4.1 Encrypt and decrypt by means of the RSA algorithm with the following system parameters
1
n=p⋅q=3⋅11=33
ϕ(n)=(p−1)(q−1)=2⋅10=20
7⋅e≡1(mod20)
7⋅3=21≡1(mod20), e=3
Public(e,n)=(3,33),
Private (d,n)=(7,33)
y≡53(mod33)
y=125(mod33)
26≡−7(mod33)
x≡267(mod33)
(−7)7≡4⋅(−7)=−28≡5(mod33)
x=5
2
n=5⋅11=55
ϕ(n)=40
3⋅d≡1(mod40)
Public (e,n)=(3,55)
Private (d,n)=(27,55)
y≡93(mod55)
x≡1427(mod55)
142=196≡31(mod55)
144≡312=961≡26(mod55)
148≡262=676≡16(mod55)
1416≡162=256≡36(mod55)
1427≡36⋅16⋅31⋅14(mod55)
36⋅14=504≡9(mod55)
x=9
2. Compute the two public keys and the common key for the DHKE scheme with the parameters p = 467, α = 2, and
1
Alice's Public Key: A≡αa(modp)
Bob's Public Key: B≡αb(modp)
Common Secret Key: K≡Ba(modp)≡Ab(modp)
p=467,α=2,a=3,b=5
A≡23(mod467), A=8
B≡25(mod467), B=32
K≡323(mod467)
K=32768(mod467)
32768=467⋅70+78
K=78
Alice's Public Key: A=8
Bob's Public Key: B=32
Common Key: K=78
2
p=467,α=2,a=400,b=134
A≡2400(mod467)
A=137
B≡2134(mod467)
B=84
K≡84400(mod467)
Alice's Public Key: A=137
Bob's Public Key: B=84
Common Key: K=90
3 Encrypt the following messages with the Elgamal scheme (p = 467 and α = 2)
ElGamal Formula
β≡αd(modp)
C1≡αi(modp)
KM≡βi(modp)
C2≡x⋅KM(modp)
KM≡C1d(modp)
x≡C2⋅KM−1(modp)
-
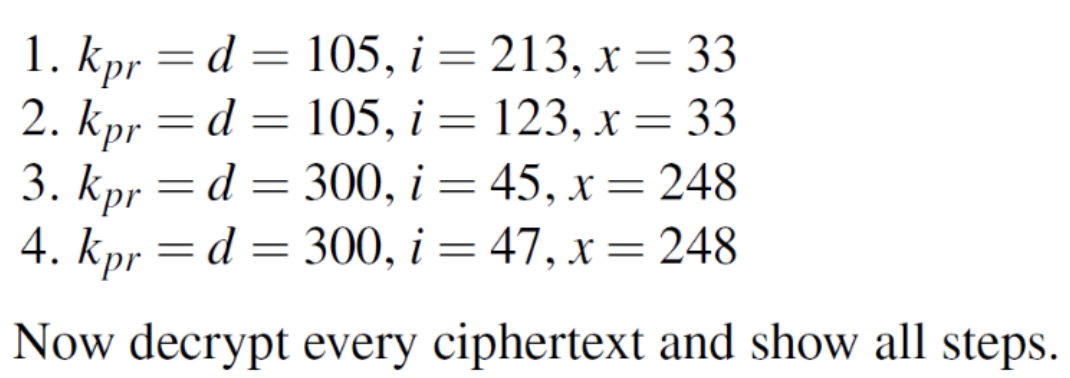
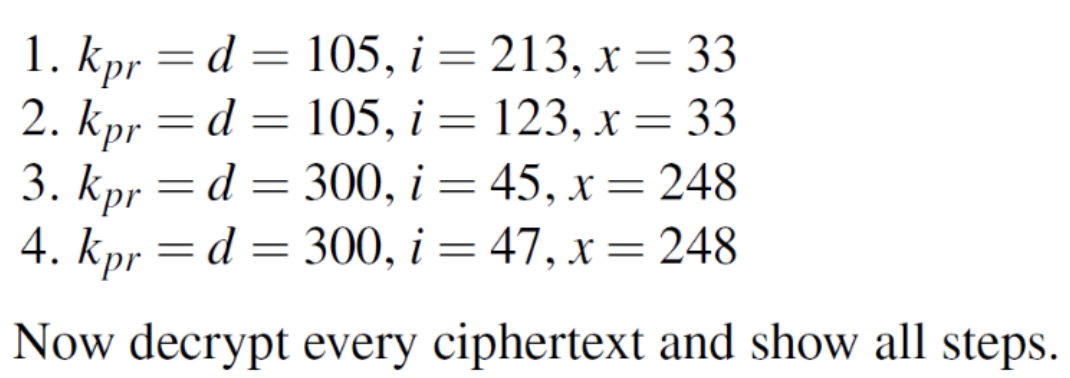
kpr=d=105,i=213,x=33
β≡2105(mod467)=226
C1≡2213(mod467)=29
KM≡226213(mod467)=234
C2≡33⋅234≡7722(mod467)=250
(C1,C2)=(29,250)
KM≡29105(mod467)=234
234−1(mod467)=2
x≡250⋅2=500≡33(mod467)
-
kpr=d=105,i=123,x=33
β≡2105(mod467)=226
C1≡2123(mod467)=274
KM≡226123(mod467)=353
C2≡33⋅353≡11649(mod467)=441
(C1,C2)=(274,441)
Decrypt
KM≡274105(mod467)=353
353−1(mod467)=340
x≡441⋅340=149940(mod467)=33
-
kpr=d=300,i=45,x=248
β≡2300(mod467)=153
C1≡245(mod467)=220
KM≡15345(mod467)=328
C2≡248⋅328≡81344(mod467)=86
(C1,C2)=(220,86)
Decrypt
KM≡220300(mod467)=328
328−1(mod467)=383
x≡86⋅383=32938(mod467)=248
-
kpr=d=300,i=47,x=248
β≡2300(mod467)=153
C1≡247(mod467)=413
KM≡15347(mod467)=314
C2≡248⋅314≡77872(mod467)=350
(C1,C2)=(413,350)
Decrypte
KM≡413300(mod467)=314
314−1(mod467)=409
x≡350⋅409=143150(mod467)=248
4.4 Considering the four examples from Problem we see that the Elgamal scheme is
nondeterministic: A given plaintext x has many valid ciphertext, e.g., both x = 33 and x =
248 have the same ciphertext in the problem above.
1. Why is the Elgamal signature scheme nondeterministic?
The ElGamal scheme is nondeterministic because a random ephemeral key (i) is chosen for every encryption process. Even if the plaintext and the public key remain identical, a different value of i will produce a completely different ciphertext pair. This inherent randomness prevents attackers from analyzing repeating patterns.
2. How many valid ciphertexts exist for each message x (general expression)?
How many are there for the system in Problem 4.1 (numerical answer)?
The number of valid ciphertexts corresponds to the number of available choices for the random variable i. Since i is selected from the multiplicative group modulo p, the general expression is p−1.
For the system in Problem 4.1 where p=467, the numerical answer is 466.
3. Is RSA crypto system nondeterministic once the public key has been chosen?
No, textbook RSA is deterministic. The algorithm relies on the fixed mathematical equation y≡xe(modn). Unless an external randomized padding scheme (such as OAEP) is applied, encrypting the same plaintext with a given public key will always generate the exact same ciphertext.
5. Given EC:
E: 𝑦2 ≡ 𝑥3 + 2𝑥 + 2 mod 17.
All points on the curve form a cyclic group and that the order is #E = 19. The basepoint/primitive element is 𝑃 = (5,1), please calculate 2P, 3P, 4P, 5P, 6P, 7P, 8P, 9P, 10P, 11P, 12P, 13P, 14P, 15P, 16P, 17P, 18P and 19P
Elliptic Curve E:y2≡x3+2x+2(mod17)
Base point P=(5,1)
Order #E=19
P=(5,1)
2P=(6,3)
3P=2P+P=(10,6)
4P=3P+P=(3,1)
5P=4P+P=(9,16)
6P=5P+P=(16,13)
7P=6P+P=(0,6)
8P=7P+P=(13,7)
9P=8P+P=(7,6)
Using Symmetry
(19−k)P=−kP, (x,−y(modp))
10P=−9P=(7,−6(mod17))=(7,11)
11P=−8P=(13,−7(mod17))=(13,10)
12P=−7P=(0,−6(mod17))=(0,11)
13P=−6P=(16,−13(mod17))=(16,4)
14P=−5P=(9,−16(mod17))=(9,1)
15P=−4P=(3,−1(mod17))=(3,16)
16P=−3P=(10,−6(mod17))=(10,11)
17P=−2P=(6,−3(mod17))=(6,14)
18P=−P=(5,−1(mod17))=(5,16)
19P=O (Point at infinity)