forage job Simulation ANZ security Management
아젠다
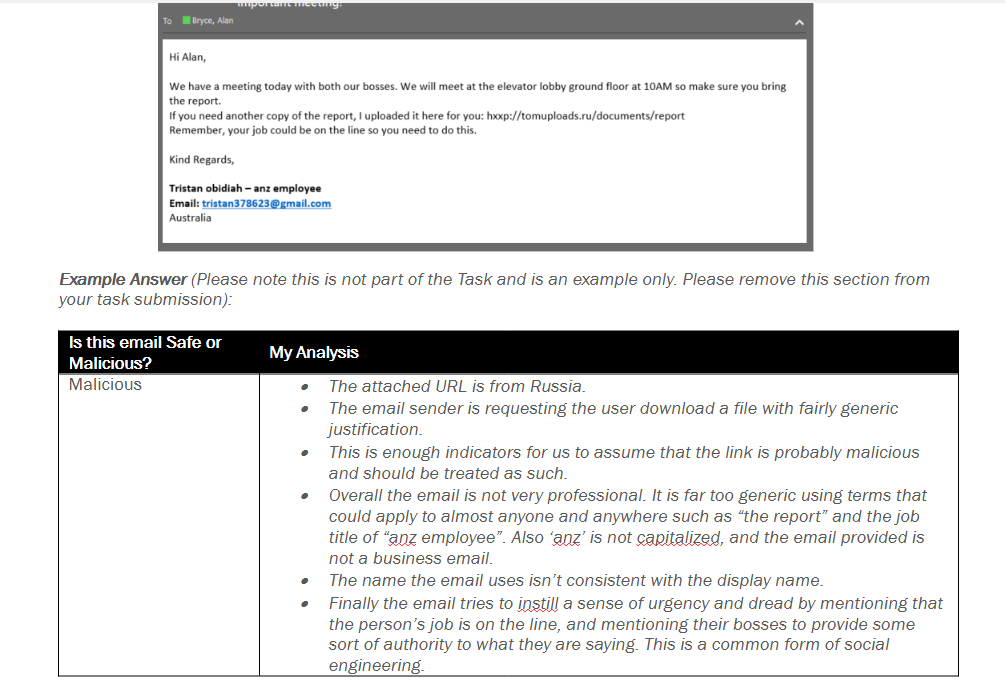
- 피싱 이메일을 식별 및 각 이메일이 안전한지 악성인지에 대한 결과를 보고
- 사용자의 최근 네트워크 활동이 포함된 패킷 캡처 파일검사
- 사용자가 액세스했을 수 있는 모든 아티팩트를 식별하는 보고서를 생성
할당 된 이메일 분석후 보고서 작성
forage 내 docx 템플릿 으로 작성 했습니다
의심스러운 인터넷 트래픽 조사 및 보고
Packet Capture Analysis Report
1. Analysis Tools Used
I used the following tools for the forensic investigation:
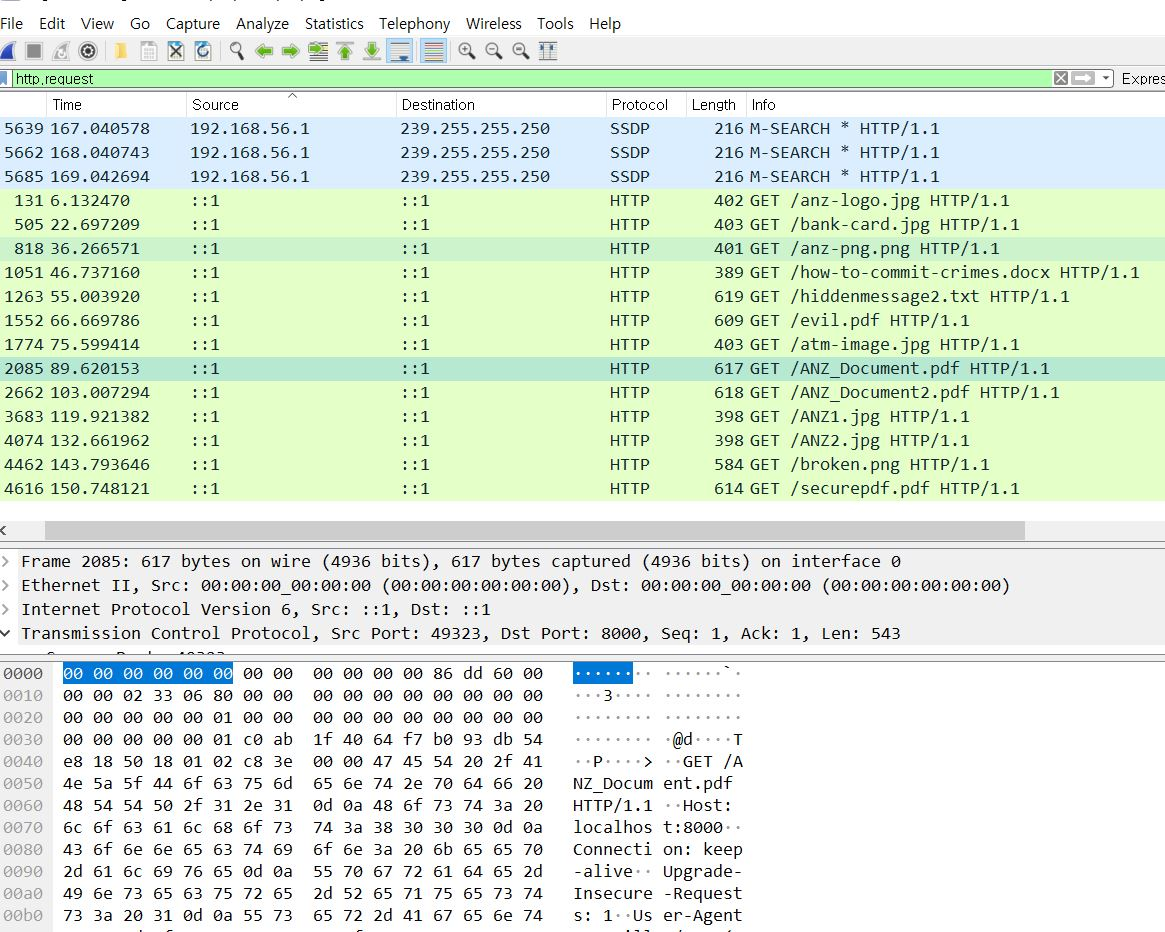
- Wireshark to analyze network packet capture (.pcapng) files
- HxD Hex Editor to isolate and reconstruct files from raw hexadecimal data
2. Identification of Suspicious Download
While filtering the `.pcapng` file using Wireshark, I applied the following filter:
`http.request`
This allowed me to isolate HTTP GET requests. One of the requests retrieved:
`GET /ANZ_Document.pdf HTTP/1.1`
This suggested that a PDF file had been downloaded over the network.
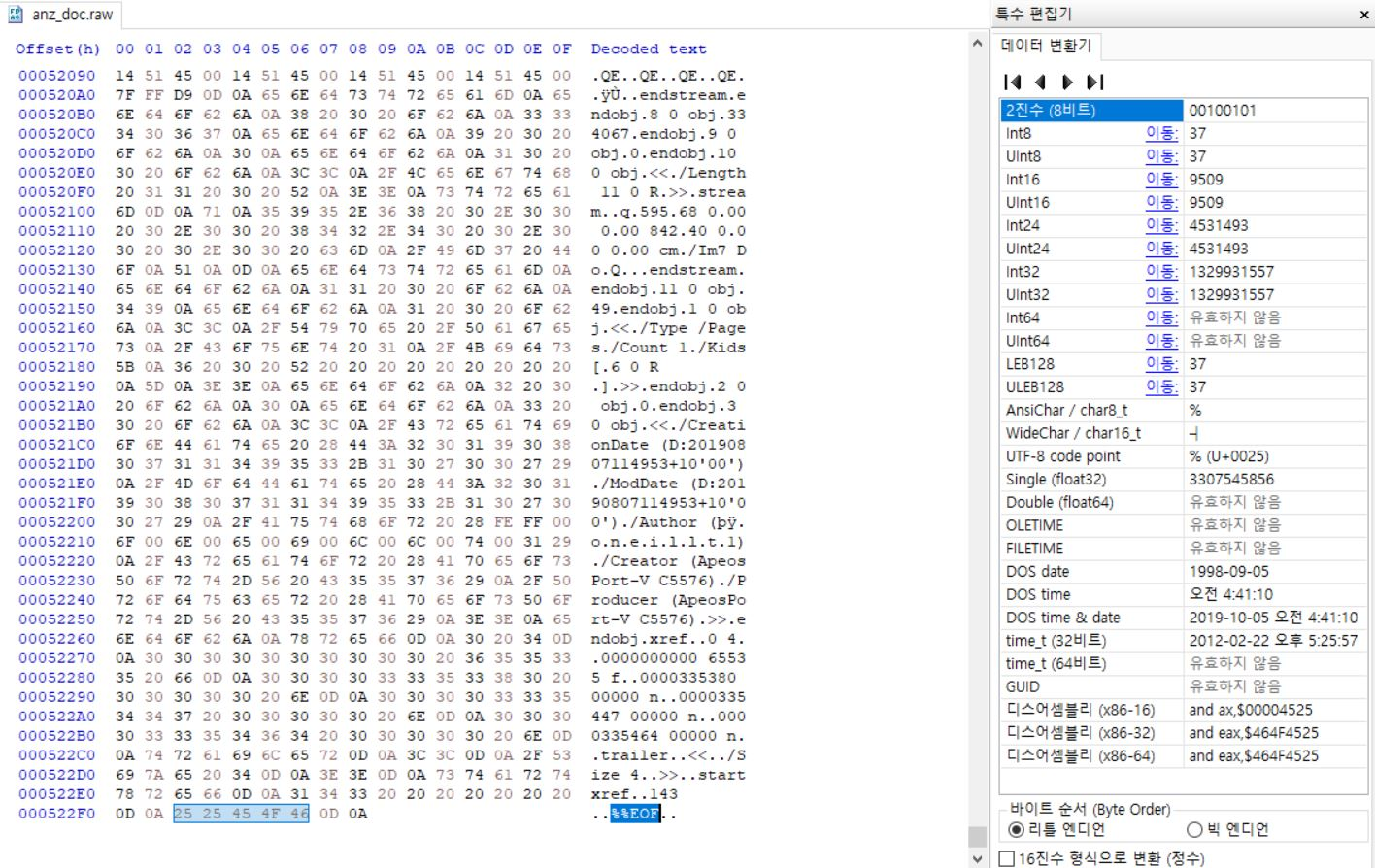
3. Extraction of TCP Stream
To examine the file contents, I right-clicked the GET request and selected:
Follow > TCP Stream
This revealed the full payload transferred. I saved the contents as a raw file: `anz_doc.raw`.
4. Hex Analysis and Signature Carving
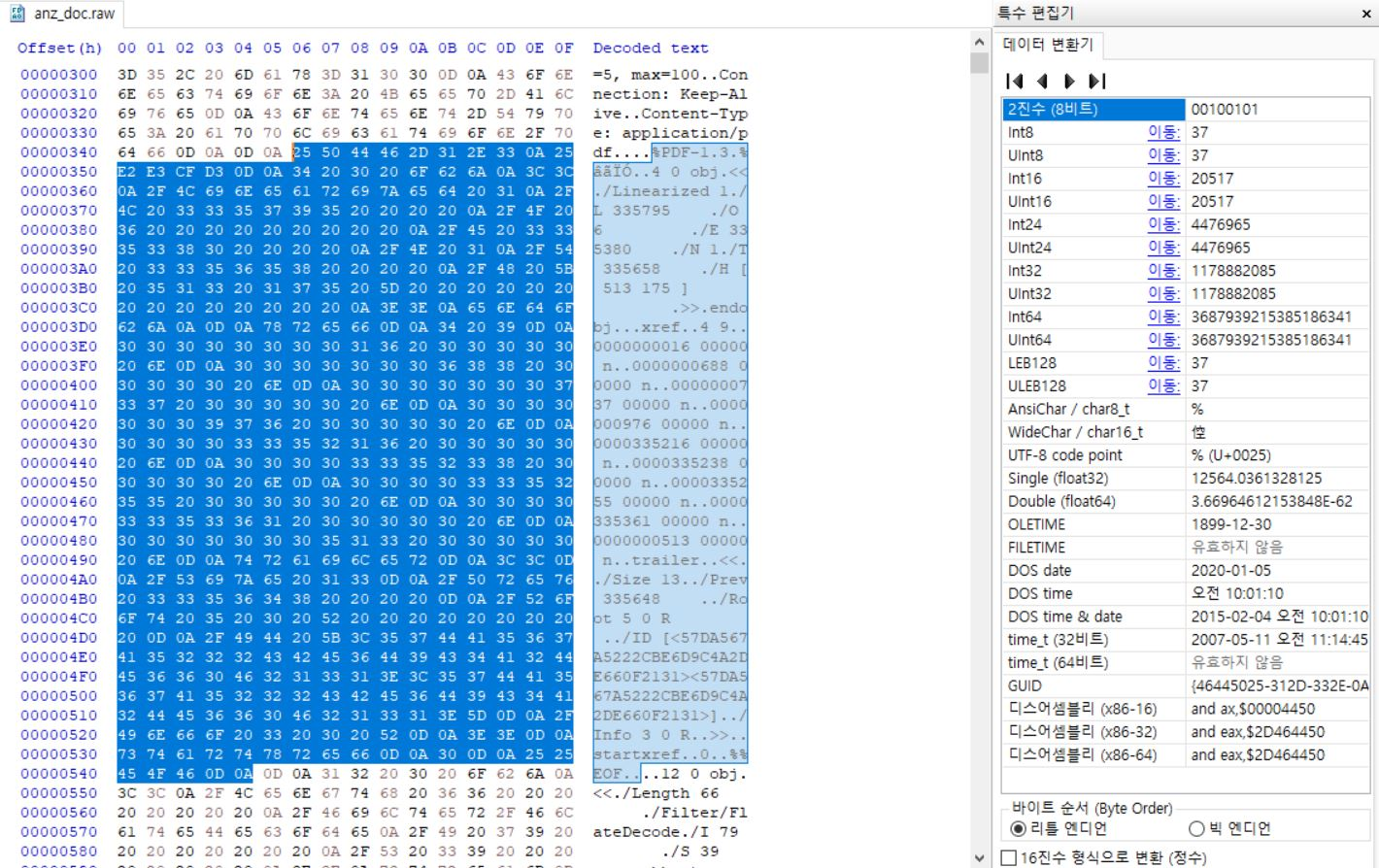
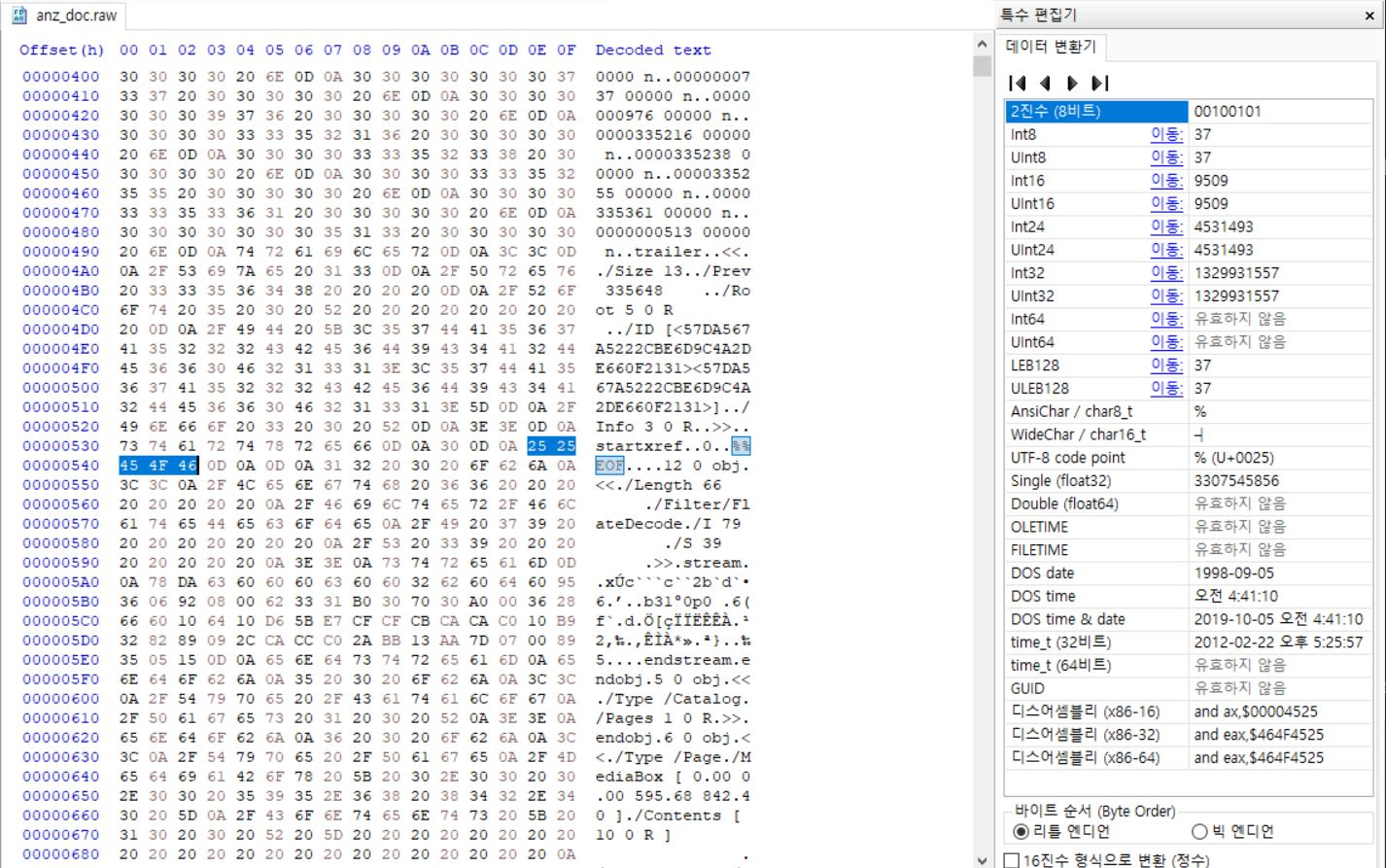
I opened `anz_doc.raw` in HxD and searched for the PDF file signature.
- Start of file: %PDF corresponds to 25 50 44 46 (hex)
- End of file: %%EOF corresponds to 25 25 45 4F 46 (hex)
Using these signatures, I selected all bytes from start to end of the PDF file in the hex editor.
5. Rebuilding the PDF File
I copied the selected hex region and pasted it into a new file within HxD.
The new file was saved as: `ANZ_Document_rebuilt.pdf`
After saving, I successfully opened the PDF file and confirmed its integrity and readability.
6. Conclusion
Through analysis of packet capture and raw byte data, I successfully reconstructed a PDF file that was transferred over HTTP. This demonstrates that full file recovery is possible using network forensic tools when proper signatures and carving techniques are applied.
7. Supporting Screenshots
Figure 1. Wireshark showing the GET request for ANZ_Document.pdf
Figure 2. TCP stream containing the PDF file content
Figure 3. Start of PDF file marked by %PDF signature in HxD
Figure 4. End of PDF file marked by %%EOF signature in HxD