📌 Secret
- password or key 같은 민감한 정보를 저장하는데 사용
- 인코딩된 형식으로 저장된다는 점만 빼면
configMap과 동일
✅ 순서
- Create Secret (시크릿 생성)
- Inject into Pod(파드에 적용)
🔨 Secret 생성하기
- Imperative - (CLI: definition 파일을 사용하지 않고 생성)
# 명령줄로 직접 key value 쌍 지정
$ kubectl create secret generic <secret-name> --from-literal=<key>=<value>
# 파일과 경로로 생성하는 방법
$ kubectl create secret generic <secret-name> --from-file=<path-to-file>
- Declarative
$ kubectl create -f
# secret-data.yaml
apiVersion: v1
kind: Secret
metadata:
name: app-secret
data:
DB_Host: mysql
DB_User: root
DB_Password: paswrd- 데이터를 인코딩된 형식으로 저장함
- 리눅스에서
echo -n커맨드를 사용하면 인코딩된 형식을 볼 수 있음
$ echo -n ‘mysql’ | base64
$ echo -n ‘root’ | base64
$ echo -n ‘paswrd’ | base64
$ echo -n ‘bXlzcWw=‘ | base64 --decode
$ echo -n ‘cm9vdA==‘ | base64 --decode
$ echo -n ‘cGFzd3Jk‘ | base64 --decode
👀 Secret 확인 방법
$ kubectl get secrets
NAME TYPE DATA AGE
empty-secret Opaque 3 2m6s
$ kubectl get secret app-secret -o yaml💉 Secrets Pod에 적용하기
# pod-definition.yaml
apiVersion: v1
kind: Pod
metadata:
name: simple-webapp
labels:
name: simple-webapp
spec:
containers:
- name: simple-webapp-container
image: simple-webapp-cotainer
ports:
- containerPort: 8080
envFrom:
- secretRef:
name: app-secret // secret 개체의 실제 이름
# secret-data.yaml
apiVersion: v1
kind: Secret
metadata:
name: app-secret
data:
DB_Host: bXlzWw=
DB_User: cm9vdA==
DB_Password: cGFzd3Jk
$ kubectl create -f pod-definition.yaml👉 SINGLE ENV 적용하기 (전체 환경 변수가 아닌 Secret 중 일부 데이터만)
env:
- name: DB_Password
valueFrom:
secretKeyRef:
name: app-secret
key: DB_Password📀 Secret 전체를 VOLUME 에 넣어 환경변수 적용하기
volumes:
- name: app-secret-volume
secret:
secretName: app-secret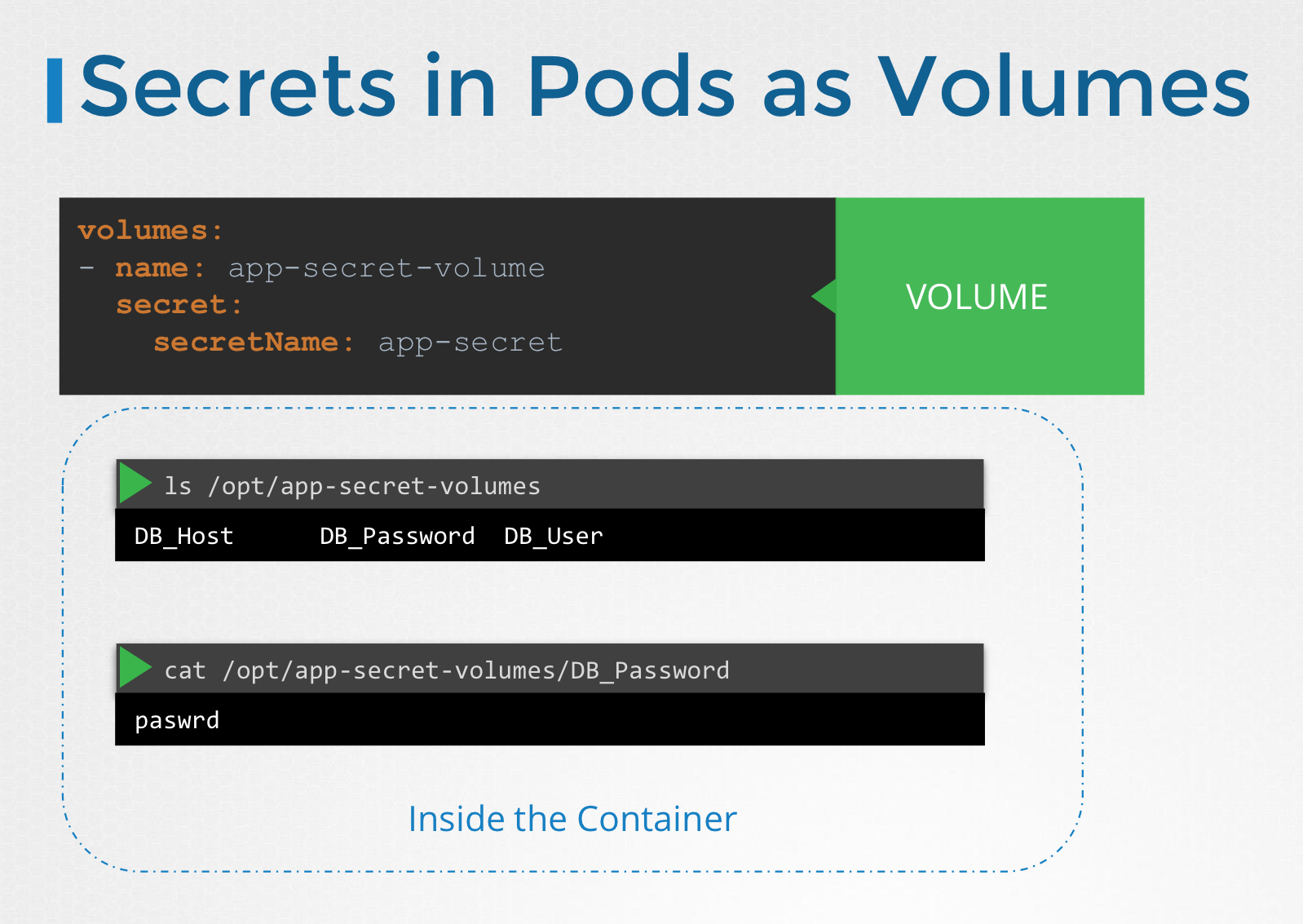
⚠️ 주의사항
- Secret은 암호화 되어있지 않다. 인코딩 되어 있기 때문에 누구든 파일을 볼 수 있다.
- 때문에 Github 등으로 Push 할때 Secret 파일을 제외하고 Push 요망
- Secret은 ETCD 안에서 암호화 되어 있지 않다
💡 https://kubernetes.io/docs/tasks/administer-cluster/encrypt-data/
apiVersion: apiserver.config.k8s.io/v1
kind: EncryptionConfiguration
resources:
- resources:
- secrets // 여기에 어떤 리소스를 암호화 할것인지 입력, 특정 리소스를 대상으로 할수 있음
- configmaps
- pandas.awesome.bears.example
providers:
- aescbc:
keys:
- name: key1
# See the following text for more details about the secret value
secret: <BASE 64 ENCODED SECRET>
- identity: {} # this fallback allows reading unencrypted secrets;
# for example, during initial migration
#
# This is a fragment of a manifest for a static Pod.
# Check whether this is correct for your cluster and for your API server.
#
apiVersion: v1
kind: Pod
metadata:
annotations:
kubeadm.kubernetes.io/kube-apiserver.advertise-address.endpoint: 10.20.30.40:443
creationTimestamp: null
labels:
app.kubernetes.io/component: kube-apiserver
tier: control-plane
name: kube-apiserver
namespace: kube-system
spec:
containers:
- command:
- kube-apiserver
...
- --encryption-provider-config=/etc/kubernetes/enc/enc.yaml # add this line
volumeMounts:
...
- name: enc # add this line
mountPath: /etc/kubernetes/enc # add this line
readOnly: true # add this line
...
volumes:
...
- name: enc # add this line
hostPath: # add this line
path: /etc/kubernetes/enc # add this line
type: DirectoryOrCreate # add this line
...
`
``
3. 동일한 네임스페이스에서 pod/deployments를 만들면 누구든 secrets에 접근 할 수 있다.
- RBAC(Role Basic Access Control) : 때문에 **역할 기반 액세스 제어**를 구성해 접근 제한을 고려할 것
4. 써드파티 암호화 공급자 (예를들어 AWS Provider, Azure Provider, GCP Provider, Vault Provider 등) 고려
- 이는 ETCD가 외부 저장소에 저장되고 보안을 대부분 보장함