 2, which helps mitigate the risk of unauthorized access and lateral movement by malicious actors.
Each isolated network area is commonly referred to as a VLAN or, from a security perspective, a security zone.
A switch is responsible for dividing a LAN into multiple VLANs. Modern switches can also enforce ACLs (Access Control Lists), perform traffic filtering, and apply QoS (Quality of Service) policies.
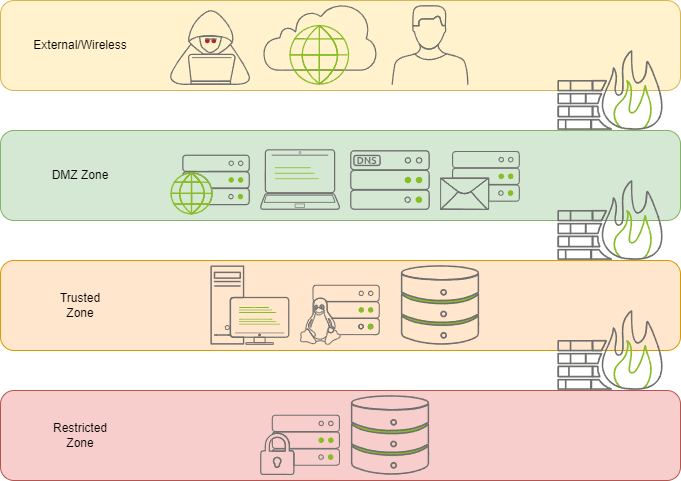
A commonly used secure network architecture
Why VLAN alone is not enough
VLANs separate only network devices logically at Layer 2 by isolating broadcast domains. they do not encompass the ability to control access. For example, by simply introducing a router between VLANs. They can start communicate.
Hence, It's important to note that A security boundary is estabilished at Layer 3 + 4 (Firewall, ACL)
Firewall
ACL vs Firewall
Stateless vs Stateful
The key difference between an ACL and a firewall lies in state awareness.
- ACLs are typically stateless. Each packet is evaluated independently based on predefined rules (source, destination, protocol, port, etc.).
- Firewalls are usually stateful. They keep track of established TCP/UDP sessions, allowing return traffic automatically if it belongs to a valid, previously established connection.
In AWS terms:
- ACLs are conceptually similar to Network ACLs (NACLs)
- Firewalls are conceptually similar to Security Groups
Firewalls also enforce security by controlling traffic between security zones, often referred to as zone-pairs.
Zone-Based Policy Example
The table below shows an example of zone-to-zone traffic control policies:
| Zone A | Zone B | Protocol | Action |
|---|---|---|---|
| LAN | WAN | ICMP | Drop |
| LAN | LOCAL | - | - |
| LAN | DMZ | - | - |
| WAN | LAN | ICMP | Accept |
| WAN | LOCAL | - | - |
| WAN | DMZ | - | - |
| LOCAL | LAN | - | - |
| LOCAL | WAN | - | - |
| LOCAL | DMZ | - | - |
| DMZ | LAN | HTTP | Accept |
| DMZ | WAN | - | - |
| DMZ | LOCAL | - | - |
-indicates that no explicit rule is defined. In most implementations, this means the default action (usually drop) is applied.
By combining VLAN-based segmentation with zone-based firewall policies, we can design a network that is not only segmented and optimized, but also secure by default.
