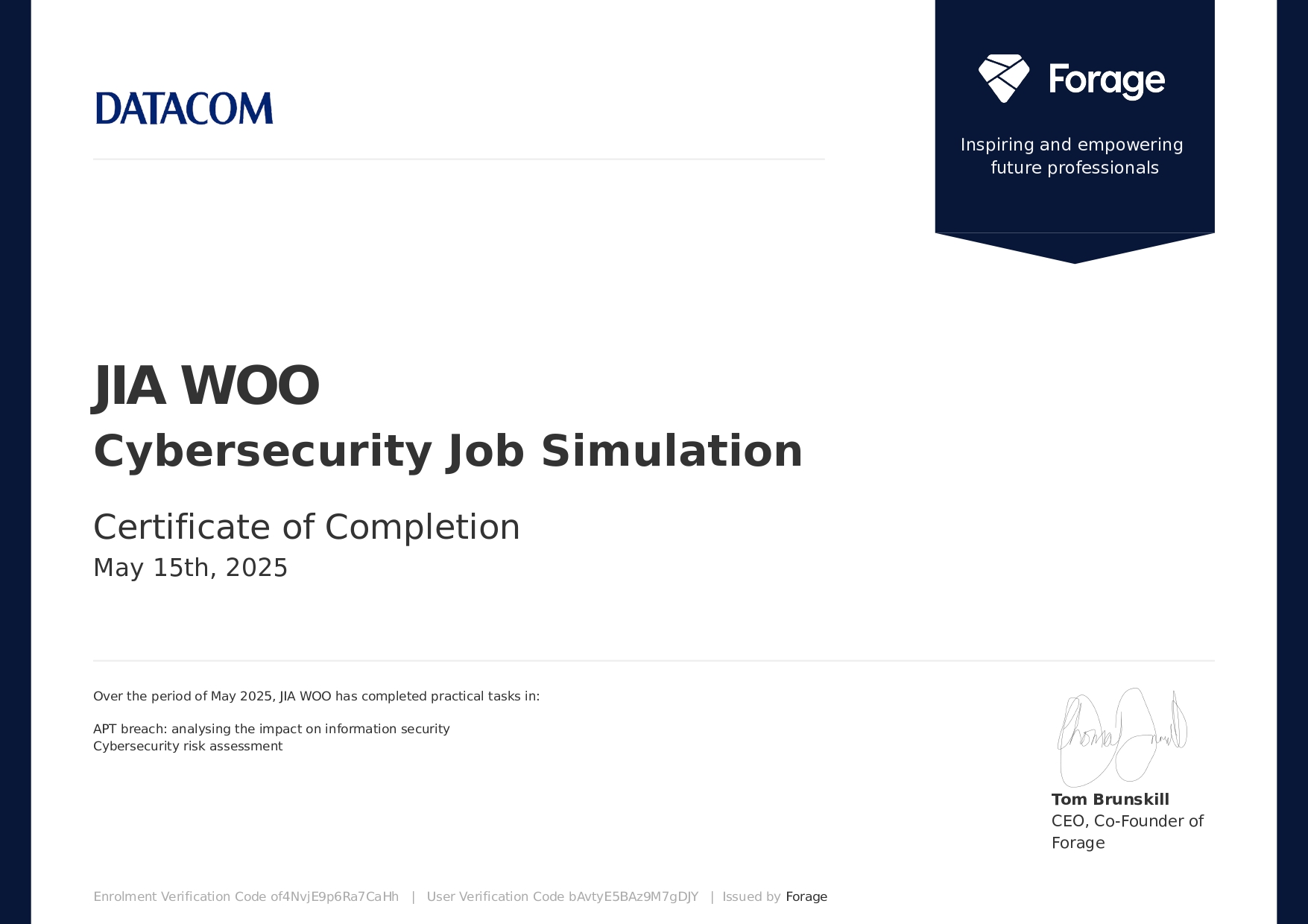
forage : DATACOM Cybersecurity Job Simulation
아젠다
- 사이버 공격을 조사하고 결과를 문서화하여 클라이언트 보안 태세 개선 권장사항 제시
- 위험 평가를 수행해 컨텍스트 정의, 위험 매트릭스 분석, 잠재적 위험 시나리오 식별
오픈소스 인텔리전스APT34 관련 정보를 수집하기 위한 (OSINT) 도구 및 기법
1. History of APT34
APT34 (also known as OilRig, Greenbug, and Helix Kitten) is a state-sponsored Iranian advanced persistent threat (APT) groupthat has been active since at least 2014.
The group primarily targets organizations in the Middle East, focusing on sectors such as energy, government, and telecommunications, with long-term espionage and intelligence-gathering operations.
Notable campaigns include:
• Deployment of malware tools such as QUADAGENTand POWBATagainst oil • companies (2016–2018)
• DNS-based command-and-control (C2)infrastructure attacks on diplomatic • entities
APT34 continues to be active and poses an ongoing threat to organizations worldwide.
2. National Attribution
APT34 is believed to be affiliated with the Iranian government, specifically the Islamic Revolutionary Guard Corps (IRGC).
The group operates in alignment with Iranian geopolitical objectives, exhibiting characteristics typical of a nation-state-sponsored cyber espionage operation, including targeted victim selection, persistence, and operational sophistication.
3. Targeted Industries
APT34 has demonstrated interest in multiple sectors, with particular emphasis on:
• Oil and gas
• Financial institutions
• Government and diplomatic organizations
• Aviation and defense
• Managed service providers (MSPs) and IT infrastructure companies
While early operations were regionally focused within the Middle East, recent activity indicates a strategic expansioninto North America, Europe, and parts of Asia, especially targeting foreign ministries, energy infrastructure, and technology firms.
4. Motivations and Strategic Objectives
The group’s operations are believed to support Iranian national interests, including:
• Political and diplomatic espionage: to gather intelligence for negotiations, • sanctions evasion, and foreign policy decision-making
• Industrial espionage: to obtain energy-sector secrets and enhance Iran's global • competitiveness
• Domestic surveillance: targeting dissident communities or opposition groups
APT34 does not appear financially motivated; rather, its operations are aligned with geopolitical and strategic intelligence collection.
5. TTPs (Tactics, Techniques, and Procedures) — MITRE ATT&CK
According to the MITRE ATT&CK framework, APT34 employs the following tactics and techniques:
■ Initial Access
• T1566.001– Spear Phishing Attachment
• T1190– Exploit Public-Facing Application
■ Execution
• T1059.001– PowerShell
• T1203– Exploitation for Client Execution
■ Persistence
• T1053.005– Scheduled Task
• T1547.001– Registry Run Keys / Startup Folder
■ Credential Access
• T1003.001– LSASS Memory
• T1555.003– Credentials from Web Browsers
■ Defense Evasion
• T1027– Obfuscated Files or Information
• T1036.005– Match Legitimate Name or Location
■ Command and Control
• T1071.001– Web Protocols (HTTP/HTTPS)
• T1105– Ingress Tool Transfer
6. Recommended Defensive Measures
Given APT34’s stealthy and persistent techniques, organizations must adopt a multi-layered defense strategyencompassing both technical and administrative controls.
■ Technical Controls
• Implement Multi-Factor Authentication (MFA)to mitigate credential theft
• Deploy EDR/XDR solutionsfor behavioral-based detection (e.g., PowerShell, web • shells)
• Configure Web Application Firewalls (WAFs)to block exploitation of public • services
• Implement User and Entity Behavior Analytics (UEBA)for anomaly detection
• Conduct regular vulnerability assessments and asset inventory checks
■ Administrative Controls
• Conduct phishing simulation trainingfor employees to improve threat awareness
• Perform regular incident response tabletop exercisesled by CSIRT
• Establish a MITRE ATT&CK-based threat hunting routinefor proactive detection
7. Conclusion and Strategic Recommendation
APT34 represents a highly capable and persistent threat actor, aligned with Iranian state interests. Their ability to infiltrate through spear phishing, exploit web-facing systems, and establish covert command-and-control channels demonstrates a mature threat profile.
Organizations—especially in energy, government, and infrastructure sectors—should treat APT34 as a credible and ongoing threat.
By applying a defense-in-depth approach, anchored in MITRE ATT&CK-based detection and response strategies, organizations can significantly improve their cyber resilienceand mitigate the risks posed by state-sponsored adversaries like APT34.위험성평가 : 클라이언트 요구사항 문서화
해당사항은 Forage 템플릿 docx 파일 진행하여 저작권 문제로 인해 업로드가 불가능 합니다
