Cybersecurity
1.Substitution cipher, classification of Attacks

computational complexity 1. classification mordern app of cybersecurity cloud computting, email encrypt credit card vpn E passport LLM cybersecurity
2.Modular Arithmetic, ultiplicative Inverse, Shift & Affine Cipher

Classical Cryptography & Modular Arithmetic 1.Substitution Cipher (치환 암호)와 보안성 분석 개념: 평문의 각 문자를 고정된 다른 문자로 1:1 대응하여 변환하는 방식. 수신자는 송신자가 수행한 치환의 역과정을 통해
3.Stream Cipher, Random Number Generator

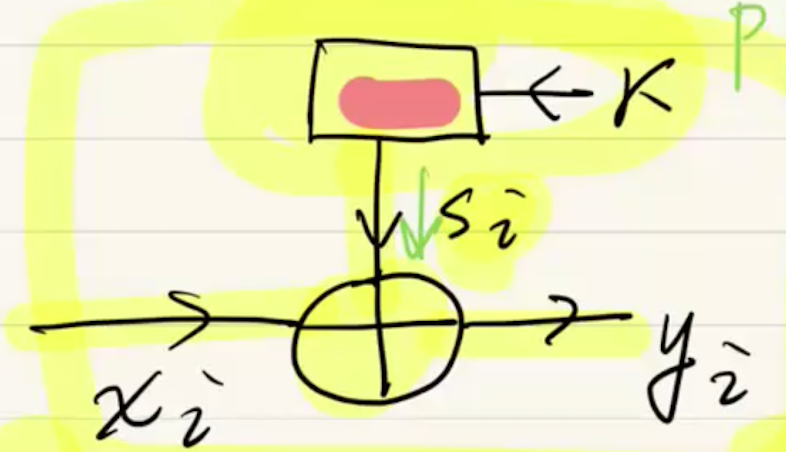
1. 스트림 암호 (Stream Cipher) 개요 개념: 데이터를 비트(Bit) 단위로 하나씩 암호화하는 방식입니다. 원리: 평문(xi)과 키 스트림(si)을 XOR(Modular 2 addition) 연산하여 암호문(yi)을 생성합니다. 수식: Encry 암호
4.DES (Data Encryption Standard)
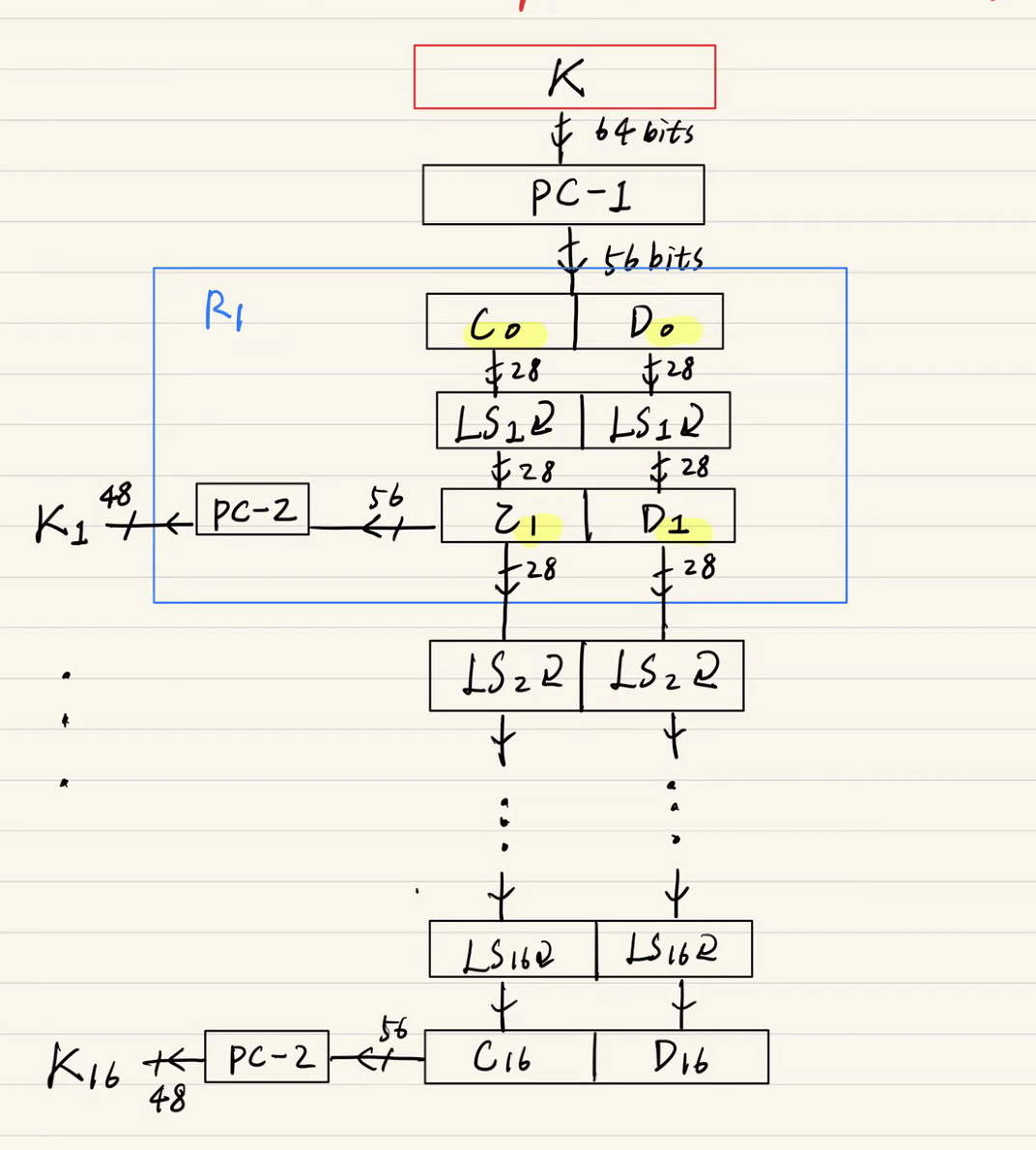
(DES) Data Encrytion standardIBM = Horst FiestelNBS1974,NSA -> IBM DES1977-1999, US standardBest studied $ applied cipher in the worldunsecure today (
5.AES Basic, GF(Galois Field)
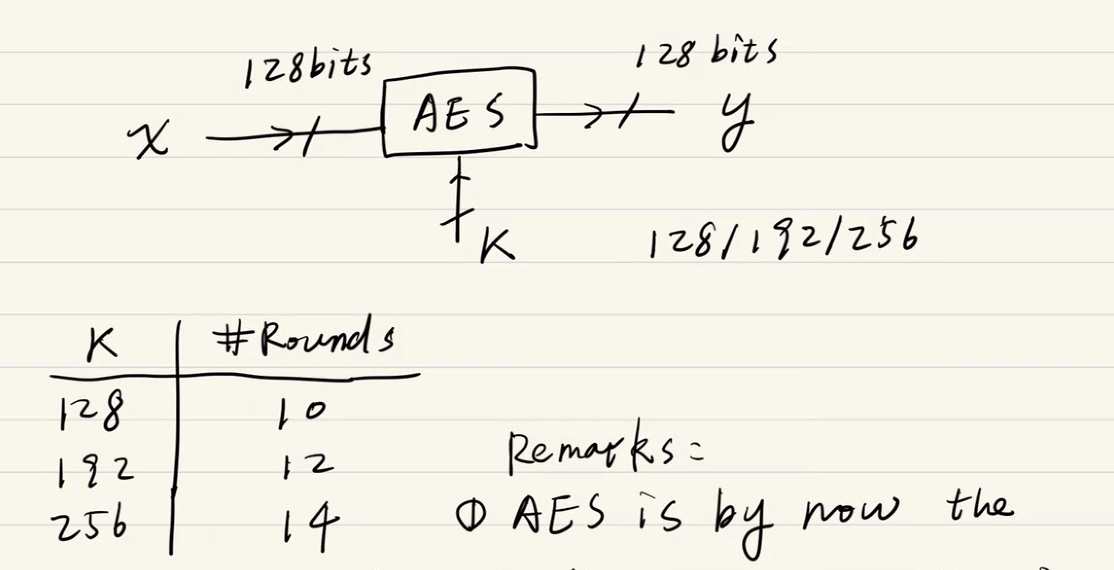
AES is by now the important symm key algorithm in the worldNSA allows AES for classified data up to Top Secret w/192 or 256 bits keyRecall:Fiestel Net
6.AES Architecture
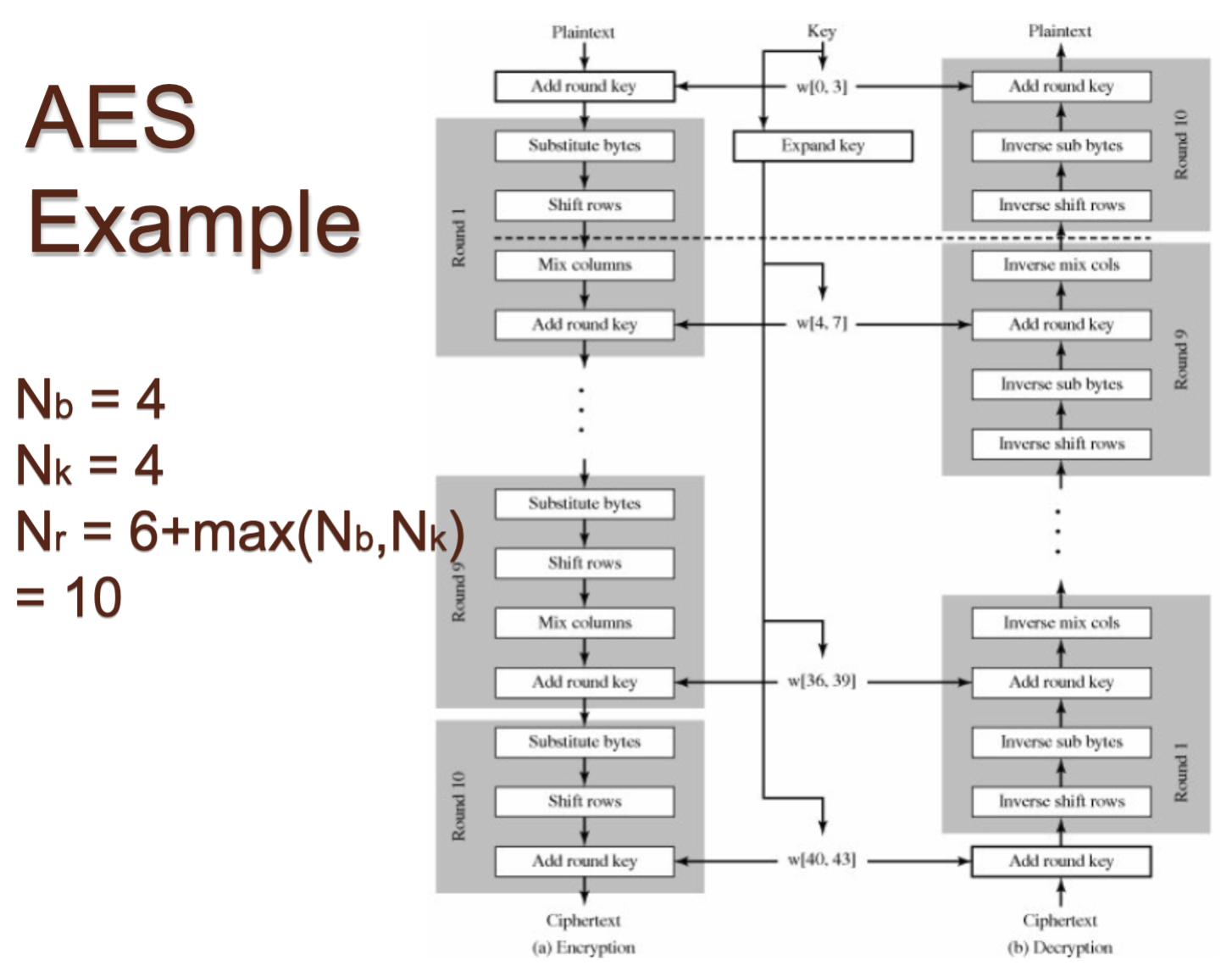
the last round does not have the mixcolumn layerAt the beginning of AES, a subkey is added.<-> Key whiteningQ: What happens inside the layers?128bi
7.Block Ciphers , ECB, CBC
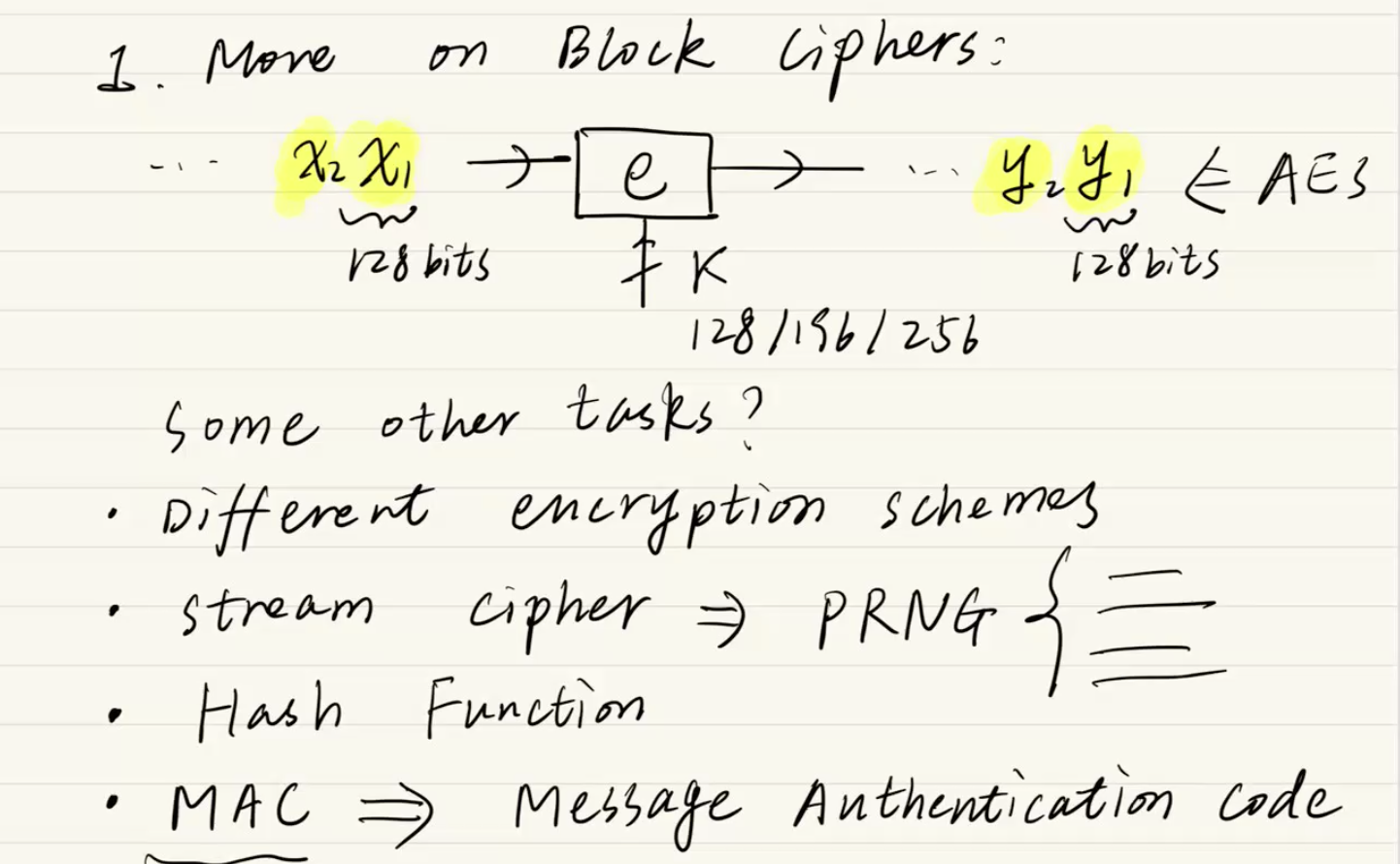
필기 상단의 그림은 AES와 같은 블록 암호가 데이터를 처리하는 기본적인 데이터 패스(Data path)를 보여줍니다.입력 (Plaintext): 암호화할 긴 데이터가 있을 때, 이를 128비트 단위의 고정된 크기인 블록($x_1, x_2, \\dots$)으로 자릅니다
8.OFB, 2DES, 3DES
Keystream Generator필기 최상단에 "idea: use the block cipher as a keystream generator"라고 적혀 있습니다. 이것이 OFB 모드의 정체성입니다.이전 모드(ECB, CBC): 평문($x_i$)이 직접 AES 같은 암
9.Euclidean algorithm, RSA
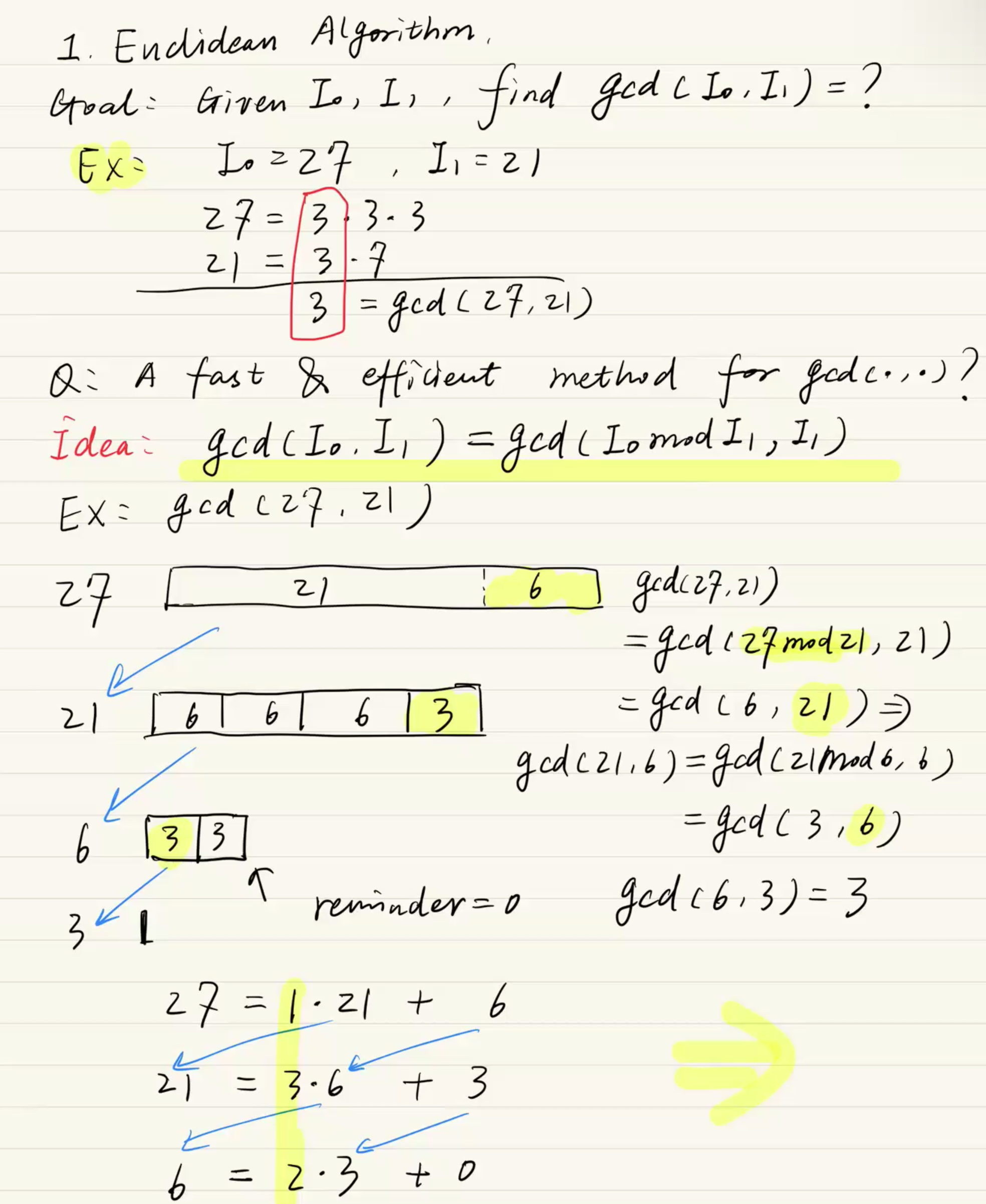
목표: 주어지는 두 수 $I_0$과 $I_1$의 최대공약수(GCD)를 빠르고 효율적으로 찾기 위함입니다.핵심 아이디어: "큰 수를 작은 수로 나눈 나머지를 구하는 과정을, 나머지가 0이 될 때까지 반복한다."수학적으로 표현하면 $gcd(I_0, I_1) = gcd(I_
10.Square-and-Multiply algorithm, Diffie-Hellman Key Exchange(DHKE)
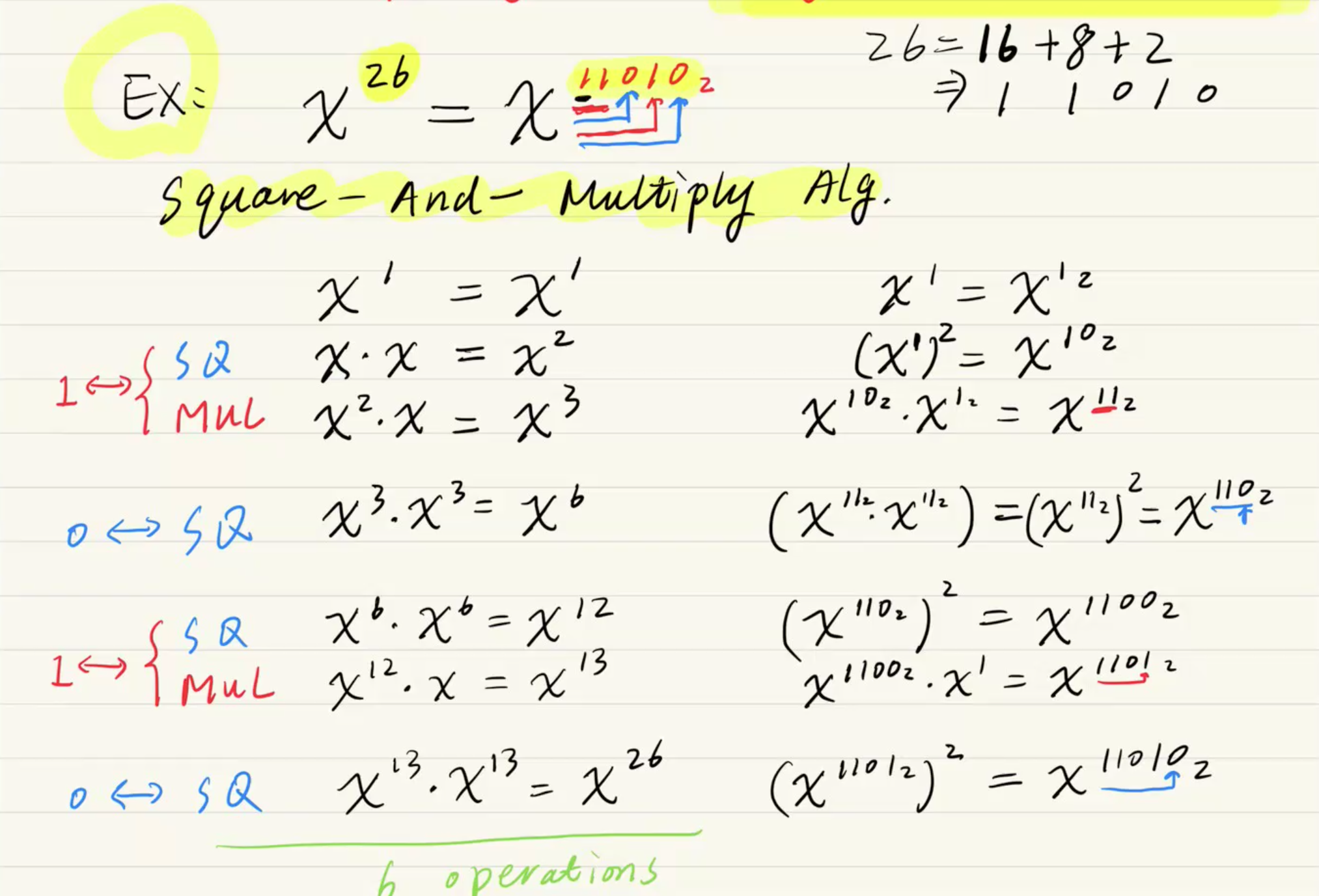
지수가 $2^{1024}$처럼 거대할 때, 곱셈 횟수를 획기적으로 줄여 컴퓨터가 실시간으로 계산할 수 있게 해주는 마법 같은 알고리즘입니다.동작 원리1\. 이진수 변환: 먼저 지수(Exponent)를 이진수(Binary Number)로 변환합니다. (예: $26 \\r
11.Cyber HW
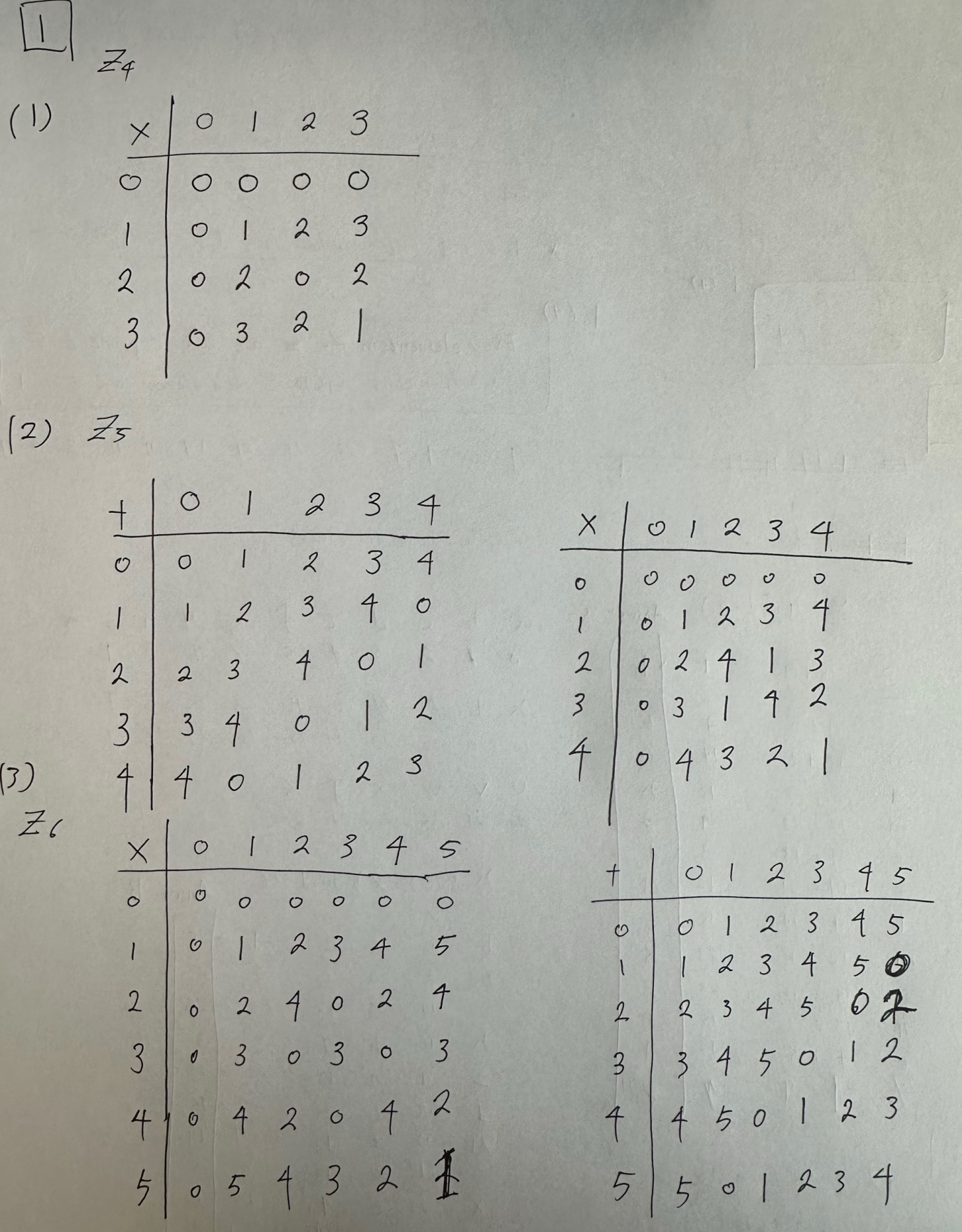
We consider the ring ℤ4. Construct a table which describes the addition of all elements in the ring with each other:(1) Construct the multiplication t
12.Mid Term Example
1) Please draw the general structure inside Round 1 of DES (i.e., the Feistel network for Round 1).2) Please draw the general structure of AES within
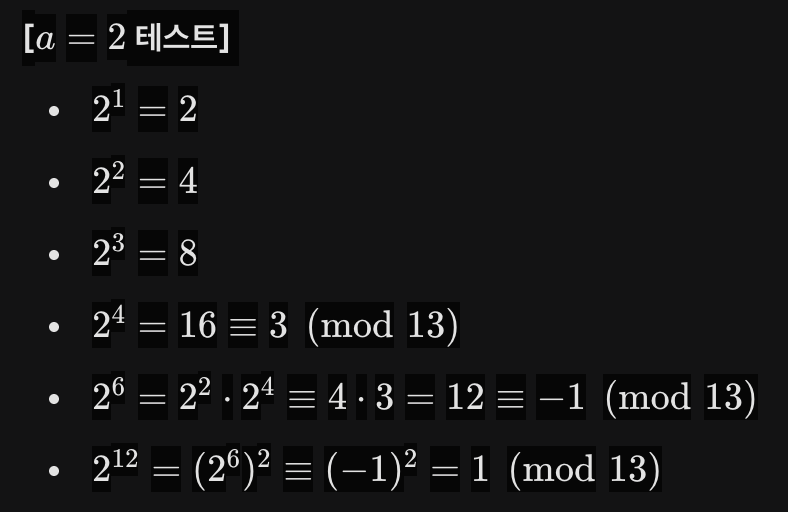
13.기말범위: Review of DLP
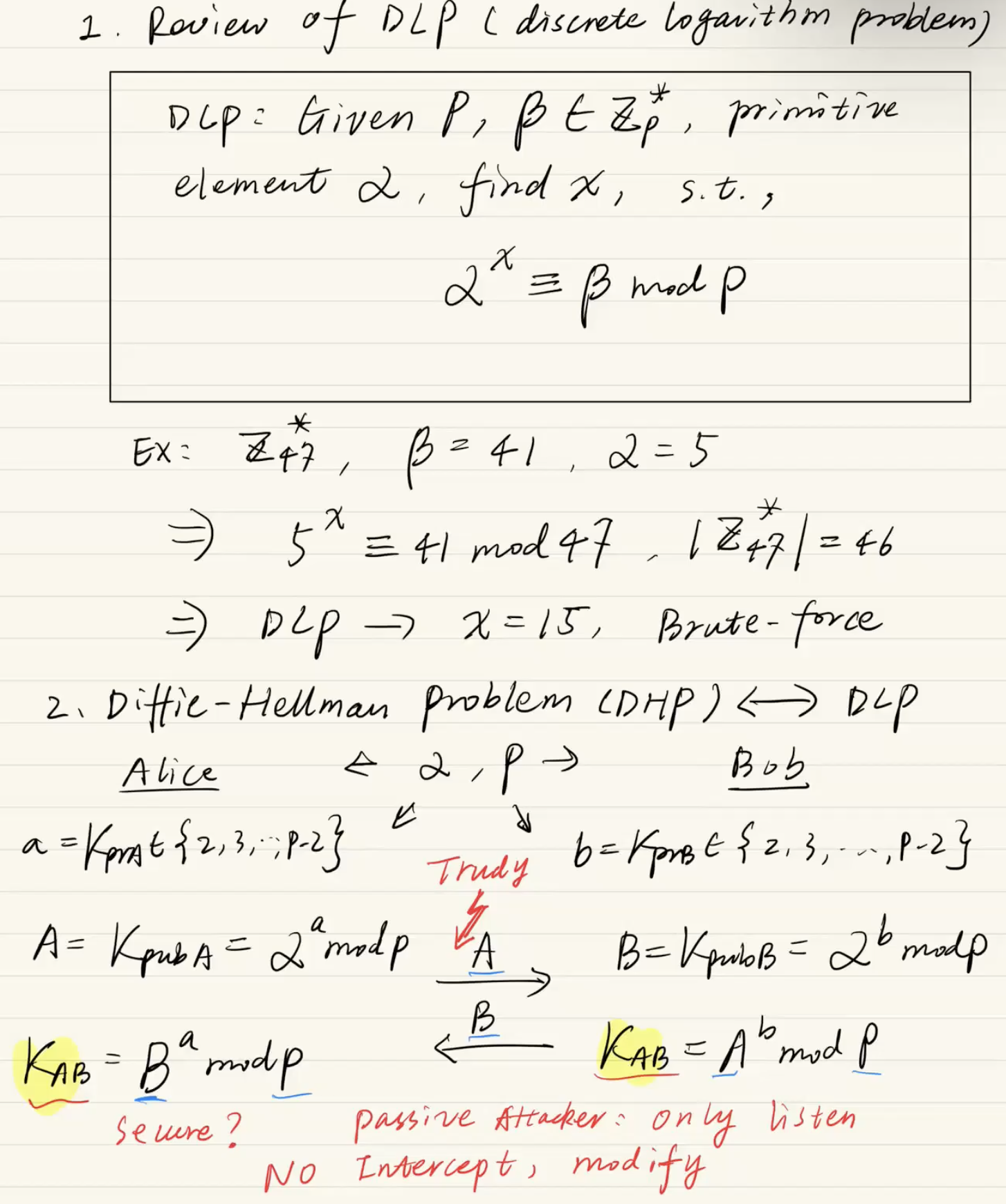

이 필기는 Elgamal Encryption(엘가말 암호화)의 작동 원리와 그것이 본질적으로 Diffie-Hellman(D-H) 키 교환과 얼마나 똑같은지를 증명하는 아주 중요한 내용입니다."Very similar to D-H, but w/ reordering of s
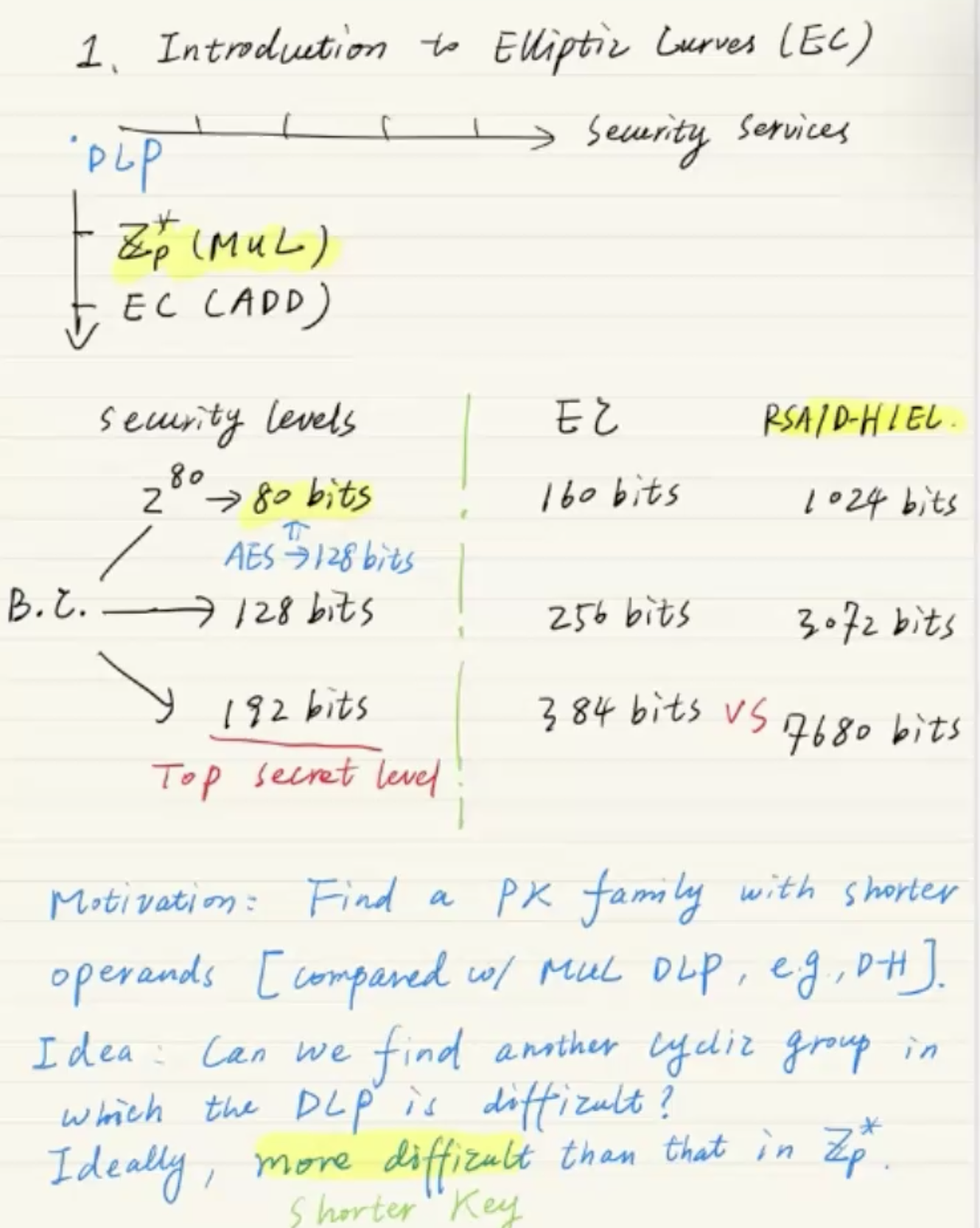
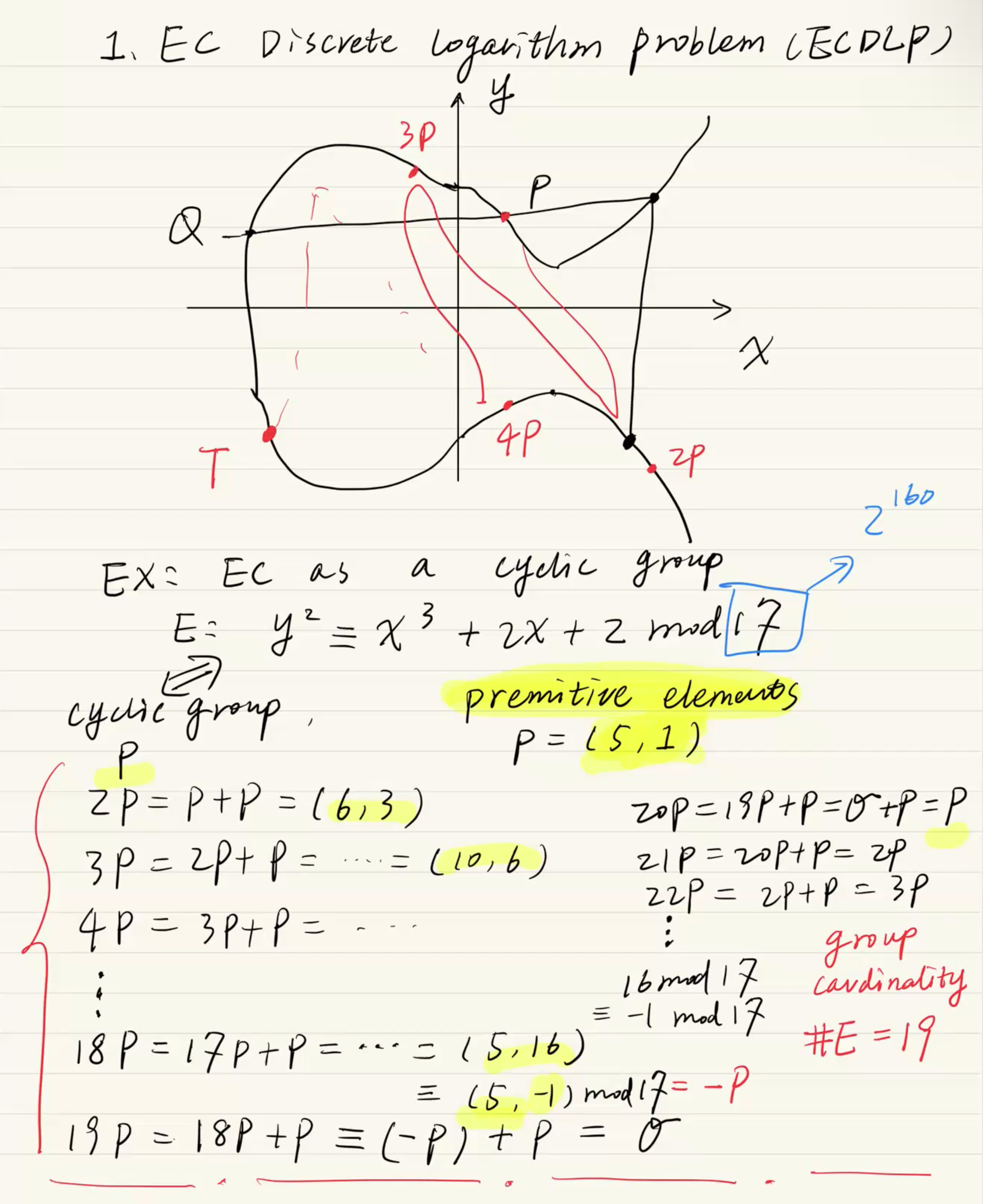
15.Elliptic Curve Cryptography(ECC)





$$n = p \\cdot q = 3 \\cdot 11 = 33$$$$\\phi(n) = (p - 1)(q - 1) = 2 \\cdot 10 = 20$$$$7 \\cdot e \\equiv 1 \\pmod{20}$$$7 \\cdot 3 = 21 \\equiv 1 \\p
21.MAC, HMAC, Markle-Damgord construction
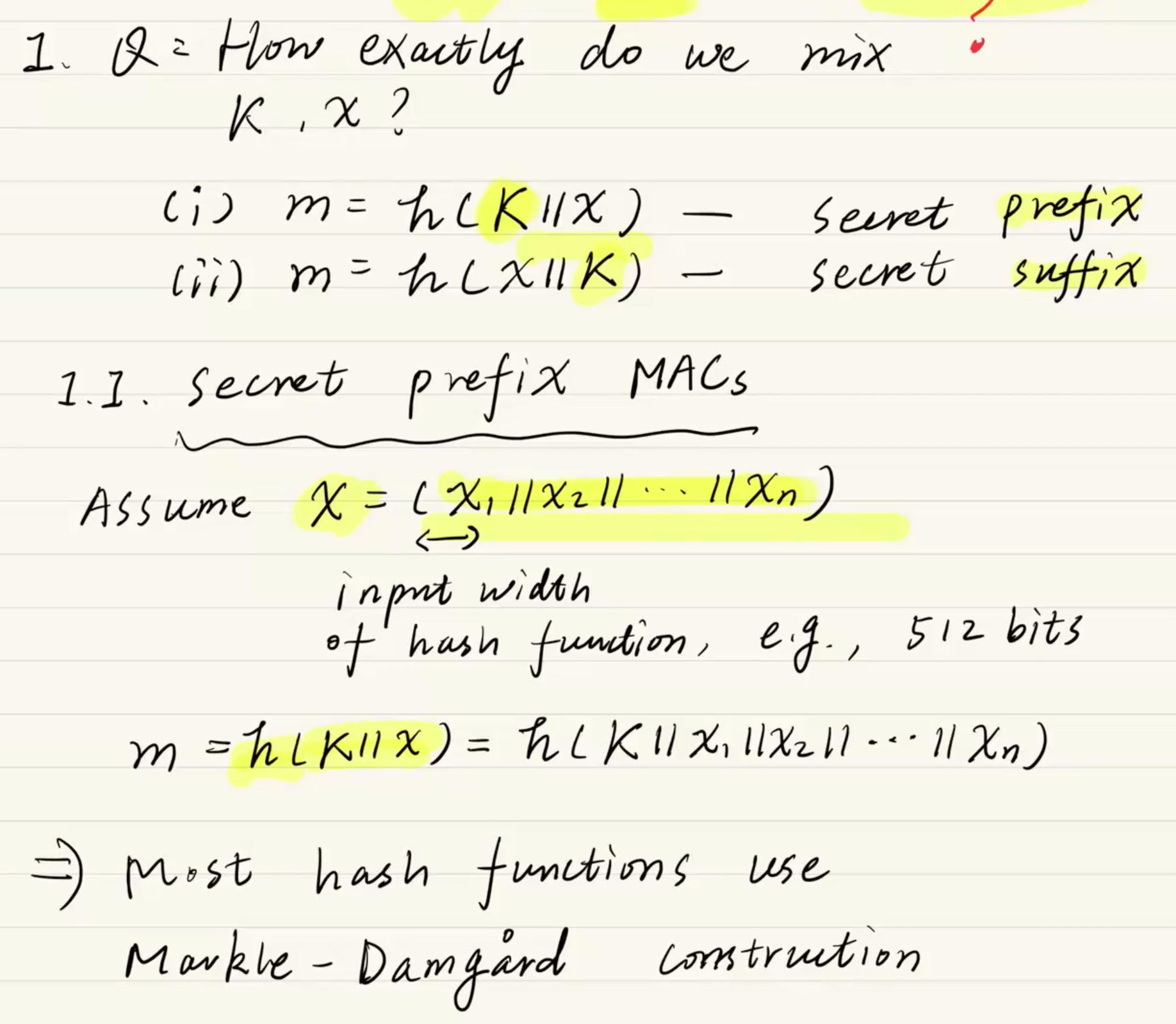
MAC을 구현하는 방법 중 하나로, 방금 전까지 뼈빠지게 배운 해시 함수를 재활용하여 MAC을 만드는 방식입니다.요구 조건: 해시 함수처럼 입력 길이는 자유롭고(Arbitrary), 출력 길이는 고정(Fixed)되어야 합니다.HMAC의 기본 아이디어:새로운 암호 알고리
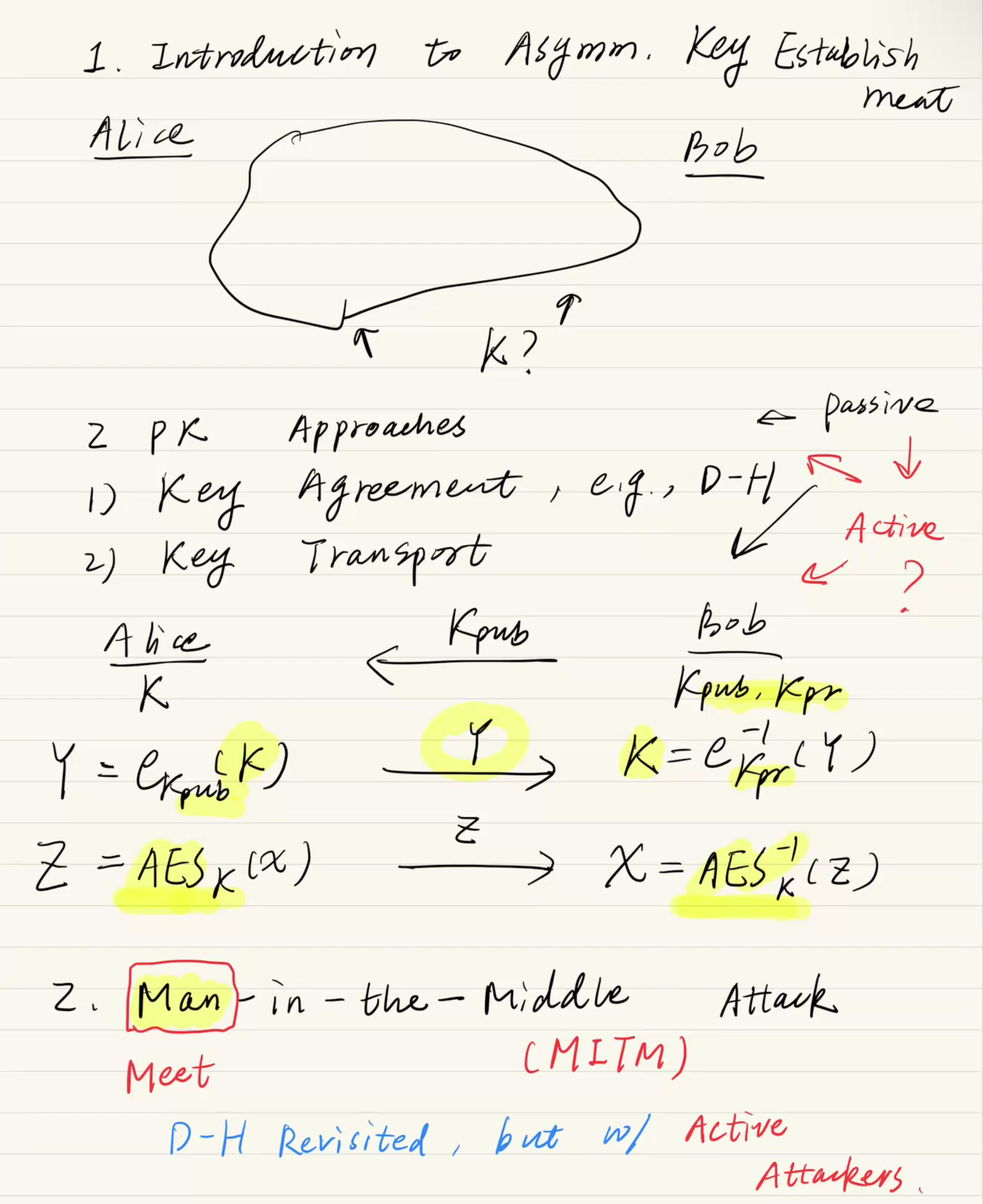
22.KDC (Key Distribution Center)
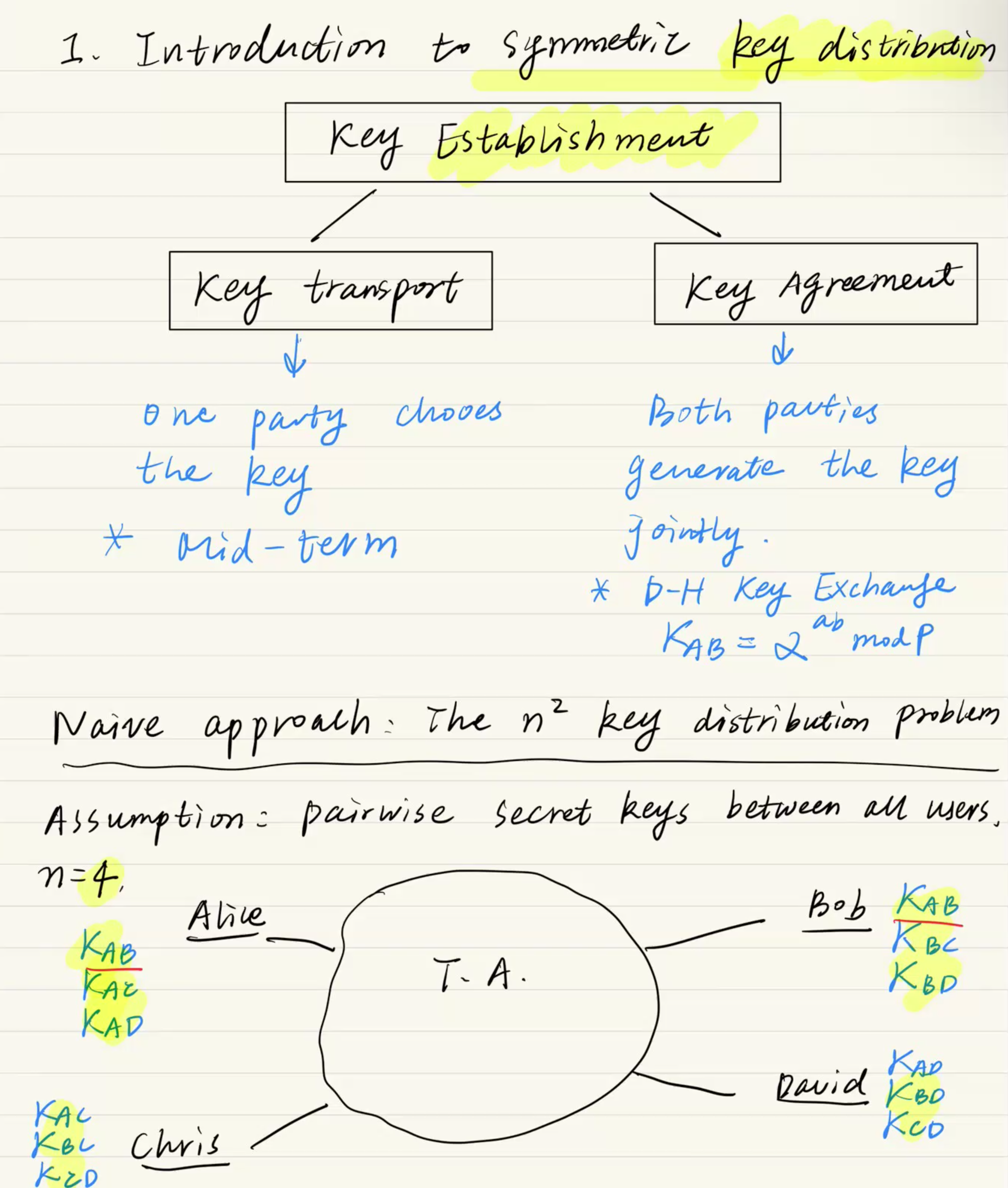
, CA

개인 키 $a = 6$상대방의 공개 키 $B = (5, 9)$타원 곡선 $E: y^2 \\equiv x^3 + x + 6 \\pmod{11}$ (즉, $A = 1, B\_{curve} = 6, p = 11$) $B \\rightarrow 2B \\rightarrow 3